Data Loss Prevention
DLP account-level settings
Account-level DLP settings are now available in Cloudflare One. You can now configure advanced DLP settings at the account level, including OCR, AI context analysis, and payload masking. This provides consistent enforcement across all DLP profiles and simplifies configuration management.
Key changes:
- Consistent enforcement: Settings configured at the account level apply to all DLP profiles
- Simplified migration: Settings enabled on any profile are automatically migrated to account level
- Deprecation notice: Profile-level advanced settings will be deprecated in a future release
Migration details:
During the migration period, if a setting is enabled on any profile, it will automatically be enabled at the account level. This means profiles that previously had a setting disabled may now have it enabled if another profile in the account had it enabled.
Settings are evaluated using OR logic - a setting is enabled if it is turned on at either the account level or the profile level. However, profile-level settings cannot be enabled when the account-level setting is off.
For more details, refer to the DLP advanced settings documentation.
Detect Cloudflare API tokens with DLP
The Credentials and Secrets DLP profile now includes three new predefined entries for detecting Cloudflare API credentials:
| Entry name | Token prefix | Detects |
|---|---|---|
| Cloudflare User API Key | cfk_ | User-scoped API keys |
| Cloudflare User API Token | cfut_ | User-scoped API tokens |
| Cloudflare Account Owned API Token | cfat_ | Account-scoped API tokens |
These detections target the new Cloudflare API credential format, which uses a structured prefix and a CRC32 checksum suffix. The identifiable prefix makes it possible to detect leaked credentials with high confidence and low false positive rates — no surrounding context such as Authorization: Bearer headers is required.
Credentials generated before this format change will not be matched by these entries.
- In the Cloudflare dashboard ↗, go to Zero Trust > DLP > DLP Profiles.
- Select the Credentials and Secrets profile.
- Turn on one or more of the new Cloudflare API token entries.
- Use the profile in a Gateway HTTP policy to log or block traffic containing these credentials.
Example policy:
| Selector | Operator | Value | Action |
|---|---|---|---|
| DLP Profile | in | Credentials and Secrets | Block |
You can also enable individual entries to scope detection to specific credential types — for example, enabling Account Owned API Token detection without enabling User API Key detection.
For more information, refer to predefined DLP profiles.
Configure how sensitive data appears in DLP payload logs
You can now configure how sensitive data matches are displayed in your DLP payload match logs — giving your incident response team the context they need to validate alerts without compromising your security posture.
To get started, go to the Cloudflare dashboard ↗, select Zero Trust > Data loss prevention > DLP settings and find the Payload log masking card.
Previously, all DLP payload logs used a single masking mode that obscured matched data entirely and hid the original character count, making it difficult to distinguish true positives from false positives. This update introduces three options:
- Full Mask (default): Masks the match while preserving character count and visual formatting (for example,
***-**-****for a Social Security Number). This is an improvement over the previous default, which did not preserve character count. - Partial Mask: Reveals 25% of the matched content while masking the remainder (for example,
***-**-6789). - Clear Text: Stores the full, unmasked violation for deep investigation (for example,
123-45-6789).
Important: The masking level you select is applied at detection time, before the payload is encrypted. This means the chosen format is what your team will see after decrypting the log with your private key — the existing encryption workflow is unchanged.
Applies to all enabled detections: When a masking level other than Full Mask is selected, it applies to all sensitive data matches found within a payload window — not just the match that triggered the policy. Any data matched by your enabled DLP detection entries will be masked at the selected level.
For more information, refer to DLP logging options.
Streaming ZIP file scanning removes per-file size limits
DLP now processes ZIP files using a streaming handler that scans archive contents element-by-element as data arrives. This removes previous file size limitations and improves memory efficiency when scanning large archives.
Microsoft Office documents (DOCX, XLSX, PPTX) also benefit from this improvement, as they use ZIP as a container format.
This improvement is automatic — no configuration changes are required.
Detect and sanitize HAR files
HTTP Archive (HAR) files are used by engineering and support teams to capture and share web traffic logs for troubleshooting. However, these files routinely contain highly sensitive data — including session cookies, authorization headers, and other credentials — that can pose a significant risk if uploaded to third-party services without being reviewed or cleaned first.
Gateway now includes a predefined DLP profile called Unsanitized HAR that detects HAR files in HTTP traffic. You can use this profile in a Gateway HTTP policy to either block HAR file uploads entirely or redirect users to a sanitization tool before allowing the upload to proceed.
In the Cloudflare dashboard ↗, go to Zero Trust > Traffic policies > Firewall Policies > HTTP and create a new HTTP policy using the DLP Profile selector:
| Selector | Operator | Value | Action |
|---|---|---|---|
| DLP Profile | in | Unsanitized HAR |
Then choose one of the following actions:
- Block: Prevents the upload of any HAR file that has not been sanitized by Cloudflare's sanitizer. Use this for strict environments where HAR file sharing must be disallowed entirely.
- Block with Gateway Redirect: Intercepts the upload and redirects the user to
https://har-sanitizer.pages.dev/, where they can sanitize the file. Once sanitized, the user can re-upload the clean file and proceed with their workflow.
HAR files processed by the Cloudflare HAR sanitizer receive a tamper-evident sanitized marker. DLP recognizes this marker and will not re-trigger the policy on a file that has already been sanitized and has not been modified since. If a previously sanitized file is edited, it will be treated as unsanitized and flagged again.
Gateway logs will reflect whether a detected HAR file was classified as Unsanitized or Sanitized, giving your security team full visibility into HAR file activity across your organization.
For more information, refer to predefined DLP profiles.
Expanded File Type Controls for Executables and Disk Images
You can now enhance your security posture by blocking additional application installer and disk image file types with Cloudflare Gateway. Preventing the download of unauthorized software packages is a critical step in securing endpoints from malware and unwanted applications.
We have expanded Gateway's file type controls to include:
- Apple Disk Image (dmg)
- Microsoft Software Installer (msix, appx)
- Apple Software Package (pkg)
You can find these new options within the Upload File Types and Download File Types selectors when creating or editing an HTTP policy. The file types are categorized as follows:
- System: Apple Disk Image (dmg)
- Executable: Microsoft Software Installer (msix), Microsoft Software Installer (appx), Apple Software Package (pkg)
To ensure these file types are blocked effectively, please note the following behaviors:
- DMG: Due to their file structure, DMG files are blocked at the very end of the transfer. A user's download may appear to progress but will fail at the last moment, preventing the browser from saving the file.
- MSIX: To comprehensively block Microsoft Software Installers, you should also include the file type Unscannable. MSIX files larger than 100 MB are identified as Unscannable ZIP files during inspection.
To get started, go to your HTTP policies in Zero Trust. For a full list of file types, refer to supported file types.
Refine DLP Scans with New Body Phase Selector
You can now more precisely control your HTTP DLP policies by specifying whether to scan the request or response body, helping to reduce false positives and target specific data flows.
In the Gateway HTTP policy builder, you will find a new selector called Body Phase. This allows you to define the direction of traffic the DLP engine will inspect:
- Request Body: Scans data sent from a user's machine to an upstream service. This is ideal for monitoring data uploads, form submissions, or other user-initiated data exfiltration attempts.
- Response Body: Scans data sent to a user's machine from an upstream service. Use this to inspect file downloads and website content for sensitive data.
For example, consider a policy that blocks Social Security Numbers (SSNs). Previously, this policy might trigger when a user visits a website that contains example SSNs in its content (the response body). Now, by setting the Body Phase to Request Body, the policy will only trigger if the user attempts to upload or submit an SSN, ignoring the content of the web page itself.
All policies without this selector will continue to scan both request and response bodies to ensure continued protection.
For more information, refer to Gateway HTTP policy selectors.
New DLP topic based detection entries for AI prompt protection
You now have access to a comprehensive suite of capabilities to secure your organization's use of generative AI. AI prompt protection introduces four key features that work together to provide deep visibility and granular control.
- Prompt Detection for AI Applications
DLP can now natively detect and inspect user prompts submitted to popular AI applications, including Google Gemini, ChatGPT, Claude, and Perplexity.
- Prompt Analysis and Topic Classification
Our DLP engine performs deep analysis on each prompt, applying topic classification. These topics are grouped into two evaluation categories:
-
Content: PII, Source Code, Credentials and Secrets, Financial Information, and Customer Data.
-
Intent: Jailbreak attempts, requests for malicious code, or attempts to extract PII.
To help you apply these topics quickly, we have also released five new predefined profiles (for example, AI Prompt: AI Security, AI Prompt: PII) that bundle these new topics.
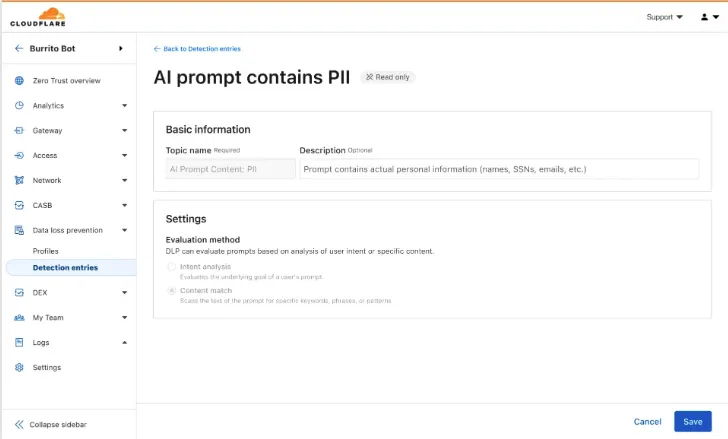
-
Granular Guardrails
You can now build guardrails using Gateway HTTP policies with application granular controls. Apply a DLP profile containing an AI prompt topic detection to individual AI applications (for example,
ChatGPT) and specific user actions (for example,SendPrompt) to block sensitive prompts.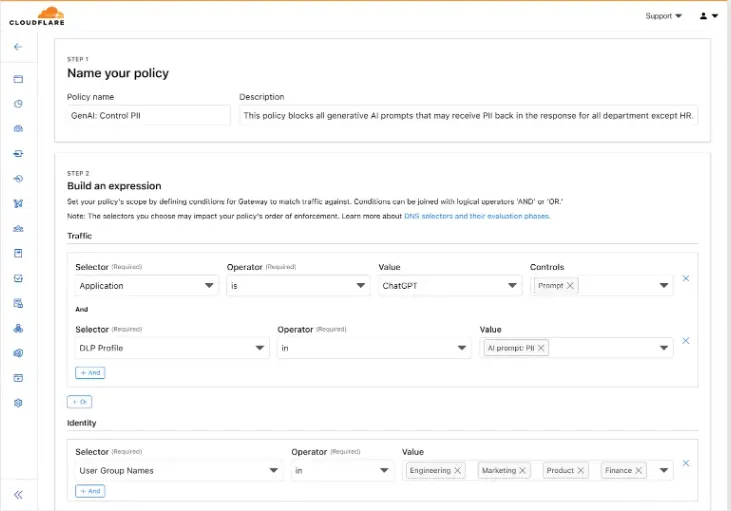
-
Full Prompt Logging
To aid in incident investigation, an optional setting in your Gateway policy allows you to capture prompt logs to store the full interaction of prompts that trigger a policy match. To make investigations easier, logs can be filtered by
conversation_id, allowing you to reconstruct the full context of an interaction that led to a policy violation.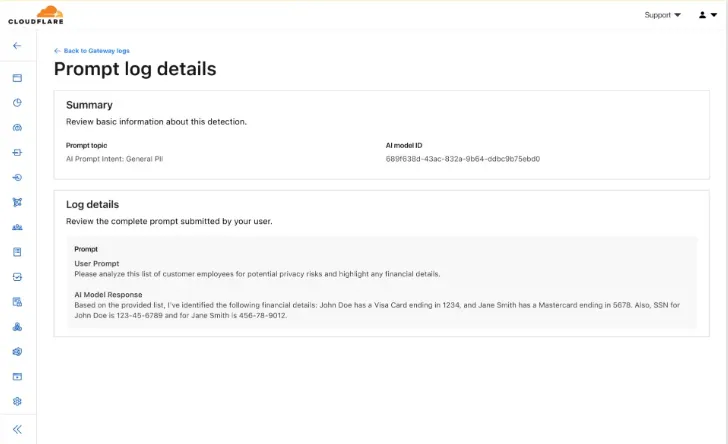
AI prompt protection is now available in open beta. To learn more about it, read the blog ↗ or refer to AI prompt topics.
New detection entry type: Document Matching for DLP
You can now create document-based detection entries in DLP by uploading example documents. Cloudflare will encrypt your documents and create a unique fingerprint of the file. This fingerprint is then used to identify similar documents or snippets within your organization's traffic and stored files.
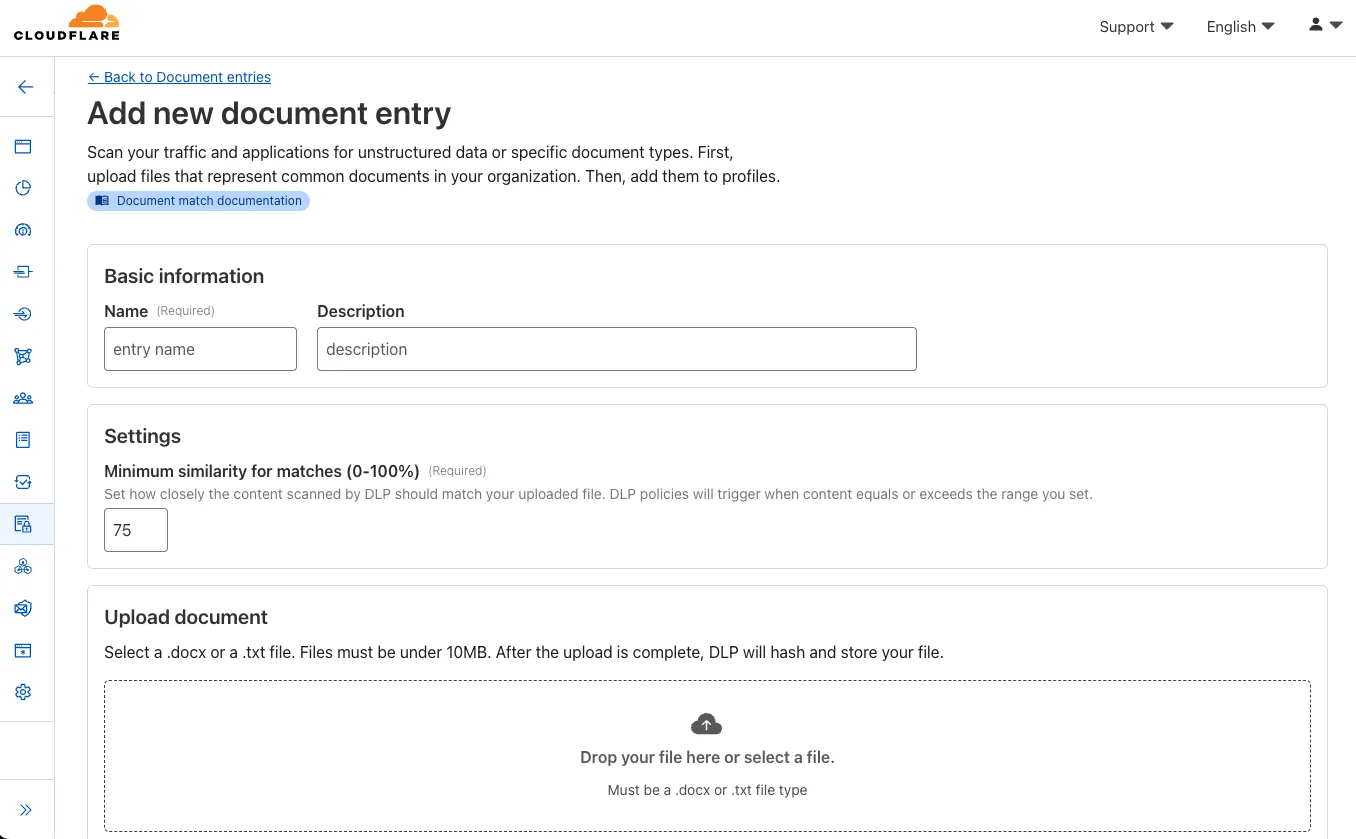
Key features and benefits:
-
Upload documents, forms, or templates: Easily upload .docx and .txt files (up to 10 MB) that contain sensitive information you want to protect.
-
Granular control with similarity percentage: Define a minimum similarity percentage (0-100%) that a document must meet to trigger a detection, reducing false positives.
-
Comprehensive coverage: Apply these document-based detection entries in:
-
Gateway policies: To inspect network traffic for sensitive documents as they are uploaded or shared.
-
CASB (Cloud Access Security Broker): To scan files stored in cloud applications for sensitive documents at rest.
-
-
Identify sensitive data: This new detection entry type is ideal for identifying sensitive data within completed forms, templates, or even small snippets of a larger document, helping you prevent data exfiltration and ensure compliance.
Once uploaded and processed, you can add this new document entry into a DLP profile and policies to enhance your data protection strategy.
Data Security Analytics in the Zero Trust dashboard
Zero Trust now includes Data security analytics, providing you with unprecedented visibility into your organization sensitive data.
The new dashboard includes:
-
Sensitive Data Movement Over Time:
- See patterns and trends in how sensitive data moves across your environment. This helps understand where data is flowing and identify common paths.
-
Sensitive Data at Rest in SaaS & Cloud:
- View an inventory of sensitive data stored within your corporate SaaS applications (for example, Google Drive, Microsoft 365) and cloud accounts (such as AWS S3).
-
DLP Policy Activity:
- Identify which of your Data Loss Prevention (DLP) policies are being triggered most often.
- See which specific users are responsible for triggering DLP policies.
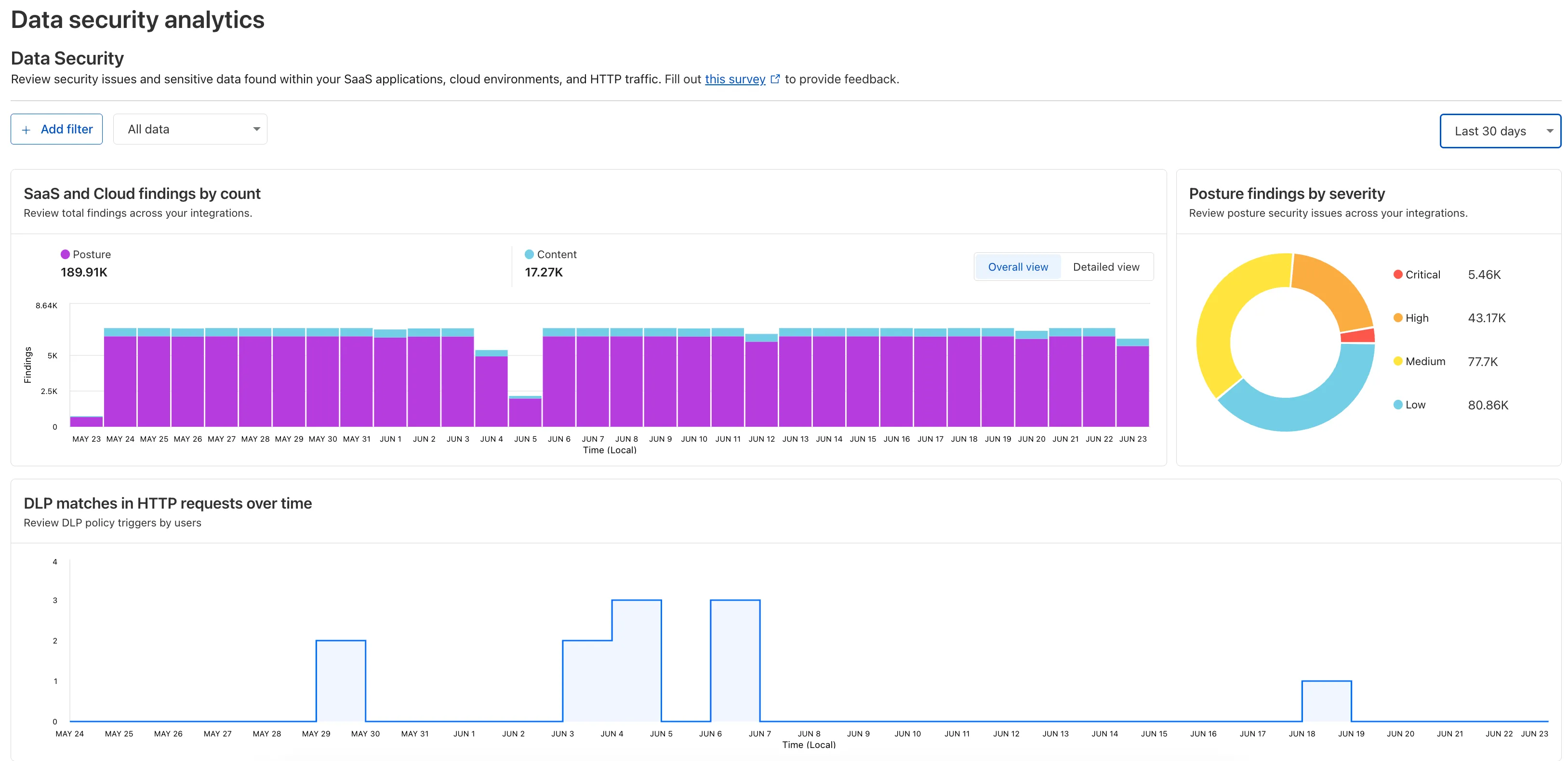
To access the new dashboard, log in to Cloudflare One ↗ and go to Insights on the sidebar.
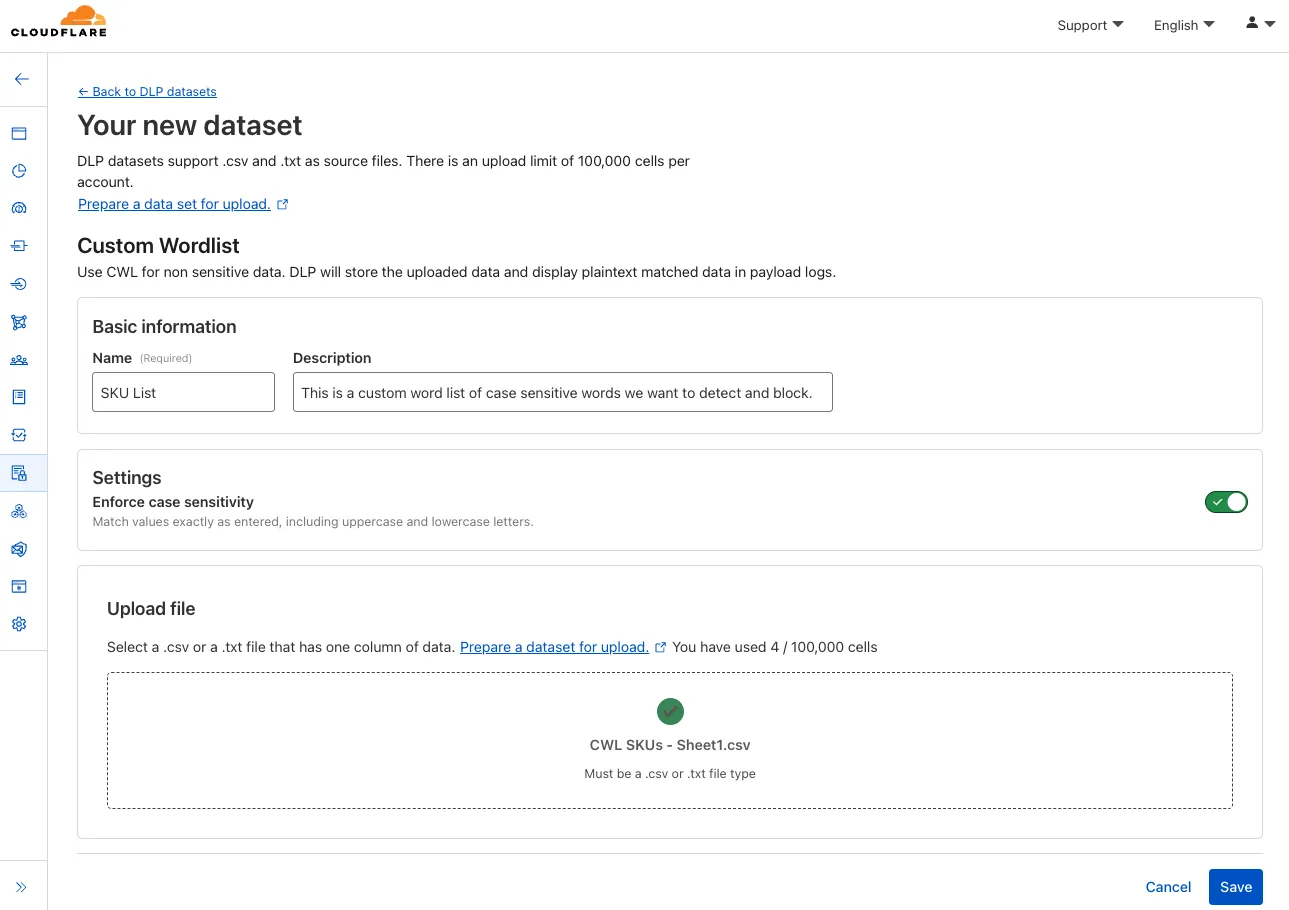
Case Sensitive Custom Word Lists
You can now configure custom word lists to enforce case sensitivity. This setting supports flexibility where needed and aims to reduce false positives where letter casing is critical.
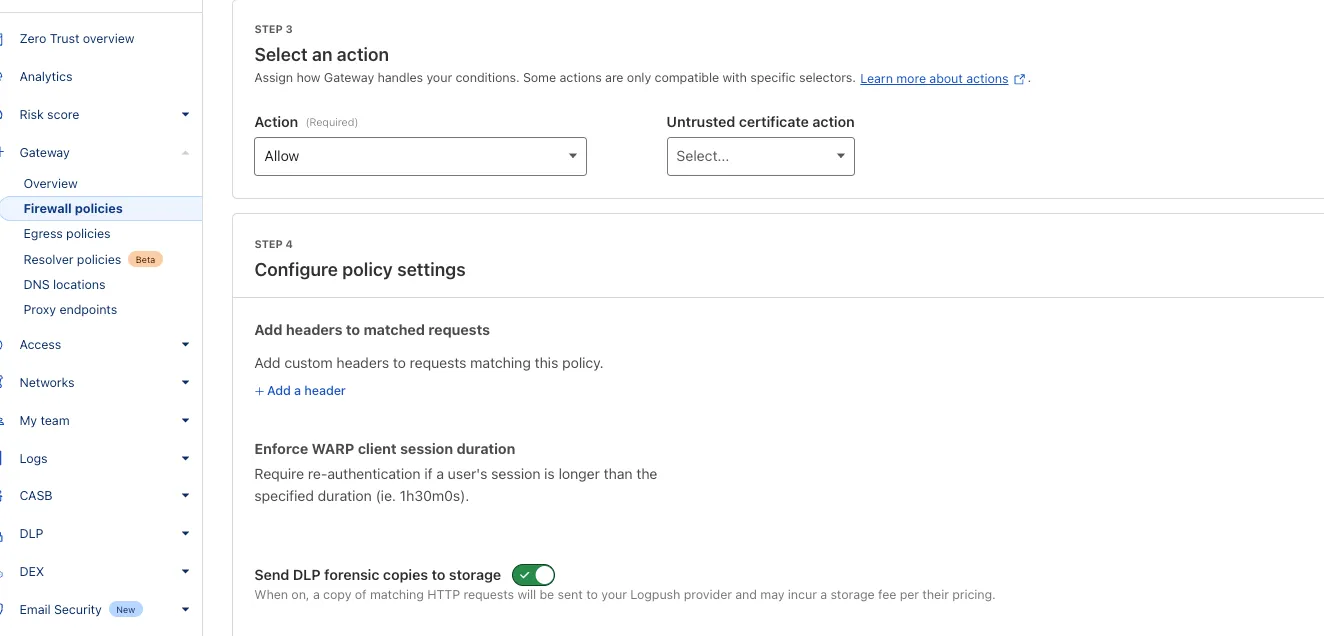
Send forensic copies to storage without DLP profiles
You can now send DLP forensic copies to third-party storage for any HTTP policy with an Allow or Block action, without needing to include a DLP profile. This change increases flexibility for data handling and forensic investigation use cases.
By default, Gateway will send all matched HTTP requests to your configured DLP Forensic Copy jobs.
New predefined detection entry for ICD-11
You now have access to the World Health Organization (WHO) 2025 edition of the International Classification of Diseases 11th Revision (ICD-11) ↗ as a predefined detection entry. The new dataset can be found in the Health Information predefined profile.
ICD-10 dataset remains available for use.
Block files that are password-protected, compressed, or otherwise unscannable.
Gateway HTTP policies can now block files that are password-protected, compressed, or otherwise unscannable.
These unscannable files are now matched with the Download and Upload File Types traffic selectors for HTTP policies:
- Password-protected Microsoft Office document
- Password-protected PDF
- Password-protected ZIP archive
- Unscannable ZIP archive
To get started inspecting and modifying behavior based on these and other rules, refer to HTTP filtering.
Detect source code leaks with Data Loss Prevention
You can now detect source code leaks with Data Loss Prevention (DLP) with predefined checks against common programming languages.
The following programming languages are validated with natural language processing (NLP).
- C
- C++
- C#
- Go
- Haskell
- Java
- JavaScript
- Lua
- Python
- R
- Rust
- Swift
DLP also supports confidence level for source code profiles.
For more details, refer to DLP profiles.
Payload log match visibility
When viewing decrypted payload log matches, DLP now provides more context by listing multiple DLP matches and the matching DLP profile.
Profile confidence levels
DLP profiles now support setting a confidence level to choose how tolerant its detections are to false positives based on the context of the detection. The higher a profile's confidence level is, the less false positives will be allowed. Confidence levels include Low, Medium, or High. DLP profile confidence levels supersede context analysis.
Send entire HTTP requests to a Logpush destination
In addition to logging the payload from HTTP requests that matched a DLP policy in Cloudflare Logs, Enterprise users can now configure a Logpush job to send the entire HTTP request that triggered a DLP match to a storage destination. This allows long-term storage of full requests for use in forensic investigation.
Exact Data Match multi-entry upload support
You can now upload files with multiple columns of data as Exact Data Match datasets. DLP can use each column as a separate existing detection entry.
Data-at-rest DLP for Box and Dropbox
You can now scan your Box and Dropbox files for DLP matches.
Optical character recognition
DLP can now detect sensitive data in jpeg, jpg, and png files. This helps companies prevent the leak of sensitive data in images, such as screenshots.