Access
User risk score selector in Access policies
You can now use user risk scores in your Access policies. The new User Risk Score selector allows you to create Access policies that respond to user behavior patterns detected by Cloudflare's risk scoring system, including impossible travel, high DLP policy matches, and more.
For more information, refer to Use risk scores in Access policies.
Clipboard controls for browser-based RDP
You can now configure clipboard controls for browser-based RDP with Cloudflare Access. Clipboard controls allow administrators to restrict whether users can copy or paste text between their local machine and the remote Windows server.
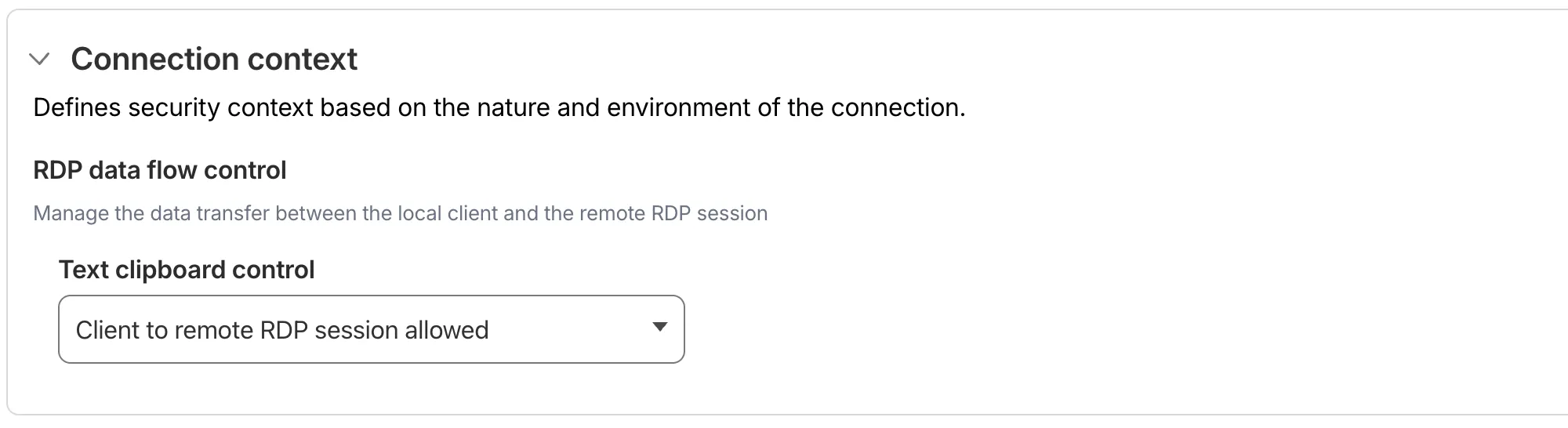
This feature is useful for organizations that support bring-your-own-device (BYOD) policies or third-party contractors using unmanaged devices. By restricting clipboard access, you can prevent sensitive data from being transferred out of the remote session to a user's personal device.
Clipboard controls are configured per policy within your Access application. For each policy, you can independently allow or deny:
- Copy from local client to remote RDP session — Users can copy/paste text from their local machine into the browser-based RDP session.
- Copy from remote RDP session to local client — Users can copy/paste text from the browser-based RDP session to their local machine.
By default, both directions are denied for new policies. For existing Access applications created before this feature was available, clipboard access remains enabled to preserve backwards compatibility.
When a user attempts a restricted clipboard action, the clipboard content is replaced with an error message informing them that the action is not allowed.
For more information, refer to Clipboard controls for browser-based RDP.
Export MCP server portal logs with Logpush
MCP server portals now supports Logpush integration. You can automatically export MCP server portal activity logs to third-party storage destinations or security information and event management (SIEM) tools for analysis and auditing.
The MCP server portal logs dataset includes fields such as:
Datetime— Timestamp of the requestPortalID/PortalAUD— Portal identifiersServerID/ServerURL— Upstream MCP server detailsMethod— JSON-RPC method (for example,tools/call,prompts/get,resources/read)ToolCallName/PromptGetName/ResourceReadURI— Method-specific identifiersUserID/UserEmail— Authenticated user informationSuccess/Error— Request outcomeServerResponseDurationMs— Response time from upstream server
For the complete field reference, refer to MCP portal logs.
To configure Logpush for MCP server portal logs, refer to Logpush integration.
Streamlined clientless browser isolation for private applications
A new Allow clientless access setting makes it easier to connect users without a device client to internal applications, without using public DNS.
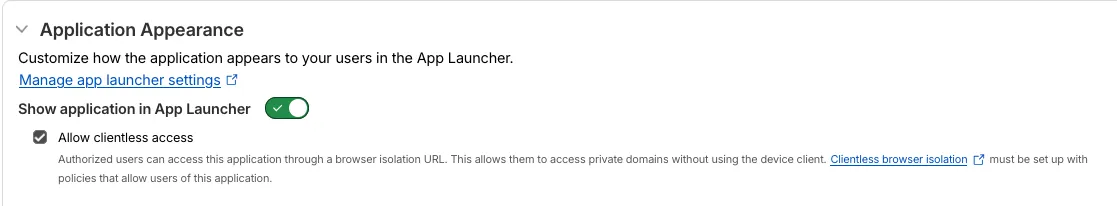
Previously, to provide clientless access to a private hostname or IP without a published application, you had to create a separate bookmark application pointing to a prefixed Clientless Web Isolation URL (for example, https://<your-teamname>.cloudflareaccess.com/browser/https://10.0.0.1/). This bookmark was visible to all users in the App Launcher, regardless of whether they had access to the underlying application.
Now, you can manage clientless access directly within your private self-hosted application. When Allow clientless access is turned on, users who pass your Access application policies will see a tile in their App Launcher pointing to the prefixed URL. Users must have remote browser permissions to open the link.
Policies for bookmark applications
You can now assign Access policies to bookmark applications. This lets you control which users see a bookmark in the App Launcher based on identity, device posture, and other policy rules.
Previously, bookmark applications were visible to all users in your organization. With policy support, you can now:
- Tailor the App Launcher to each user — Users only see the applications they have access to, reducing clutter and preventing accidental clicks on irrelevant resources.
- Restrict visibility of sensitive bookmarks — Limit who can view bookmarks to internal tools or partner resources based on group membership, identity provider, or device posture.
Bookmarks support all Access policy configurations except purpose justification, temporary authentication, and application isolation. If no policy is assigned, the bookmark remains visible to all users (maintaining backwards compatibility).
For more information, refer to Add bookmarks.
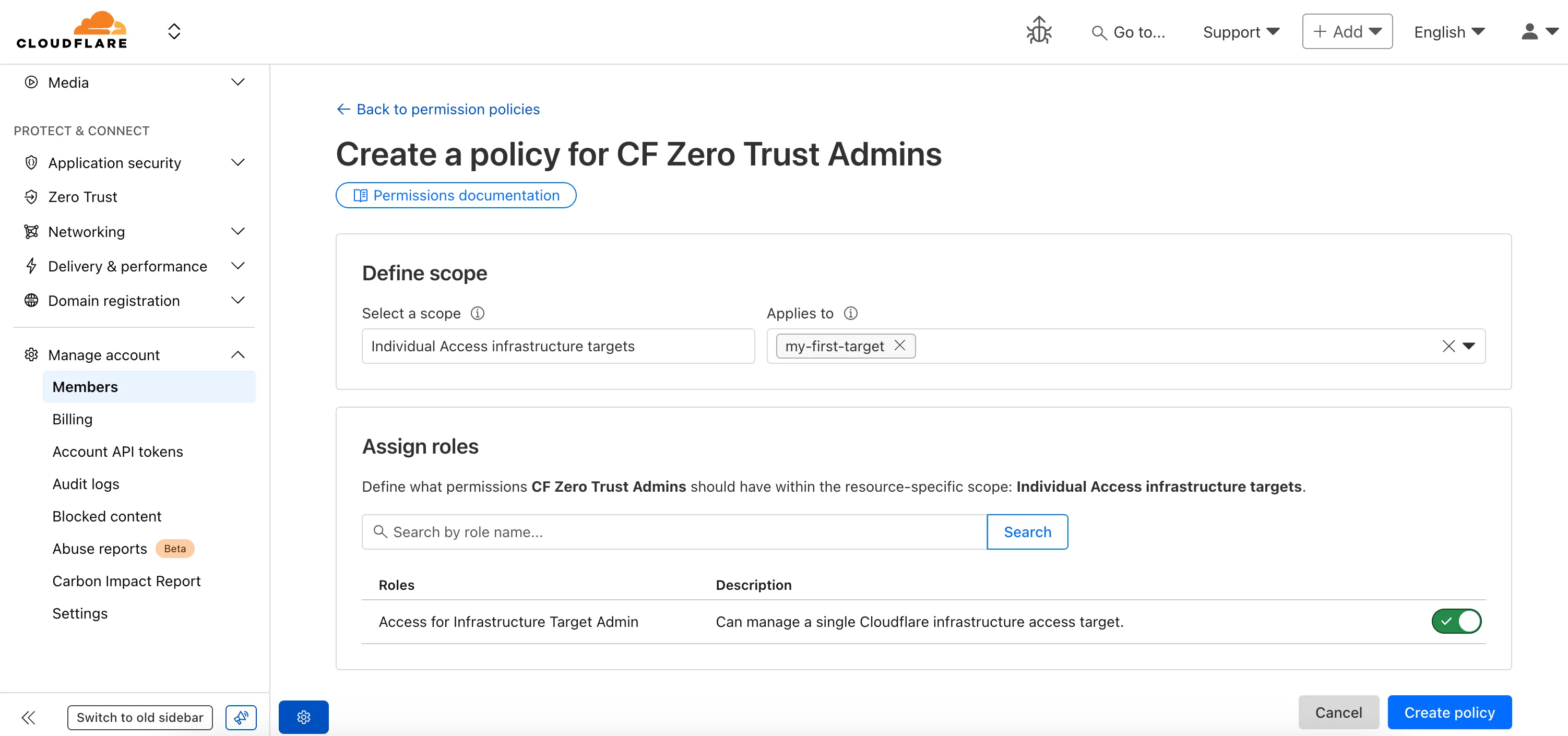
Fine-grained permissions for Access policies and service tokens
Fine-grained permissions for Access policies and Access service tokens are available. These new resource-scoped roles expand the existing RBAC model, enabling administrators to grant permissions scoped to individual resources.
- Cloudflare Access policy admin: Can edit a specific Access policy in an account.
- Cloudflare Access service token admin: Can edit a specific Access service token in an account.
These roles complement the existing resource-scoped roles for Access applications, identity providers, and infrastructure targets.
For more information:
Require Access protection for zones
You can now require Cloudflare Access protection for all hostnames in your account. When enabled, traffic to any hostname that does not have a matching Access application is automatically blocked.
This deny-by-default approach prevents accidental exposure of internal resources to the public Internet. If a developer deploys a new application or creates a DNS record without configuring an Access application, the traffic is blocked rather than exposed.
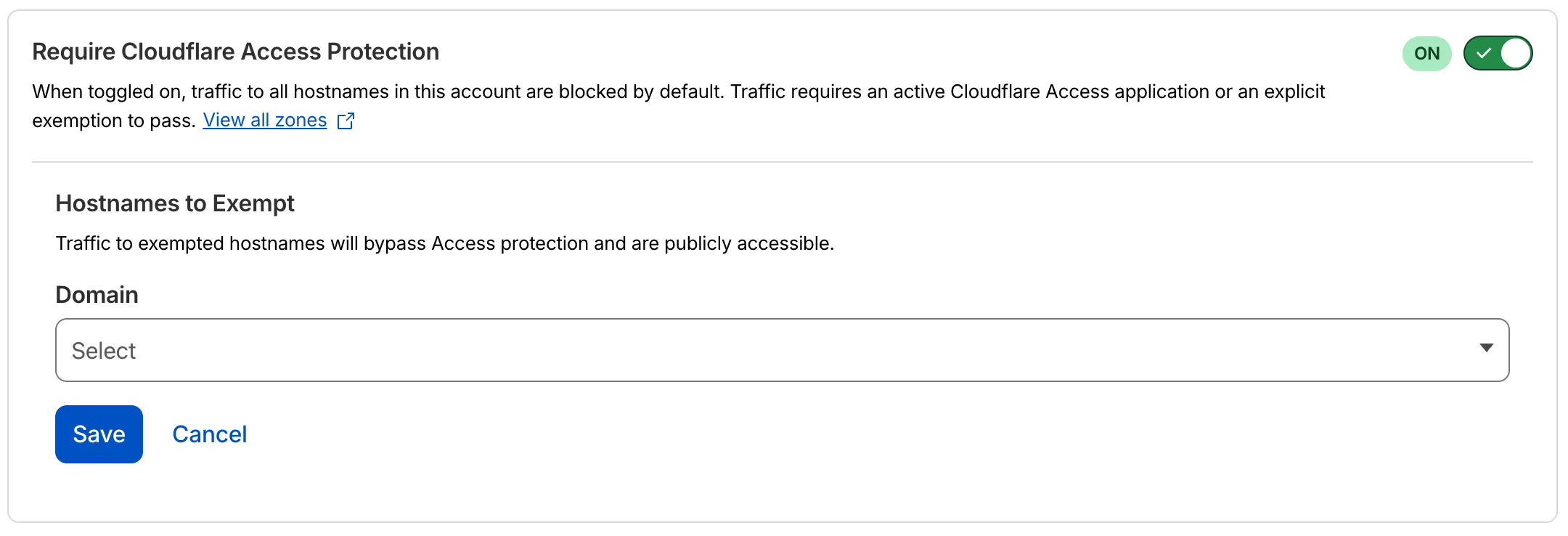
- Blocked by default: Traffic to all hostnames in the account is blocked unless an Access application exists for that hostname.
- Explicit access required: To allow traffic, create an Access application with an Allow or Bypass policy.
- Hostname exemptions: You can exempt specific hostnames from this requirement.
To turn on this feature, refer to Require Access protection.
Cloudflare admin activity logs capture creation of DNS over HTTP (DoH) users
Cloudflare admin activity logs now capture each time a DNS over HTTP (DoH) user is created.
These logs can be viewed from the Cloudflare One dashboard ↗, pulled via the Cloudflare API, and exported through Logpush.
Generate Cloudflare Access SSH certificate authority (CA) directly from the Cloudflare dashboard
SSH with Cloudflare Access for Infrastructure allows you to use short-lived SSH certificates to eliminate SSH key management and reduce security risks associated with lost or stolen keys.
Previously, users had to generate this certificate by using the Cloudflare API ↗ directly. With this update, you can now create and manage this certificate in the Cloudflare One dashboard ↗ from the Access controls > Service credentials page.
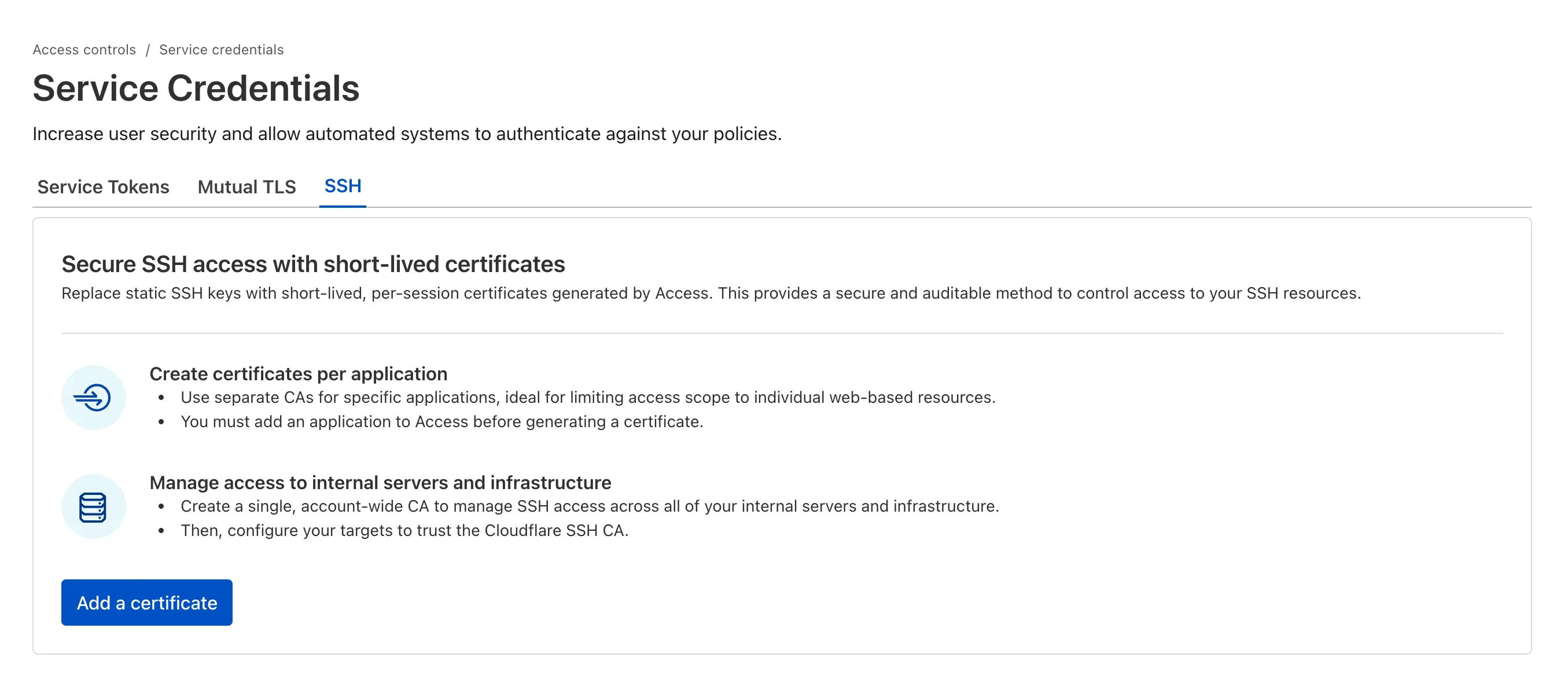
For more details, refer to Generate a Cloudflare SSH CA.
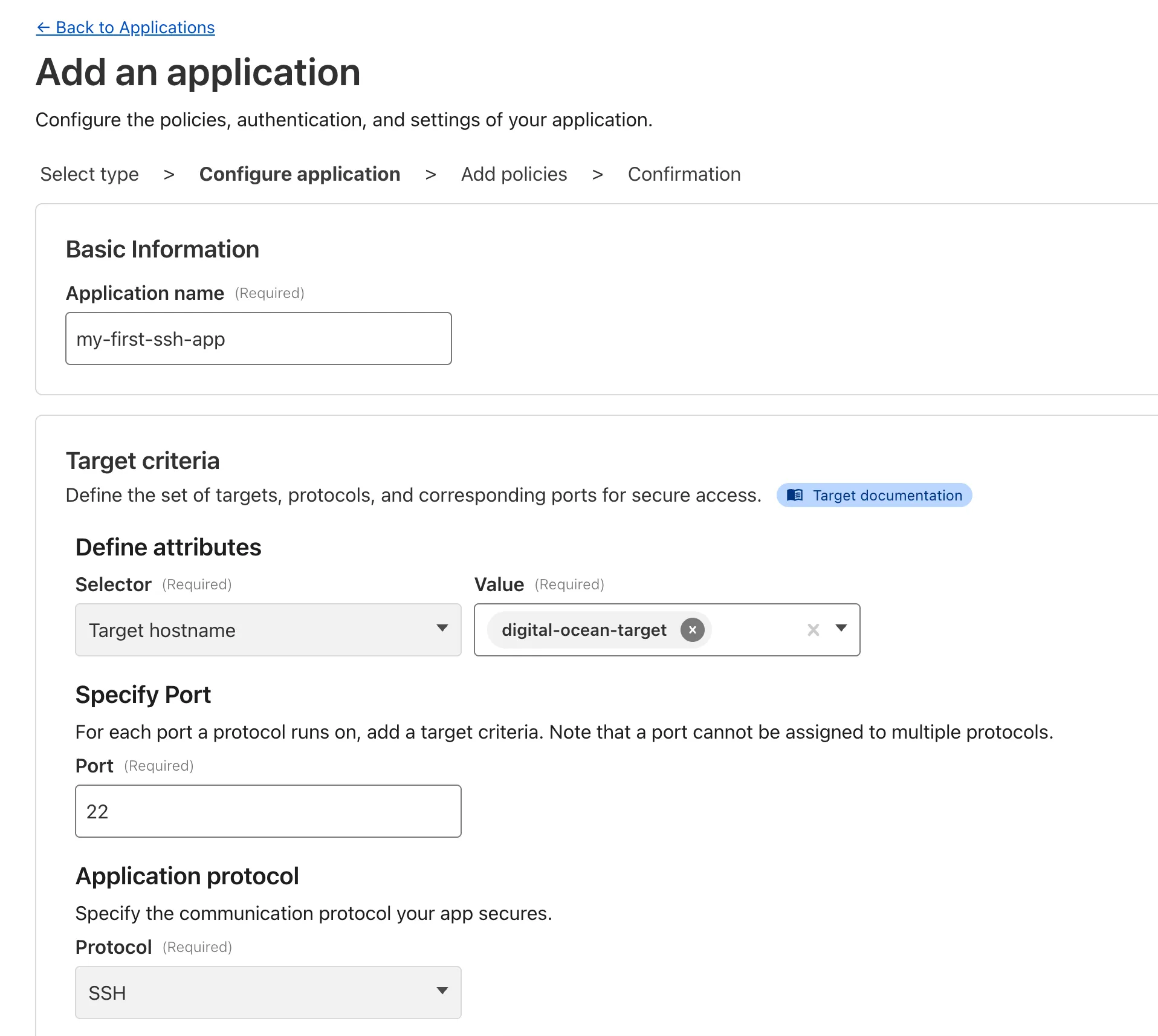
Access private hostname applications support all ports/protocols
Cloudflare Access for private hostname applications can now secure traffic on all ports and protocols.
Previously, applying Zero Trust policies to private applications required the application to use HTTPS on port 443 and support Server Name Indicator (SNI).
This update removes that limitation. As long as the application is reachable via a Cloudflare off-ramp, you can now enforce your critical security controls — like single sign-on (SSO), MFA, device posture, and variable session lengths — to any private application. This allows you to extend Zero Trust security to services like SSH, RDP, internal databases, and other non-HTTPS applications.
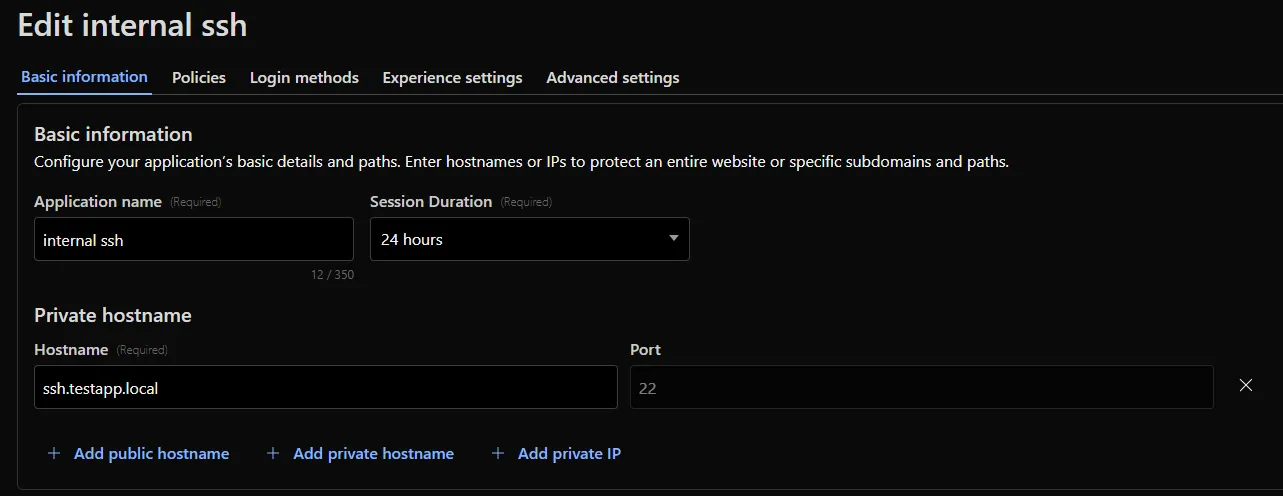
For example, you can now create a self-hosted application in Access for ssh.testapp.local running on port 22. You can then build a policy that only allows engineers in your organization to connect after they pass an SSO/MFA check and are using a corporate device.
This feature is generally available across all plans.
Fine-grained Permissioning for Access for Apps, IdPs, & Targets now in Public Beta
Fine-grained permissions for Access Applications, Identity Providers (IdPs), and Targets is now available in Public Beta. This expands our RBAC model beyond account & zone-scoped roles, enabling administrators to grant permissions scoped to individual resources.
- Access Applications ↗: Grant admin permissions to specific Access Applications.
- Identity Providers ↗: Grant admin permissions to individual Identity Providers.
- Targets ↗: Grant admin rights to specific Targets
For more info:
Access Remote Desktop Protocol (RDP) destinations securely from your browser — now generally available!
Browser-based RDP with Cloudflare Access is now generally available for all Cloudflare customers. It enables secure, remote Windows server access without VPNs or RDP clients.
Since we announced our open beta, we've made a few improvements:
- Support for targets with IPv6.
- Support for Magic WAN and WARP Connector as on-ramps.
- More robust error messaging on the login page to help you if you encounter an issue.
- Worldwide keyboard support. Whether your day-to-day is in Portuguese, Chinese, or something in between, your browser-based RDP experience will look and feel exactly like you are using a desktop RDP client.
- Cleaned up some other miscellaneous issues, including but not limited to enhanced support for Entra ID accounts and support for usernames with spaces, quotes, and special characters.
As a refresher, here are some benefits browser-based RDP provides:
- Control how users authenticate to internal RDP resources with single sign-on (SSO), multi-factor authentication (MFA), and granular access policies.
- Record who is accessing which servers and when to support regulatory compliance requirements and to gain greater visibility in the event of a security event.
- Eliminate the need to install and manage software on user devices. You will only need a web browser.
- Reduce your attack surface by keeping your RDP servers off the public Internet and protecting them from common threats like credential stuffing or brute-force attacks.
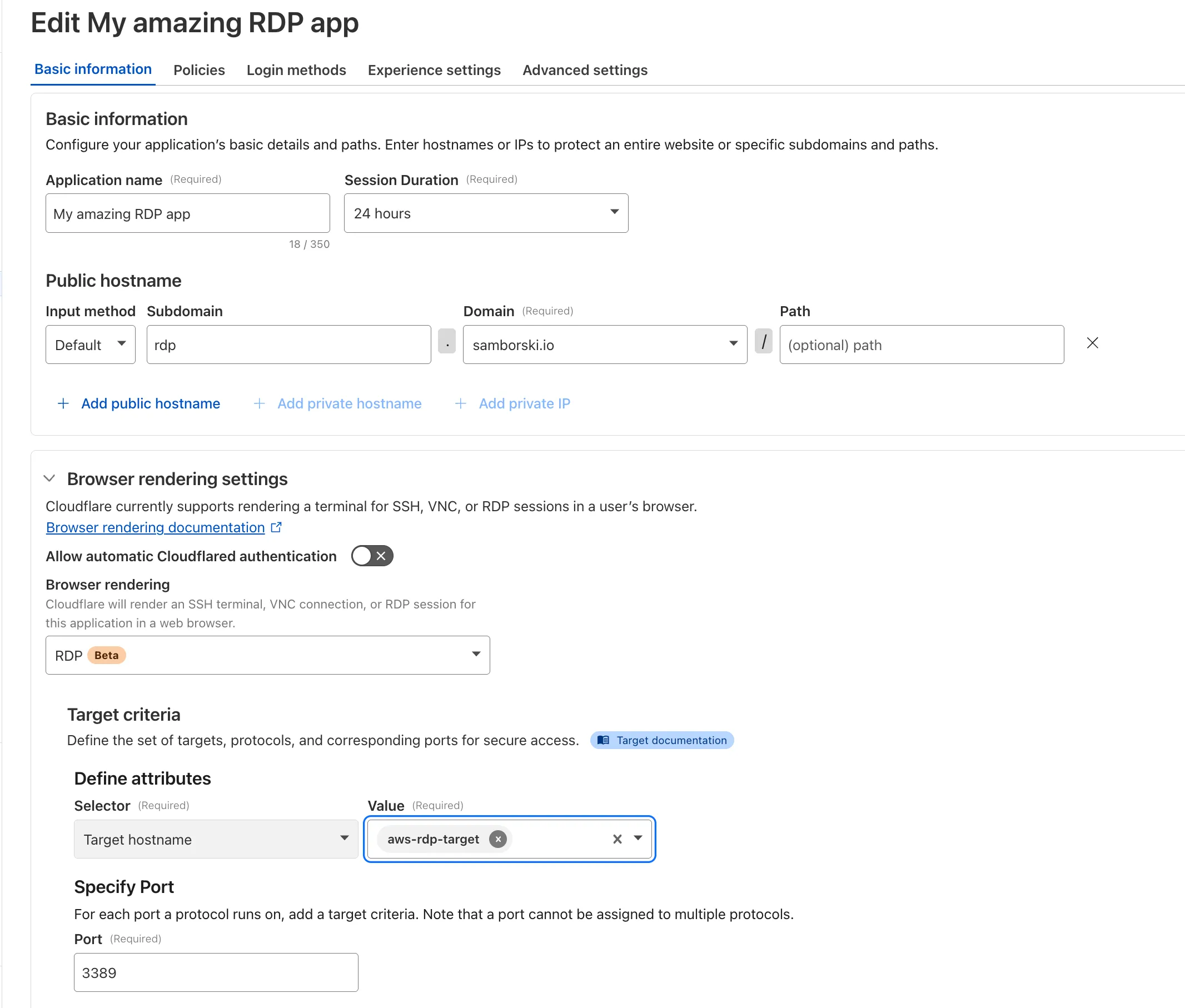
To get started, refer to Connect to RDP in a browser.
Manage and restrict access to internal MCP servers with Cloudflare Access
You can now control who within your organization has access to internal MCP servers, by putting internal MCP servers behind Cloudflare Access.
Self-hosted applications in Cloudflare Access now support OAuth for MCP server authentication. This allows Cloudflare to delegate access from any self-hosted application to an MCP server via OAuth. The OAuth access token authorizes the MCP server to make requests to your self-hosted applications on behalf of the authorized user, using that user's specific permissions and scopes.
For example, if you have an MCP server designed for internal use within your organization, you can configure Access policies to ensure that only authorized users can access it, regardless of which MCP client they use. Support for internal, self-hosted MCP servers also works with MCP server portals, allowing you to provide a single MCP endpoint for multiple MCP servers. For more on MCP server portals, read the blog post ↗ on the Cloudflare Blog.
MCP server portals
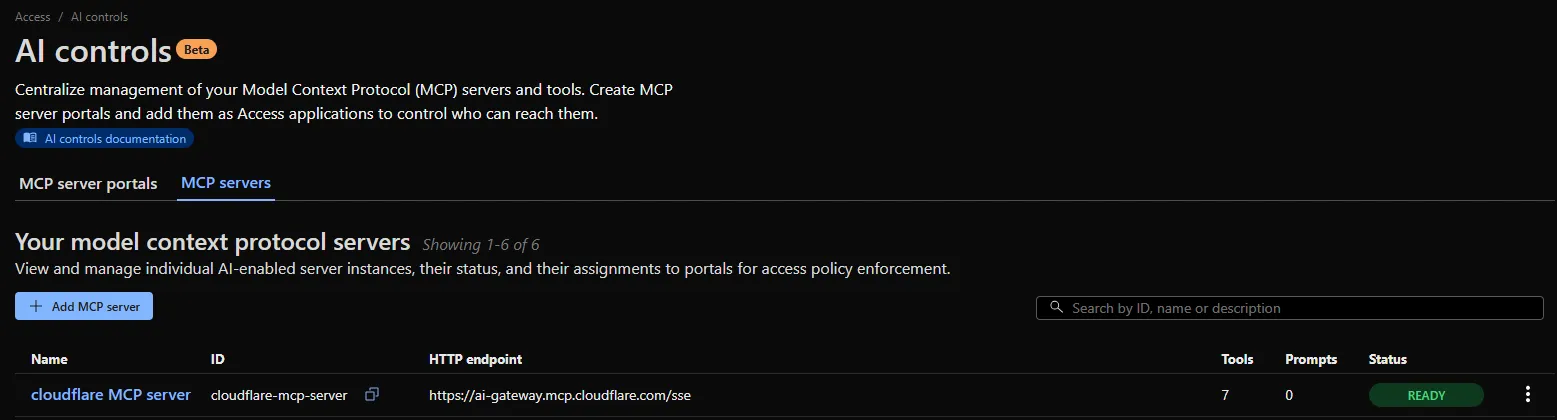
An MCP server portal centralizes multiple Model Context Protocol (MCP) servers onto a single HTTP endpoint. Key benefits include:
- Streamlined access to multiple MCP servers: MCP server portals support both unauthenticated MCP servers as well as MCP servers secured using any third-party or custom OAuth provider. Users log in to the portal URL through Cloudflare Access and are prompted to authenticate separately to each server that requires OAuth.
- Customized tools per portal: Admins can tailor an MCP portal to a particular use case by choosing the specific tools and prompt templates that they want to make available to users through the portal. This allows users to access a curated set of tools and prompts — the less external context exposed to the AI model, the better the AI responses tend to be.
- Observability: Once the user's AI agent is connected to the portal, Cloudflare Access logs the indiviudal requests made using the tools in the portal.
This is available in an open beta for all customers across all plans! For more information check out our blog ↗ for this release.
SFTP support for SSH with Cloudflare Access for Infrastructure
SSH with Cloudflare Access for Infrastructure now supports SFTP. It is compatible with SFTP clients, such as Cyberduck.
Cloudflare Access Logging supports the Customer Metadata Boundary (CMB)
Cloudflare Access logs now support the Customer Metadata Boundary (CMB). If you have configured the CMB for your account, all Access logging will respect that configuration.
Access RDP securely from your browser — now in open beta
Browser-based RDP with Cloudflare Access is now available in open beta for all Cloudflare customers. It enables secure, remote Windows server access without VPNs or RDP clients.
With browser-based RDP, you can:
- Control how users authenticate to internal RDP resources with single sign-on (SSO), multi-factor authentication (MFA), and granular access policies.
- Record who is accessing which servers and when to support regulatory compliance requirements and to gain greater visibility in the event of a security event.
- Eliminate the need to install and manage software on user devices. You will only need a web browser.
- Reduce your attack surface by keeping your RDP servers off the public Internet and protecting them from common threats like credential stuffing or brute-force attacks.
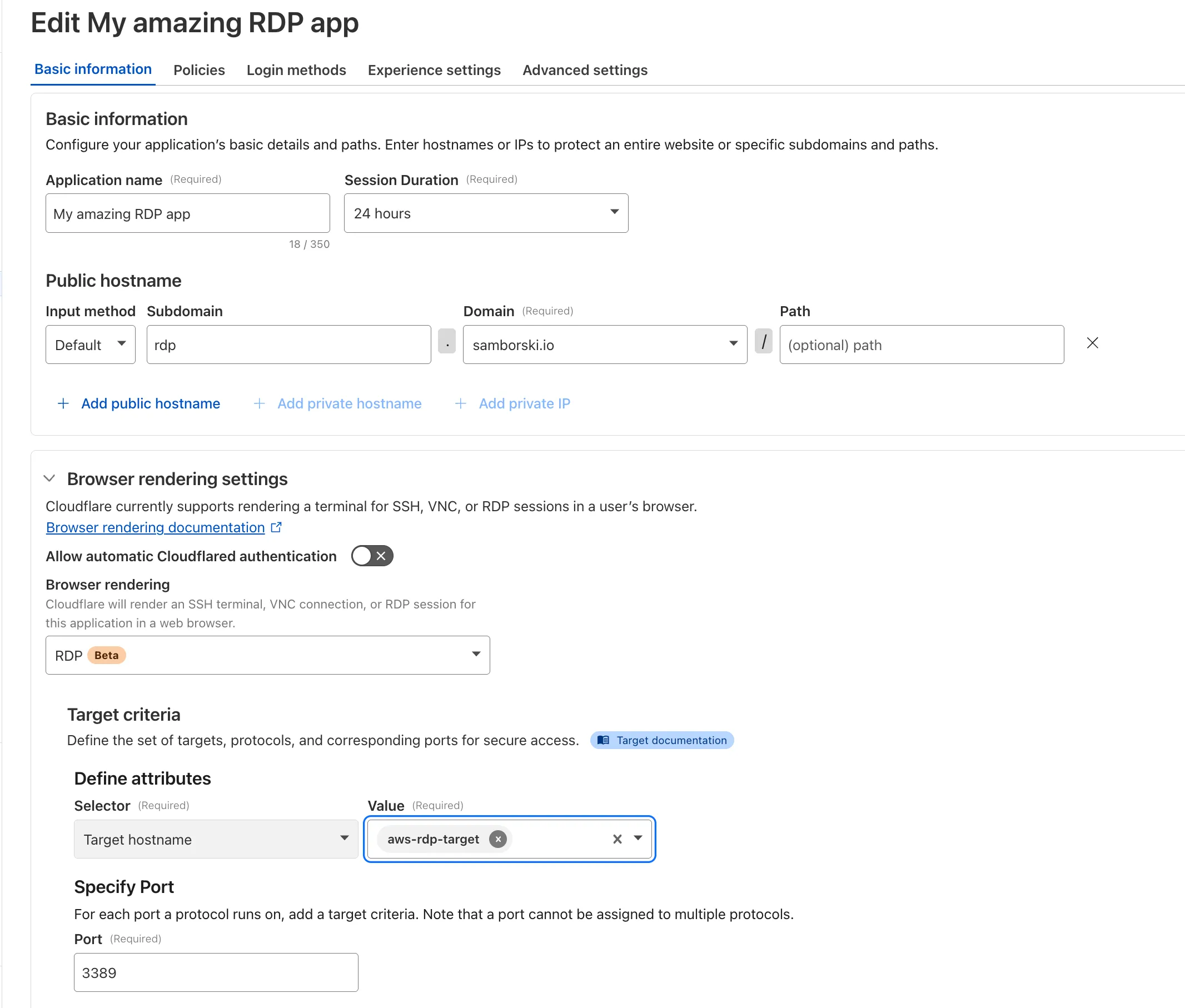
To get started, see Connect to RDP in a browser.
Cloudflare One Analytics Dashboards and Exportable Access Report
Cloudflare One now offers powerful new analytics dashboards to help customers easily discover available insights into their application access and network activity. These dashboards provide a centralized, intuitive view for understanding user behavior, application usage, and security posture.

Additionally, a new exportable access report is available, allowing customers to quickly view high-level metrics and trends in their application access. A preview of the report is shown below, with more to be found in the report:
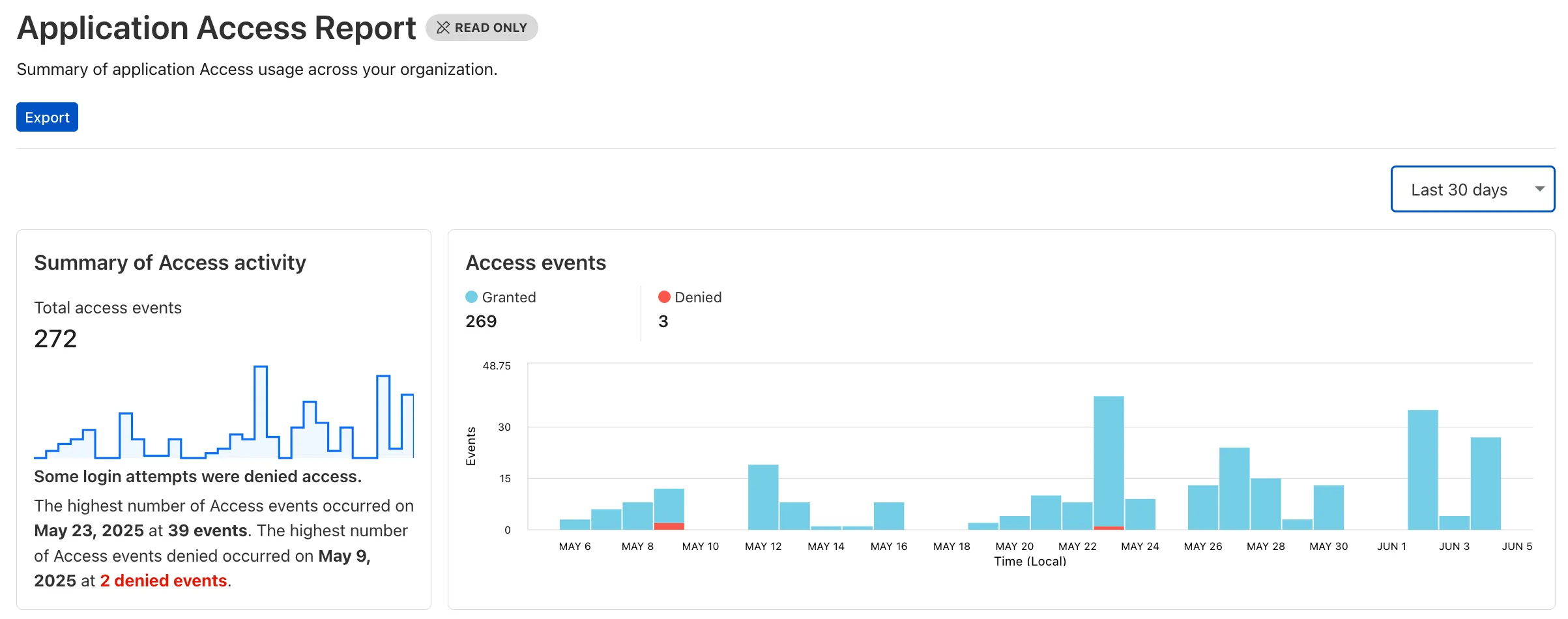
Both features are accessible in the Cloudflare Zero Trust dashboard ↗, empowering organizations with better visibility and control.
New Access Analytics in the Cloudflare One Dashboard
A new Access Analytics dashboard is now available to all Cloudflare One customers. Customers can apply and combine multiple filters to dive into specific slices of their Access metrics. These filters include:
- Logins granted and denied
- Access events by type (SSO, Login, Logout)
- Application name (Salesforce, Jira, Slack, etc.)
- Identity provider (Okta, Google, Microsoft, onetimepin, etc.)
- Users (
chris@cloudflare.com,sally@cloudflare.com,rachel@cloudflare.com, etc.) - Countries (US, CA, UK, FR, BR, CN, etc.)
- Source IP address
- App type (self-hosted, Infrastructure, RDP, etc.)
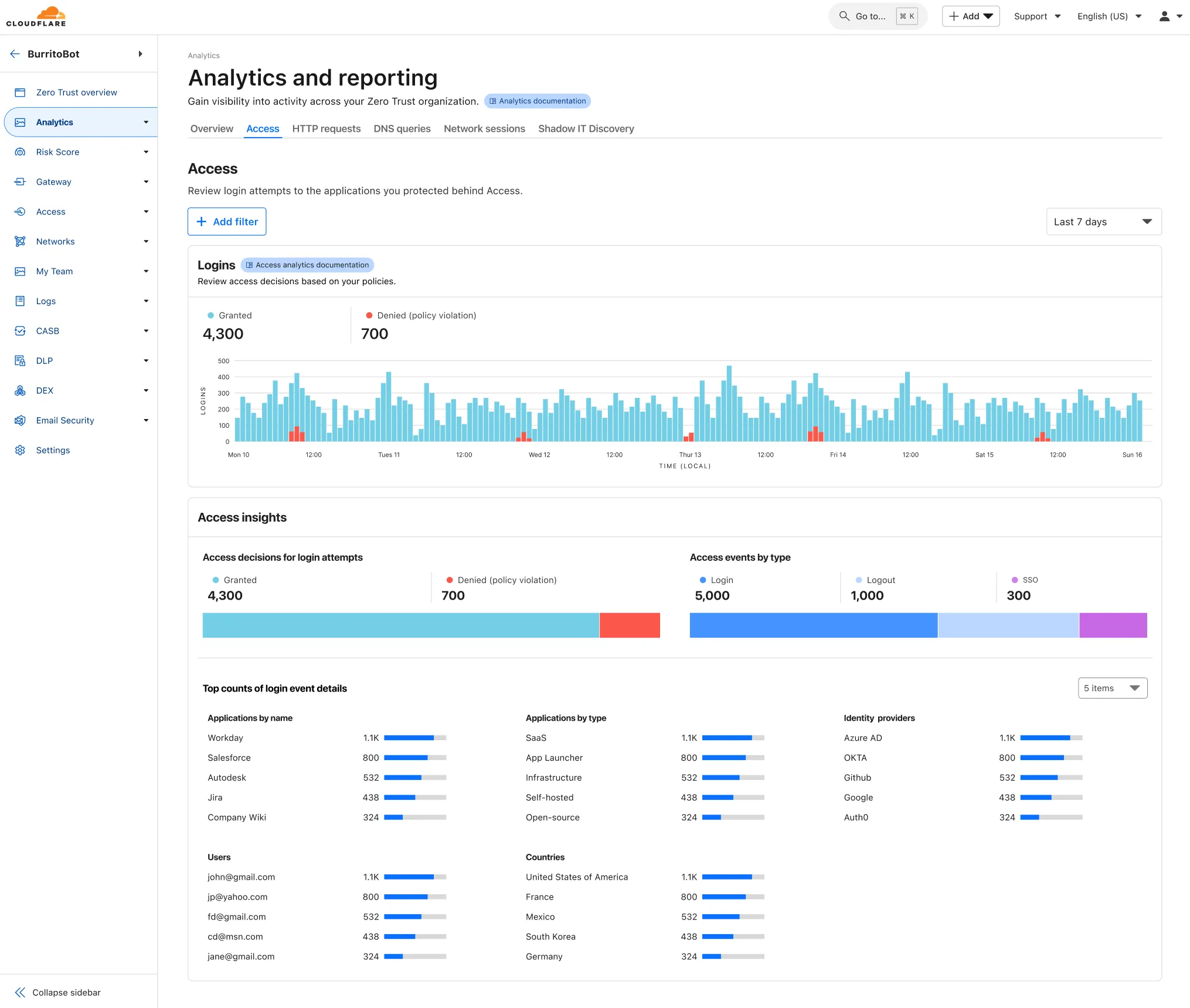
To access the new overview, log in to your Cloudflare Zero Trust dashboard ↗ and find Analytics in the side navigation bar.
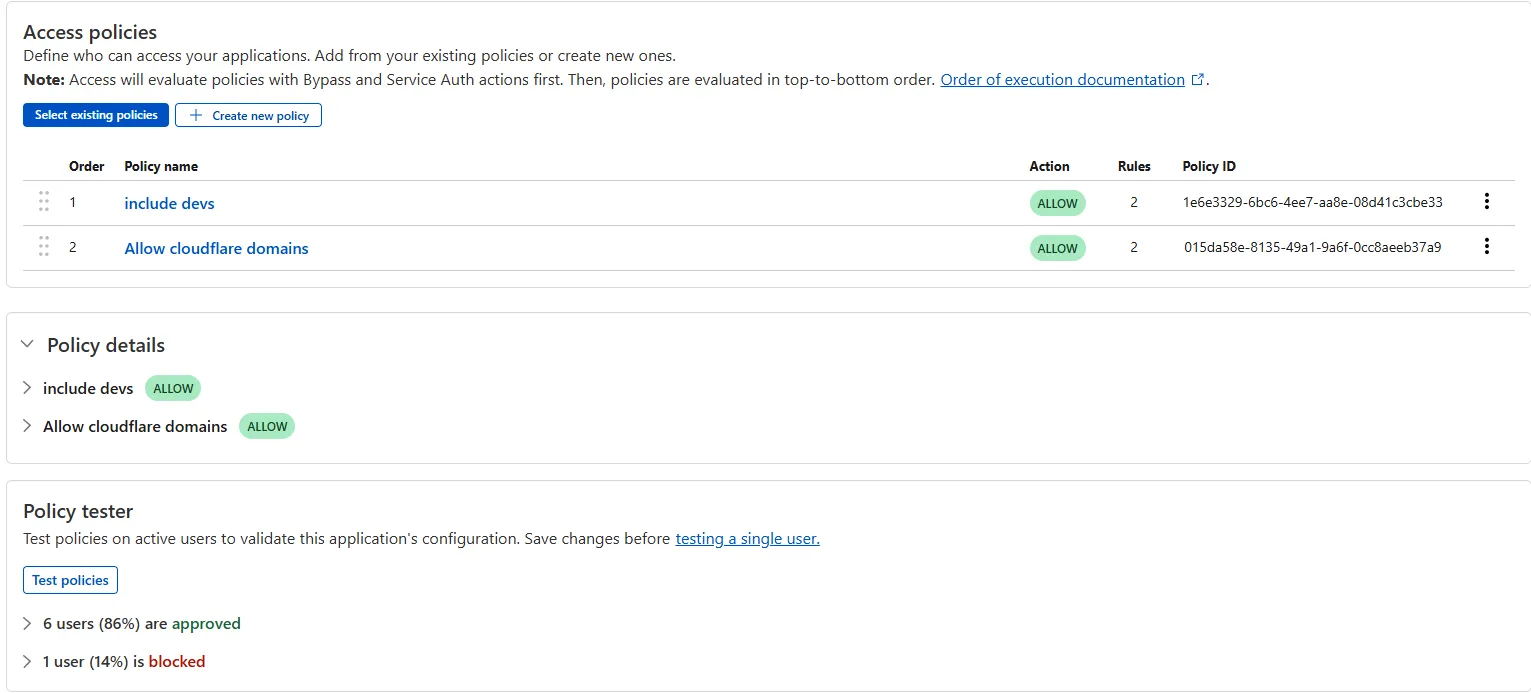
Access bulk policy tester
The Access bulk policy tester is now available in the Cloudflare Zero Trust dashboard. The bulk policy tester allows you to simulate Access policies against your entire user base before and after deploying any changes. The policy tester will simulate the configured policy against each user's last seen identity and device posture (if applicable).
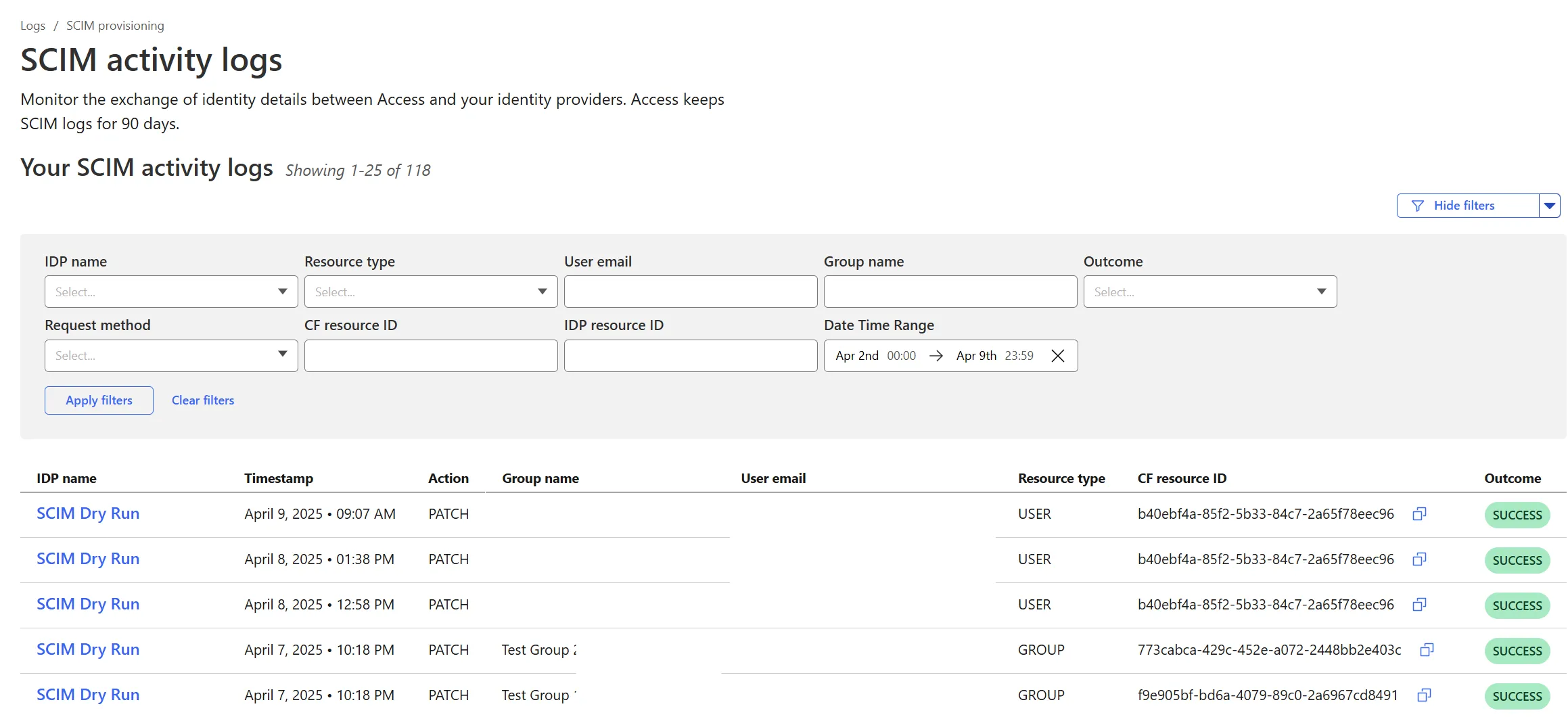
Cloudflare Zero Trust SCIM User and Group Provisioning Logs
Cloudflare Zero Trust SCIM provisioning now has a full audit log of all create, update and delete event from any SCIM Enabled IdP. The SCIM logs support filtering by IdP, Event type, Result and many more fields. This will help with debugging user and group update issues and questions.
SCIM logs can be found on the Zero Trust Dashboard under Logs -> SCIM provisioning.
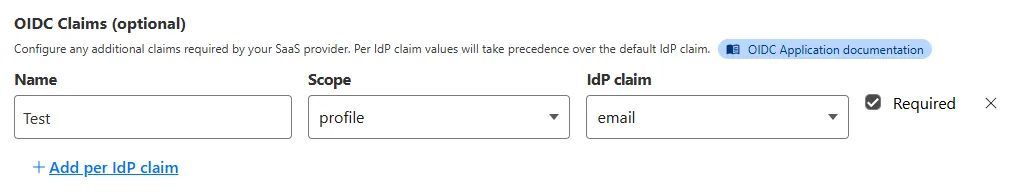
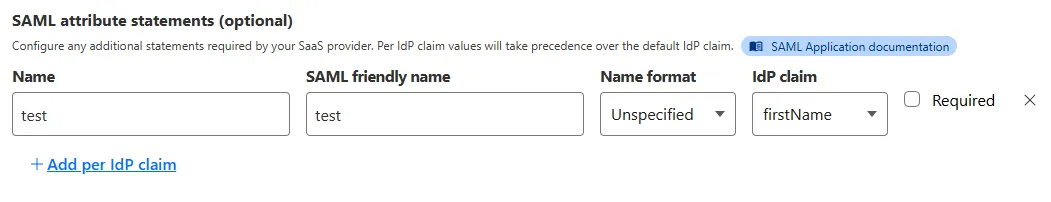
New SAML and OIDC Fields and SAML transforms for Access for SaaS
Access for SaaS applications now include more configuration options to support a wider array of SaaS applications.
SAML and OIDC Field Additions
OIDC apps now include:
- Group Filtering via RegEx
- OIDC Claim mapping from an IdP
- OIDC token lifetime control
- Advanced OIDC auth flows including hybrid and implicit flows
SAML apps now include improved SAML attribute mapping from an IdP.
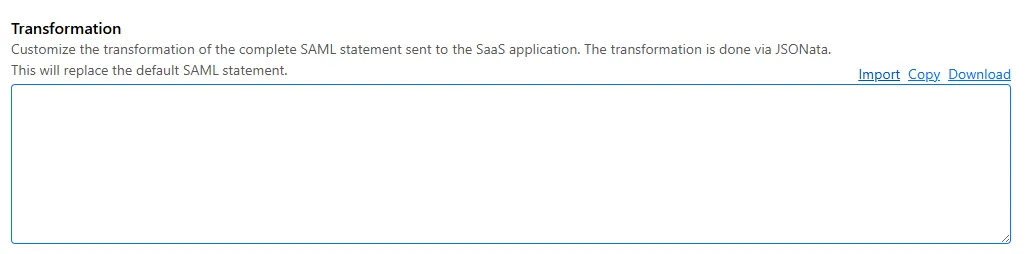
SAML transformations
SAML identities sent to Access applications can be fully customized using JSONata expressions. This allows admins to configure the precise identity SAML statement sent to a SaaS application.
Export SSH command logs with Access for Infrastructure using Logpush
Cloudflare now allows you to send SSH command logs to storage destinations configured in Logpush, including third-party destinations. Once exported, analyze and audit the data as best fits your organization! For a list of available data fields, refer to the SSH logs dataset.
To set up a Logpush job, refer to Logpush integration.
Eliminate long-lived credentials and enhance SSH security with Cloudflare Access for Infrastructure
Organizations can now eliminate long-lived credentials from their SSH setup and enable strong multi-factor authentication for SSH access, similar to other Access applications, all while generating access and command logs.
SSH with Access for Infrastructure uses short-lived SSH certificates from Cloudflare, eliminating SSH key management and reducing the security risks associated with lost or stolen keys. It also leverages a common deployment model for Cloudflare One customers: WARP-to-Tunnel.
SSH with Access for Infrastructure enables you to:
- Author fine-grained policy to control who may access your SSH servers, including specific ports, protocols, and SSH users.
- Monitor infrastructure access with Access and SSH command logs, supporting regulatory compliance and providing visibility in case of security breach.
- Preserve your end users' workflows. SSH with Access for Infrastructure supports native SSH clients and does not require any modifications to users’ SSH configs.
To get started, refer to SSH with Access for Infrastructure.
Access policies support filtering
You can now filter Access policies by their action, selectors, rule groups, and assigned applications.
Private self-hosted applications and reusable policies GA
Private self-hosted applications and reusable Access policies are now generally available (GA) for all customers.
Access Applications support private hostnames/IPs and reusable Access policies.
Cloudflare Access self-hosted applications can now be defined by private IPs, private hostnames (on port 443) and public hostnames. Additionally, we made Access policies into their own object which can be reused across multiple applications. These updates involved significant updates to the overall Access dashboard experience. The updates will be slowly rolled out to different customer cohorts. If you are an Enterprise customer and would like early access, reach out to your account team.
Logpush for SSH command logs
Enterprise customers can now use Logpush to export SSH command logs for Access for Infrastructure targets.
SCIM GA for Okta and Microsoft Entra ID
Cloudflare's SCIM integrations with Okta and Microsoft Entra ID (formerly AzureAD) are now out of beta and generally available (GA) for all customers. These integrations can be used for Access and Gateway policies and Zero Trust user management. Note: This GA release does not include Dashboard SSO SCIM support.
SSH with Access for Infrastructure
Admins can now use Access for Infrastructure to manage privileged access to SSH servers. Access for Infrastructure provides improved control and visibility over who accessed what service and what they did during their SSH session. Access for Infrastructure also eliminates the risk and overhead associated with managing SSH keys by using short-lived SSH certificates to access SSH servers.
Reduce automatic seat deprovisioning minimum to 1 month, down from 2 months.
Admins can now configure Zero Trust seats to automatically expire after 1 month of user inactivity. The previous minimum was 2 months.
Scalability improvements to the App Launcher
Applications now load more quickly for customers with a large number of applications or complex policies.
Add option to bypass CORS to origin server
Access admins can defer all CORS enforcement to their origin server for specific Access applications.
Zero Trust User identity audit logs
All user identity changes via SCIM or Authentication events are logged against a user's registry identity.
Access for SaaS OIDC Support
Access for SaaS applications can be setup with OIDC as an authentication method. OIDC and SAML 2.0 are now both fully supported.
WARP as an identity source for Access
Allow users to log in to Access applications with their WARP session identity. Users need to reauthenticate based on default session durations. WARP authentication identity must be turned on in your device enrollment permissions and can be enabled on a per application basis.
Unique Entity IDs in Access for SaaS
All new Access for SaaS applications have unique Entity IDs. This allows for multiple integrations with the same SaaS provider if required. The unique Entity ID has the application audience tag appended. Existing apps are unchanged.
Default relay state support in Access for SaaS
Allows Access admins to set a default relay state on Access for SaaS apps.
App launcher supports tags and filters
Access admins can now tag applications and allow users to filter by those tags in the App Launcher.
App launcher customization
Allow Access admins to configure the App Launcher page within Zero Trust.
View active Access user identities in the dashboard and API
Access admins can now view the full contents of a user's identity and device information for all active application sessions.
Custom OIDC claims for named IdPs
Access admins can now add custom claims to the existing named IdP providers. Previously this was locked to the generic OIDC provider.
Azure AD authentication contexts
Support Azure AD authentication contexts directly in Access policies.
Custom block pages for Access applications
Allow Access admins to customize the block pages presented by Access to end users.