Changelog
New updates and improvements at Cloudflare.
You can now scope Cloudflare permissions to individual Cloudflare Tunnel instances and Cloudflare Mesh nodes. Administrators can delegate access to specific Tunnels or Mesh nodes without granting account-wide control over private networking.
When you add a member or create a permission policy, the resource picker now lists Cloudflare Tunnel instances and Cloudflare Mesh nodes as scopable resource types. You can:
- Grant a read-only role on a single Cloudflare Tunnel instance to a support operator for log streaming and diagnostics — without exposing other Tunnels or destructive actions.
- Grant a write role on a specific Cloudflare Mesh node to an application team — without giving them access to the rest of your private network.
- Scope a single policy to one or many Tunnels and Mesh nodes at once.
Granular permissions are a parallel layer to existing account-level roles — they do not replace them.
- Existing account-level roles continue to work. A member with
Cloudflare AccessorCloudflare Zero Trustretains write access to every Tunnel and Mesh node in the account. This ensures backward compatibility for existing automation and tokens. - Granular permissions are additive. For any API request on a specific Tunnel or Mesh node, access is granted if the principal has either the account-level role or a granular permission for that resource.
- Resource enumeration is authorization-aware. Listing endpoints (
GET /accounts/{id}/cfd_tunnel,GET /accounts/{id}/warp_connector) return only the resources the principal has at least read access to.
- Configure granular permissions for Cloudflare Tunnel.
- Configure granular permissions for Cloudflare Tunnel and Cloudflare Mesh in Cloudflare One.
- Review the resource-scoped roles on the Cloudflare role reference.
You can now navigate, switch context, and take common actions in the Cloudflare dashboard without leaving your keyboard. Press
?anywhere to see the full list. Keyboard shortcuts can be disabled by visiting your profile settings ↗.Shortcut Action g hGo to Home g aGo to account overview g zGo to zone overview g pGo to your profile g wGo to Workers & Pages g oGo to Zero Trust g bGo to billing g 1–g 5Go to a recent or pinned item (by position in sidebar) t →Move to the next tab t ←Move to the previous tab p →Move to the next page of a table p ←Move to the previous page of a table Shortcut Action /Open quick search ?Show keyboard shortcuts s aSwitch account s zSwitch zone s .Star or unstar the current zone p .Pin or unpin the current page t sToggle the sidebar open or closed t mExpand or collapse all sidebar menus t aToggle Ask AI sidebar d .Toggle dark mode c uCopy the current URL c dCopy a deep link URL
You can now pay for Cloudflare services directly from your bank account using Instant Bank Payments via Link.
Link ↗ now supports bank account payments in addition to cards. If you have a bank account saved in Link, it appears as a payment option at checkout. If not, you can connect one during the checkout flow.
- During checkout, select your bank account from your saved Link payment methods.
- Confirm the payment.
After your first Link authentication, your bank account is available for future purchases without re-entering details.
Instant Bank Payments via Link is available to US-based self-serve accounts across all Cloudflare products. Your existing cards remain available at checkout.
Bank-based Link payments appear in your billing history with the payment method shown as
linkand last four digits as0000. For details, refer to the Instant Bank Payments via Link documentation.
Cloudflare-generated 5xx error responses now return structured JSON and Markdown when agents request them, matching the format already available for 1xxx errors. Responses follow RFC 9457 (Problem Details for HTTP APIs) ↗ and include a
Retry-AfterHTTP header on retryable codes.5xx coverage. Ten Cloudflare-generated error codes (500, 502, 504, 520-526) now serve structured responses. These are errors Cloudflare itself generates when it cannot reach or understand the origin server. Origin-generated 5xx responses that Cloudflare passes through are not affected.
Fault attribution. The
error_categoryfield tells agents where the fault lies:origin(502, 504, 520-524) — the origin server is responsible. Transient; retry with the backoff inretry_after.cloudflare(500) — Cloudflare's fault, not the website or the request. Short retry.ssl(525, 526) — the origin's TLS configuration is broken. Do not retry.
Retry-After header. Retryable codes (500, 502, 504, 520-524) include a
Retry-AfterHTTP header matching theretry_afterbody field. Non-retryable codes (525, 526) do not include the header.Request header sent Response format Accept: application/jsonJSON ( application/jsoncontent type)Accept: application/problem+jsonJSON ( application/problem+jsoncontent type)Accept: application/json, text/markdown;q=0.9JSON Accept: text/markdownMarkdown Accept: text/markdown, application/jsonMarkdown (equal q, first-listed wins)Accept: */*HTML (default) Available now for all zones on all plans.
Get JSON response for error 522:
Terminal window curl -s --compressed -H "Accept: application/json" -A "TestAgent/1.0" -H "Accept-Encoding: gzip, deflate" "<YOUR_DOMAIN>/cdn-cgi/error/522" | jq .Check presence of the
Retry-AfterHTTP header associated with the JSON response for error 521:Terminal window curl -s --compressed -D - -o /dev/null -H "Accept: application/json" -A "TestAgent/1.0" -H "Accept-Encoding: gzip, deflate" "<YOUR_DOMAIN>/cdn-cgi/error/521" | grep -i retry-afterReferences:
Resource Tagging is now in public beta and rolling out to all Cloudflare accounts over the coming days. You can attach custom key-value metadata to your Cloudflare resources and query across your entire account to find what you need.
- Broad resource type support — Tag zones, custom hostnames, Cloudflare Tunnels, Workers, D1 databases, R2 buckets, KV namespaces, Durable Object namespaces, Queues, Stream videos, Images, Access applications, Gateway rules, AI Gateways, and more. Refer to the full list of supported resource types.
- Powerful filtering — Query tagged resources using AND/OR logic, negation, and key-only matching. Combine up to 20 filters per query to build precise resource views.
- Account and zone-level endpoints — Full CRUD operations across both scopes.
- Token-based authentication — Tagging supports Account Owned Tokens that persist independently of individual users, so your automation keeps running through credential rotations and team changes.
- Flexible role support — Super Administrators, Workers Admins, and Tag Admins can all manage tags.
The API is the primary interface for Resource Tagging and the recommended path for all workflows — scripting tag assignments, building CI/CD pipelines, or integrating with your infrastructure-as-code toolchain.
You can also view and manage tagged resources directly in the Cloudflare dashboard. Navigate to Manage Account > Resource Tagging to see all tagged resources across your account, filter by resource name or tag, and add or edit tags inline.
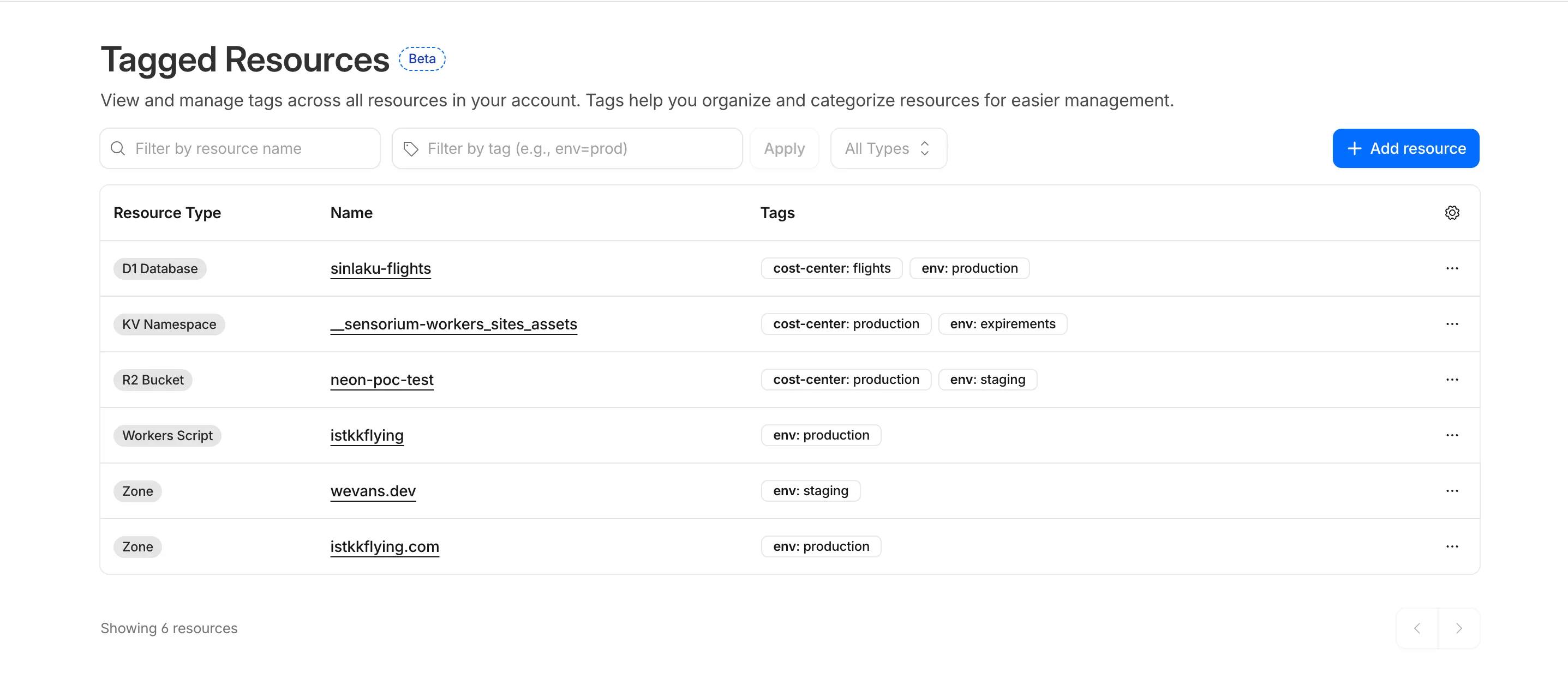
In future releases, expect support for additional resource types across the Cloudflare platform, tag-based access control policies for scoping user permissions to tagged resources, billing and usage attribution by tag for breaking down costs by team, project, or environment, and Terraform provider support for managing tags declaratively.
PUTreplaces all tags on a resource (no partial update). Use the GET, merge, PUT workflow to modify individual tags safely.DELETEremoves all tags from a resource. To remove a single tag, PUT the remaining tags back.- Querying tags for a resource that has never been tagged returns
500instead of404. This is a known beta limitation.
To get started, refer to the Resource Tagging documentation.
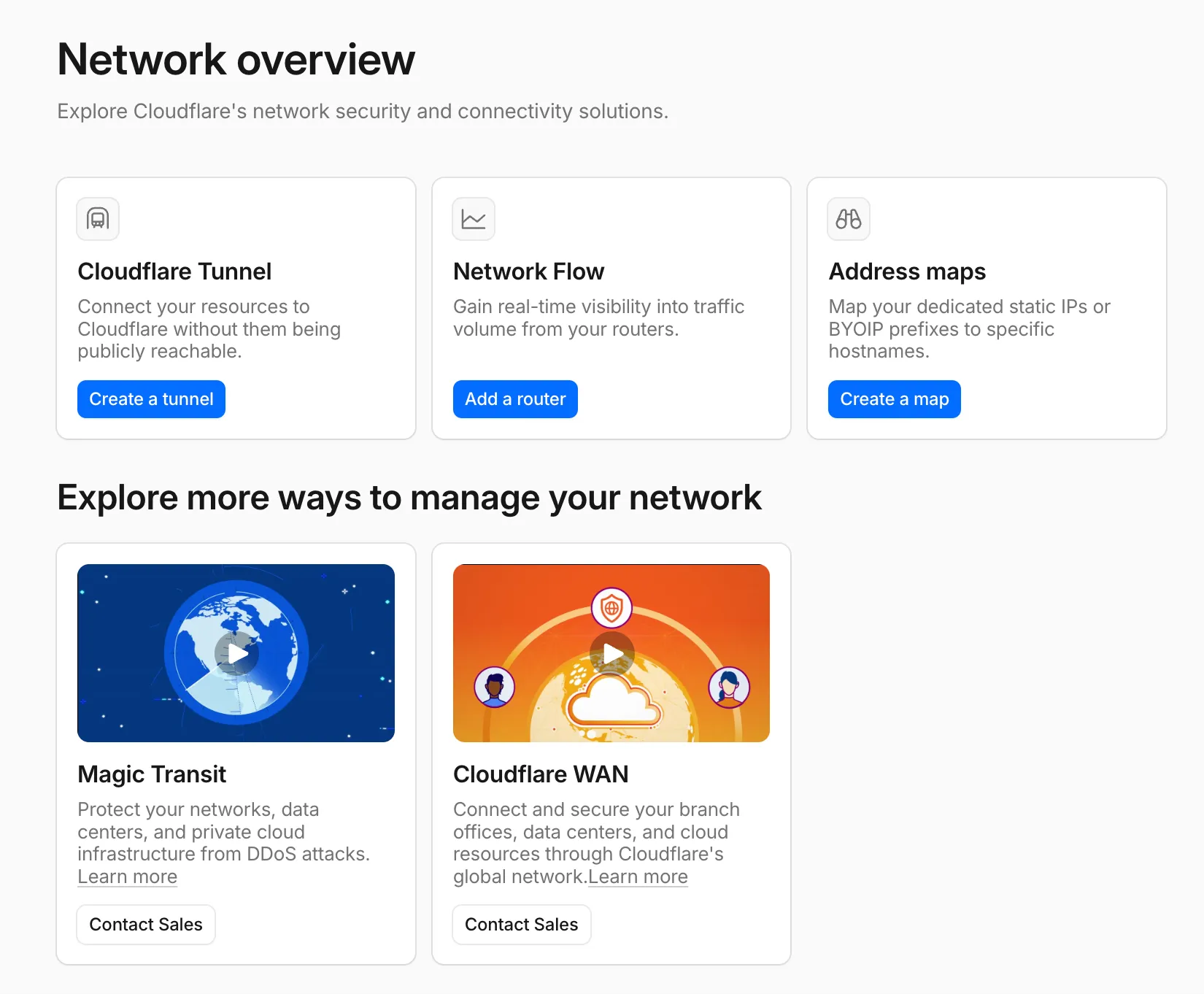
A new Network Overview page in the Cloudflare dashboard gives you a single starting point for network security and connectivity products.
From the Network Overview page, you can:
- Connect resources with Cloudflare Tunnel - Create tunnels to connect your infrastructure to Cloudflare without exposing it to the public Internet.
- Monitor traffic with Network Flow - Get real-time visibility into traffic volume from your routers.
- Configure Address Maps - Map dedicated static IPs or BYOIP prefixes to specific hostnames.
- Explore Magic Transit and Cloudflare WAN - Set up DDoS protection for your networks and connectivity for your branch offices and data centers.
To find it, go to Networking ↗ in the dashboard sidebar.
If you already use Magic Transit, Cloudflare WAN, or other Cloudflare network services products, your existing experience is unchanged.
Pay-as-you-go customers can now monitor usage-based costs and configure spend alerts through two new features: the Billable Usage dashboard and Budget alerts.
The Billable Usage dashboard provides daily visibility into usage-based costs across your Cloudflare account. The data comes from the same system that generates your monthly invoice, so the figures match your bill.
The dashboard displays:
- A bar chart showing daily usage charges for your billing period
- A sortable table breaking down usage by product, including total usage, billable usage, and cumulative costs
- Ability to view previous billing periods
Usage data aligns to your billing cycle, not the calendar month. The total usage cost shown at the end of a completed billing period matches the usage overage charges on your corresponding invoice.
To access the dashboard, go to Manage Account > Billing > Billable Usage.
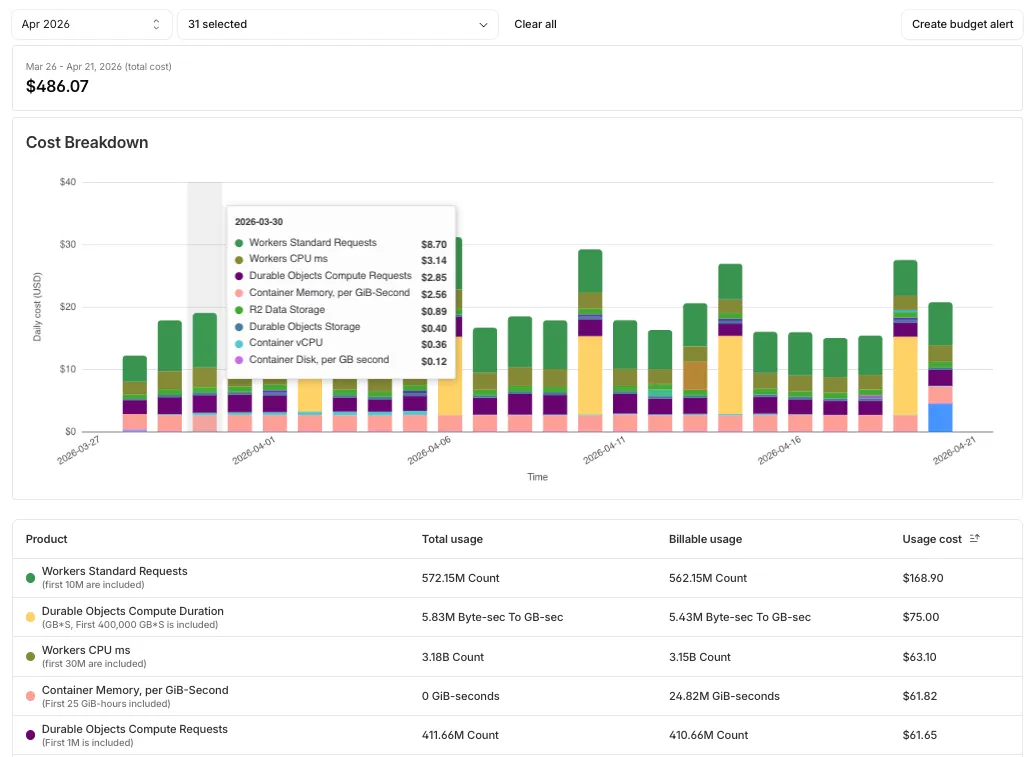
Budget alerts allow you to set dollar-based thresholds for your account-level usage spend. You receive an email notification when your projected monthly spend reaches your configured threshold, giving you proactive visibility into your bill before month-end.
To configure a budget alert:
- Go to Manage Account > Billing > Billable Usage.
- Select Set Budget Alert.
- Enter a budget threshold amount greater than $0.
- Select Create.
Alternatively, configure alerts via Notifications > Add > Budget Alert.
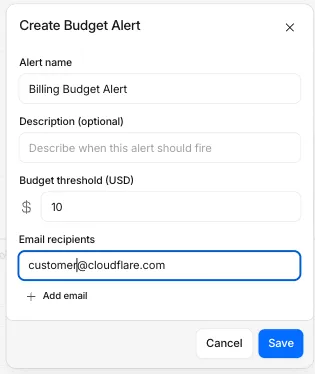
You can create multiple budget alerts at different dollar amounts. The notifications system automatically deduplicates alerts if multiple thresholds trigger at the same time. Budget alerts are calculated daily based on your usage trends and fire once per billing cycle when your projected spend first crosses your threshold.
Both features are available to Pay-as-you-go accounts with usage-based products (Workers, R2, Images, etc.). Enterprise contract accounts are not supported.
For more information, refer to the Usage based billing documentation.
OAuth allows third-party applications to access your Cloudflare account on your behalf — like when Wrangler deploys Workers or when monitoring tools read your analytics. You now have granular control over which accounts these applications can access, plus the ability to revoke access anytime.
When authorizing an OAuth application, you can now select specific accounts instead of granting access to all your accounts:
- Account-by-account selection — Choose exactly which accounts the application can access
- "All accounts" option — Still available for trusted tools like Wrangler This gives you precise control who can access your data.
The OAuth consent screen now shows:
- What the application can access — Explicit list of permissions being requested
- Who created the application — Application owner and contact information
- Which accounts you're authorizing — Checkboxes for account selection
Manage authorized OAuth applications from your profile:
- See all connected apps — View every OAuth application with access to your accounts
- Review permissions and scope — Check what each application can do and which accounts it can access
- Revoke instantly — Remove access with one click when you no longer need it To manage your OAuth applications, navigate to Profile > Access Management > Connected Applications ↗.
These updates give you:
- Granular control — Authorize apps per-account instead of all-or-nothing
- Transparency — Know exactly what you're authorizing before you consent
- Security — Limit blast radius by restricting access to only necessary accounts
- Easy cleanup — Revoke access when applications are no longer needed
Read more about these improvements in our blog post: Improving the OAuth consent experience ↗.
Cloudflare API tokens now include identifiable patterns that enable secret scanning tools to automatically detect them when leaked in code repositories, configuration files, or other public locations.
API tokens generated by Cloudflare now follow a standardized format that secret scanning tools can recognize. When a Cloudflare token is accidentally committed to GitHub, GitLab, or another platform with secret scanning enabled, the tool will flag it and alert you.
Leaked credentials are a common security risk. By making Cloudflare tokens detectable by scanning tools, you can:
- Detect leaks faster — Get notified immediately when a token is exposed.
- Reduce risk window — Exposed tokens are deactivated immediately, before they can be exploited.
- Automate security — Leverage existing secret scanning infrastructure without additional configuration.
When a third-party secret scanning tool detects a leaked Cloudflare API token:
- Cloudflare immediately deactivates the token to prevent unauthorized access.
- The token creator receives an email notification alerting them to the leak.
- The token is marked as "Exposed" in the Cloudflare dashboard.
- You can then roll or delete the token from the token management pages.
- GitHub Secret Scanning — Automatically enabled for public repositories
For more information on token formats and secret scanning, refer to API token formats.
We're announcing the public beta of Organizations for enterprise customers, a new top-level Cloudflare container that lets Cloudflare customers manage multiple accounts, members, analytics, and shared policies from one centralized location.
What's New
Organizations [BETA]: Organizations are a new top-level container for centrally managing multiple accounts. Each Organization supports up to 500 accounts and 5000 zones, giving larger teams a single place to administer resources at scale.
Self-serve onboarding: Enterprise customers can create an Organization in the dashboard and assign accounts where they are already Super Administrators.
Centralized Account Management: At launch, every Organization member has the Organization Super Admin role. Organization Super Admins can invite other users and manage any child account under the Organization implicitly. Shared policies: Share WAF or Gateway policies across multiple accounts within your Organization to simplify centralized policy management. Implicit access: Members of an Organization automatically receive Super Administrator permissions across child accounts, removing the need for explicit membership on each account. Additional Org-level roles will be available over the course of the year.
Unified analytics: View, filter, and download aggregate HTTP analytics across all Organization child accounts from a single dashboard for centralized visibility into traffic patterns and security events.
Terraform provider support: Manage Organizations with infrastructure as code from day one. Provision organizations, assign accounts, and configure settings programmatically with the Cloudflare Terraform provider ↗.
Shared policies: Share WAF or Gateway policies across multiple accounts within your Organization to simplify centralized policy management.
For more info:
Service Key authentication for the Cloudflare API is deprecated. Service Keys will stop working on September 30, 2026.
API Tokens replace Service Keys with fine-grained permissions, expiration, and revocation.
Replace any use of the
X-Auth-User-Service-Keyheader with an API Token scoped to the permissions your integration requires.If you use
cloudflared, update to a version from November 2022 or later. These versions already use API Tokens.If you use origin-ca-issuer ↗, update to a version that supports API Token authentication.
For more information, refer to API deprecations.
Cloudflare dashboard SCIM provisioning now supports Authentik ↗ as an identity provider, joining Okta and Microsoft Entra ID as explicitly supported providers.
Customers can now sync users and group information from Authentik to Cloudflare, apply Permission Policies to those groups, and manage the lifecycle of users & groups directly from your Authentik Identity Provider.
For more information:
Cloudflare dashboard SCIM provisioning operations are now captured in Audit Logs v2, giving you visibility into user and group changes made by your identity provider.
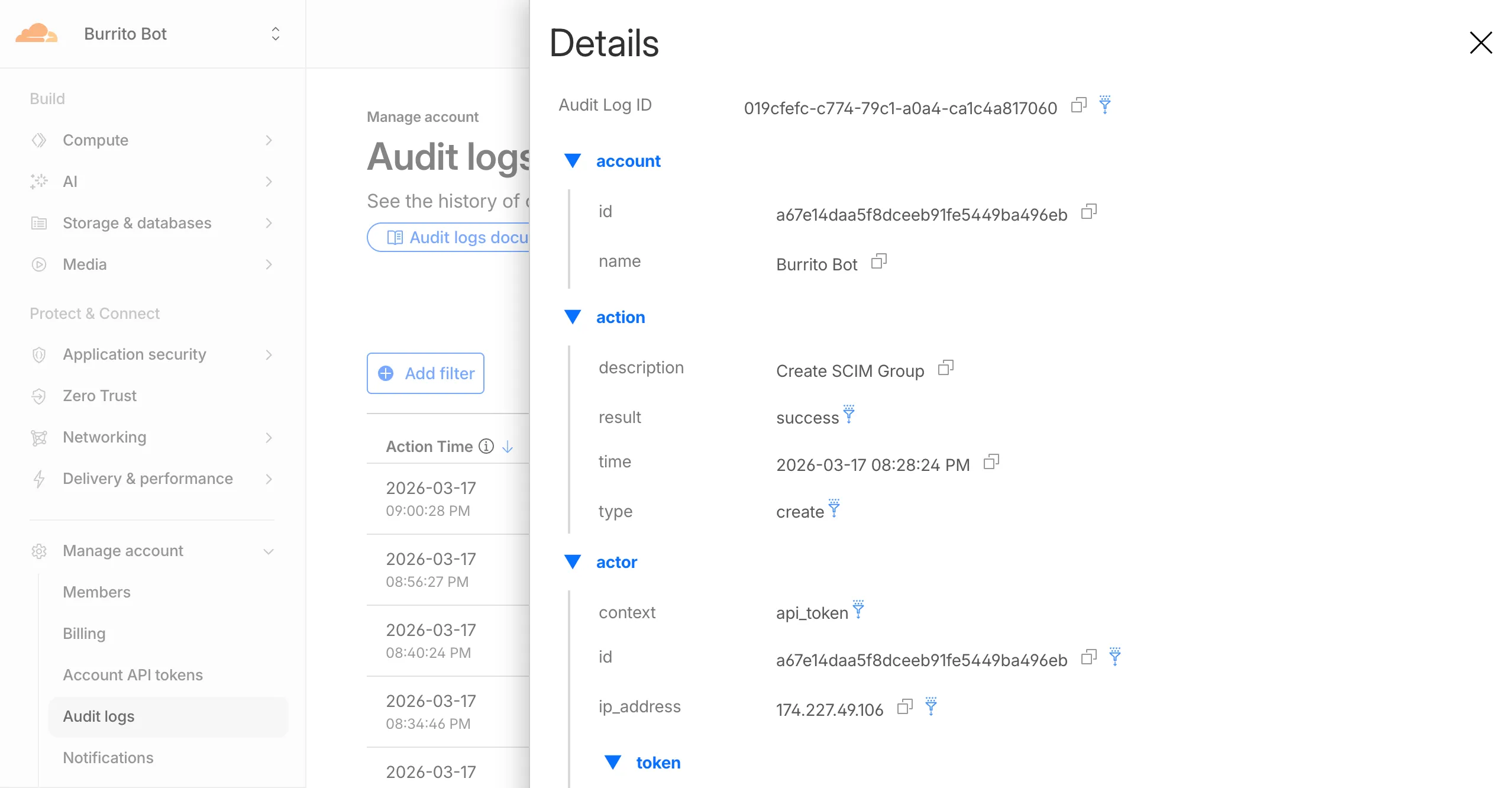
Logged actions:
Action Type Description Create SCIM User User provisioned from IdP Replace SCIM User User fully replaced (PUT) Update SCIM User User attributes modified (PATCH) Delete SCIM User Member deprovisioned Create SCIM Group Group provisioned from IdP Update SCIM Group Group membership or attributes modified Delete SCIM Group Group deprovisioned For more details, refer to the Audit Logs v2 documentation.
Cloudflare-generated 1xxx error responses now include a standard
Retry-AfterHTTP header when the error is retryable. Agents and HTTP clients can read the recommended wait time from response headers alone — no body parsing required.Seven retryable error codes now emit
Retry-After:Error code Retry-After (seconds) Error name 1004 120 DNS resolution error 1005 120 Banned zone 1015 30 Rate limited 1033 120 Argo Tunnel error 1038 60 HTTP headers limit exceeded 1200 60 Cache connection limit 1205 5 Too many redirects The header value matches the existing
retry_afterbody field in JSON and Markdown responses.If a WAF rate limiting rule has already set a dynamic
Retry-Aftervalue on the response, that value takes precedence.Available for all zones on all plans.
Check for the header on any retryable error:
Terminal window curl -s --compressed -D - -o /dev/null -H "Accept: application/json" -A "TestAgent/1.0" -H "Accept-Encoding: gzip, deflate" "<YOUR_DOMAIN>/cdn-cgi/error/1015" | grep -i retry-afterReferences:
Cloudflare-generated 1xxx errors now return structured JSON when clients send
Accept: application/jsonorAccept: application/problem+json. JSON responses follow RFC 9457 (Problem Details for HTTP APIs) ↗, so any HTTP client that understands Problem Details can parse the base members without Cloudflare-specific code.The Markdown frontmatter field
http_statushas been renamed tostatus. Agents consuming Markdown frontmatter should update parsers accordingly.JSON format. Clients sending
Accept: application/jsonorAccept: application/problem+jsonnow receive a structured JSON object with the same operational fields as Markdown frontmatter, plus RFC 9457 standard members.RFC 9457 standard members (JSON only):
type— URI pointing to Cloudflare documentation for the specific error codestatus— HTTP status code (matching the response status)title— short, human-readable summarydetail— human-readable explanation specific to this occurrenceinstance— Ray ID identifying this specific error occurrence
Field renames:
http_status->status(JSON and Markdown)what_happened->detail(JSON only — Markdown prose sections are unchanged)
Content-Type mirroring. Clients sending
Accept: application/problem+jsonreceiveContent-Type: application/problem+json; charset=utf-8back;Accept: application/jsonreceivesapplication/json; charset=utf-8. Same body in both cases.Request header sent Response format Accept: application/jsonJSON ( application/jsoncontent type)Accept: application/problem+jsonJSON ( application/problem+jsoncontent type)Accept: application/json, text/markdown;q=0.9JSON Accept: text/markdownMarkdown Accept: text/markdown, application/jsonMarkdown (equal q, first-listed wins)Accept: */*HTML (default) Available now for Cloudflare-generated 1xxx errors.
Terminal window curl -s --compressed -H "Accept: application/json" -A "TestAgent/1.0" -H "Accept-Encoding: gzip, deflate" "<YOUR_DOMAIN>/cdn-cgi/error/1015" | jq .Terminal window curl -s --compressed -H "Accept: application/problem+json" -A "TestAgent/1.0" -H "Accept-Encoding: gzip, deflate" "<YOUR_DOMAIN>/cdn-cgi/error/1015" | jq .References:
Cloudflare now returns structured Markdown responses for Cloudflare-generated 1xxx errors when clients send
Accept: text/markdown.Each response includes YAML frontmatter plus guidance sections (
What happened/What you should do) so agents can make deterministic retry and escalation decisions without parsing HTML.In measured 1,015 comparisons, Markdown reduced payload size and token footprint by over 98% versus HTML.
Included frontmatter fields:
error_code,error_name,error_category,http_statusray_id,timestamp,zonecloudflare_error,retryable,retry_after(when applicable),owner_action_required
Default behavior is unchanged: clients that do not explicitly request Markdown continue to receive HTML error pages.
Cloudflare uses standard HTTP content negotiation on the
Acceptheader.Accept: text/markdown-> MarkdownAccept: text/markdown, text/html;q=0.9-> MarkdownAccept: text/*-> MarkdownAccept: */*-> HTML (default browser behavior)
When multiple values are present, Cloudflare selects the highest-priority supported media type using
qvalues. If Markdown is not explicitly preferred, HTML is returned.Available now for Cloudflare-generated 1xxx errors.
Terminal window curl -H "Accept: text/markdown" https://<your-domain>/cdn-cgi/error/1015Reference: Cloudflare 1xxx error documentation
When AI systems request pages from any website that uses Cloudflare and has Markdown for Agents enabled, they can express the preference for
text/markdownin the request: our network will automatically and efficiently convert the HTML to markdown, when possible, on the fly.This release adds the following improvements:
- The origin response limit was raised from 1 MB to 2 MB (2,097,152 bytes).
- We no longer require the origin to send the
content-lengthheader. - We now support content encoded responses from the origin.
If you haven’t enabled automatic Markdown conversion yet, visit the AI Crawl Control ↗ section of the Cloudflare dashboard and enable Markdown for Agents.
Refer to our developer documentation for more details.
Fine-grained permissions for Access policies and Access service tokens are available. These new resource-scoped roles expand the existing RBAC model, enabling administrators to grant permissions scoped to individual resources.
- Cloudflare Access policy admin: Can edit a specific Access policy in an account.
- Cloudflare Access service token admin: Can edit a specific Access service token in an account.
These roles complement the existing resource-scoped roles for Access applications, identity providers, and infrastructure targets.
For more information:
Disclaimer: Please note that v5.0.0-beta.1 is in Beta and we are still testing it for stability.
Full Changelog: v4.3.1...v5.0.0-beta.1 ↗
In this release, you'll see a large number of breaking changes. This is primarily due to a change in OpenAPI definitions, which our libraries are based off of, and codegen updates that we rely on to read those OpenAPI definitions and produce our SDK libraries. As the codegen is always evolving and improving, so are our code bases.
There may be changes that are not captured in this changelog. Feel free to open an issue to report any inaccuracies, and we will make sure it gets into the changelog before the v5.0.0 release.
Most of the breaking changes below are caused by improvements to the accuracy of the base OpenAPI schemas, which sometimes translates to breaking changes in downstream clients that depend on those schemas.
Please ensure you read through the list of changes below and the migration guide before moving to this version - this will help you understand any down or upstream issues it may cause to your environments.
The following resources have breaking changes. See the v5 Migration Guide ↗ for detailed migration instructions.
abusereportsacm.totaltlsapigateway.configurationscloudforceone.threateventsd1.databaseintel.indicatorfeedslogpush.edgeorigintlsclientauth.hostnamesqueues.consumersradar.bgprulesets.rulesschemavalidation.schemassnippetszerotrust.dlpzerotrust.networks
abusereports- Abuse report managementabusereports.mitigations- Abuse report mitigation actionsai.tomarkdown- AI-powered markdown conversionaigateway.dynamicrouting- AI Gateway dynamic routing configurationaigateway.providerconfigs- AI Gateway provider configurationsaisearch- AI-powered search functionalityaisearch.instances- AI Search instance managementaisearch.tokens- AI Search authentication tokensalerting.silences- Alert silence managementbrandprotection.logomatches- Brand protection logo match detectionbrandprotection.logos- Brand protection logo managementbrandprotection.matches- Brand protection match resultsbrandprotection.queries- Brand protection query managementcloudforceone.binarystorage- CloudForce One binary storageconnectivity.directory- Connectivity directory servicesd1.database- D1 database managementdiagnostics.endpointhealthchecks- Endpoint health check diagnosticsfraud- Fraud detection and preventioniam.sso- IAM Single Sign-On configurationloadbalancers.monitorgroups- Load balancer monitor groupsorganizations- Organization managementorganizations.organizationprofile- Organization profile settingsorigintlsclientauth.hostnamecertificates- Origin TLS client auth hostname certificatesorigintlsclientauth.hostnames- Origin TLS client auth hostnamesorigintlsclientauth.zonecertificates- Origin TLS client auth zone certificatespipelines- Data pipeline managementpipelines.sinks- Pipeline sink configurationspipelines.streams- Pipeline stream configurationsqueues.subscriptions- Queue subscription managementr2datacatalog- R2 Data Catalog integrationr2datacatalog.credentials- R2 Data Catalog credentialsr2datacatalog.maintenanceconfigs- R2 Data Catalog maintenance configurationsr2datacatalog.namespaces- R2 Data Catalog namespacesradar.bots- Radar bot analyticsradar.ct- Radar certificate transparency dataradar.geolocations- Radar geolocation datarealtimekit.activesession- Real-time Kit active session managementrealtimekit.analytics- Real-time Kit analyticsrealtimekit.apps- Real-time Kit application managementrealtimekit.livestreams- Real-time Kit live streamingrealtimekit.meetings- Real-time Kit meeting managementrealtimekit.presets- Real-time Kit preset configurationsrealtimekit.recordings- Real-time Kit recording managementrealtimekit.sessions- Real-time Kit session managementrealtimekit.webhooks- Real-time Kit webhook configurationstokenvalidation.configuration- Token validation configurationtokenvalidation.rules- Token validation rulesworkers.beta- Workers beta features
edit()update()
list()
create()get()update()
scan_list()scan_review()scan_trigger()
create()delete()list()
get()
list()
summary()timeseries()timeseries_groups()
changes()snapshot()
delete()
create()delete()edit()get()list()
- Type inference improvements: Allow Pyright to properly infer TypedDict types within SequenceNotStr
- Type completeness: Add missing types to method arguments and response models
- Pydantic compatibility: Ensure compatibility with Pydantic versions prior to 2.8.0 when using additional fields
- Multipart form data: Correctly handle sending multipart/form-data requests with JSON data
- Header handling: Do not send headers with default values set to omit
- GET request headers: Don't send Content-Type header on GET requests
- Response body model accuracy: Broad improvements to the correctness of models
- Discriminated unions: Correctly handle nested discriminated unions in response parsing
- Extra field types: Parse extra field types correctly
- Empty metadata: Ignore empty metadata fields during parsing
- Singularization rules: Update resource name singularization rules for better consistency
Cloudflare's network now supports real-time content conversion at the source, for enabled zones using content negotiation ↗ headers. When AI systems request pages from any website that uses Cloudflare and has Markdown for Agents enabled, they can express the preference for
text/markdownin the request: our network will automatically and efficiently convert the HTML to markdown, when possible, on the fly.Here is a curl example with the
Acceptnegotiation header requesting this page from our developer documentation:Terminal window curl https://developers.cloudflare.com/fundamentals/reference/markdown-for-agents/ \-H "Accept: text/markdown"The response to this request is now formatted in markdown:
HTTP/2 200date: Wed, 11 Feb 2026 11:44:48 GMTcontent-type: text/markdown; charset=utf-8content-length: 2899vary: acceptx-markdown-tokens: 725content-signal: ai-train=yes, search=yes, ai-input=yes---title: Markdown for Agents · Cloudflare Agents docs---## What is Markdown for AgentsMarkdown has quickly become the lingua franca for agents and AI systemsas a whole. The format’s explicit structure makes it ideal for AI processing,ultimately resulting in better results while minimizing token waste....Refer to our developer documentation and our blog announcement ↗ for more details.
In January 2025, we announced the launch of the new Terraform v5 Provider. We greatly appreciate the proactive engagement and valuable feedback from the Cloudflare community following the v5 release. In response, we have established a consistent and rapid 2-3 week cadence ↗ for releasing targeted improvements, demonstrating our commitment to stability and reliability.
With the help of the community, we have a growing number of resources that we have marked as stable ↗, with that list continuing to grow with every release. The most used resources ↗ are on track to be stable by the end of March 2026, when we will also be releasing a new migration tool to help you migrate from v4 to v5 with ease.
This release brings new capabilities for AI Search, enhanced Workers Script placement controls, and numerous bug fixes based on community feedback. We also begun laying foundational work for improving the v4 to v5 migration process. Stay tuned for more details as we approach the March 2026 release timeline.
Thank you for continuing to raise issues. They make our provider stronger and help us build products that reflect your needs.
- ai_search_instance: add data source for querying AI Search instances
- ai_search_token: add data source for querying AI Search tokens
- account: add support for tenant unit management with new
unitfield - account: add automatic mapping from
managed_by.parent_org_idtounit.id - authenticated_origin_pulls_certificate: add data source for querying authenticated origin pull certificates
- authenticated_origin_pulls_hostname_certificate: add data source for querying hostname-specific authenticated origin pull certificates
- authenticated_origin_pulls_settings: add data source for querying authenticated origin pull settings
- workers_kv: add
valuefield to data source to retrieve KV values directly - workers_script: add
scriptfield to data source to retrieve script content - workers_script: add support for
simplerate limit binding - workers_script: add support for targeted placement mode with
placement.targetarray for specifying placement targets (region, hostname, host) - workers_script: add
placement_modeandplacement_statuscomputed fields - zero_trust_dex_test: add data source with filter support for finding specific tests
- zero_trust_dlp_predefined_profile: add
enabled_entriesfield for flexible entry management
- account: map
managed_by.parent_org_idtounit.idin unmarshall and add acceptance tests - authenticated_origin_pulls_certificate: add certificate normalization to prevent drift
- authenticated_origin_pulls: handle array response and implement full lifecycle
- authenticated_origin_pulls_hostname_certificate: fix resource and tests
- cloudforce_one_request_message: use correct
request_idfield instead ofidin API calls - dns_zone_transfers_incoming: use correct
zone_idfield instead ofidin API calls - dns_zone_transfers_outgoing: use correct
zone_idfield instead ofidin API calls - email_routing_settings: use correct
zone_idfield instead ofidin API calls - hyperdrive_config: add proper handling for write-only fields to prevent state drift
- hyperdrive_config: add normalization for empty
mtlsobjects to prevent unnecessary diffs - magic_network_monitoring_rule: use correct
account_idfield instead ofidin API calls - mtls_certificates: fix resource and test
- pages_project: revert build_config to computed optional
- stream_key: use correct
account_idfield instead ofidin API calls - total_tls: use upsert pattern for singleton zone setting
- waiting_room_rules: use correct
waiting_room_idfield instead ofidin API calls - workers_script: add support for placement mode/status
- zero_trust_access_application: update v4 version on migration tests
- zero_trust_device_posture_rule: update tests to match API
- zero_trust_dlp_integration_entry: use correct
entry_idfield instead ofidin API calls - zero_trust_dlp_predefined_entry: use correct
entry_idfield instead ofidin API calls - zero_trust_organization: fix plan issues
- add state upgraders to 95+ resources to lay the foundation for replacing Grit (still under active development)
- certificate_pack: add state migration handler for SDKv2 to Framework conversion
- custom_hostname_fallback_origin: add comprehensive lifecycle test and migration support
- dns_record: add state migration handler for SDKv2 to Framework conversion
- leaked_credential_check: add import functionality and tests
- load_balancer_pool: add state migration handler with detection for v4 vs v5 format
- pages_project: add state migration handlers
- tiered_cache: add state migration handlers
- zero_trust_dlp_predefined_profile: deprecate
entriesfield in favor ofenabled_entries
You can now set the timezone in the Cloudflare dashboard as Coordinated Universal Time (UTC) or your browser or system's timezone.
Unless otherwise specified in the user interface, all dates and times in the Cloudflare dashboard are now displayed in the selected timezone.
You can change the timezone setting from the user profile dropdown.
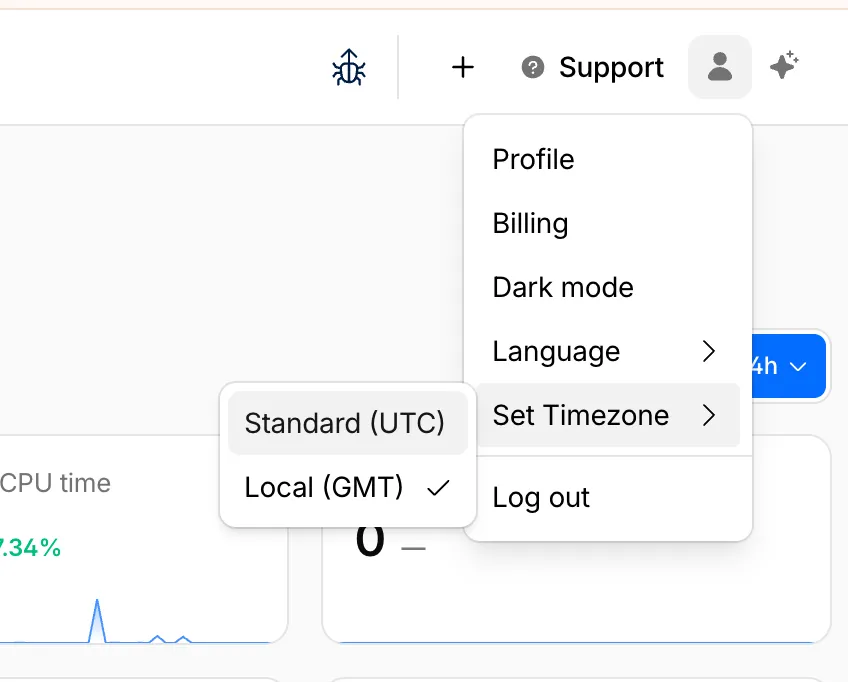
The page will reload to apply the new timezone setting.
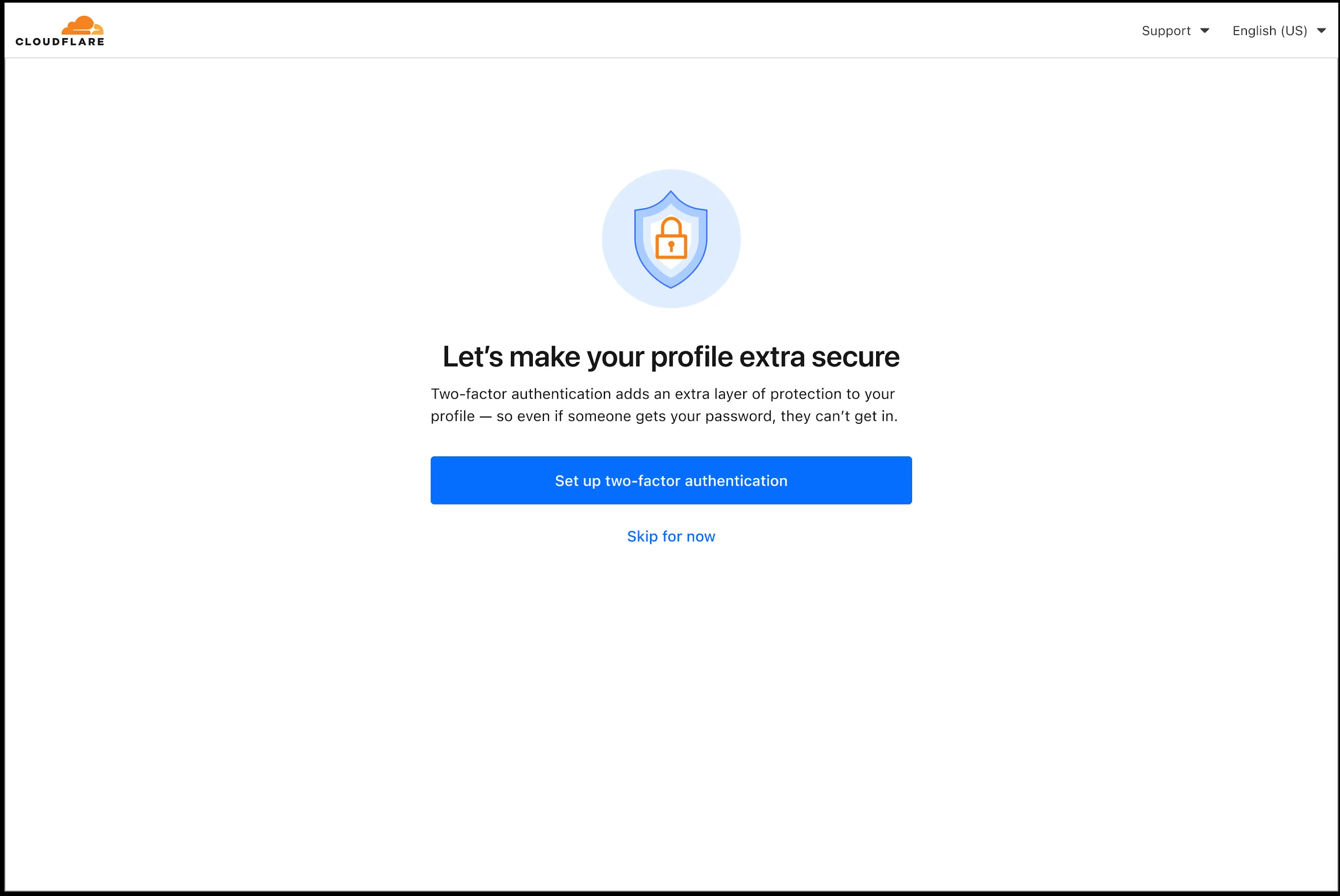
In an effort to improve overall user security, users without 2FA will be prompted upon login to enroll in email 2FA. This will improve user security posture while minimizing friction. Users without email 2FA enabled will see a prompt to secure their account with additional factors upon logging in. Enrolling in 2FA remains optional, but strongly encouraged as it is the best way to prevent account takeovers.
We also made changes to existing 2FA screens to improve the user experience. Now we have distinct experiences for each 2FA factor type, reflective of the way that factor works.
Disclaimer: Please note that v6.0.0-beta.1 is in Beta and we are still testing it for stability.
Full Changelog: v5.2.0...v6.0.0-beta.1 ↗
In this release, you'll see a large number of breaking changes. This is primarily due to a change in OpenAPI definitions, which our libraries are based off of, and codegen updates that we rely on to read those OpenAPI definitions and produce our SDK libraries. As the codegen is always evolving and improving, so are our code bases.
Some breaking changes were introduced due to bug fixes, also listed below.
Please ensure you read through the list of changes below before moving to this version - this will help you understand any down or upstream issues it may cause to your environments.
BGPPrefixCreateParams.cidr: optional → requiredPrefixCreateParams.asn:number | null→numberPrefixCreateParams.loa_document_id: required → optionalServiceBindingCreateParams.cidr: optional → requiredServiceBindingCreateParams.service_id: optional → required
ConfigurationUpdateResponseremovedPublicSchema→OldPublicSchemaSchemaUpload→UserSchemaCreateResponseConfigurationUpdateParams.propertiesremoved; usenormalize
ThreatEventBulkCreateResponse:number→ complex object with counts and errors
DatabaseQueryParams: simple interface → union type (D1SingleQuery | MultipleQueries)DatabaseRawParams: same change- Supports batch queries via
batcharray
All record type interfaces renamed from
*Recordto short names:RecordResponse.ARecord→RecordResponse.ARecordResponse.AAAARecord→RecordResponse.AAAARecordResponse.CNAMERecord→RecordResponse.CNAMERecordResponse.MXRecord→RecordResponse.MXRecordResponse.NSRecord→RecordResponse.NSRecordResponse.PTRRecord→RecordResponse.PTRRecordResponse.TXTRecord→RecordResponse.TXTRecordResponse.CAARecord→RecordResponse.CAARecordResponse.CERTRecord→RecordResponse.CERTRecordResponse.DNSKEYRecord→RecordResponse.DNSKEYRecordResponse.DSRecord→RecordResponse.DSRecordResponse.HTTPSRecord→RecordResponse.HTTPSRecordResponse.LOCRecord→RecordResponse.LOCRecordResponse.NAPTRRecord→RecordResponse.NAPTRRecordResponse.SMIMEARecord→RecordResponse.SMIMEARecordResponse.SRVRecord→RecordResponse.SRVRecordResponse.SSHFPRecord→RecordResponse.SSHFPRecordResponse.SVCBRecord→RecordResponse.SVCBRecordResponse.TLSARecord→RecordResponse.TLSARecordResponse.URIRecord→RecordResponse.URIRecordResponse.OpenpgpkeyRecord→RecordResponse.Openpgpkey
ResourceGroupCreateResponse.scope: optional single → required arrayResourceGroupCreateResponse.id: optional → required
OriginCACertificateCreateParams.csr: optional → requiredOriginCACertificateCreateParams.hostnames: optional → requiredOriginCACertificateCreateParams.request_type: optional → required
- Renamed:
DeploymentsSinglePage→DeploymentListResponsesV4PagePaginationArray - Domain response fields: many optional → required
- Entire v0 API deprecated; use v1 methods (
createV1,listV1, etc.) - New sub-resources:
Sinks,Streams
EventNotificationUpdateParams.rules: optional → required- Super Slurper:
bucket,secretnow required in source params
dataSource:string→ typed enum (23 values)eventType:string→ typed enum (6 values)- V2 methods require
dimensionparameter (breaking signature change)
- Removed:
status_messagefield from all recipient response types
- Consolidated
SchemaCreateResponse,SchemaListResponse,SchemaEditResponse,SchemaGetResponse→PublicSchema - Renamed:
SchemaListResponsesV4PagePaginationArray→PublicSchemasV4PagePaginationArray
- Renamed union members:
AppListResponse.UnionMember0→SpectrumConfigAppConfig - Renamed union members:
AppListResponse.UnionMember1→SpectrumConfigPaygoAppConfig
- Removed:
WorkersBindingKindTailConsumertype (all occurrences) - Renamed:
ScriptsSinglePage→ScriptListResponsesSinglePage - Removed:
DeploymentsSinglePage
datasets.create(),update(),get()return types changedPredefinedGetResponseunion members renamed toUnionMember0-5
- Removed:
CloudflaredCreateResponse,CloudflaredListResponse,CloudflaredDeleteResponse,CloudflaredEditResponse,CloudflaredGetResponse - Removed:
CloudflaredListResponsesV4PagePaginationArray
- Reports:
create,list,get - Mitigations: sub-resource for abuse mitigations
- Instances:
create,update,list,delete,read,stats - Items:
list,get - Jobs:
create,list,get,logs - Tokens:
create,update,list,delete,read
- Directory Services:
create,update,list,delete,get - Supports IPv4, IPv6, dual-stack, and hostname configurations
- Organizations:
create,update,list,delete,get - OrganizationProfile:
update,get - Hierarchical organization support with parent/child relationships
- Catalog:
list,enable,disable,get - Credentials:
create - MaintenanceConfigs:
update,get - Namespaces:
list - Tables:
list, maintenance config management - Apache Iceberg integration
- Apps:
get,post - Meetings:
create,get, participant management - Livestreams: 10+ methods for streaming
- Recordings: start, pause, stop, get
- Sessions: transcripts, summaries, chat
- Webhooks: full CRUD
- ActiveSession: polls, kick participants
- Analytics: organization analytics
- Configuration:
create,list,delete,edit,get - Credentials:
update - Rules:
create,list,delete,bulkCreate,bulkEdit,edit,get - JWT validation with RS256/384/512, PS256/384/512, ES256, ES384
create,update,list,delete,get
create,update,list,delete,get,beginVerification
- Sinks:
create,list,delete,get - Streams:
create,update,list,delete,get
- Portals:
create,update,list,delete,read - Servers:
create,update,list,delete,read,sync
managed_byfield withparent_org_id,parent_org_name
auto_generatedfield onLOADocumentCreateResponse
delegate_loa_creation,irr_validation_state,ownership_validation_state,ownership_validation_token,rpki_validation_state
- Added
toMarkdown.supported()method to get all supported conversion formats
zdrfield added to all responses and params
- New alert type:
abuse_report_alert typefield added to PolicyFilter
ContentCreateParams: refined to discriminated union (Variant0 | Variant1)- Split into URL-based and HTML-based parameter variants for better type safety
reactivateparameter in edit
ThreatEventCreateParams.indicatorType: required → optionalhasChildrenfield added to all threat event response typesdatasetIdsquery parameter onAttackerListParams,CategoryListParams,TargetIndustryListParamscategoryUuidfield onTagCreateResponseindicatorsarray for multi-indicator support per eventuuidandpreserveUuidfields for UUID preservation in bulk createformatquery parameter ('json' | 'stix2') onThreatEventListParamscreatedAt,datasetIdfields onThreatEventEditParams
- Added
create(),update(),get()methods
- New page types:
basic_challenge,under_attack,waf_challenge
served_by_colo- colo that handled queryjurisdiction-'eu' | 'fedramp'- Time Travel (
client.d1.database.timeTravel):getBookmark(),restore()- point-in-time recovery
- New fields on
InvestigateListResponse/InvestigateGetResponse:envelope_from,envelope_to,postfix_id_outbound,replyto - New detection classification:
'outbound_ndr' - Enhanced
Findinginterface withattachment,detection,field,portion,reason,score - Added
cursorquery parameter toInvestigateListParams
- New list types:
CATEGORY,LOCATION,DEVICE
- New issue type:
'configuration_suggestion' payloadfield:unknown→ typedPayloadinterface withdetection_method,zone_tag
- Added
detections.get()method
- New datasets:
dex_application_tests,dex_device_state_events,ipsec_logs,warp_config_changes,warp_toggle_changes
Monitor.port:number→number | nullPool.load_shedding:LoadShedding→LoadShedding | nullPool.origin_steering:OriginSteering→OriginSteering | null
license_keyfield on connectorsprovision_licenseparameter for auto-provisioning- IPSec:
custom_remote_identitieswith FQDN support - Snapshots: Bond interface,
probed_mtufield
- New response types:
ProjectCreateResponse,ProjectListResponse,ProjectEditResponse,ProjectGetResponse - Deployment methods return specific response types instead of generic
Deployment
- Added
subscriptions.get()method - Enhanced
SubscriptionGetResponsewith typed event source interfaces - New event source types: Images, KV, R2, Vectorize, Workers AI, Workers Builds, Workflows
- Sippy: new provider
s3(S3-compatible endpoints) - Sippy:
bucketUrlfield for S3-compatible sources - Super Slurper:
keysfield on source response schemas (specify specific keys to migrate) - Super Slurper:
pathPrefixfield on source schemas - Super Slurper:
regionfield on S3 source params
- Added
geolocations.list(),geolocations.get()methods - Added V2 dimension-based methods (
summaryV2,timeseriesGroupsV2) to radar sub-resources
- Added
terminalboolean field to Resource Error interfaces
- Added
idfield toItemDeleteParams.Item
- New buffering fields on
SetConfigRule:request_body_buffering,response_body_buffering
- New scopes:
'dex','access'(in addition to'workers','ai_gateway')
- Response types now proper interfaces (was
unknown) - Fields now required:
id,certificates,hosts,status,type
payloadfield:unknown→ typedPayloadinterface withdetection_method,zone_tag
- Added:
CloudflareTunnelsV4PagePaginationArraypagination class
- Added
subdomains.delete()method Worker.references- track external dependencies (domains, Durable Objects, queues)Worker.startup_time_ms- startup timingScript.observability- observability settings with loggingScript.tag,Script.tags- immutable ID and tags- Placement: support for region, hostname, host-based placement
tags,tail_consumersnow accept| null- Telemetry:
tracesfield,$containersevent info,durableObjectId,transactionName,abr_levelfields
ScriptUpdateResponse: new fieldsentry_point,observability,tag,tagsplacementfield now union of 4 variants (smart mode, region, hostname, host)tags,tail_consumersnow nullableTagUpdateParams.bodynow acceptsnull
instance_retention:unknown→ typedInstanceRetentioninterface witherror_retention,success_retention- New status option:
'restart'added toStatusEditParams.status
- External emergency disconnect settings (4 new fields)
antivirusdevice posture check typeos_version_extradocumentation improvements
- New response types:
SubscriptionCreateResponse,SubscriptionUpdateResponse,SubscriptionGetResponse
- New
ApplicationTypevalues:'mcp','mcp_portal','proxy_endpoint' - New destination type:
ViaMcpServerPortalDestinationfor MCP server access
- Added
rules.listTenant()method
ProxyEndpoint: interface → discriminated union (ZeroTrustGatewayProxyEndpointIP | ZeroTrustGatewayProxyEndpointIdentity)ProxyEndpointCreateParams: interface → union type- Added
kindfield:'ip' | 'identity'
WARPConnector*Response: union type → interface
- API Gateway:
UserSchemas,Settings,SchemaValidationresources - Audit Logs:
auditLogId.not(useid.not) - CloudforceOne:
ThreatEvents.get(),IndicatorTypes.list() - Devices:
public_ipfield (use DEX API) - Email Security:
item_countfield in Move responses - Pipelines: v0 methods (use v1)
- Radar: old
summary()andtimeseriesGroups()methods (use V2) - Rulesets:
disable_apps,miragefields - WARP Connector:
connectionsfield - Workers:
environmentparameter in Domains - Zones:
ResponseBufferingpage rule
- mcp: correct code tool API endpoint (599703c ↗)
- mcp: return correct lines on typescript errors (5d6f999 ↗)
- organization_profile: fix bad reference (d84ea77 ↗)
- schema_validation: correctly reflect model to openapi mapping (bb86151 ↗)
- workers: fix tests (2ee37f7 ↗)
In January 2025, we announced the launch of the new Terraform v5 Provider. We greatly appreciate the proactive engagement and valuable feedback from the Cloudflare community following the v5 release. In response, we've established a consistent and rapid 2-3 week cadence ↗ for releasing targeted improvements, demonstrating our commitment to stability and reliability.
With the help of the community, we have a growing number of resources that we have marked as stable ↗, with that list continuing to grow with every release. The most used resources ↗ are on track to be stable by the end of March 2026, when we will also be releasing a new migration tool to you migrate from v4 to v5 with ease.
Thank you for continuing to raise issues. They make our provider stronger and help us build products that reflect your needs.
This release includes bug fixes, the stabilization of even more popular resources, and more.
- custom_pages: add "waf_challenge" as new supported error page type identifier in both resource and data source schemas
- list: enhance CIDR validator to check for normalized CIDR notation requiring network address for IPv4 and IPv6
- magic_wan_gre_tunnel: add automatic_return_routing attribute for automatic routing control
- magic_wan_gre_tunnel: add BGP configuration support with new BGP model attribute
- magic_wan_gre_tunnel: add bgp_status computed attribute for BGP connection status information
- magic_wan_gre_tunnel: enhance schema with BGP-related attributes and validators
- magic_wan_ipsec_tunnel: add automatic_return_routing attribute for automatic routing control
- magic_wan_ipsec_tunnel: add BGP configuration support with new BGP model attribute
- magic_wan_ipsec_tunnel: add bgp_status computed attribute for BGP connection status information
- magic_wan_ipsec_tunnel: add custom_remote_identities attribute for custom identity configuration
- magic_wan_ipsec_tunnel: enhance schema with BGP and identity-related attributes
- ruleset: add request body buffering support
- ruleset: enhance ruleset data source with additional configuration options
- workers_script: add observability logs attributes to list data source model
- workers_script: enhance list data source schema with additional configuration options
- account_member: fix resource importability issues
- dns_record: remove unnecessary fmt.Sprintf wrapper around LoadTestCase call in test configuration helper function
- load_balancer: fix session_affinity_ttl type expectations to match Float64 in initial creation and Int64 after migration
- workers_kv: handle special characters correctly in URL encoding
- account_subscription: update schema description for rate_plan.sets attribute to clarify it returns an array of strings
- api_shield: add resource-level description for API Shield management of auth ID characteristics
- api_shield: enhance auth_id_characteristics.name attribute description to include JWT token configuration format requirements
- api_shield: specify JSONPath expression format for JWT claim locations
- hyperdrive_config: add description attribute to name attribute explaining its purpose in dashboard and API identification
- hyperdrive_config: apply description improvements across resource, data source, and list data source schemas
- hyperdrive_config: improve schema descriptions for cache settings to clarify default values
- hyperdrive_config: update port description to clarify defaults for different database types