App Launcher
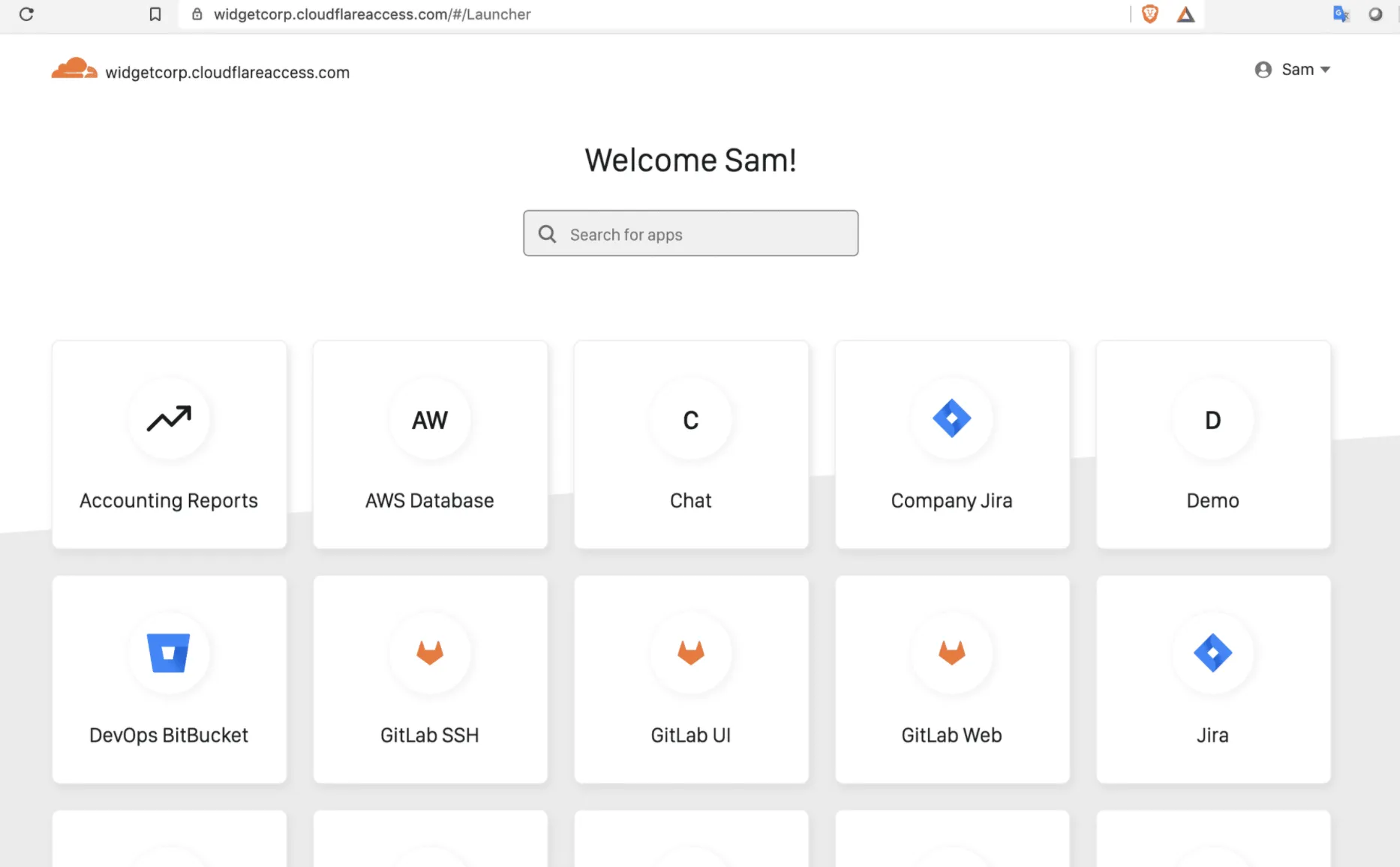
With the Access App Launcher, users can open all applications that they have access to from a single dashboard.
The App Launcher is available at a team domain unique to your Cloudflare Zero Trust account, for example mycompany.cloudflareaccess.com.
Users log in using one of the identity providers configured for the account. Once Access authenticates the user, the App Launcher displays applications they are authorized to use, in the form of application tiles. Selecting an application tile launches the application's hostname, sending the user to that tool as part of their SSO flow.
By default, the App Launcher is disabled. To enable it, you must configure a policy that defines which users can access the App Launcher.
To enable the App Launcher:
-
In the Cloudflare dashboard ↗, go to Zero Trust > Access controls > Access settings.
-
Under the Manage your App Launcher card, select Manage.
-
On the Policies tab, build a policy to define who can access your App Launcher portal. These rules do not impact permissions for the applications secured behind Access.
-
On the Authentication tab, choose the identity providers users can authenticate with.
-
Select Save.
The App Launcher is now available at <your-team-name>.cloudflareaccess.com. You can always edit your App Launcher rules by going to Access controls > Access settings.
Tiles have a one-to-one relationship with each application you create in Access. The tile names displayed in the Access App Launcher portal correspond to the application names listed under Access controls > Applications. For example, if you create one application for general access to your Jira deployment and a separate application that restricts requests to a particular Jira path, a user authorized for both will see separate tiles for each. If you add multiple hostnames to a single application, the user will only see the domain selected in the application's App Launcher settings.
To show an Access application in the App Launcher:
-
In the Cloudflare dashboard ↗, go to Zero Trust > Access controls > Applications.
-
Select an application and select Configure.
-
Go to Experience settings.
-
Select Show application in App Launcher. The App Launcher link will only appear for users who are allowed by your Access policies. Blocked users will not see the app in their App Launcher.
-
(Optional) To use a custom logo for the application tile, select Use custom logo and enter a link to your desired image.
-
In Application domains, choose a domain to use for the App Launcher link.
-
(Optional) In Tags, add custom tags so that users can more easily find the application in their App Launcher.
To customize the App Launcher with your own branding, messages, and links, refer to the Custom pages documentation.