Office 365 retraction
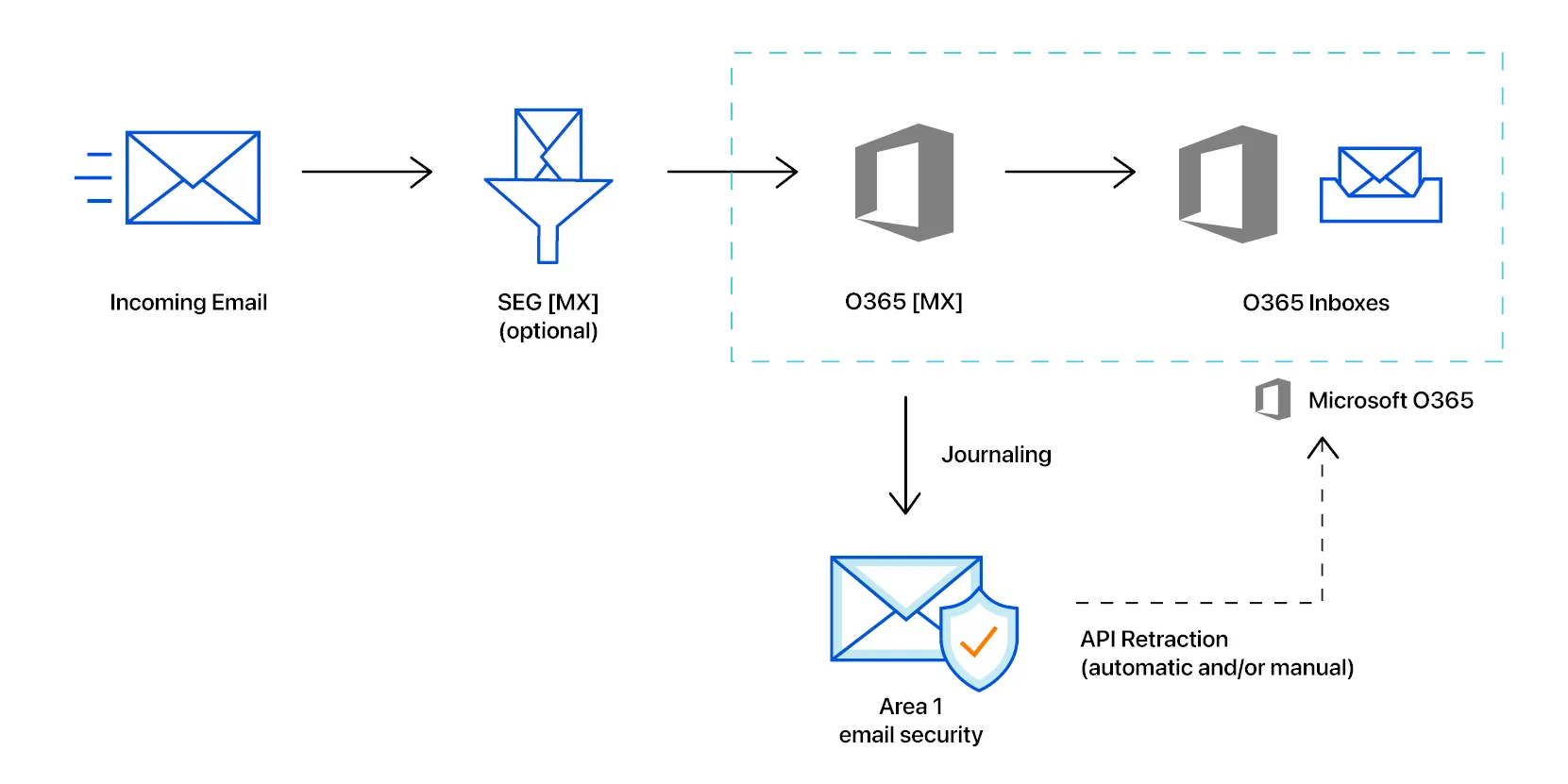
In this tutorial you will learn how to set up email retraction for Microsoft Office 365.
For message retraction to successfully execute, Email Security needs to be authorized to make API calls into the Office 365 Graph API architecture. The account used to authorize Email Security requires the Privileged role admin role.
When assigning user roles in the Office 365 console, you will find these roles in User permissions > Roles configuration > Identity admin roles.
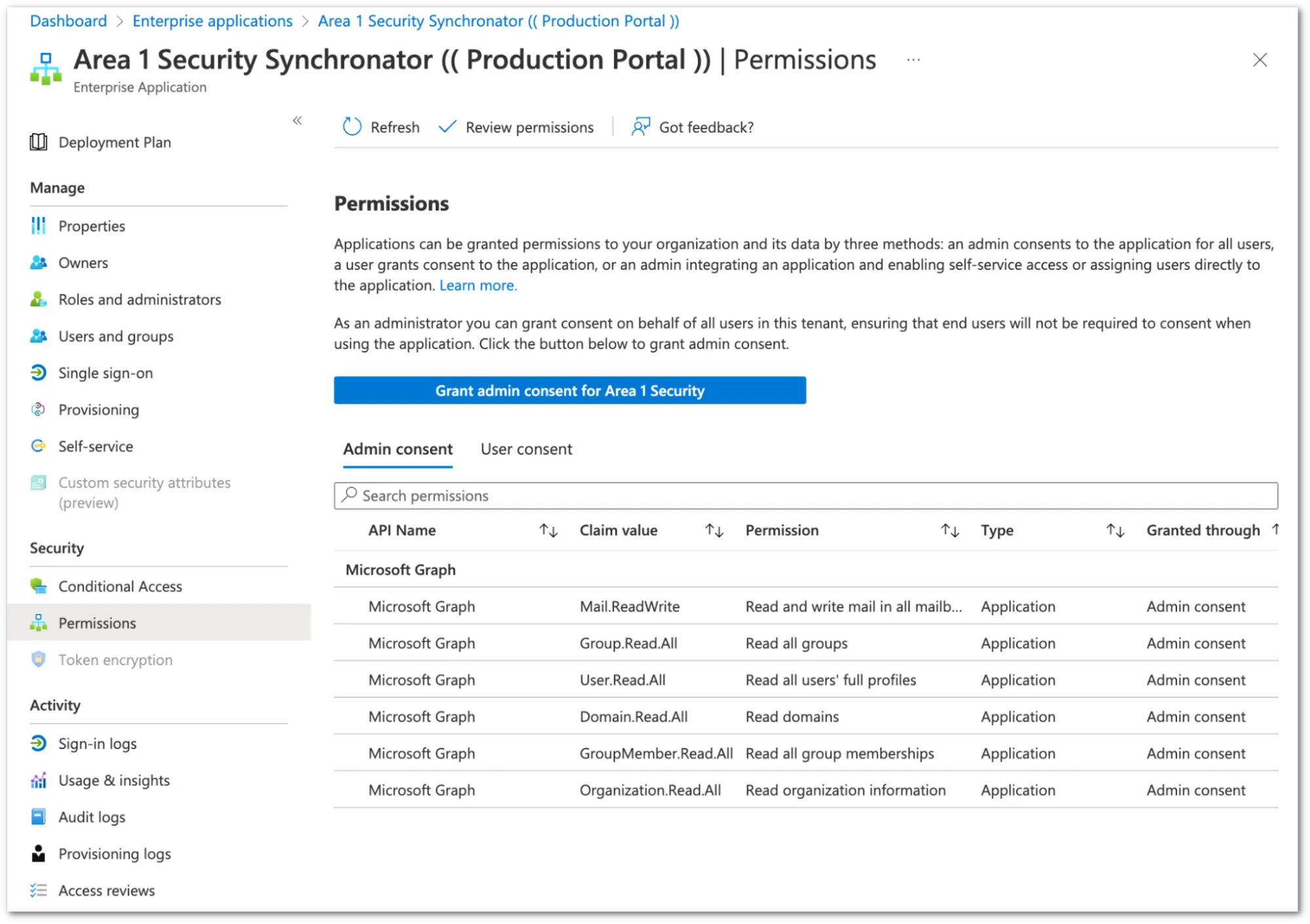
The authorization process grants Email Security access to the Azure environment with the least applicable privileges required to function. The Enterprise Application that Email Security registers (the Email Security Synchronator) is not tied to any administrator account. Inside of the Azure Active Directory admin center you can review the permissions granted to the application in the Enterprise Application section.
-
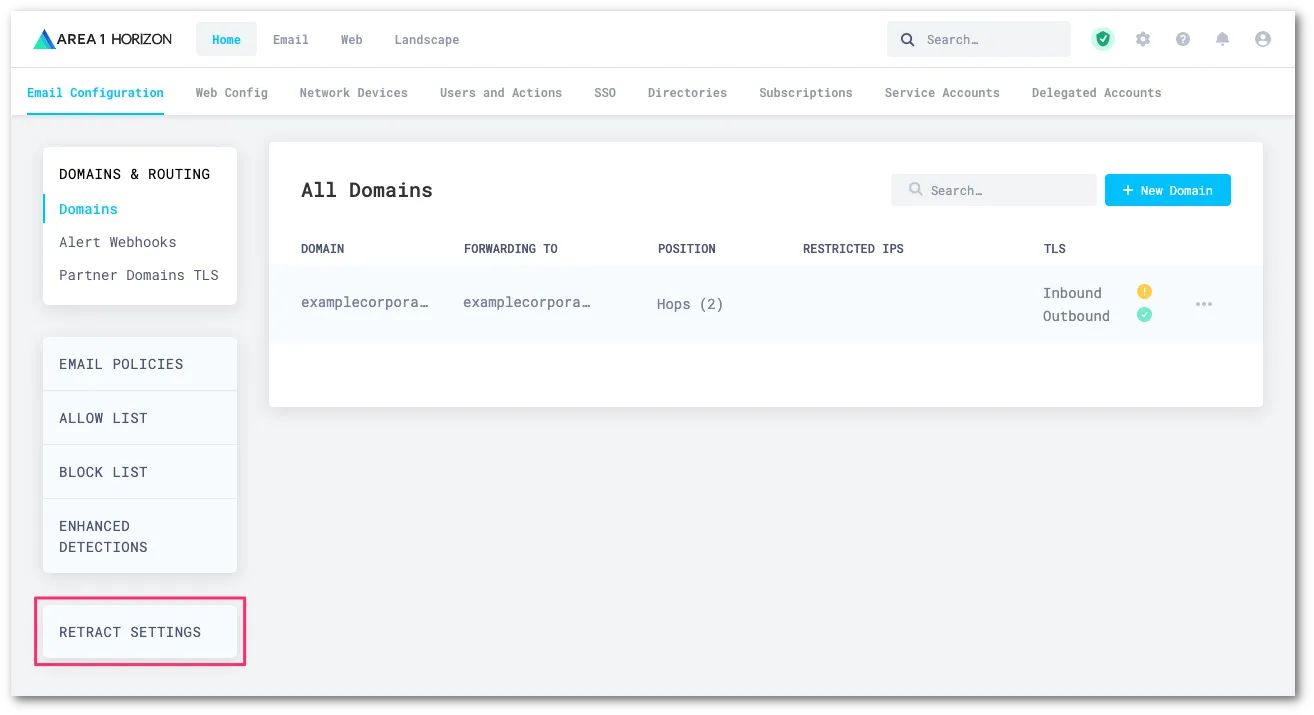
Log in to the Email Security dashboard ↗, and select Settings (the gear icon).
-
Go to Email Configuration > RETRACT SETTINGS.
-
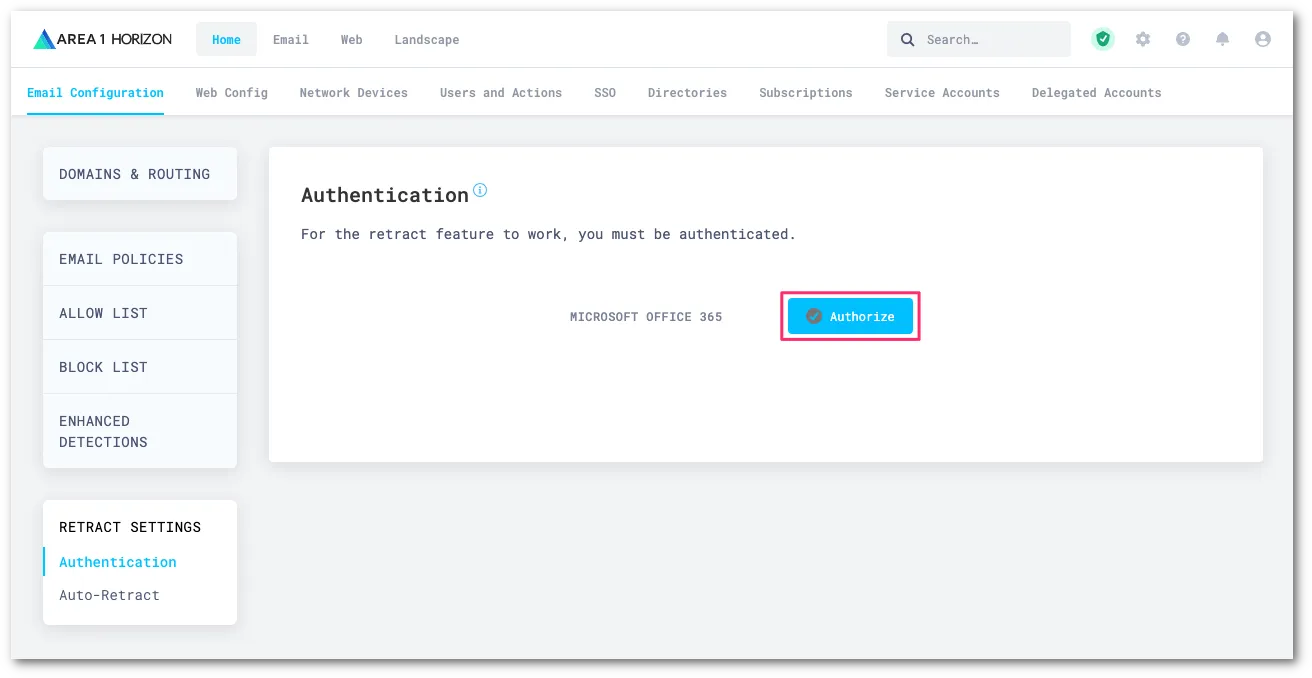
You need to authorize Email Security to execute retractions through the Graph API of Office 365. Make sure that the account that you will be using to authenticate has the appropriate administrative roles assigned. Select Authorize to start the process.
-
The Email Security dashboard will redirect you to a Microsoft login page. Select or enter the appropriate account to initiate the authentication process.
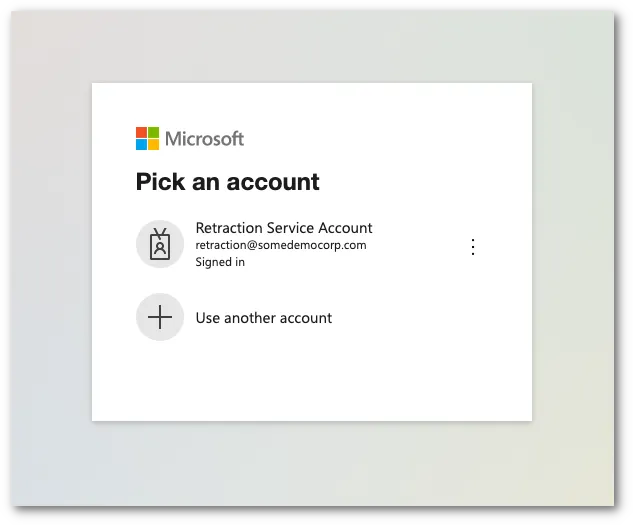
-
Once authenticated, the system will show a dialog box with a list of the requested permissions. Select Accept to authorize the change.
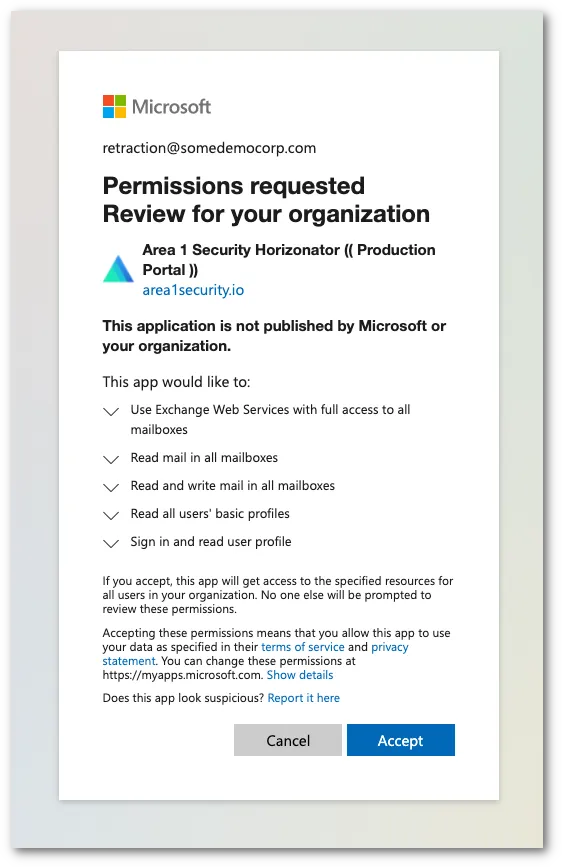
-
Upon authorization, you will be automatically redirected to the Email Security dashboard, with a notification that the authorization completed successfully. Select Dismiss to clear the notification.
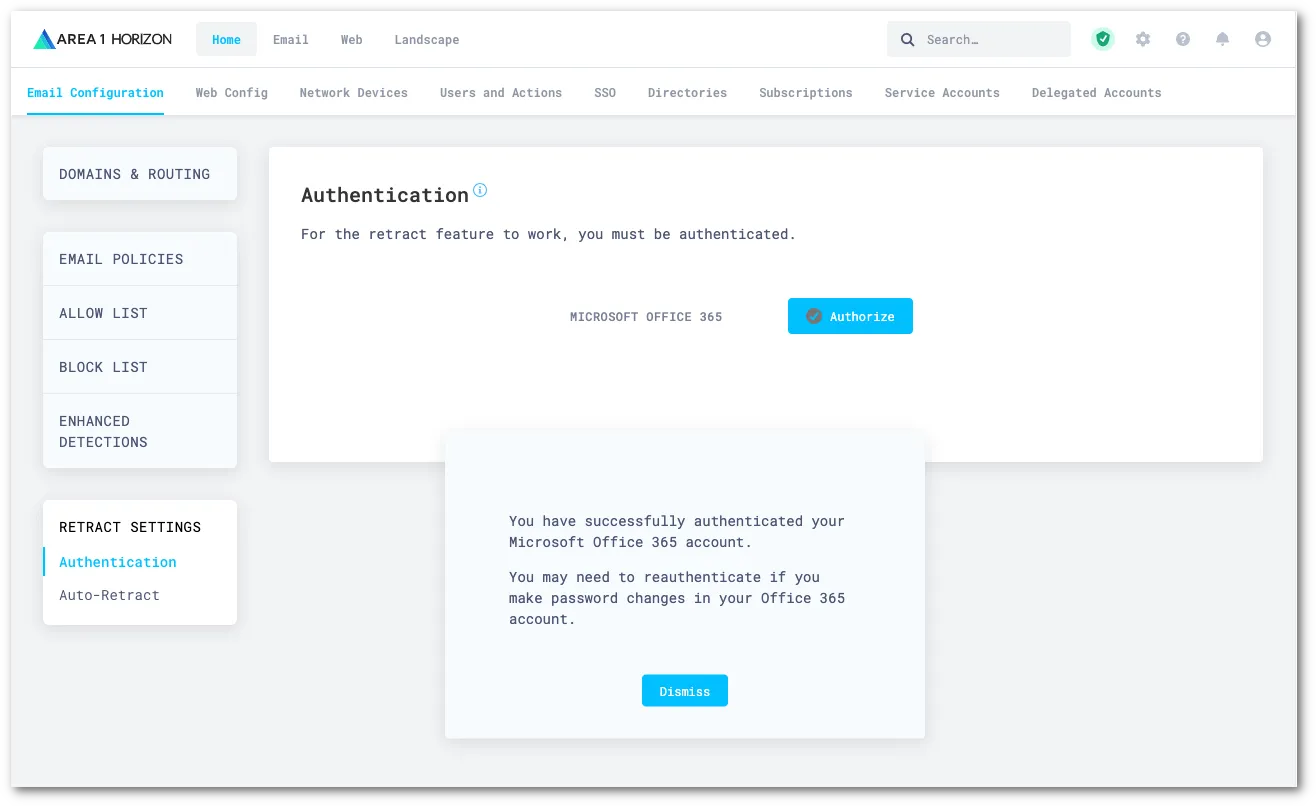
You can set up auto-retraction to automatically move messages matching certain dispositions to specific folders within a user's mailbox.
To set up automatic retraction:
-
Log in to the Email Security (formerly Area 1) dashboard ↗.
-
Go to Settings (the gear icon).
-
On Email Configuration, go to Retract Settings > Auto-Retract.
-
Select Edit.
-
For each disposition, choose which folder the message should be sent to:
- No Action: Do not move the message.
- Junk Email: Sends the message to the junk or spam email folder.
- Trash: Sends the message to the trash or deleted items email folder.
- Soft Delete — user recoverable (Microsoft only): Sends the message to the user's Deleted Items folder. Messages can be recovered by the user.
- Hard Delete — admin recoverable: Completely deletes messages from a user's inbox. Office 365 messages cannot be recovered without using the eDiscovery feature or the Exchange admin center. Refer to [Recover hard deleted messages](#recover-hard-deleted-messages) for more information.
-
Select Update Auto-retract Settings.
Email Security (formerly Area 1) is continuously gathering new information about phishing campaigns. Users might have email messages in their inboxes that were scanned by Email Security (formerly Area 1) but not retracted initially because, at the time of scan, these email messages had not been identified as a threat. To mitigate risk, Email Security (formerly Area 1) offers you tools to re-evaluate email messages at a fixed time interval based on knowledge Cloudflare may have acquired since initial delivery. Any email messages that fit this new threat knowledge will be retracted.
You can enable two options:
- Post Delivery Response: Email Security (formerly Area 1) will continue to re-evaluate emails already delivered to your users' inboxes at a fixed time interval in search for phishing sites or campaigns not previously known to Cloudflare. If any email messages fitting these new criteria are found, Email Security (formerly Area 1) retracts them. Rescans occur at a five minute, 12 hour, and 24 hour intervals.
- Phish Submission Response: Email Security (formerly Area 1) will retract emails already delivered that are reported by your users as phishing, and are found to be malicious by Email Security (formerly Area 1). Retraction will occur according to your configuration.
If your email architecture does not include an outbound gateway, you can skip this step and proceed to the next one.
On the other hand, if your email architecture requires outbound messages to traverse your email gateway, you may want to consider configuring a connector to send the journal messages directly to Email Security.
-
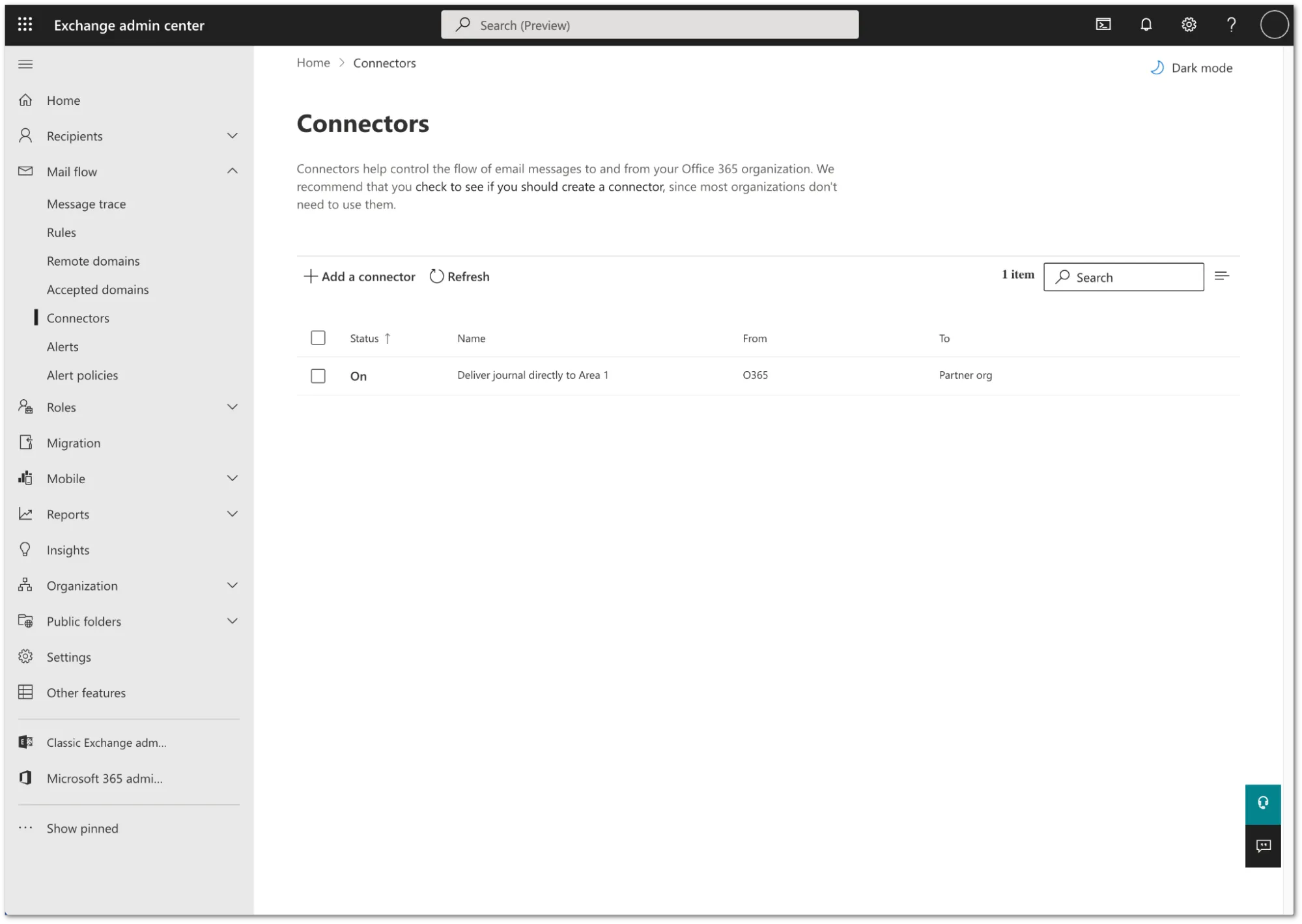
Log in to the Exchange admin center ↗, and go to Mail flow > Connectors.
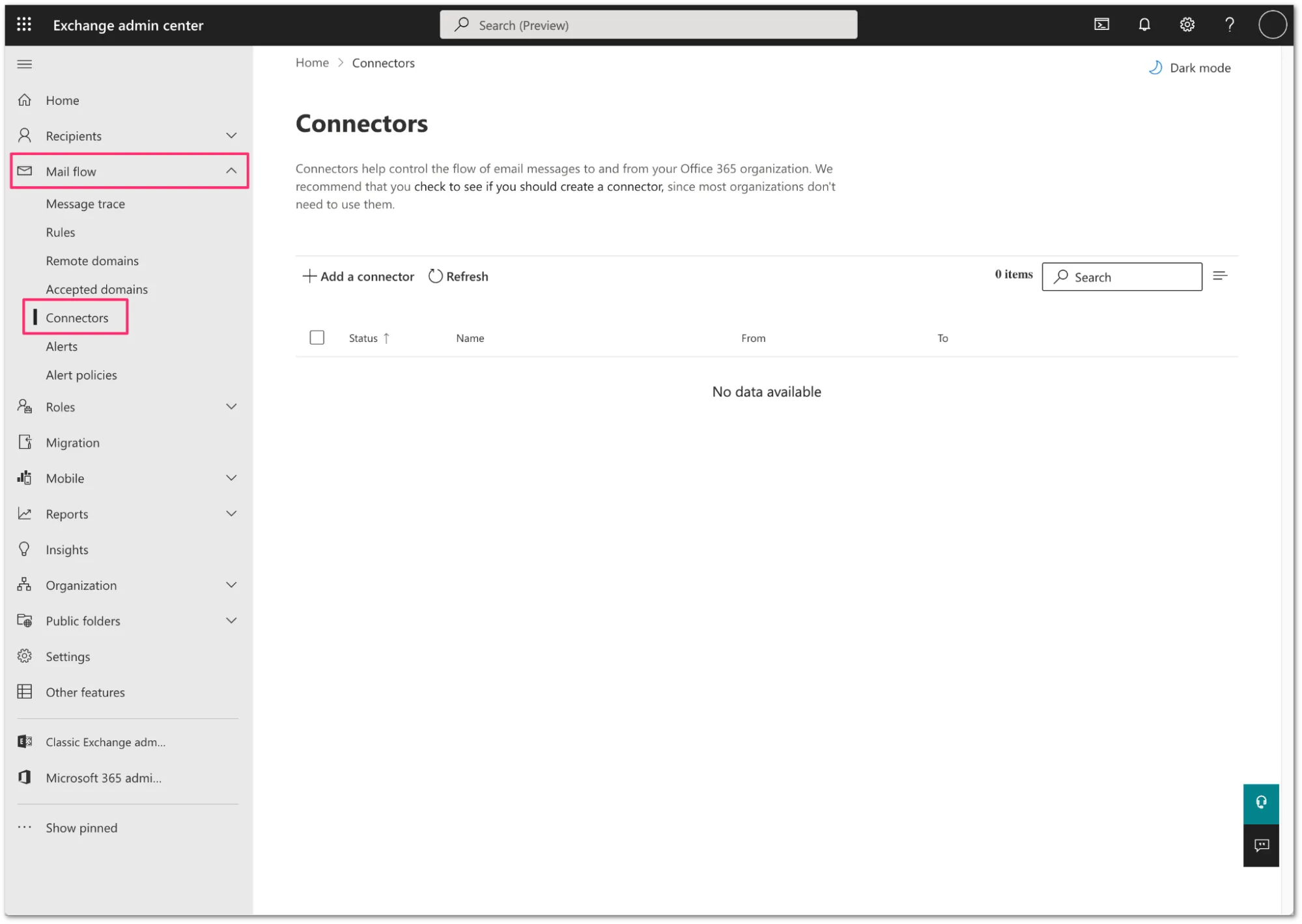
-
Select Add a connector.
-
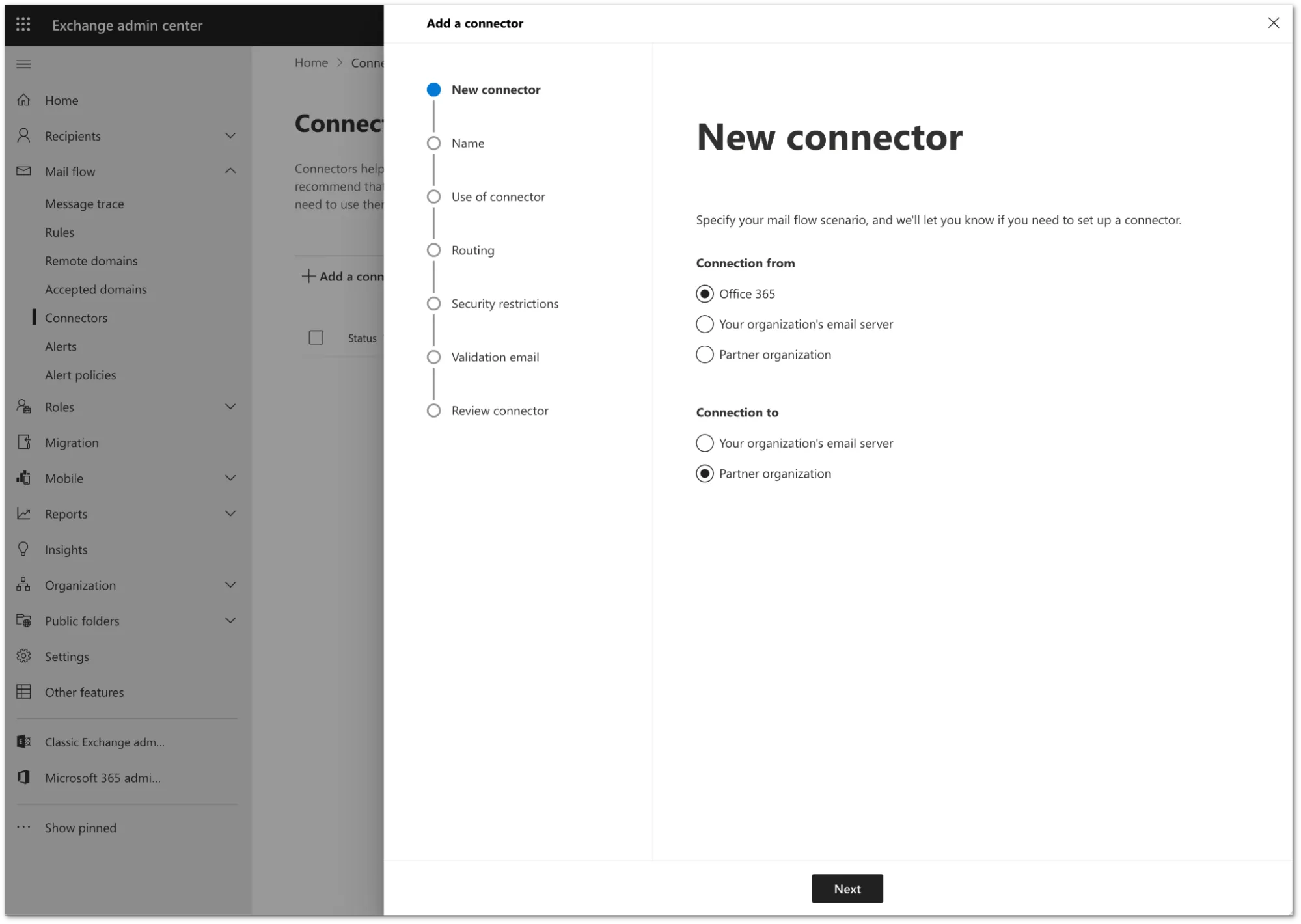
Configure the new connector as follows:
- Connection From: Office 365
- Connection to: Partner Organization
-
Select Next.
-
Configure the connector as follows:
- Name:
Deliver journal directly to Area 1 - Description:
Deliver journal directly to Area 1 - Turn it on: Enabled.
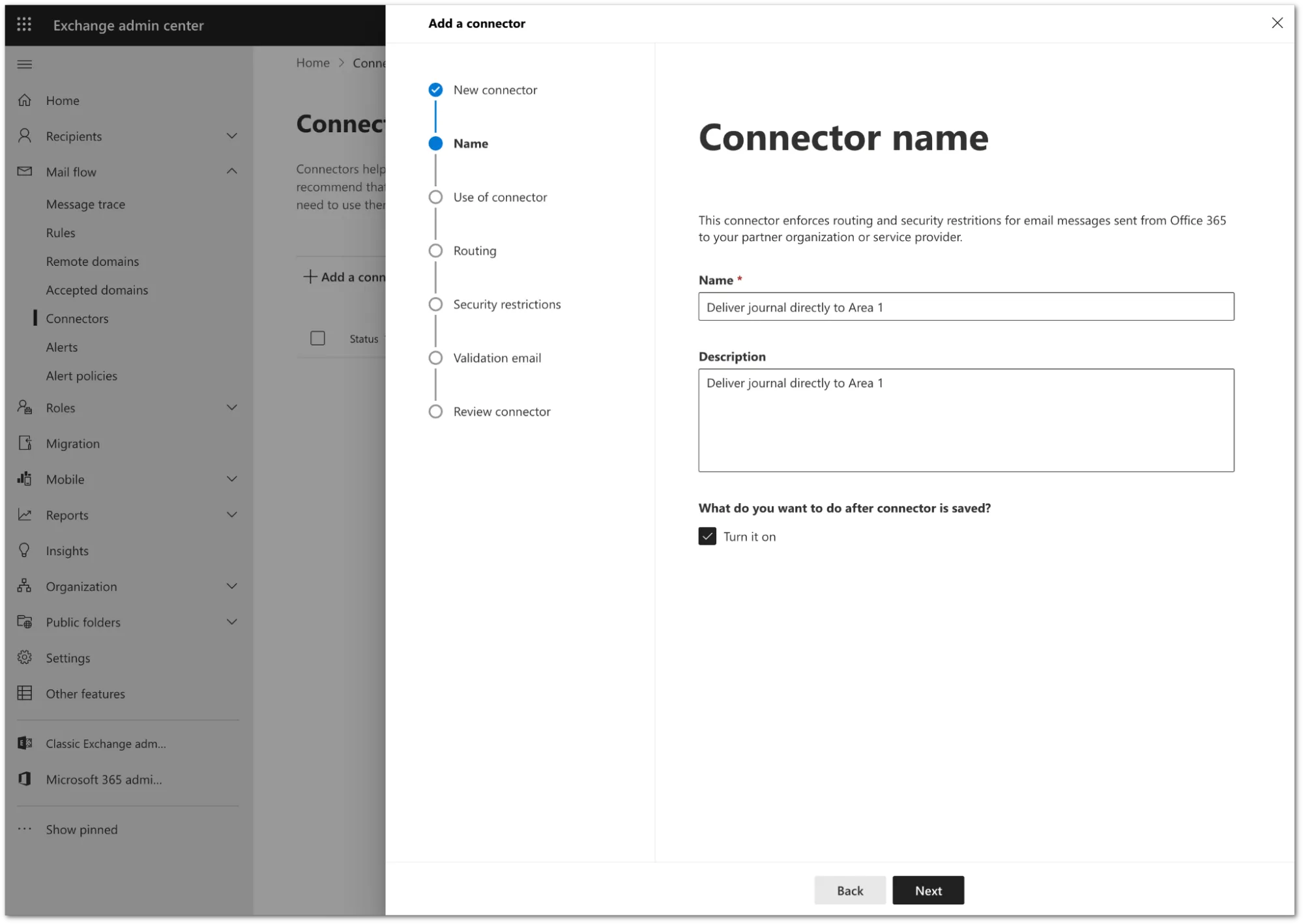
- Name:
-
Select Next.
-
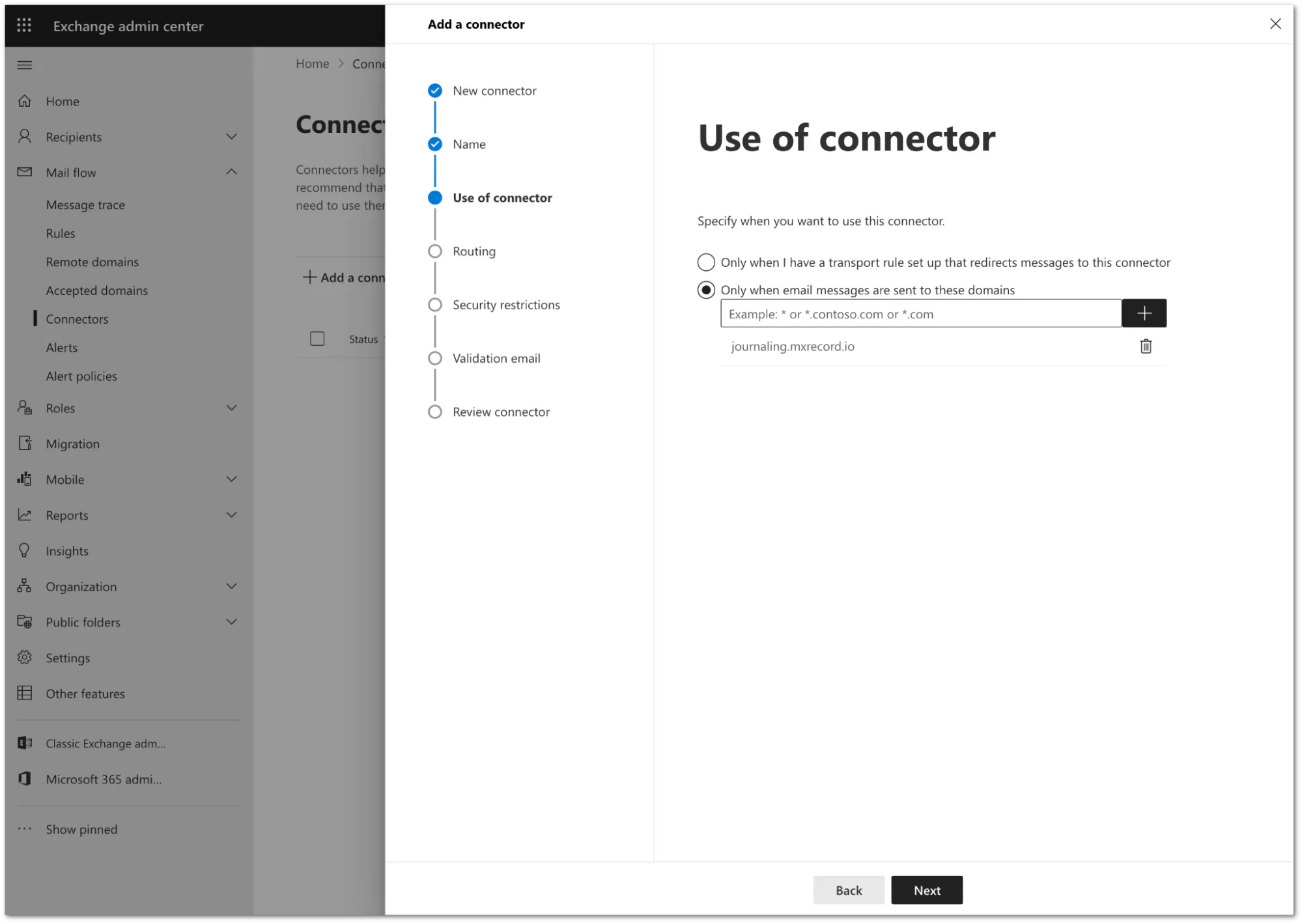
Configure the Use of connector setting as follows:
- Select Only when email messages are sent to these domains.
- In the text field, enter
journaling.mxrecord.ioas the host address, and select + to add the domain.
-
Select Next.
-
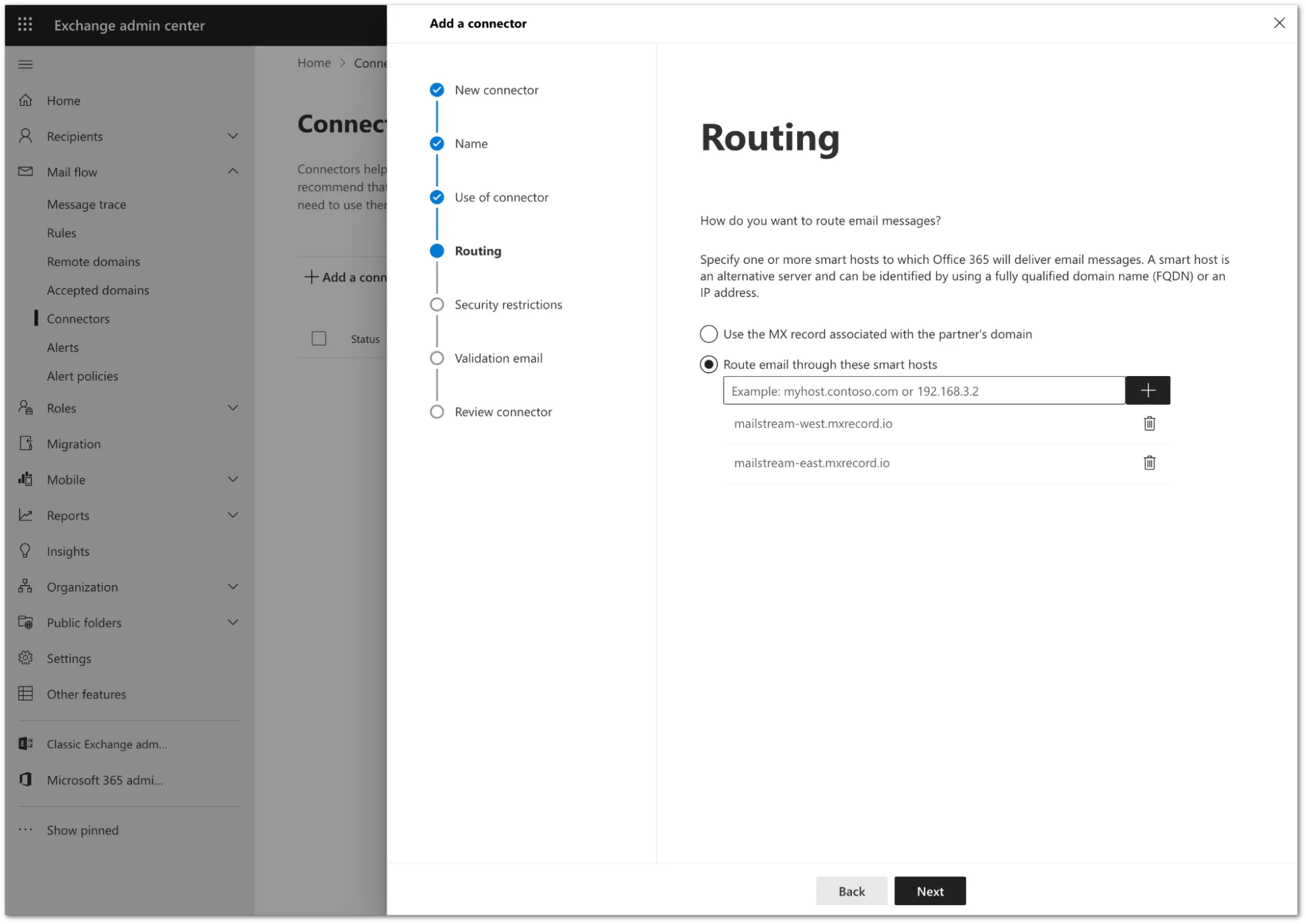
Configure the Routing setting as follows:
- Select Route email through these smart hosts.
- In the text field, enter
journaling.mxrecord.ioas the smart host ↗ address, and select + to add the domain.
-
Select Next.
-
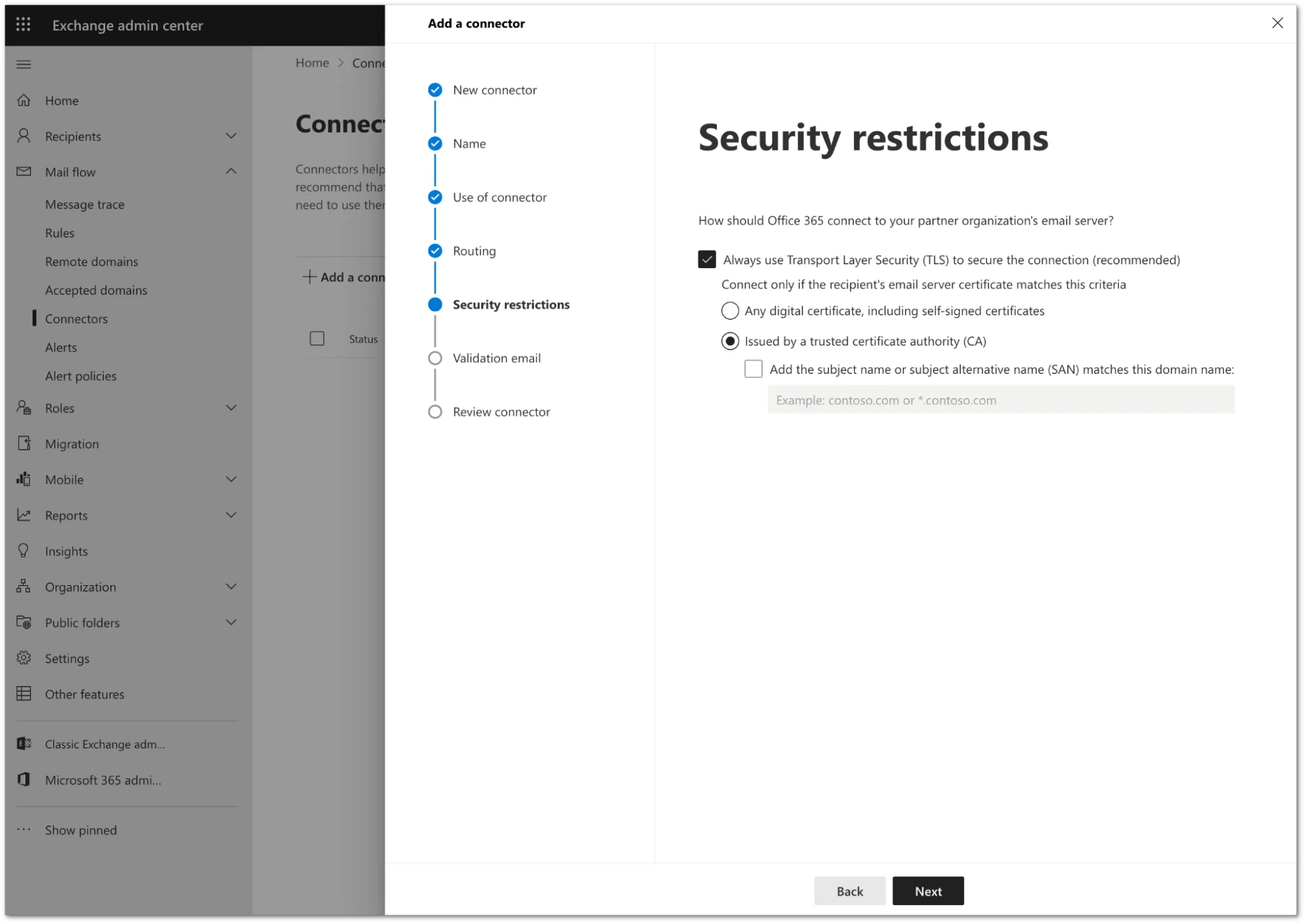
In Security restrictions, you need to keep the default TLS configuration. Review the following settings:
- Make sure the Always use Transport Layer Security (TLS) to secure the connection (recommended) checkbox is selected.
- In Connect only if the recipients email server certificate matches this criteria select Issued by a trusted certificate authority (CA).
-
Select Next.
-
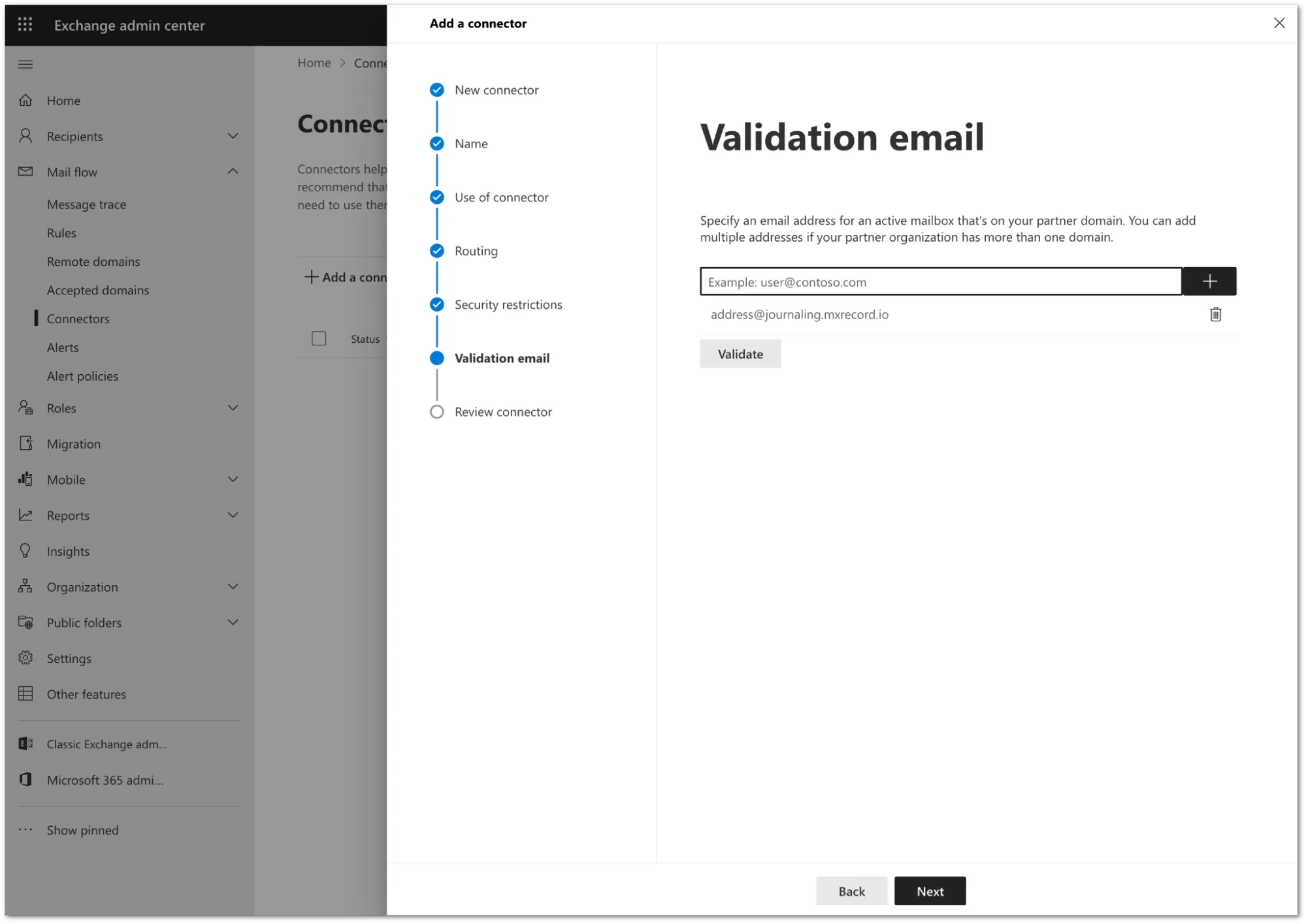
You need to validate the connector by using your tenant’s specific journaling address. To find this address, go to the Email Security dashboard ↗ > Support > Service Addresses page.
-
Add the address and select Validate.
-
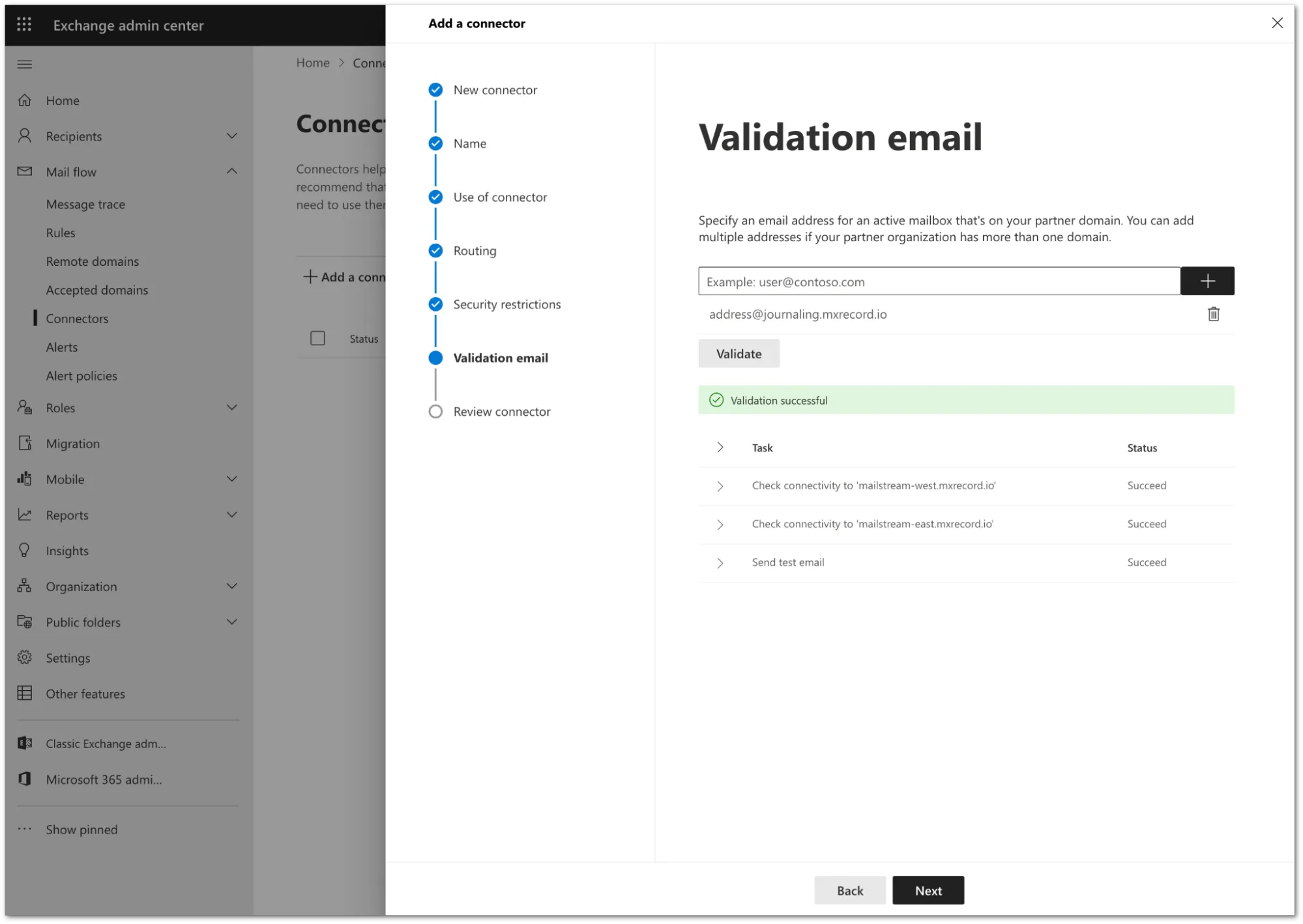
Once the validation completes, you should receive a Succeed status for all the tasks. Select Next.
-
Review the configuration and select Create connector.
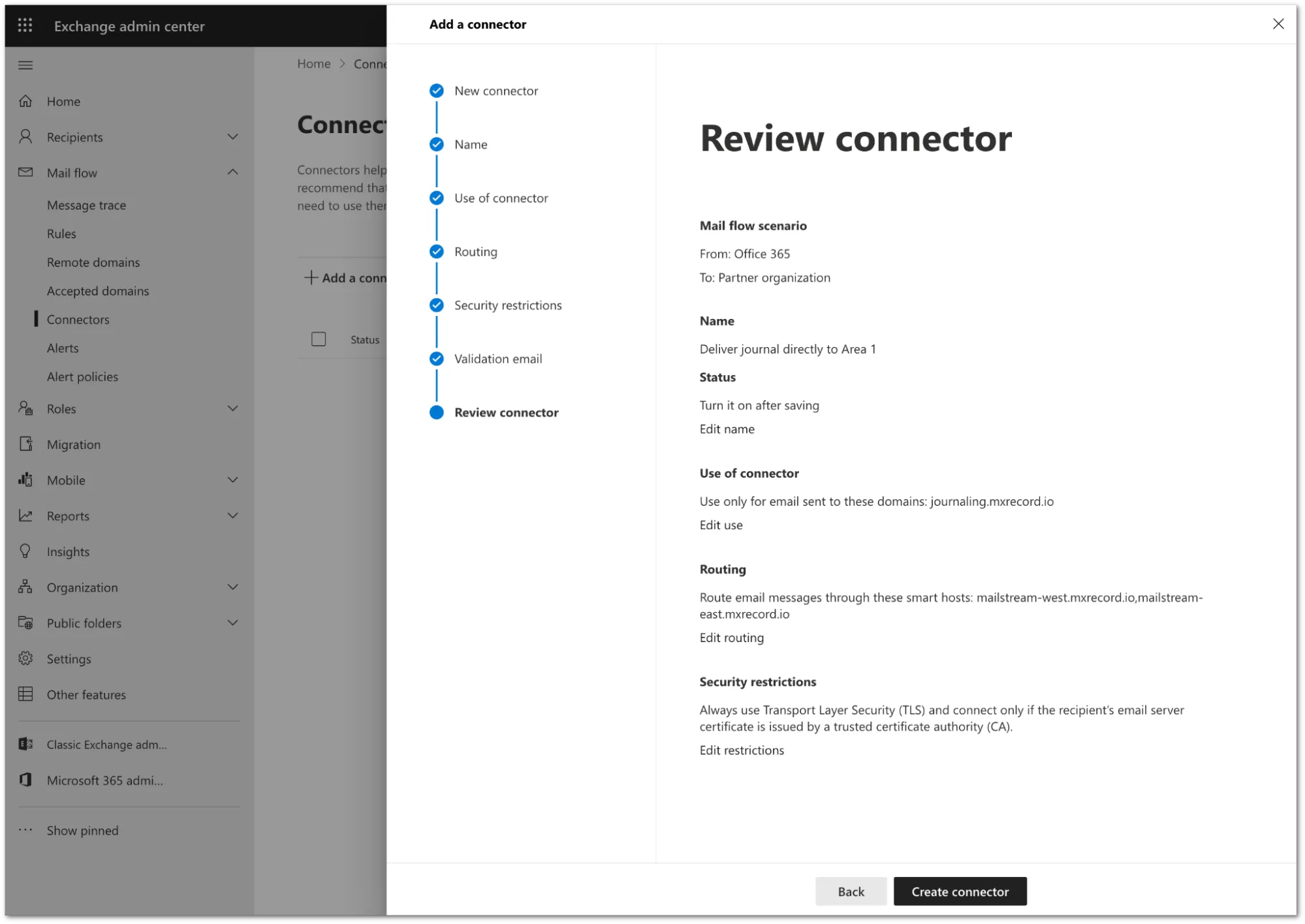
Your connector is now active. You can find it in Exchange admin center > Mail flow > Connectors.
-
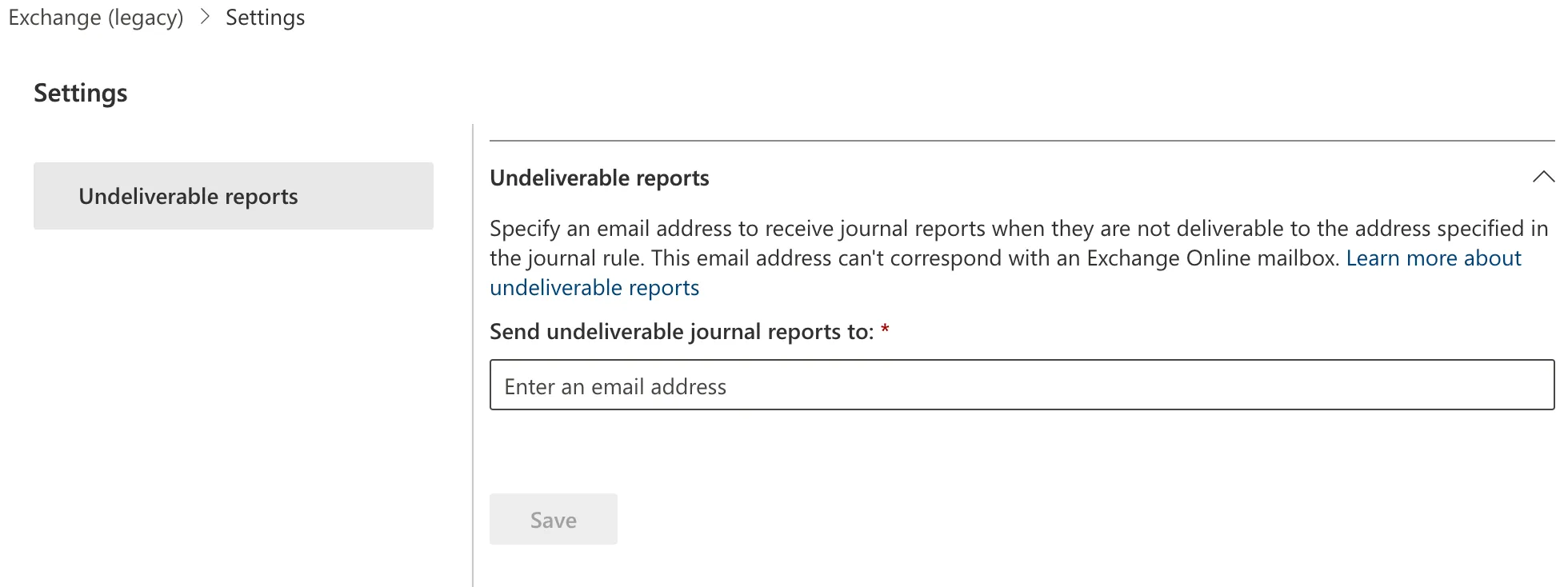
Log in to the Microsoft Purview compliance portal ↗.
-
Go to Data lifecycle management > Exchange (legacy).
-
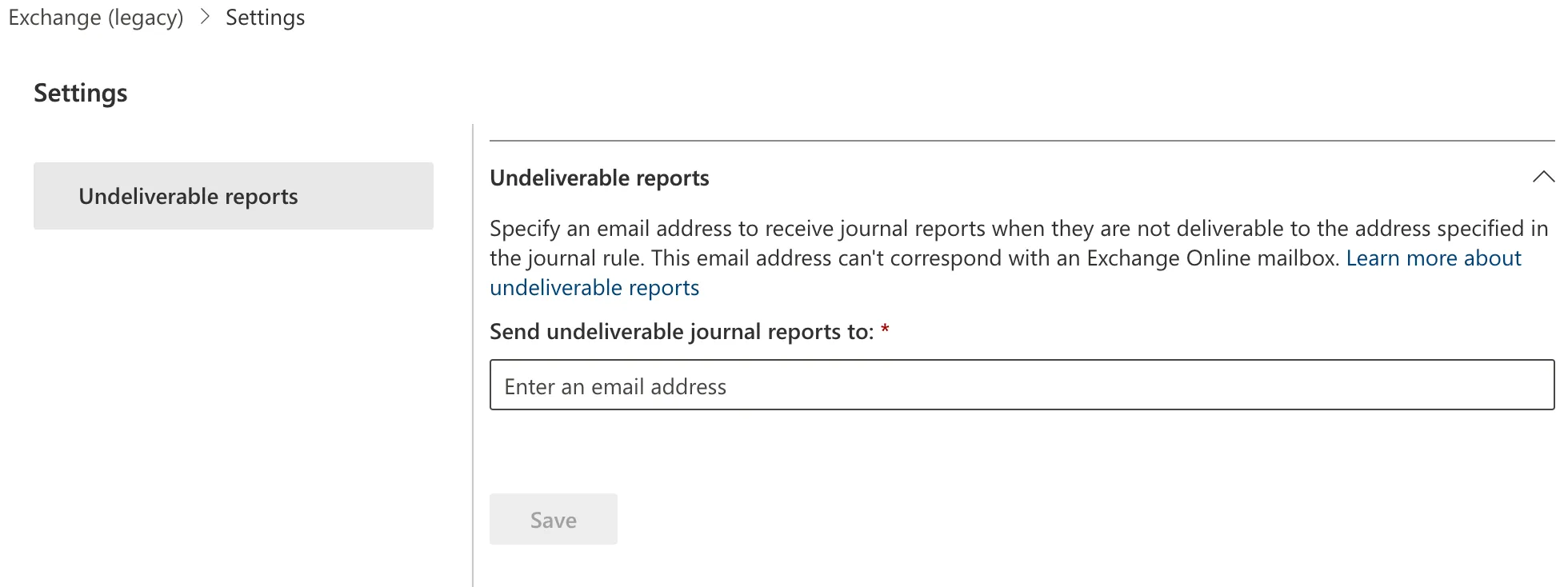
Select Settings (the gear icon).
-
In Send undeliverable journal reports to enter the email address of a valid user account. Note that you cannot use a team or group address.
-
Select Save.
-
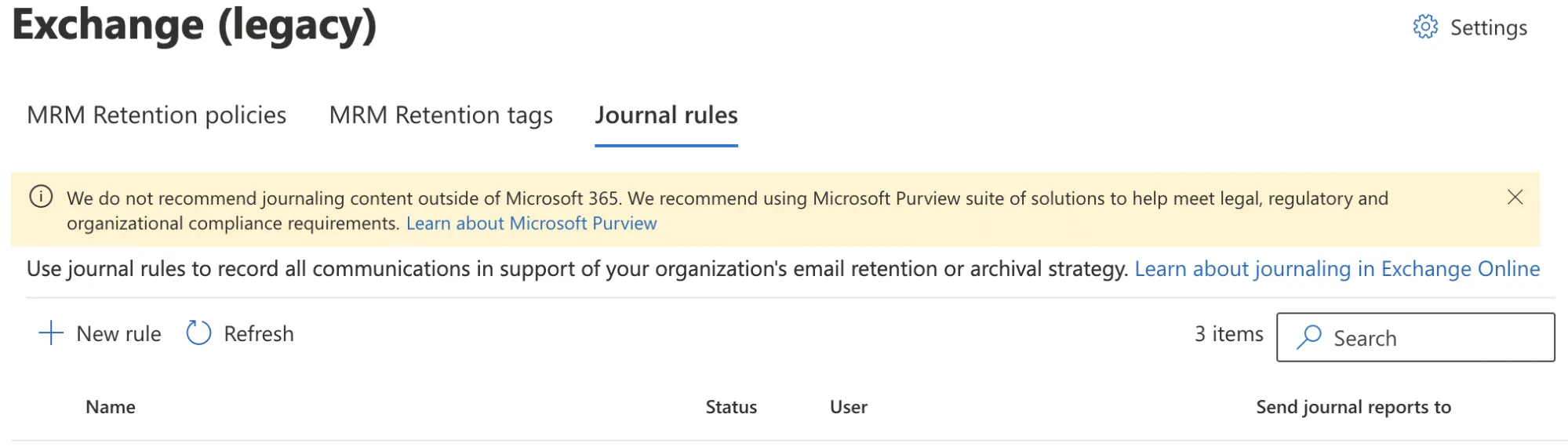
Still in the Exchange (legacy) screen, select Journal Rules.
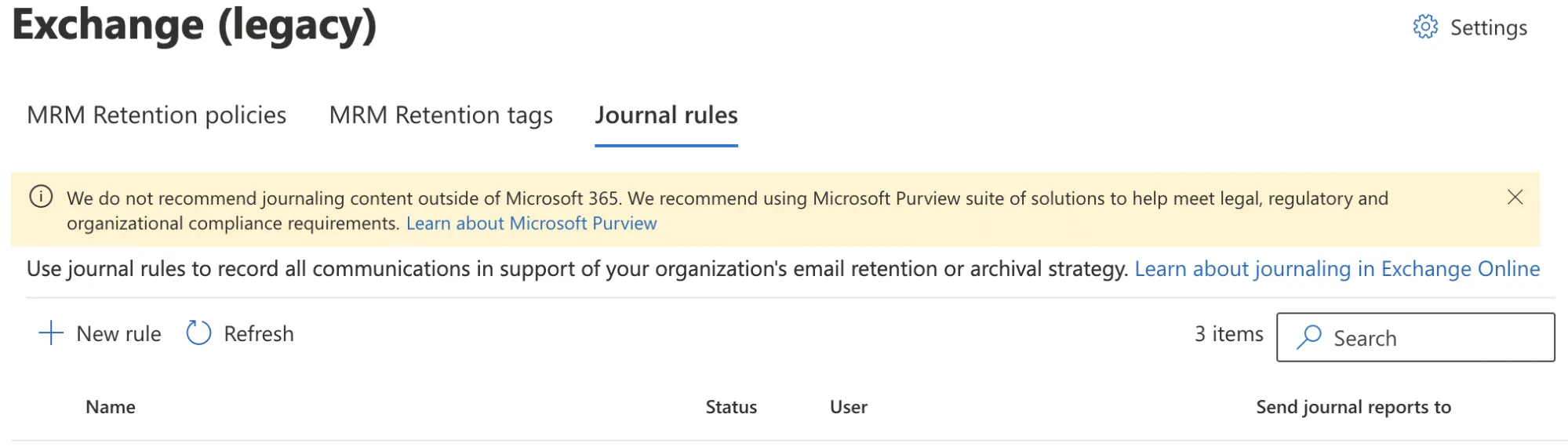
-
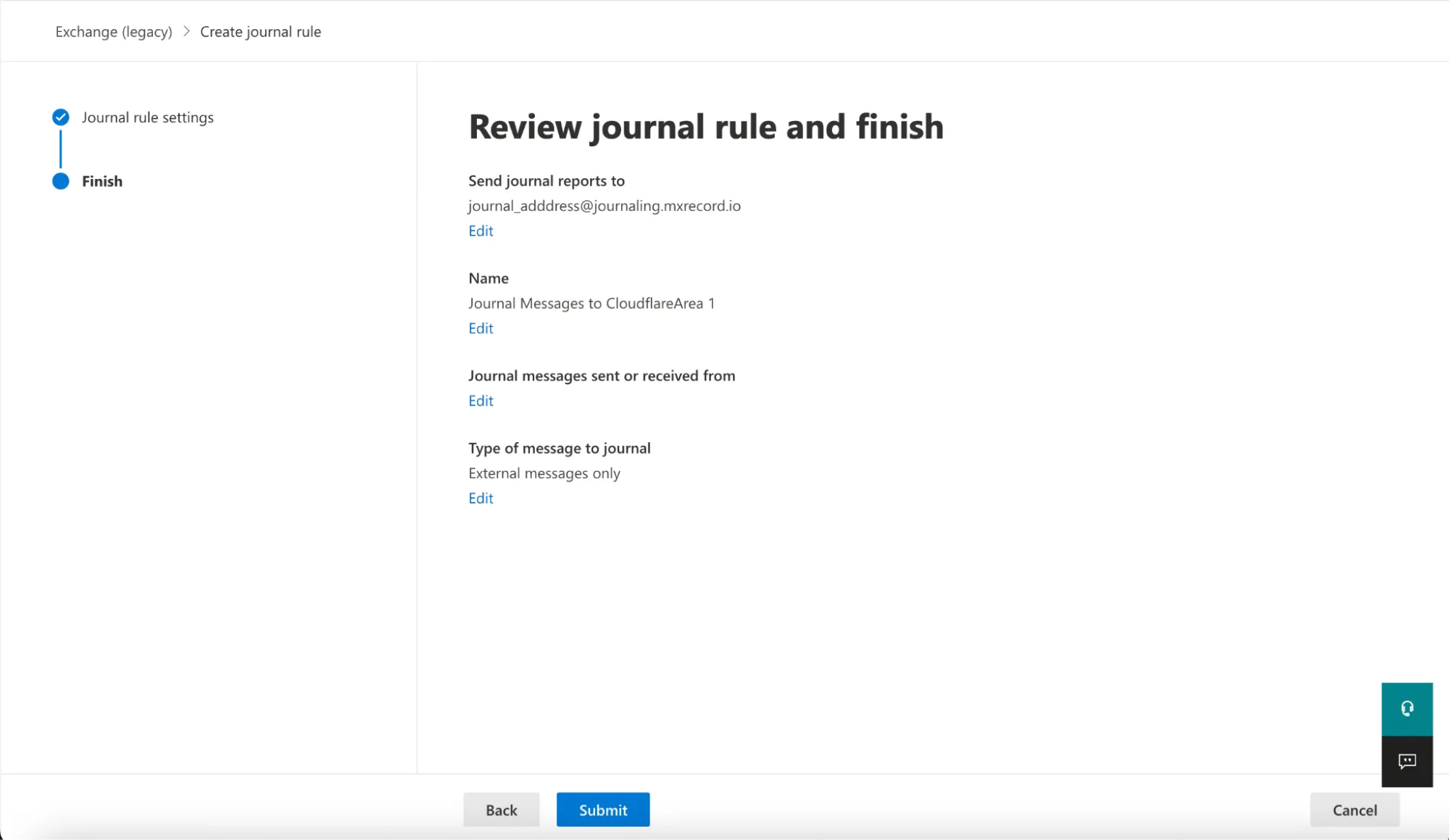
Select New rule to configure a journaling rule, and configure it as follows:
- Send journal reports to: This address is specific to each customer tenant, and can be found in your Email Security dashboard ↗. For example,
<customer_name>@journaling.mxrecord.io. - Journal Rule Name:
Journal Messages to CloudflareArea 1 - Journal messages sent or received from: Everyone
- Type of message to journal: External messages only
- Send journal reports to: This address is specific to each customer tenant, and can be found in your Email Security dashboard ↗. For example,
-
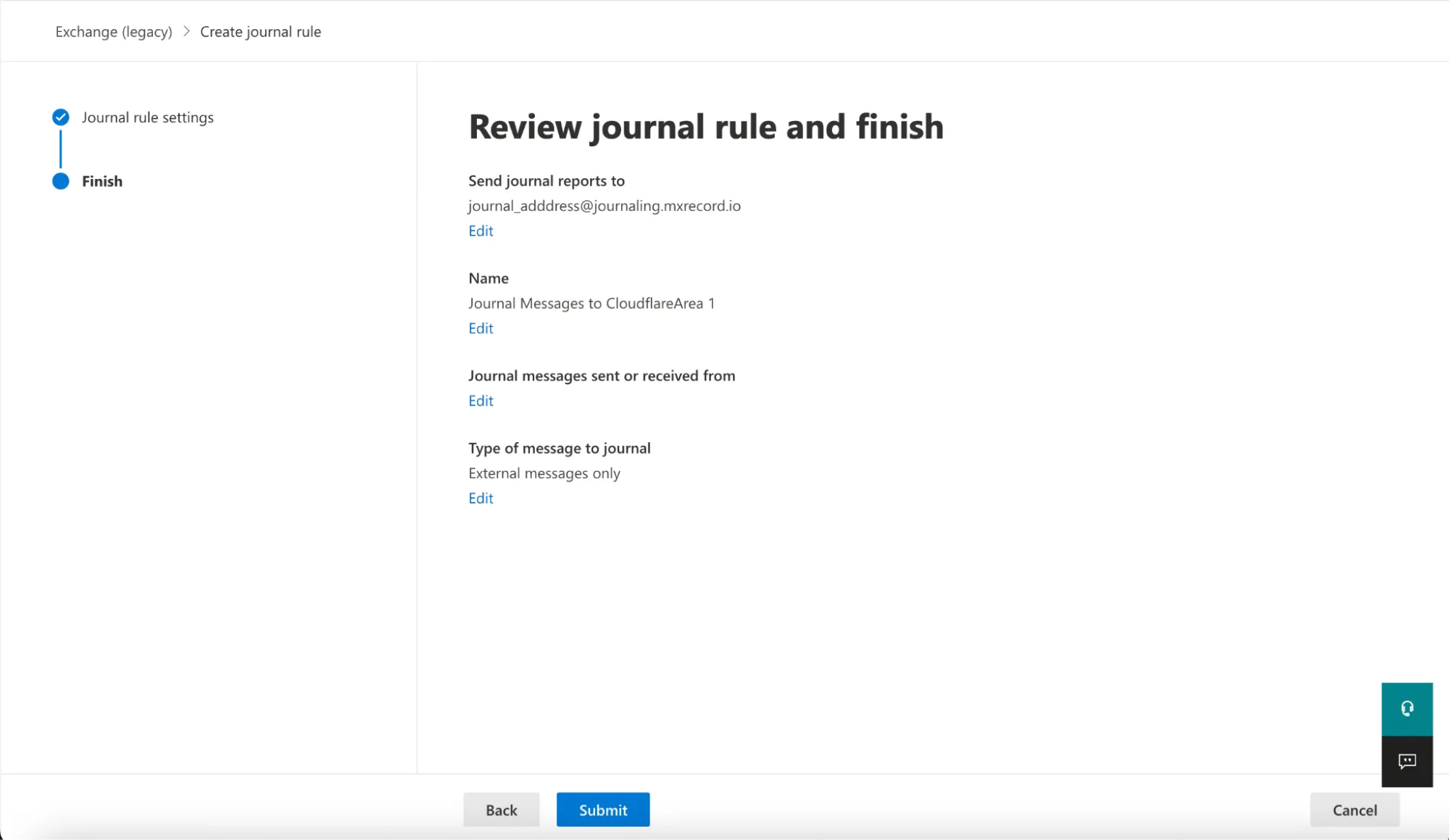
Select Next.
-
Verify the information is correct, and select Submit > Done.
Once saved, the rule is automatically active. However, it may take a few minutes for the configuration to propagate and start pushing messages to Cloudflare Email Security. After it propagates, you can access the Cloudflare Email Security dashboard to check the number of messages processed. This number will grow as journaled messages are sent to Cloudflare Email Security from your Exchange server.
For compliance purposes, you might be required to process emails in certain geographic regions such as India or the EU. If that is your case, you should create Office 365 distribution lists ↗ for each geographic region where you need to process your emails, before configuring your journal rule.
After creating the distribution lists based on regions for your users, configure your journal rule:
-
Log in to the Microsoft Purview compliance portal ↗.
-
Go to Data lifecycle management > Exchange (legacy).
-
Select Settings (the gear icon).
-
In Send undeliverable journal reports to enter the email address of a valid user account. Note that you cannot use a team or group address.
-
Select Save.
-
Still in the Exchange (legacy) screen, select Journal Rules.
-
Select New rule to configure a journaling rule, and configure it as follows:
- Send journal reports to: This address is specific to each customer tenant, and can be found in your Email Security dashboard ↗. If you need to process emails in certain geographic regions, refer to the Geographic locations table for more information on what address you should use.
- Journal Rule Name:
Journal Messages to CloudflareArea 1 - Journal messages sent or received from: A specific user or group and select the user group you created above.
- Type of message to journal: External messages only
-
Select Next.
-
Verify the information is correct, and select Submit > Done.
Once saved, the rule is automatically active. However, it may take a few minutes for the configuration to propagate and start pushing messages to Cloudflare Email Security. After it propagates, you can access the Cloudflare Email Security dashboard to check the number of messages processed. This number will grow as journaled messages are sent to Cloudflare Email Security from your Exchange server.
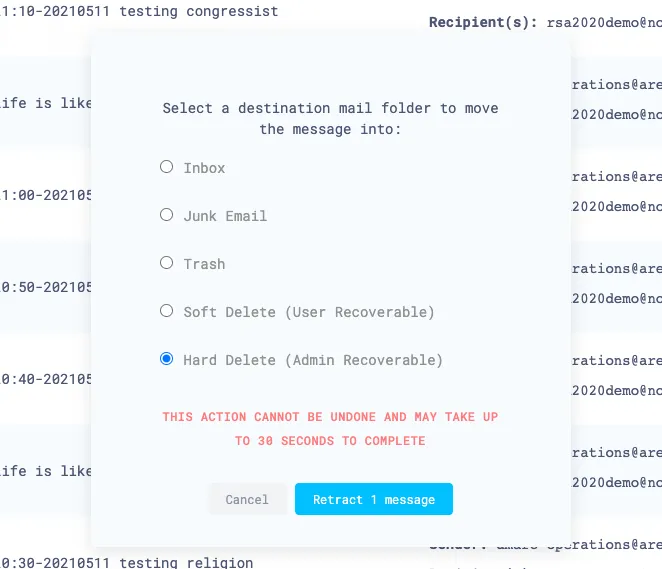
When retraction is enabled, you can manually retract messages that were not automatically retracted.
-
Log in to the Email Security (formerly Area 1) dashboard ↗.
-
Select the search bar and enter the search parameters to find the emails you are looking for.
-
To retract a single message, select Retract. To retract multiple messages, first select the checkboxes on the messages you want to retract. Then, select Retract.
-
Choose where you want to retract the message to, and select Retract message.
-
If the retraction was successful, there will be positive confirmation on Email Security (formerly Area 1) dashboard.
Office 365 has two ways for recovering hard deleted email messages:
Refer to Microsoft's documentation to learn more about how to use these tools to recover deleted email messages.
Select from the following BCC addresses to process email in the correct geographic location.
| Host | Location | Note |
|---|---|---|
<customer_name>@journaling.mxrecord.io | US | Best option to ensure all email traffic processing happens US data centers. |
<customer_name>@journaling.mailstream-eu-primary.mxrecord.io | EU | Best option to ensure all email traffic processing happens in Germany, with backup to US data centers. |
<customer_name>@journaling.mailstream-eu1.mxrecord.io | EU | Best option to ensure all email traffic processing happens within the EU without backup to US data centers. |
<customer_name>@journaling.mailstream-bom.mxrecord.mx | India | Best option to ensure all email traffic processing happens within India. |
<customer_name>@journaling.mailstream-india-primary.mxrecord.mx | India | Same as mailstream-bom.mxrecord.mx, with backup to US data centers. |
<customer_name>@journaling.mailstream-asia.mxrecord.mx | India | Best option to ensure all email traffic processing happens in India, with Australia data centers as backup. |
<customer_name>@journaling.mailstream-syd.area1.cloudflare.net | Australia / New Zealand | Best option to ensure all email traffic processing happens within Australia. |
<customer_name>@journaling.mailstream-australia.area1.cloudflare.net | Australia / New Zealand | Best option to ensure all email traffic processing happens in Australia, with India and US data centers as backup. |