Radar now includes two new charts on the traffic page ↗ that provide deeper insights into the composition of HTTP traffic: a content type distribution chart and an API traffic share chart.
The new Content type ↗ chart displays the distribution of HTTP response content types, grouped into high-level categories. A traffic type selector allows filtering by human, bot, or all traffic. The existing Bot vs. Human ↗ chart also gained a content type category filter, allowing users to see the bot/human split for specific content categories.
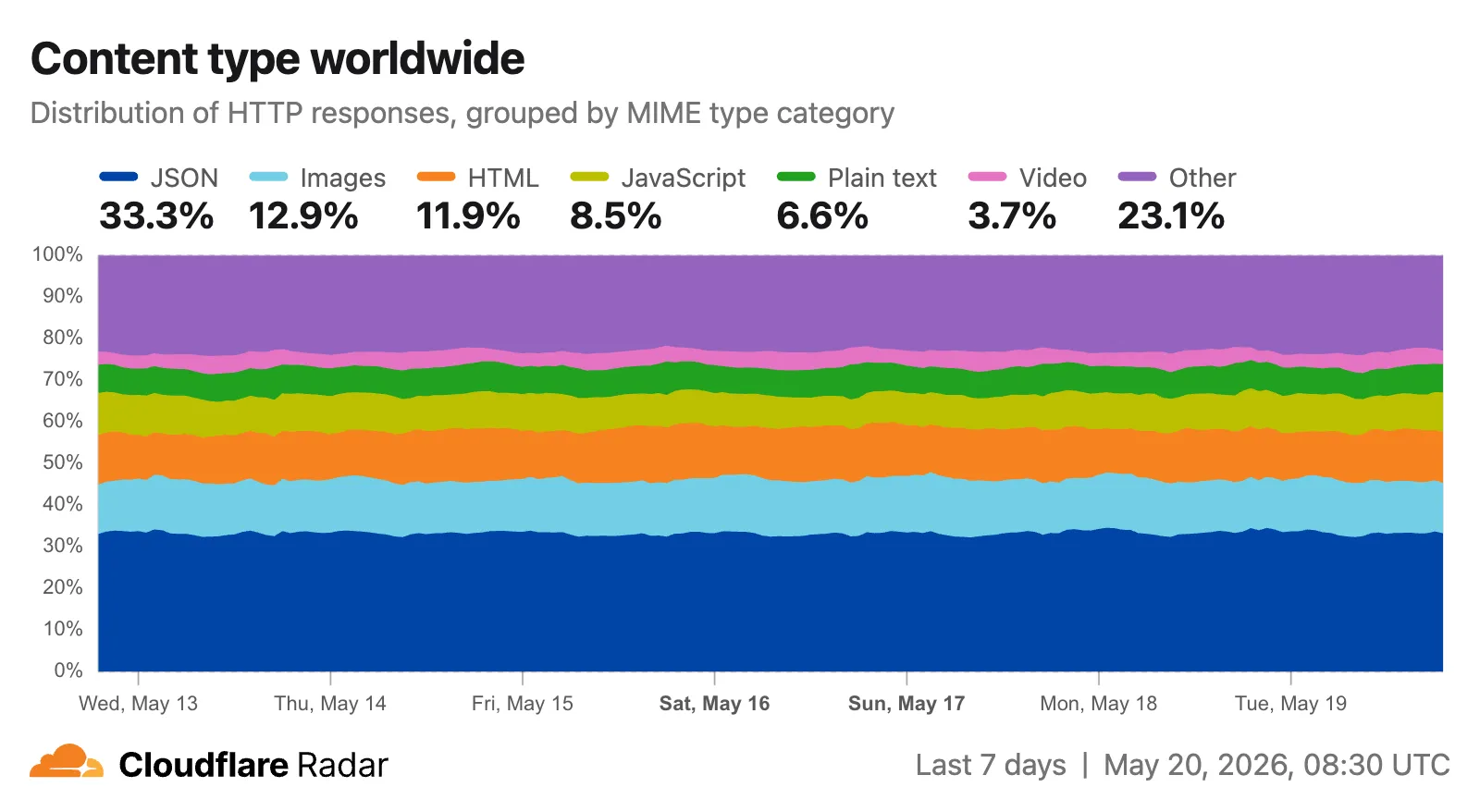
Content type categories:
- HTML — Web pages (
text/html) - Images — All image formats (
image/*) - JSON — JSON data and API responses (
application/json,*+json) - JavaScript — Scripts (
application/javascript,text/javascript) - CSS — Stylesheets (
text/css) - Plain Text — Unformatted text (
text/plain) - Fonts — Web fonts (
font/*,application/font-*) - XML — XML documents and feeds (
text/xml,application/xml,application/rss+xml,application/atom+xml) - YAML — Configuration files (
text/yaml,application/yaml) - Video — Video content and streaming (
video/*,application/ogg,*mpegurl) - Audio — Audio content (
audio/*) - Markdown — Markdown documents (
text/markdown) - Documents — PDFs, Office documents, ePub, CSV (
application/pdf,application/msword,text/csv) - Binary — Executables, archives, WebAssembly (
application/octet-stream,application/zip,application/wasm) - Serialization — Binary API formats (
application/protobuf,application/grpc,application/msgpack) - Other — All other content types
The
CONTENT_TYPEdimension andcontentTypefilter are available on the HTTP summary, timeseries groups, and timeseries endpoints.The new API traffic ↗ chart shows the percentage of dynamic (non-cacheable) HTTP request traffic that is API-related. API traffic is identified by JSON or XML response content types (
application/json,application/xml,text/xml) on HTTP requests that returned a 200 status code. A traffic type selector allows switching between human traffic, bot traffic, or all traffic.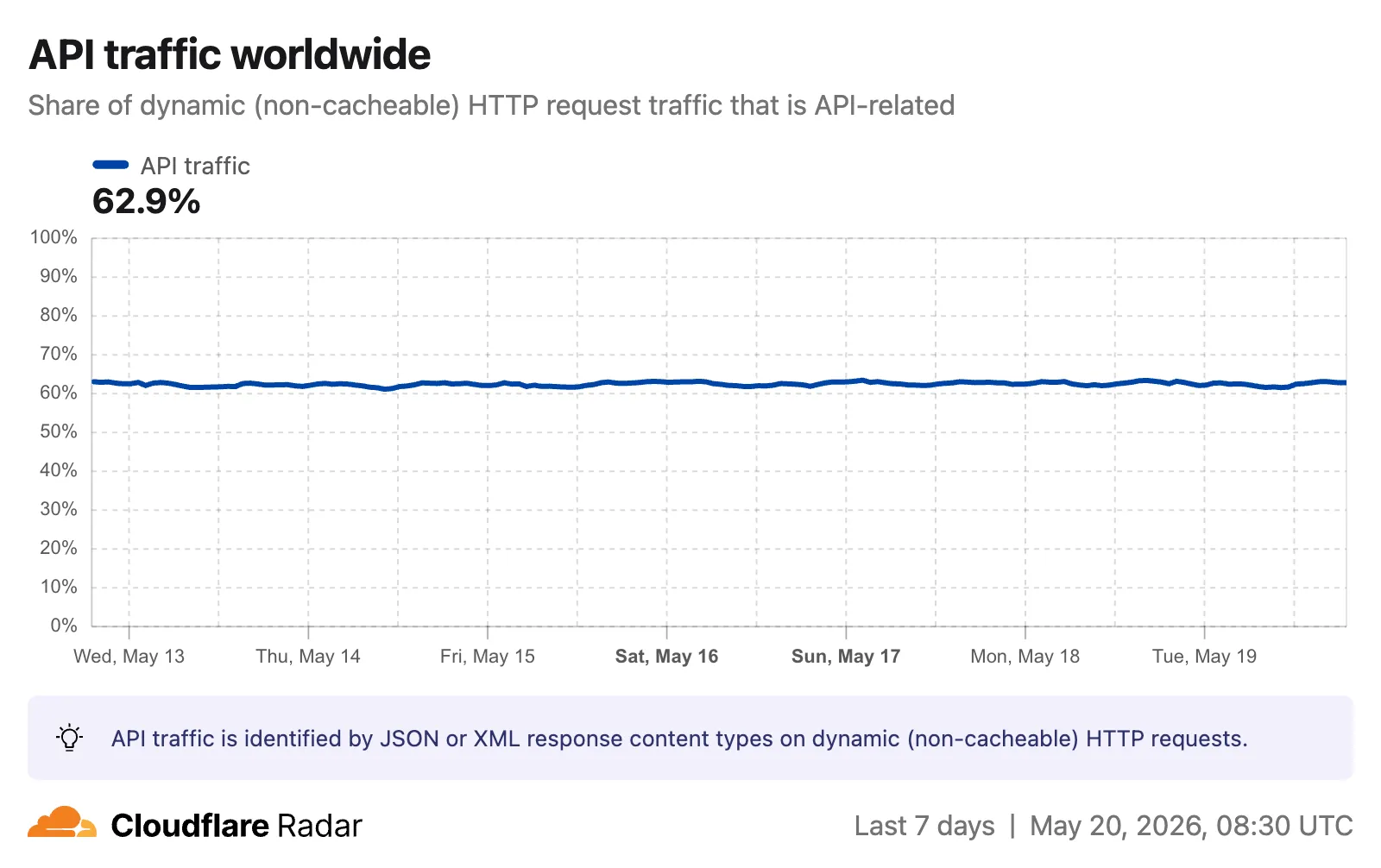
The
API_TRAFFICdimension is available on the existing HTTP summary and timeseries groups endpoints. AnapiTrafficfilter (APIorNON_API) can also be applied to HTTP timeseries requests to retrieve raw request counts for API-only or non-API traffic.Visit the Radar traffic page ↗ to explore these new charts.
- HTML — Web pages (
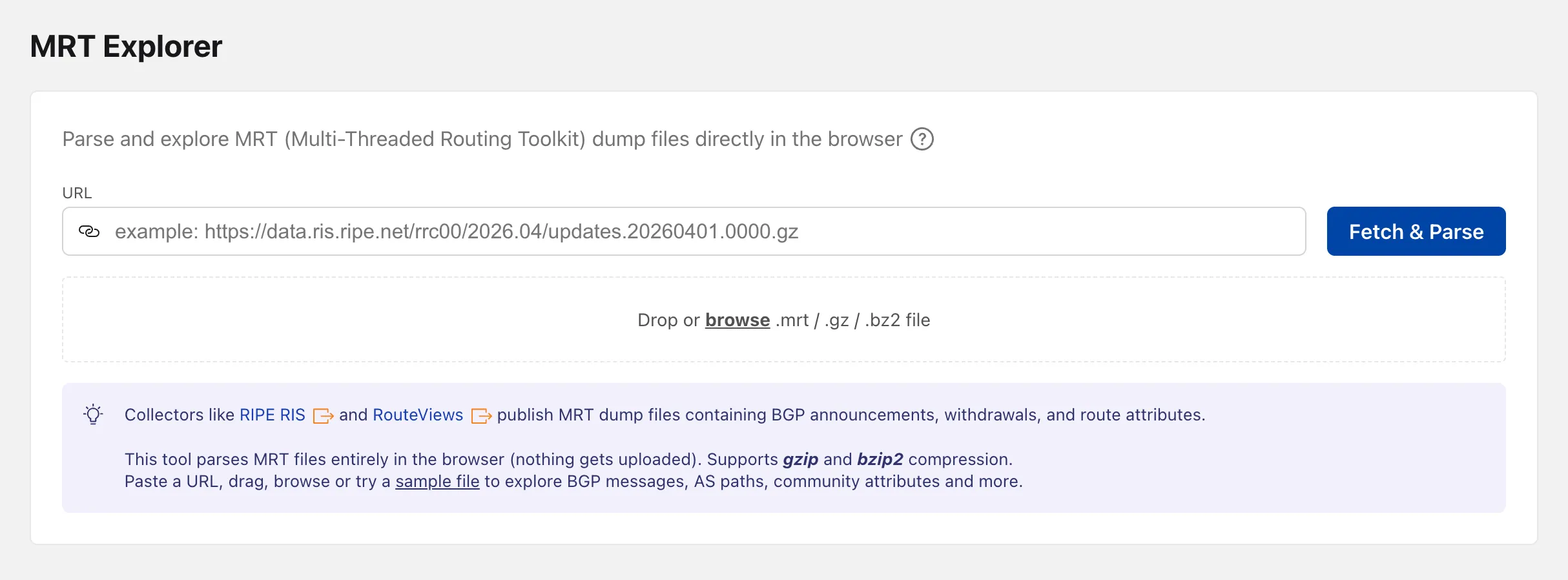
Radar now includes an MRT Explorer ↗ tool in the Routing section. Route collectors like RIPE RIS and RouteViews publish MRT (Multi-Threaded Routing Toolkit) dump files containing BGP announcements, withdrawals, and route attributes. The new tool parses these files entirely in the browser — nothing gets uploaded.
Paste a URL to fetch an MRT file remotely, drag and drop one onto the page, or browse for a local file. Gzip and bzip2 compressed files are supported. A sample file is also available to get started right away.
Once parsed, the tool lists every BGP event with its timestamp, prefix, AS path, OTC (Only to Customer), and community attributes.
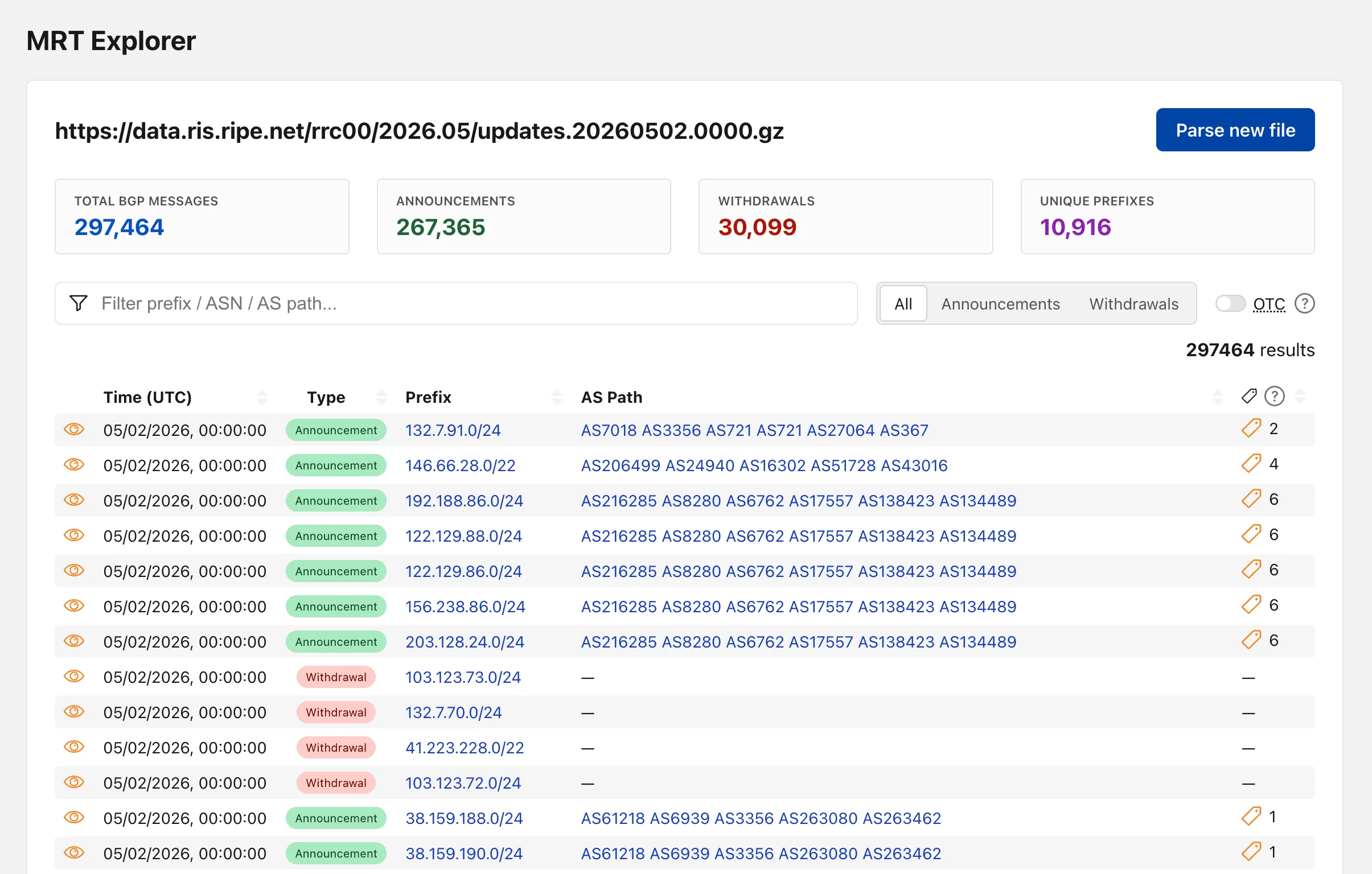
Clicking on the "View details" action opens a modal with additional properties and the full event JSON.
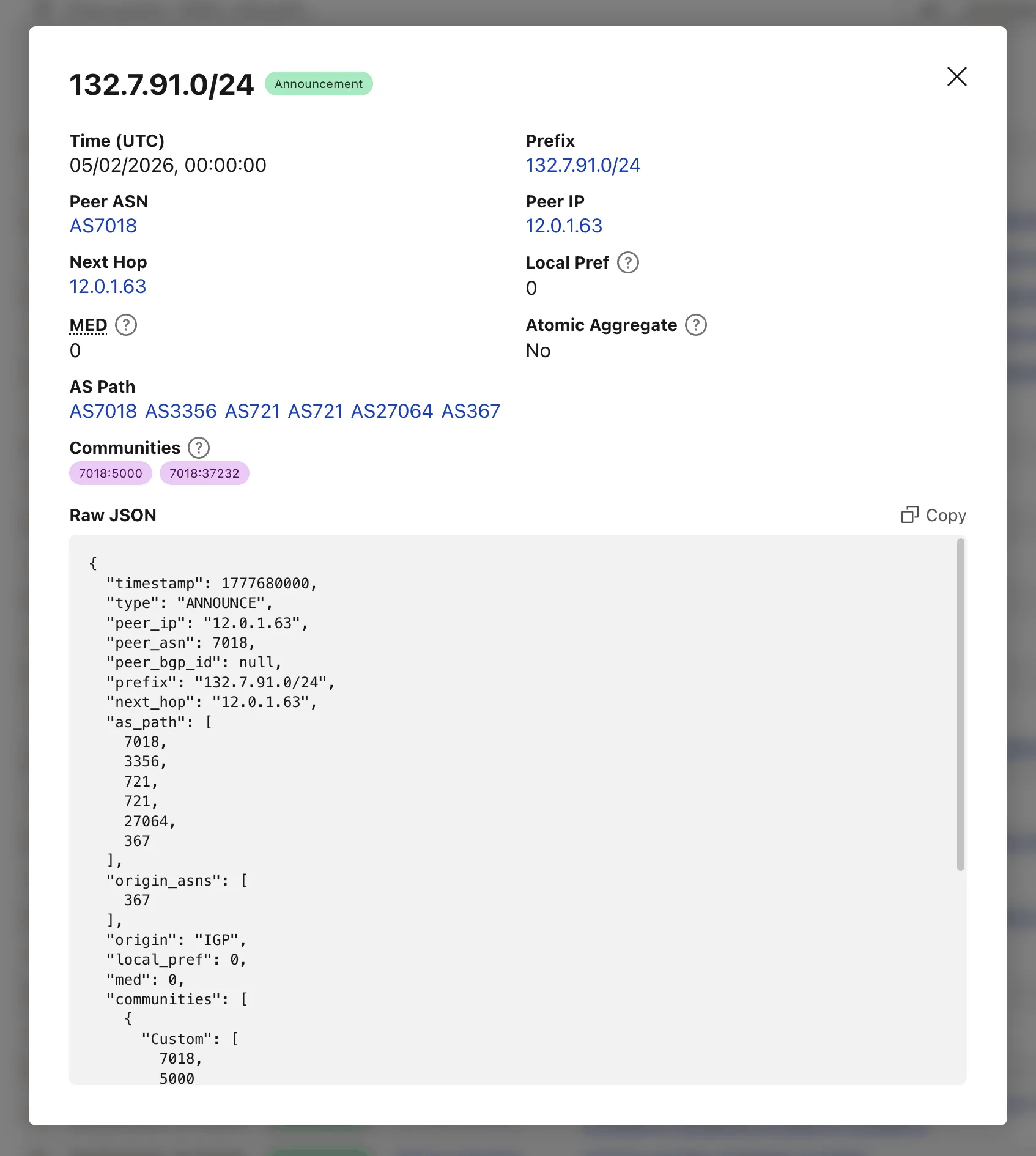
When loading a file by URL, the query string captures the source so the link can be shared directly — the recipient's browser immediately fetches and parses the same file.
Try the MRT Explorer on Cloudflare Radar ↗.
Cloudflare has updated Logpush datasets:
- Email Security Post-Delivery Events: A new dataset with fields including
AlertID,CompletedAt,Destination,FinalDisposition,Folder,From,FromName,MessageID,MessageTimestamp,MicrosoftTenantID,Operation,PostfixID,Reasons,Recipient,RequestedAt,RequestedBy,RequestedDisposition,Status,Subject,Success, andTo. - Magic Network Monitoring Flow Logs: A new dataset with fields including
AWSVPCFlowJSON,Bits,DestinationAS,DestinationAddress,DestinationPort,DeviceID,EgressBits,EgressPackets,Ethertype,FlowProtocol,FlowTimestamp,NumFlows,PacketID,Packets,Protocol,RuleIDs,SampleRate,SampleRateType,SamplerAddress,SourceAS,SourceAddress,SourcePort,TcpFlags, andTimestamp.
- Firewall events (added):
AISecurityInjectionScore,AISecurityPIICategories,AISecurityTokenCount, andAISecurityUnsafeTopicCategories. - HTTP requests (added):
AISecurityInjectionScore,AISecurityPIICategories,AISecurityTokenCount,AISecurityUnsafeTopicCategories, andSubrequests.
For the complete field definitions for each dataset, refer to Logpush datasets.
- Email Security Post-Delivery Events: A new dataset with fields including
The
/cdn-cgi/rumbeacon endpoint now returns405 Method Not Allowedfor non-POST requests instead of404 Not Found. The response includes anAllow: POST, OPTIONSheader per RFC 9110 §15.5.6 ↗.Previously, sending a
GETor other non-POST request to this endpoint returned a404, which was misleading because it suggested the endpoint did not exist. The new405response clearly indicates that the endpoint exists but only acceptsPOSTrequests.The Web Analytics beacon (
beacon.min.js) already usesPOSTfor all metric submissions, so this change does not affect normal beacon operation.OPTIONSrequests for CORS preflight continue to work as before.For more information, refer to the Web Analytics FAQ.
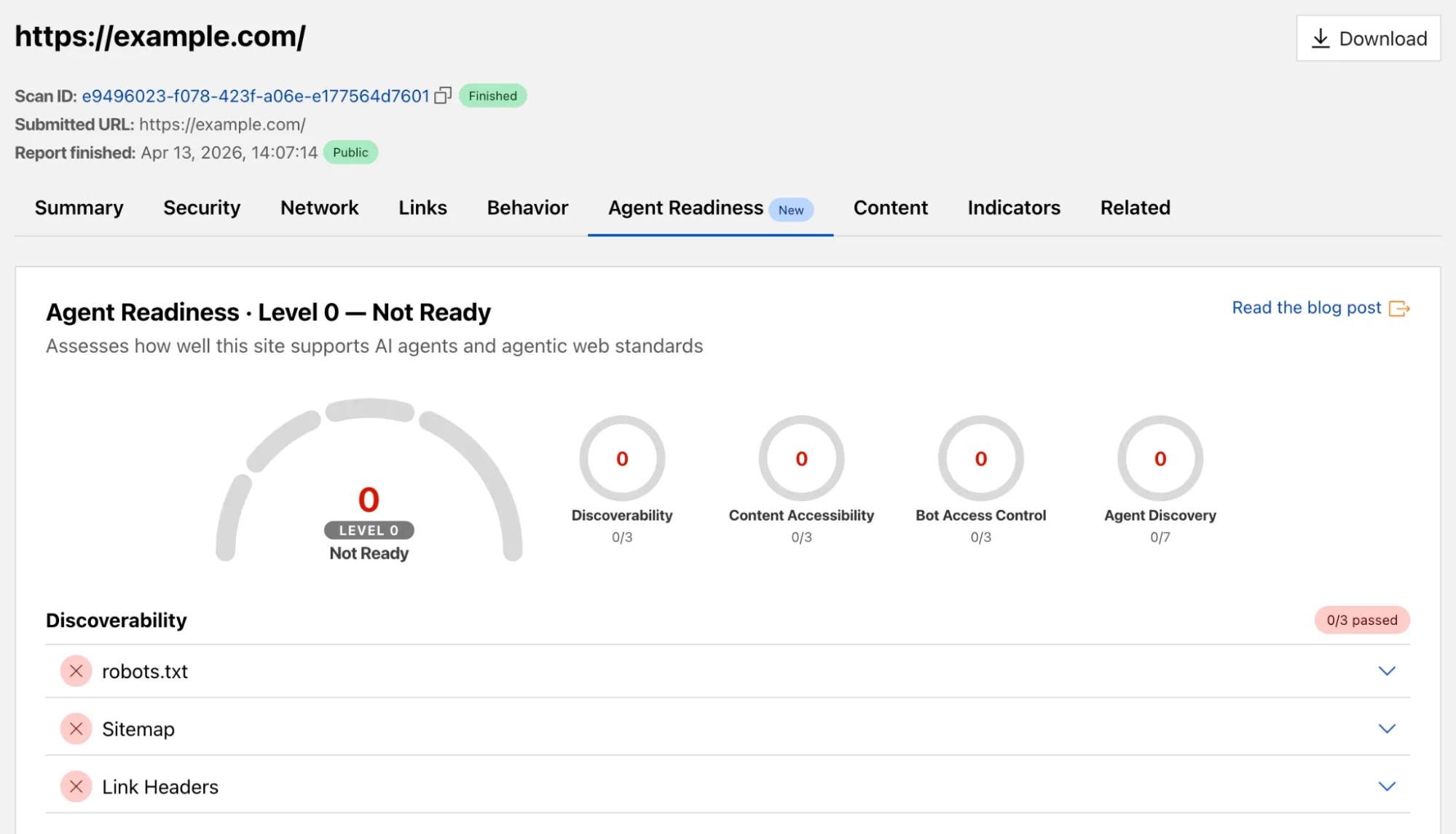
We’ve added a new Agent Readiness tab to URL Scanner reports accessible via the Cloudflare dashboard. This feature evaluates your site against emerging AI standards and provides six specialized scores to help you optimize for the next generation of AI agents and automated discovery.
The Internet is shifting from a human-read web to a machine-read web. AI agents now browse, interact with, and even perform transactions on websites. If a site isn't "agent-ready," these bots may consume excessive bandwidth, fail to find critical information, or be unable to navigate your services efficiently.
This update provides material value by breaking down readiness into six actionable categories:
- Basic Web Presence
- Discoverability
- Content Accessibility
- Bot Access Control
- Protocol Discovery
- Commerce
You can view these scores for any scanned URL directly in the dashboard or via our API.
- Dashboard: Go to Protect & Connect > Application Security > Investigate. After running a scan, select the Agent Readiness tab in the report.
- API: Use the URL Scanner API ↗ to programmatically retrieve these scores for your infrastructure.
To learn more about the methodology behind these scores, refer to the blogpost ↗.
You can now export your Requests for Information (RFI) history to a CSV document and customize your dashboard view by choosing how many RFI records to load per page.
These quality-of-life updates focus on data portability and dashboard performance, allowing power users to manage high volumes of requests more efficiently:
- The new CSV export allows you to move RFI data into external tools for custom reporting, internal auditing, or cross-referencing with other security projects without manual data entry
- With adjustable page density, you can now choose to load more records at once (10, 25 or 50) to scan through history faster
Cloudforce One subscribers can find these new options in Cloudflare Dashboard > Application Security > Threat Intelligence > Requests for Information ↗.
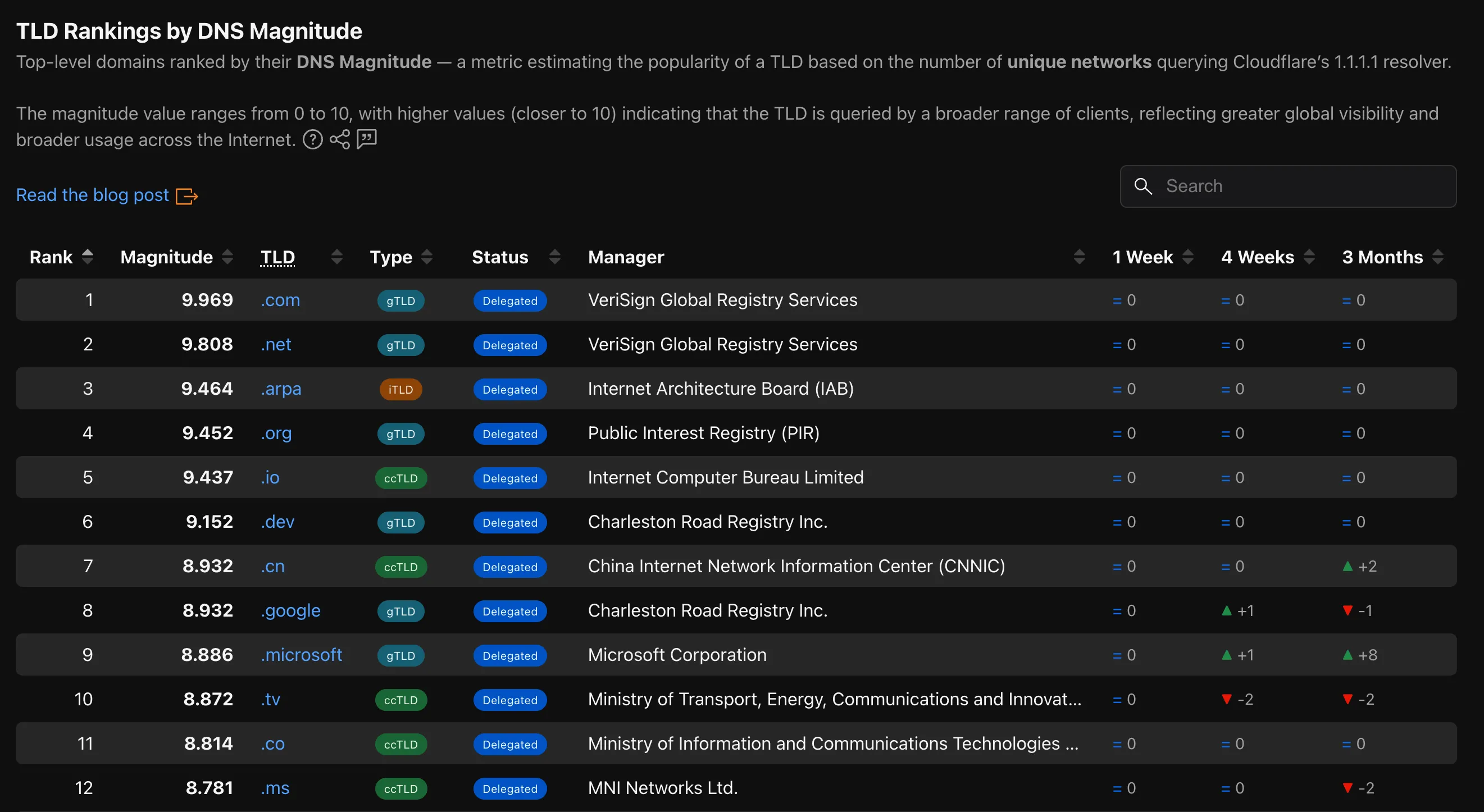
Radar now provides TLD authoritative nameserver performance insights, measuring response time (latency) as observed from Cloudflare's 1.1.1.1 resolver infrastructure when forwarding queries upstream to TLD nameservers.
New widgets on TLD detail pages ↗:
- Aggregate nameserver latency ↗: Response time percentiles (p25/p50/p75) for all authoritative nameservers of the selected TLD.
- Latency per nameserver ↗: Median response time (p50) broken down by each authoritative nameserver over time.
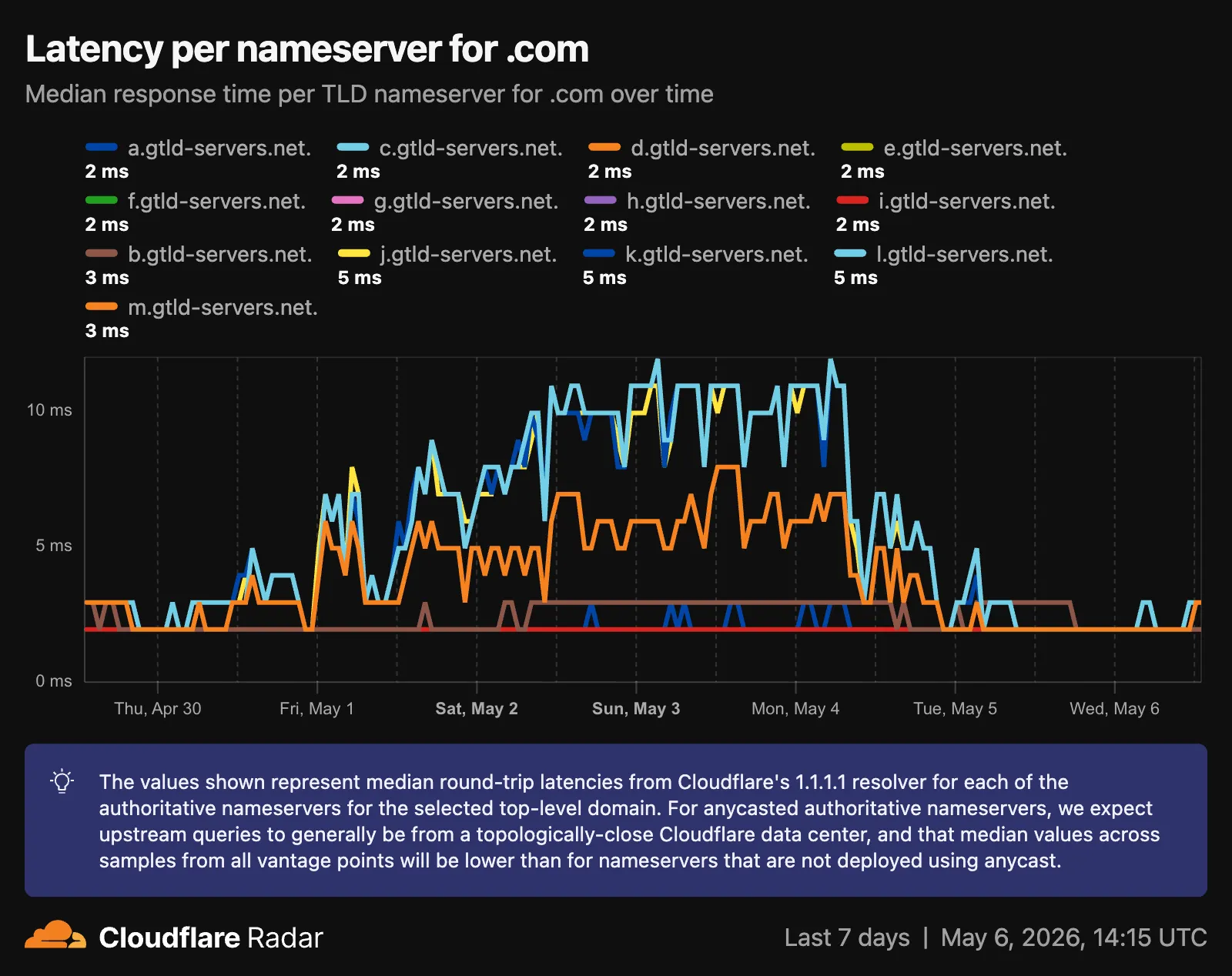
- Median latency geographic distribution ↗: p50 response time by Cloudflare data center country, displayed on a choropleth map.
- TLD ranking over time ↗: Daily DNS magnitude rank and magnitude value with a Rank/Magnitude toggle.
- Rank change deltas ↗: 1 week, 4 weeks, and 3 months rank changes added to the TLD magnitude table and the TLD detail info panel.
The new
TLD PerformanceAPI provides the following endpoints:/tlds/performance/summary/{dimension}— TLD nameserver performance summarized by dimension./tlds/performance/timeseries_groups/{dimension}— TLD nameserver performance over time grouped by dimension.
Available dimensions:
LATENCY(aggregate p25/p50/p75),NAMESERVER_LATENCY(per-nameserver p50),LOCATION_LATENCY(per-data-center-country p50).TLD Performance is also available as a dataset in the Data Explorer ↗.
Check out the updated TLD detail page ↗.
The Cloudforce One Threat Events API now supports TAXII ↗ as an output format, enabling standardized, automated sharing of cyber threat intelligence with your existing security stack.
- You can now ingest Cloudforce One threat data directly into your SIEM, TIP or SOAR tools that prefer TAXII-formatted streams without needing custom translation scripts.
- By supporting the TAXII format parameter in our API, security teams can automate the synchronization of indicator data, reducing the manual overhead of updating blocklists and detection rules.
- This alignment with industry standards ensures that your threat data remains consistent across different security ecosystems and partner integrations.
When calling the Threat Events API, you can now specify
taxiiin theformatquery parameter:GET /accounts/{account_id}/cloudforce_one/threat_events?format=taxiiYou can find the updated documentation in the Cloudflare API Reference ↗.
Radar is expanding its Routing section ↗ with two new widgets that give a deeper view into how networks announce address space and how RPKI ROA coverage evolves over time.
Country routing pages now include a Top ASes by announced IP space chart, breaking down the IPv4 and IPv6 address space announced from a country across the autonomous systems that originate it. The chart stacks the IPv4 and IPv6 views vertically, with the top contributing ASes called out by color and the remaining networks aggregated as Other.

The RPKI sub-page ↗ adds an RPKI ROA deployment timeseries widget that tracks the share of announced BGP space covered by a valid Route Origin Authorization (ROA) over time, with separate IPv4 and IPv6 lines. A toggle switches the view between the share of covered prefixes and the share of covered IP address space. The widget is available on global, country, and AS views, so operators can monitor RPKI adoption progress and compare deployment trends across different scopes.
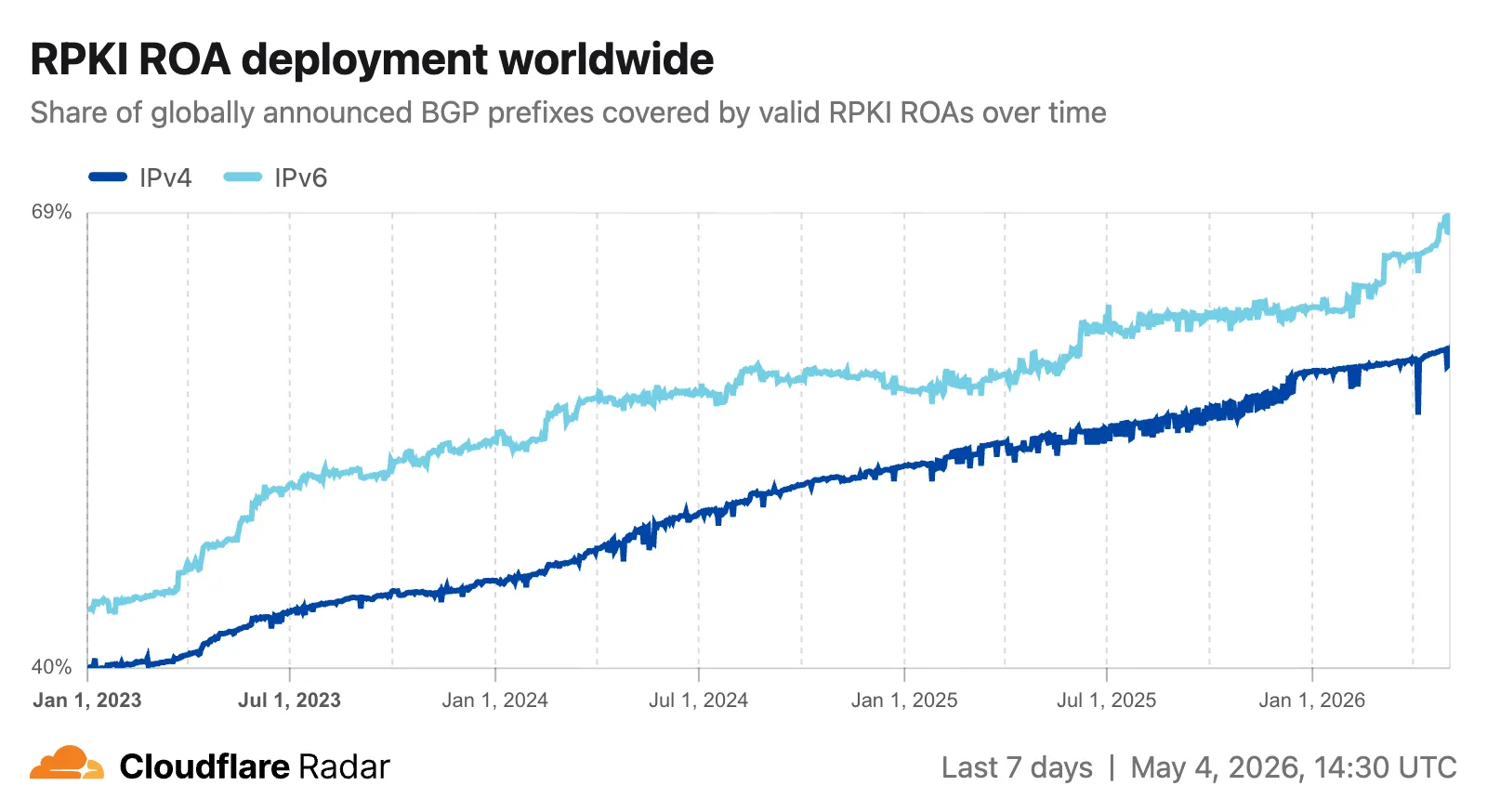
The data behind these widgets is also available through two new endpoints on the
BGPAPI:/bgp/ips/top/ases- Returns the top autonomous systems by announced IP space (IPv4/24s or IPv6/48s), globally or filtered by country, snapped to the nearest 8-hour RIB boundary./bgp/rpki/roas/timeseries- Returns RPKI ROA validation coverage over time, by share of prefixes or share of IP address space, split by IP version, with optional ASN or location filters.
Visit the Radar routing section ↗ to explore both widgets.
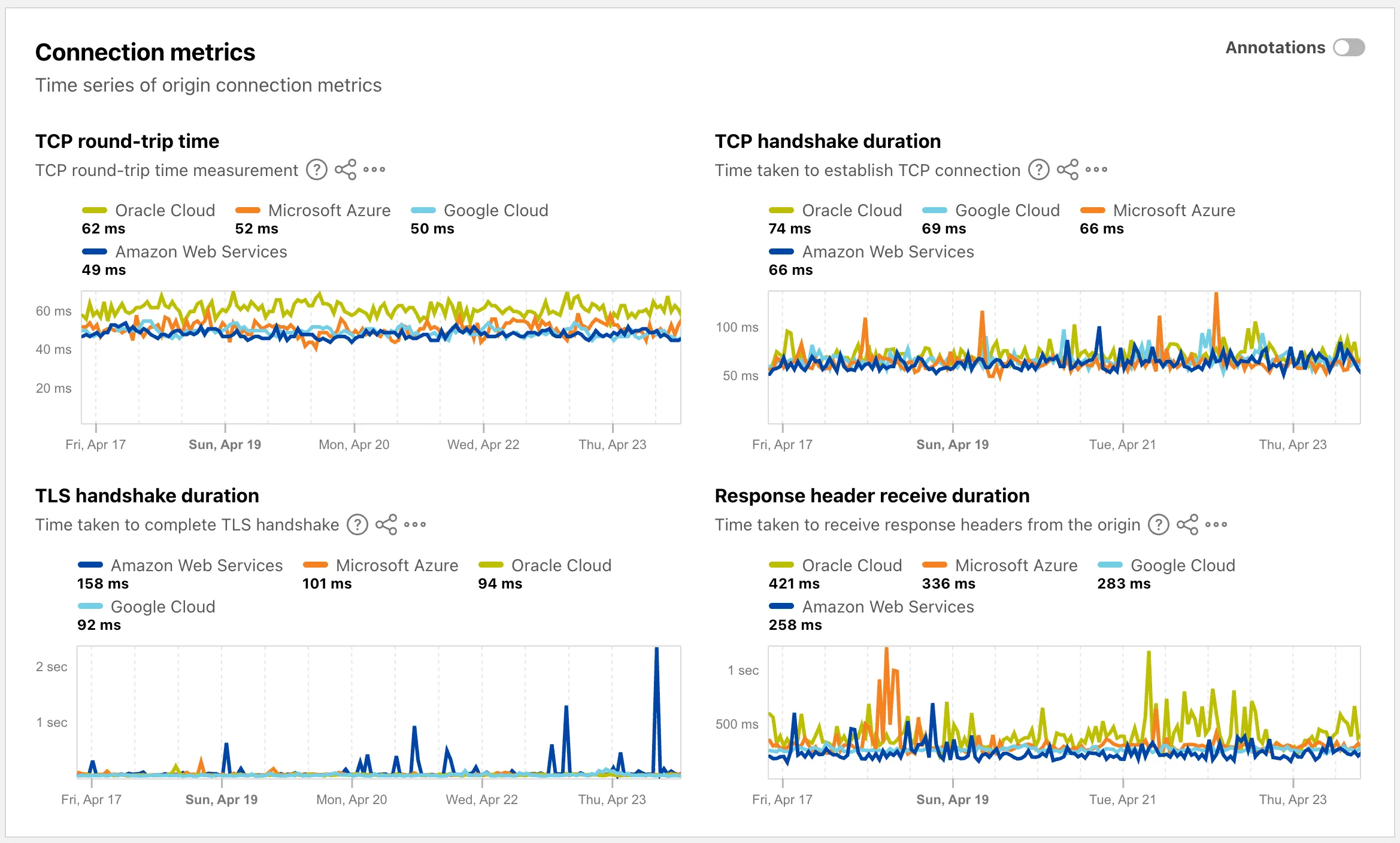
The Cloud Observatory ↗ on Radar now provides improved connection metric insights, offering new ways to explore TCP round-trip time, TCP handshake duration, TLS handshake duration, and response header receive duration across cloud provider origin servers.
The Cloud Observatory overview ↗ now shows connection metrics broken down by cloud provider, making it easy to compare connection performance across Amazon Web Services, Google Cloud, Microsoft Azure, and Oracle Cloud.
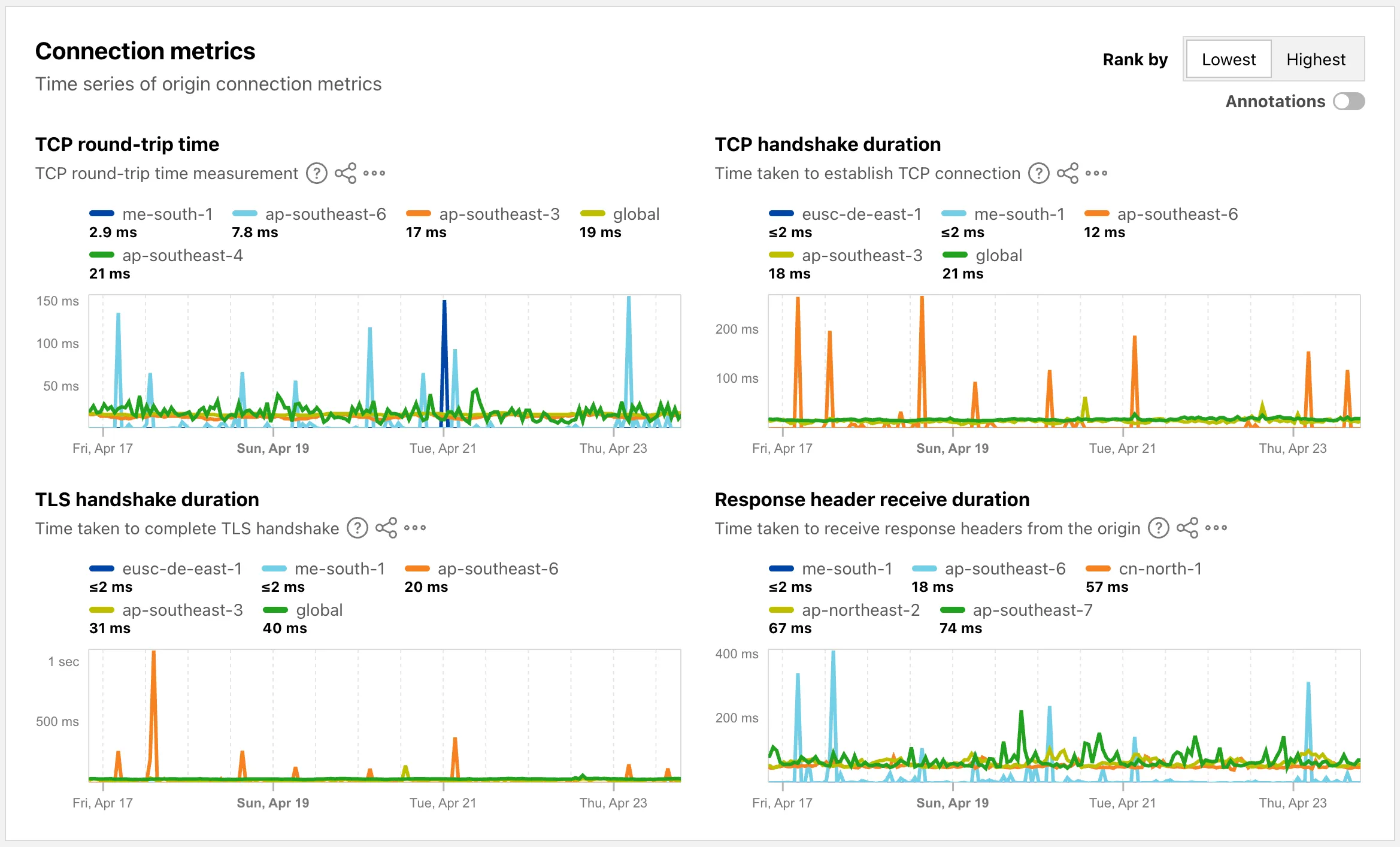
Each provider page ↗ now shows connection metrics for the top five regions, with a selector to rank by lowest or highest values.
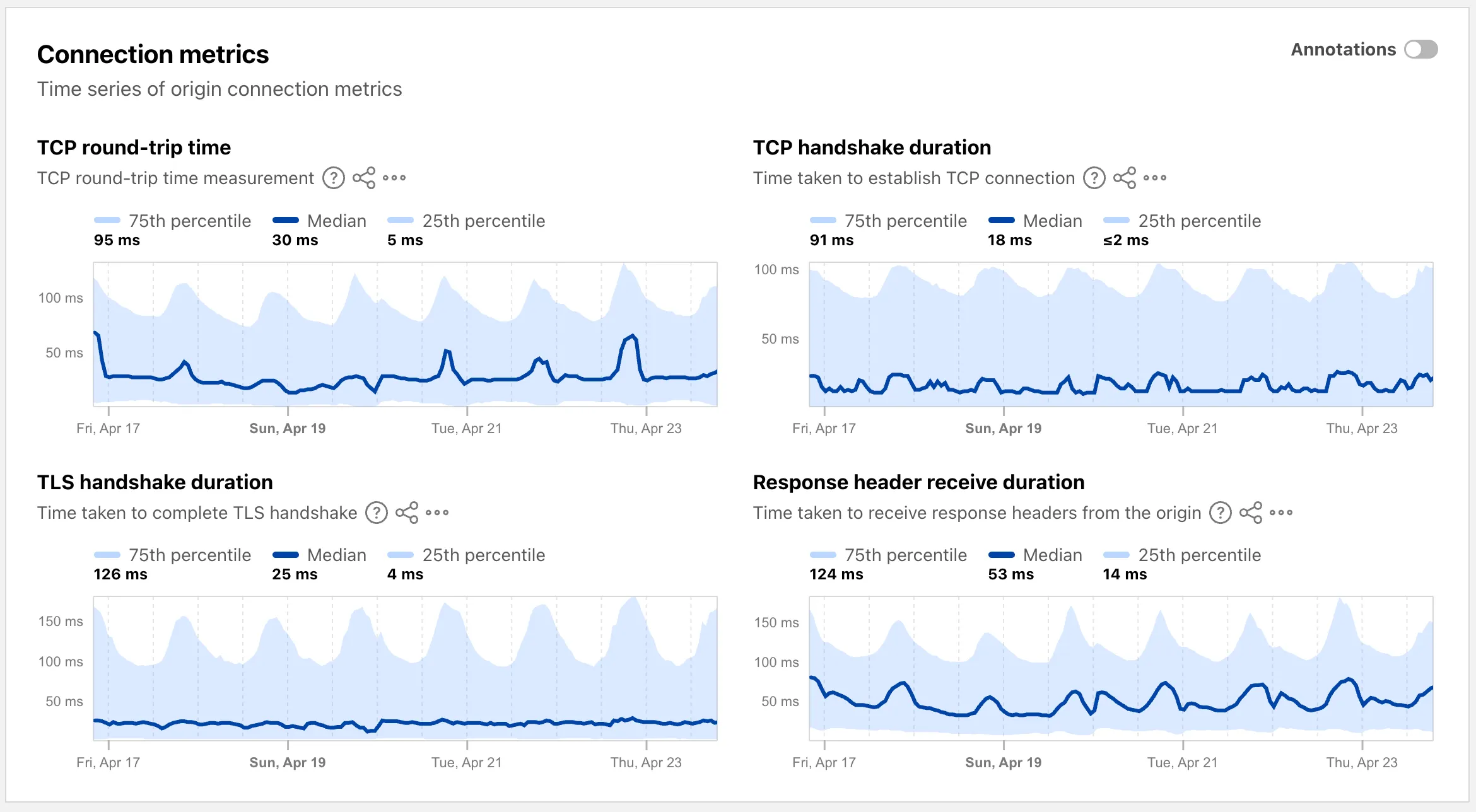
Each region page ↗ now displays connection metrics as percentile distributions (25th percentile, median, and 75th percentile), providing insight into the range and variability of connection times.
These views are also available through the
OriginsAPI, using thetimeseries_groupsendpoint with theORIGIN,REGION, orPERCENTILEdimension.
Radar now supports dark mode. A theme selector in the upper right corner of the page lets users explicitly choose between three display options:
- Light — standard light theme
- Dark — full dark theme
- System — follows the operating system preference
The selected theme applies consistently across all Radar pages and widgets.
The theme choice also applies to shared and embedded graphs.
Try it out at Cloudflare Radar ↗.
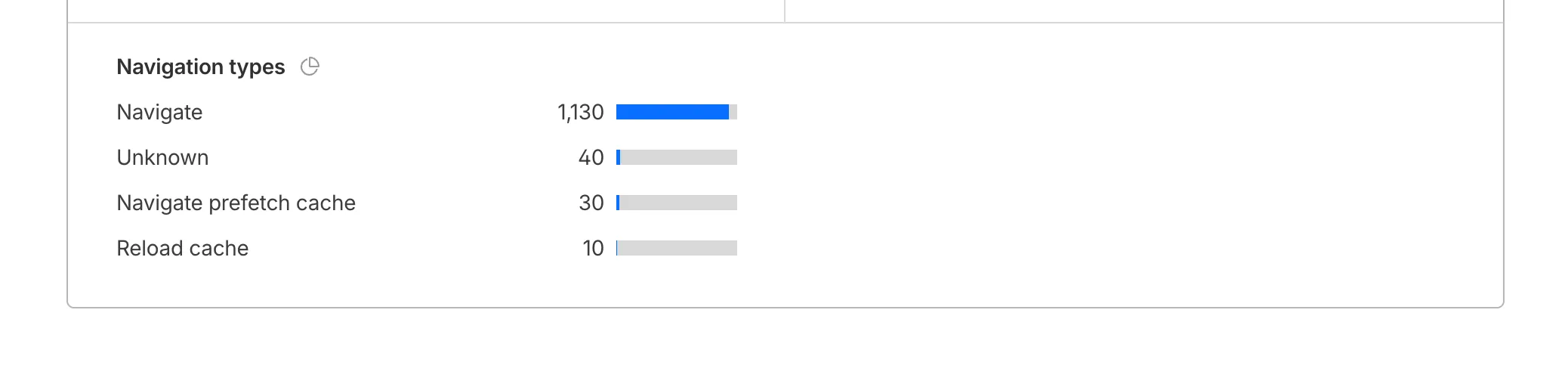
Cloudflare Web Analytics now supports Navigation Type reporting and filtering.
This update allows developers and performance analysts to see how users are navigating between pages — whether through a link click or form submission, a page reload, or using the browser's back/forward buttons — and whether a browser cache hit occurred for these behaviors.
Understanding navigation types is critical for optimizing user experience. For example, if a high volume of your traffic consists of "Back-forward" navigations versus "Back-forward Cache", those visitors are not benefiting from the Back/Forward Cache (bfcache) and therefore are experiencing higher load times due to potentially unnecessary network requests.
The same applies for regular "Navigate" entries — where "Navigate Cache", "Navigate Prefetch Cache" and "Prerender" would provide instant document retrieval — and "Reload", where "Reload cache" would be more optimal.
A high volume of "Reload" entries can also indicate a potential stability problem with your website.
By identifying these patterns, you can tune your browser caching strategies to ensure HTML documents are served instantaneously from local caches rather than requiring a roundtrip to the network.
For more information, refer to Navigation Types.
- Monitor Cache Effectiveness: See how often your site is served from the HTTP cache or bfcache.
- Identify Performance Bottlenecks: Filter by the different types to understand performance opportunity of improving browser cache hit ratio.
You can now find the Navigation Type dimension in the Web Analytics dashboard. You can filter to include/exclude one or more specific types using "equals", "does not equal", "in", or "not in" matchers.

To check the list of popular navigation types, select Page views on the Web Analytics sidebar and scroll down to the bottom:
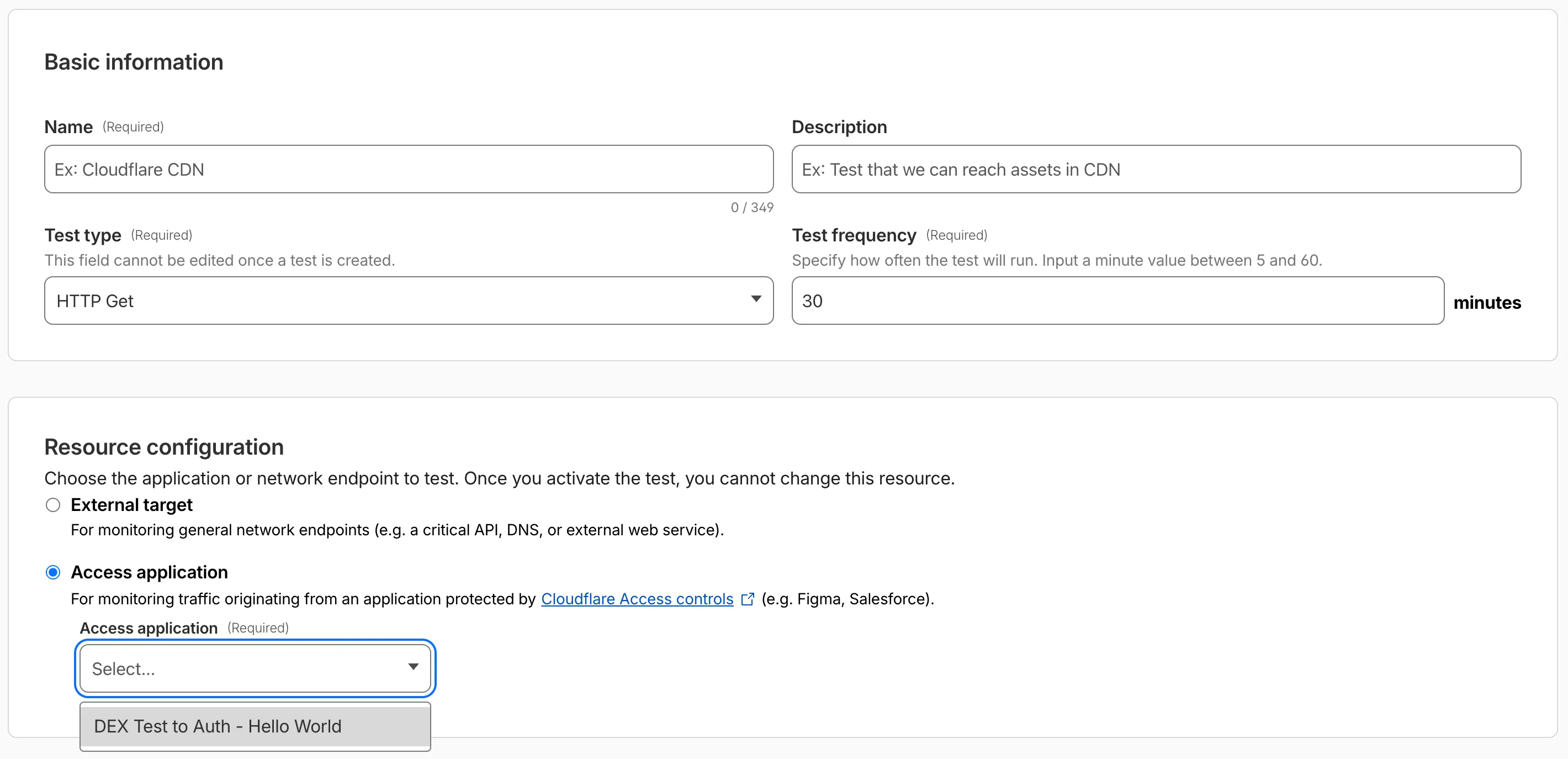
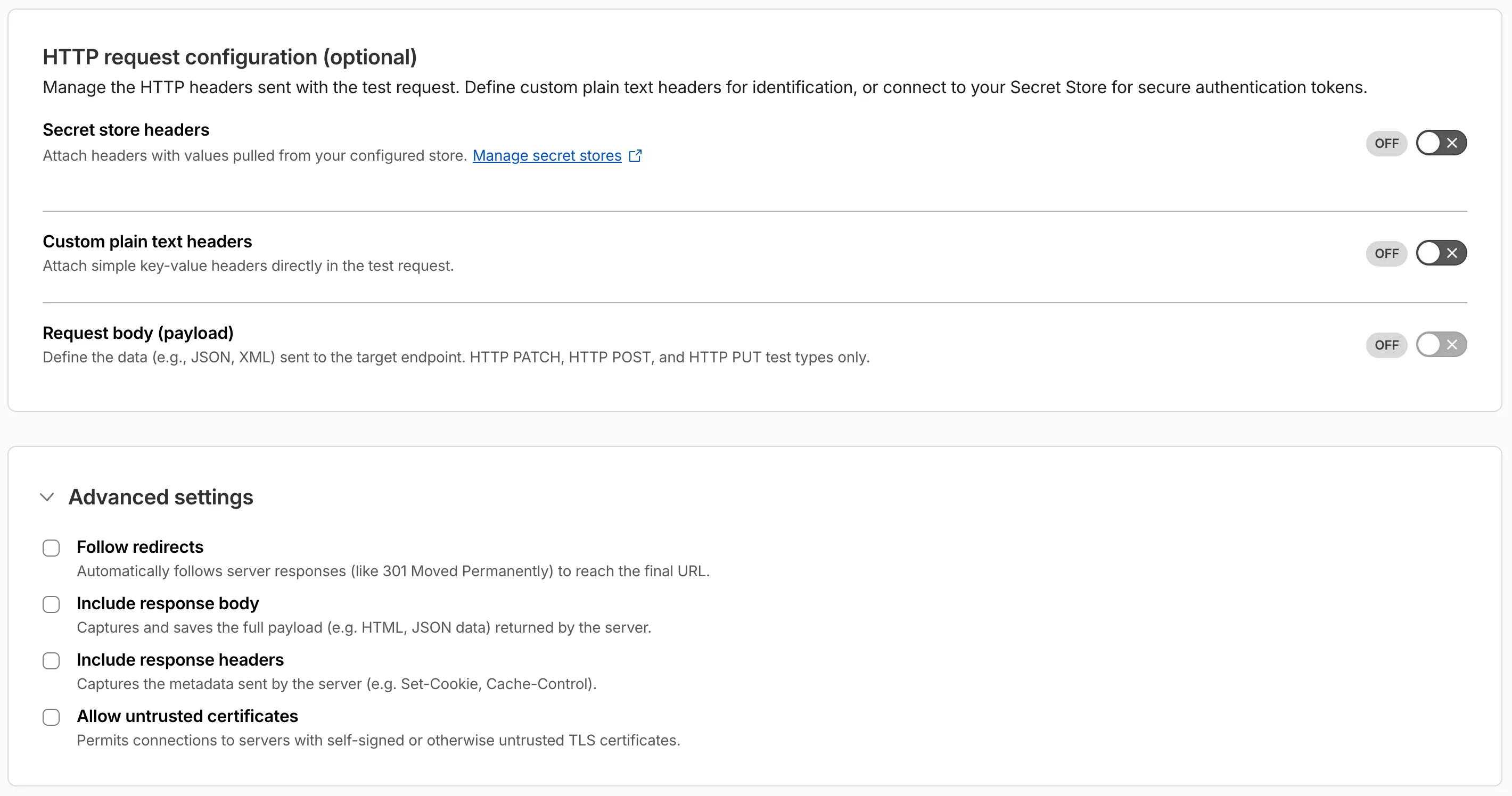
Digital experience tests now support testing applications protected by Cloudflare Access or third-party authentication. All authentication secrets are managed via Cloudflare Secret Store.
Digital experience tests also have enhanced configuration options including:
- New HTTP methods (DELETE, PATCH, POST, PUT)
- Secret Store headers, custom plain text headers, and custom request bodies
- Advanced settings: follow redirects, response bodies, response headers, and allow untrusted certificates
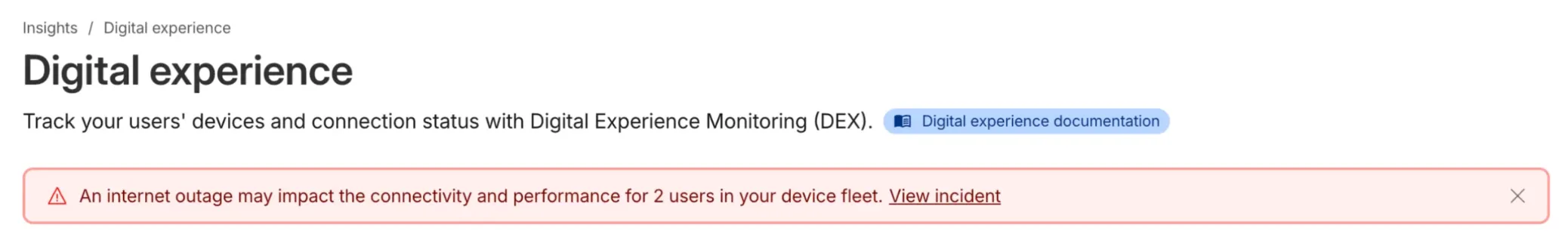
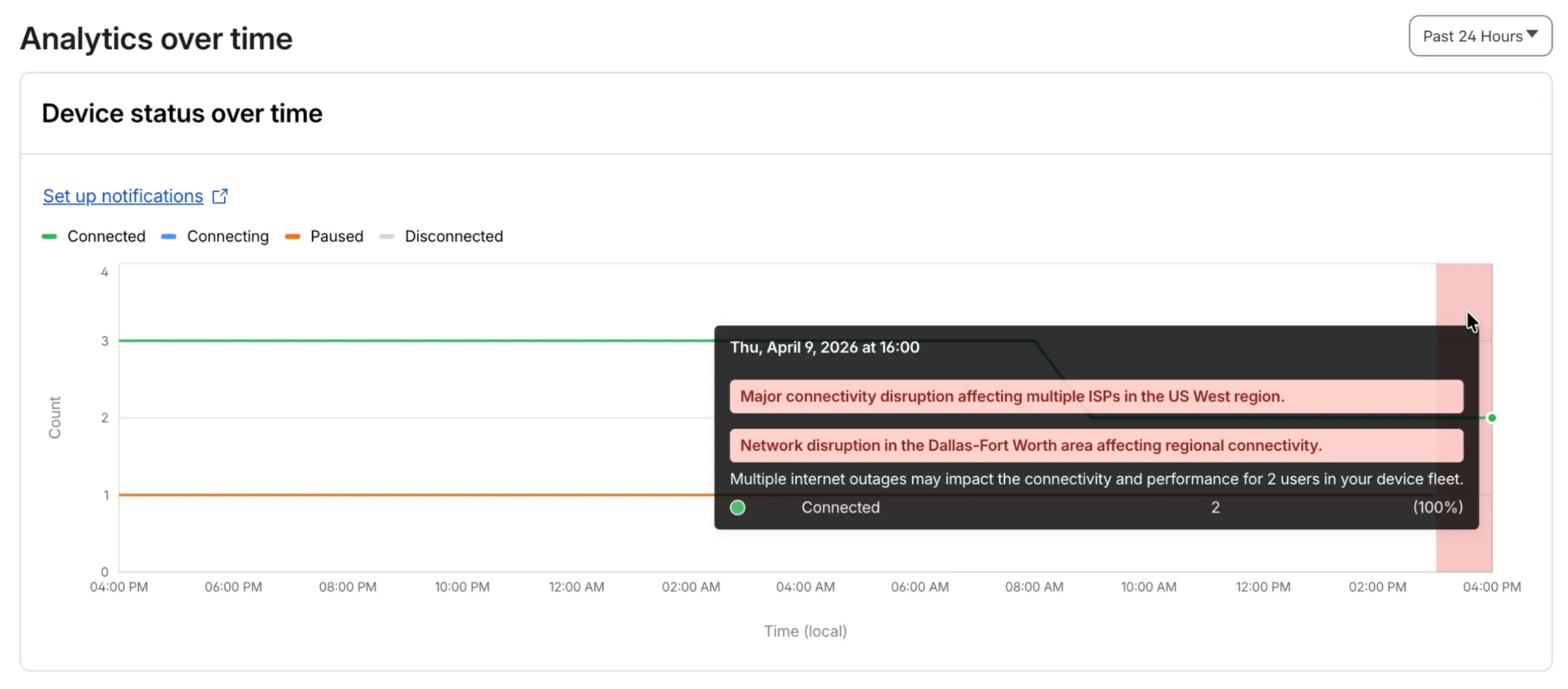
Digital Experience will display a dashboard notification when an Internet outage or traffic anomaly may impact a Cloudflare One Client device based on its geographic location or network connection.
This Internet outage and traffic anomaly data is pulled from Cloudflare Radar ↗. All Internet outage and traffic anomaly observations can be viewed in the Radar Outage Center ↗.
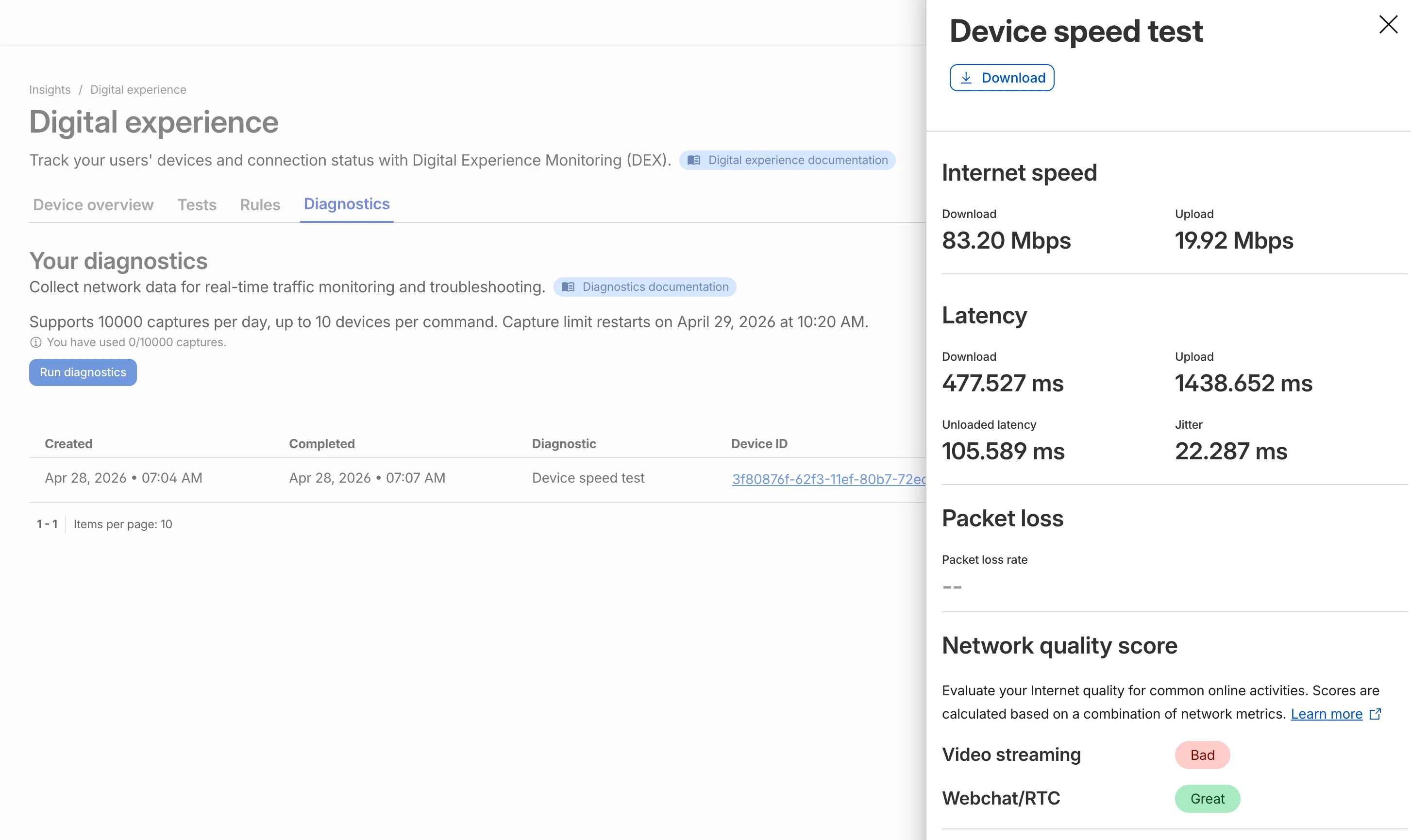
IT teams can now remotely run speed tests from the Cloudflare One Client to Cloudflare's network edge.
Each speed test includes the following metrics:
- Internet speed: download and upload throughput
- Latency: download, upload, unloaded latency, and jitter
- Network quality score: video streaming, webchat/real-time communication (RTC)
In the Cloudflare dashboard ↗, go to Zero Trust > Insights > Digital experience > Diagnostics and select Run diagnostics to use the feature today.
We have introduced a unified investigation workspace within Brand Protection to help analysts manage complex brand portfolios. Instead of jumping between individual queries, you can now consolidate your workflow into a single, cohesive view.
- You can now elect multiple saved queries from your dashboard to generate a consolidated "Combined Matches" view. This allows you to triage results from different brand queries in one unified table
- You can open query extended views in distinct tabs within the Brand Protection dashboard. This enables you to maintain multiple investigation contexts simultaneously and switch between them without losing your place.
- You can reset your workspace using the new "Clear Selection" action, making it easier to pivot between different investigation sets.
- Eliminate fragmented workflows by viewing all matches across different query buckets in a single table, reducing the need to click through dozens of individual query pages
- Correlate related campaigns by seeing similar domains or infrastructure patterns that appear across multiple saved queries
Learn more in our Brand Protection documentation.
Custom Dashboards are now available to all Cloudflare customers. Build personalized views that highlight the metrics most critical to your infrastructure and security posture, moving beyond standard product dashboards.
This update significantly expands the data available for visualization. Build charts based on any of the 100+ datasets available via the Cloudflare GraphQL API, covering everything from WAF events and Workers metrics to Load Balancing and Zero Trust logs.
For Log Explorer customers, you can now turn raw log queries directly into dashboard charts. When you identify a specific pattern or spike while investigating logs, save that query as a visualization to monitor those signals in real-time without leaving the dashboard.
- Unified visibility: Consolidate signals from different Cloudflare products (for example, HTTP Traffic and R2 Storage) into a single view.
- Flexible monitoring: Create charts that focus on specific status codes, ASN regions, or security actions that matter to your business.
- Expanded limits: Log Explorer customers can create up to 100 dashboards (up from 25 for standard customers).
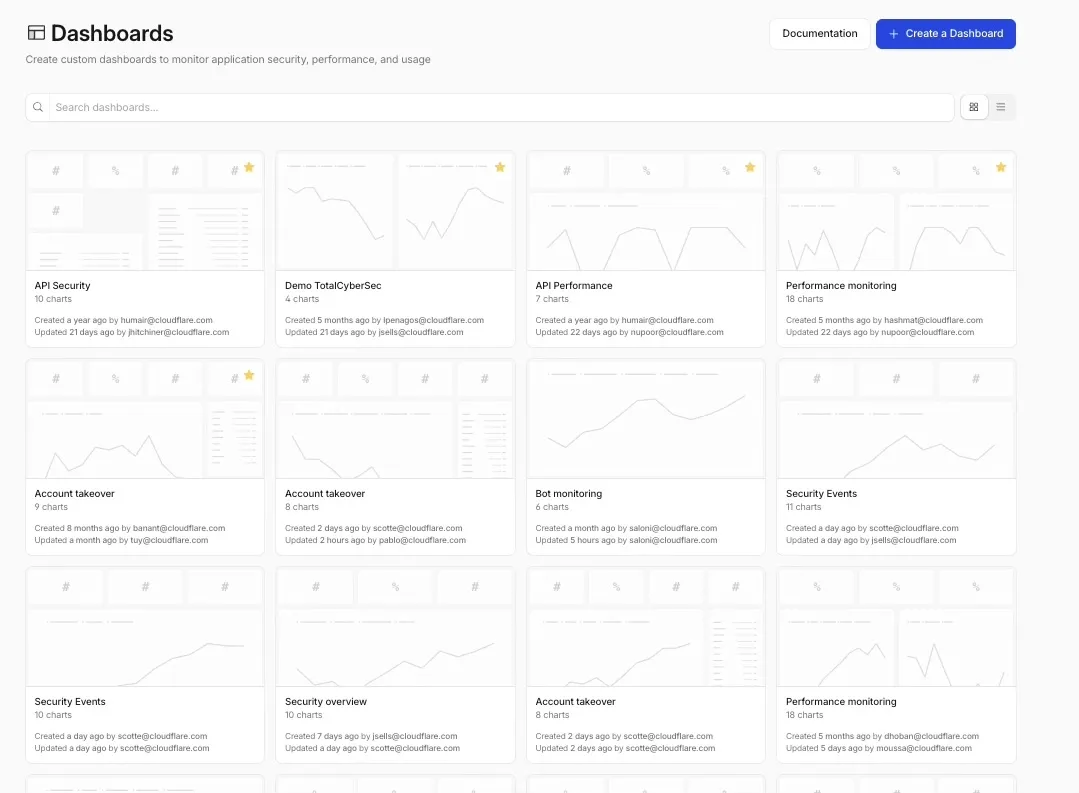
To get started, refer to the Custom Dashboards documentation.
When a Cloudflare Worker intercepts a visitor request, it can dispatch additional outbound fetch calls called subrequests. By default, each subrequest generates its own log entry in Logpush, resulting in multiple log lines per visitor request. With subrequest merging enabled, subrequest data is embedded as a nested array field on the parent log record instead.
- New subrequest_merging field on Logpush jobs — Set "merge_subrequests": true when creating or updating an http_requests Logpush job to enable the feature.
- New Subrequests log field — When subrequest merging is enabled, a Subrequests field (
array\<object\>) is added to each parent request log record. Each element in the array contains the standard http_requests fields for that subrequest.
- Applies to the http_requests (zone-scoped) dataset only.
- A maximum of 50 subrequests are merged per parent request. Subrequests beyond this limit are passed through unmodified as individual log entries.
- Subrequests must complete within 5 minutes of the visitor request. Subrequests that exceed this window are passed through unmodified.
- Subrequests that do not qualify appear as separate log entries — no data is lost.
- Subrequest merging is being gradually rolled out and is not yet available on all zones. Contact your account team for concerns or to ensure it is enabled for your zone.
- For more information, refer to Subrequests.
Logpush has traditionally been great at delivering Cloudflare logs to a variety of destinations in JSON format. While JSON is flexible and easily readable, it can be inefficient to store and query at scale.
With this release, you can now send your logs directly to Pipelines to ingest, transform, and store your logs in R2 as Parquet files or Apache Iceberg tables managed by R2 Data Catalog. This makes the data footprint more compact and more efficient at querying your logs instantly with R2 SQL or any other query engine that supports Apache Iceberg or Parquet.
Pipelines SQL runs on each log record in-flight, so you can reshape your data before it is written. For example, you can drop noisy fields, redact sensitive values, or derive new columns:
INSERT INTO http_logs_sinkSELECTClientIP,EdgeResponseStatus,to_timestamp_micros(EdgeStartTimestamp) AS event_time,upper(ClientRequestMethod) AS method,sha256(ClientIP) AS hashed_ipFROM http_logs_streamWHERE EdgeResponseStatus >= 400;Pipelines SQL supports string functions, regex, hashing, JSON extraction, timestamp conversion, conditional expressions, and more. For the full list, refer to the Pipelines SQL reference.
To configure Pipelines as a Logpush destination, refer to Enable Cloudflare Pipelines.
Radar adds three new features to the AI Insights ↗ page, expanding visibility into how AI bots, crawlers, and agents interact with the web.
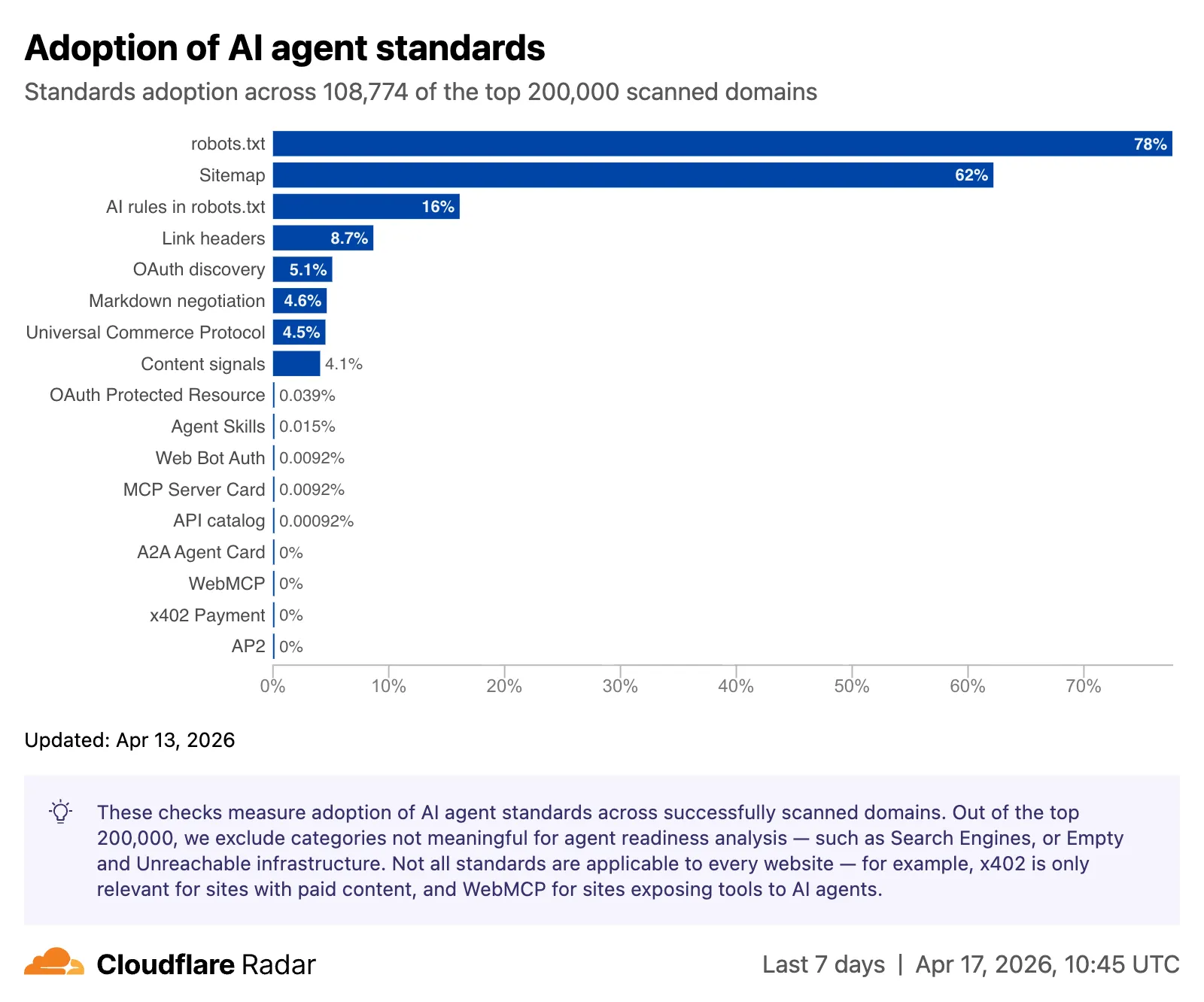
The AI Insights page now includes an adoption of AI agent standards ↗ widget that tracks how websites adopt agent-facing standards. The data is filterable by domain category and updated weekly on Mondays. This data is also available through the Agent Readiness API reference.
URL Scanner ↗ reports now include an Agent readiness tab that evaluates a scanned URL against the criteria used by the Agent Readiness score tool ↗.
For more details, refer to the Agent Readiness blog post ↗.
A new savings gauge ↗ shows the median response-size reduction when serving Markdown instead of HTML to AI bots and crawlers. This highlights the bandwidth and token savings that Markdown for Agents provides.
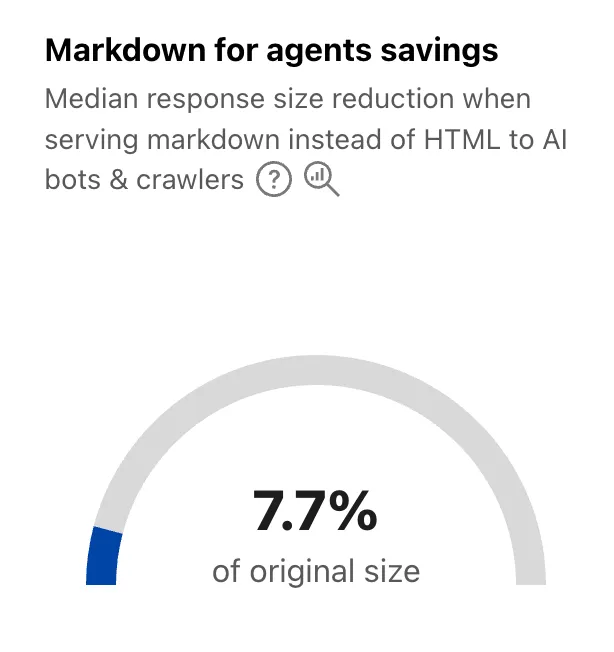
For more details, refer to the Markdown for Agents API reference.
The new response status widget ↗ displays the distribution of HTTP response status codes returned to AI bots and crawlers. Results are groupable by individual status code (200, 403, 404) or by category (2xx, 3xx, 4xx, 5xx).
The same widget is available on each verified bot's detail page (only available for AI bots), for example Google ↗.
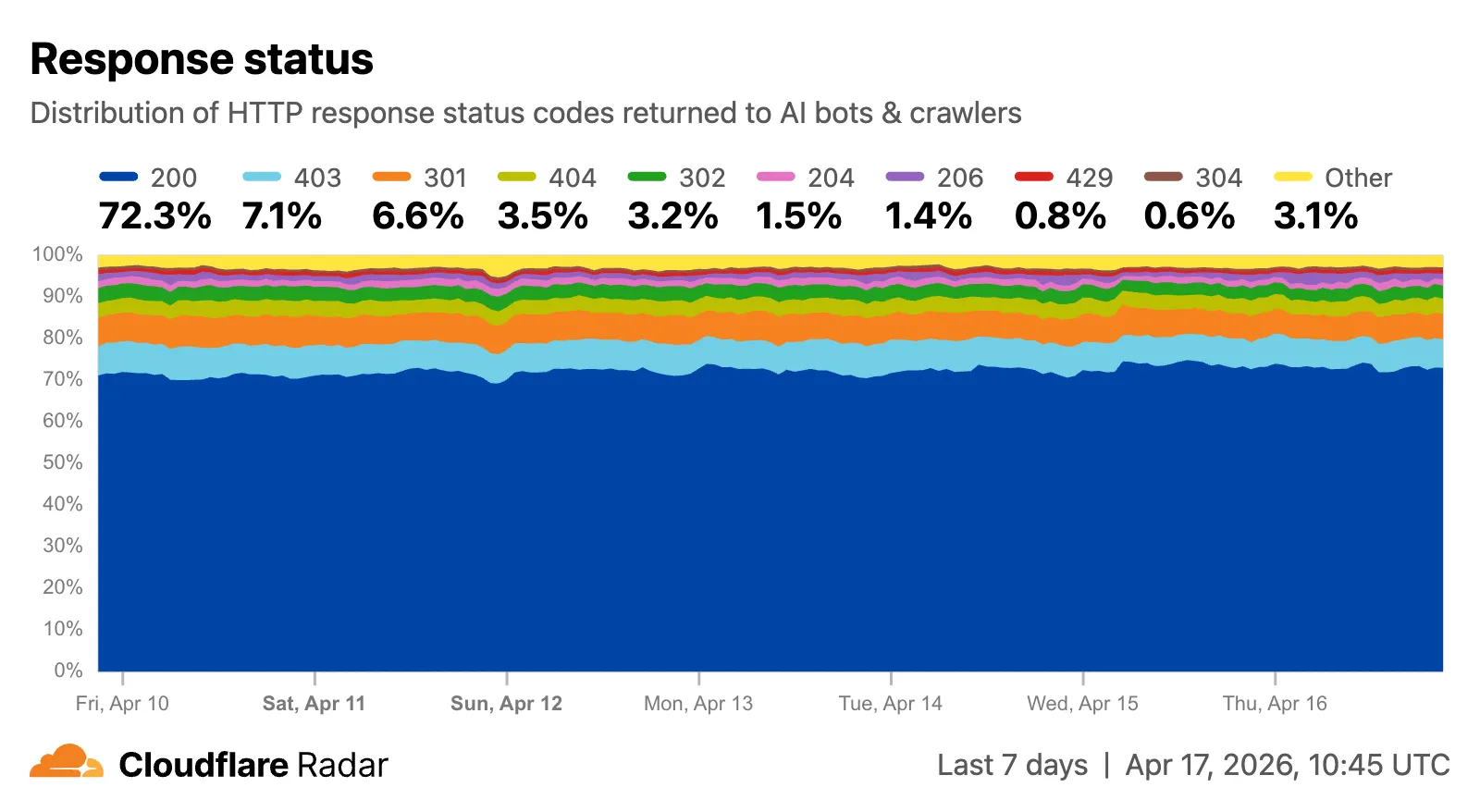
Explore all three features on the Cloudflare Radar AI Insights ↗ page.
The last seen timestamp for Cloudflare One Client devices is now more consistent across the dashboard. IT teams will see more consistent information about the most recent client event between a device and Cloudflare's network.
Cloudflare has added new fields to multiple Logpush datasets:
The following Gateway and Zero Trust datasets now include a
TenantIDfield:- Gateway DNS: Identifies the tenant ID of the DNS request, if it exists.
- Gateway HTTP: Identifies the tenant ID of the HTTP request, if it exists.
- Gateway Network: Identifies the tenant ID of the network session, if it exists.
- Zero Trust Network Sessions: Identifies the tenant ID of the network session, if it exists.
The following datasets now include Firewall for AI fields:
-
FirewallForAIInjectionScore: The score indicating the likelihood of a prompt injection attack in the request.FirewallForAIPIICategories: List of PII categories detected in the request.FirewallForAITokenCount: The number of tokens in the request.FirewallForAIUnsafeTopicCategories: List of unsafe topic categories detected in the request.
-
FirewallForAIInjectionScore: The score indicating the likelihood of a prompt injection attack in the request.FirewallForAIPIICategories: List of PII categories detected in the request.FirewallForAITokenCount: The number of tokens in the request.FirewallForAIUnsafeTopicCategories: List of unsafe topic categories detected in the request.
For the complete field definitions for each dataset, refer to Logpush datasets.
You can now configure Logpush jobs to Google BigQuery directly from the Cloudflare dashboard, in addition to the existing API-based setup.
Previously, setting up a BigQuery Logpush destination required using the Logpush API. Now you can create and manage BigQuery Logpush jobs from the Logpush page in the Cloudflare dashboard by selecting Google BigQuery as the destination and entering your Google Cloud project ID, dataset ID, table ID, and service account credentials.
For more information, refer to Enable Logpush to Google BigQuery.
Radar shareable widgets now include a generate citation action, making it easier to reference Cloudflare Radar ↗ data in research papers and other publications.
Select the citation icon to open a modal with five supported citation styles:
- BibTeX
- APA
- MLA
- Chicago
- RIS
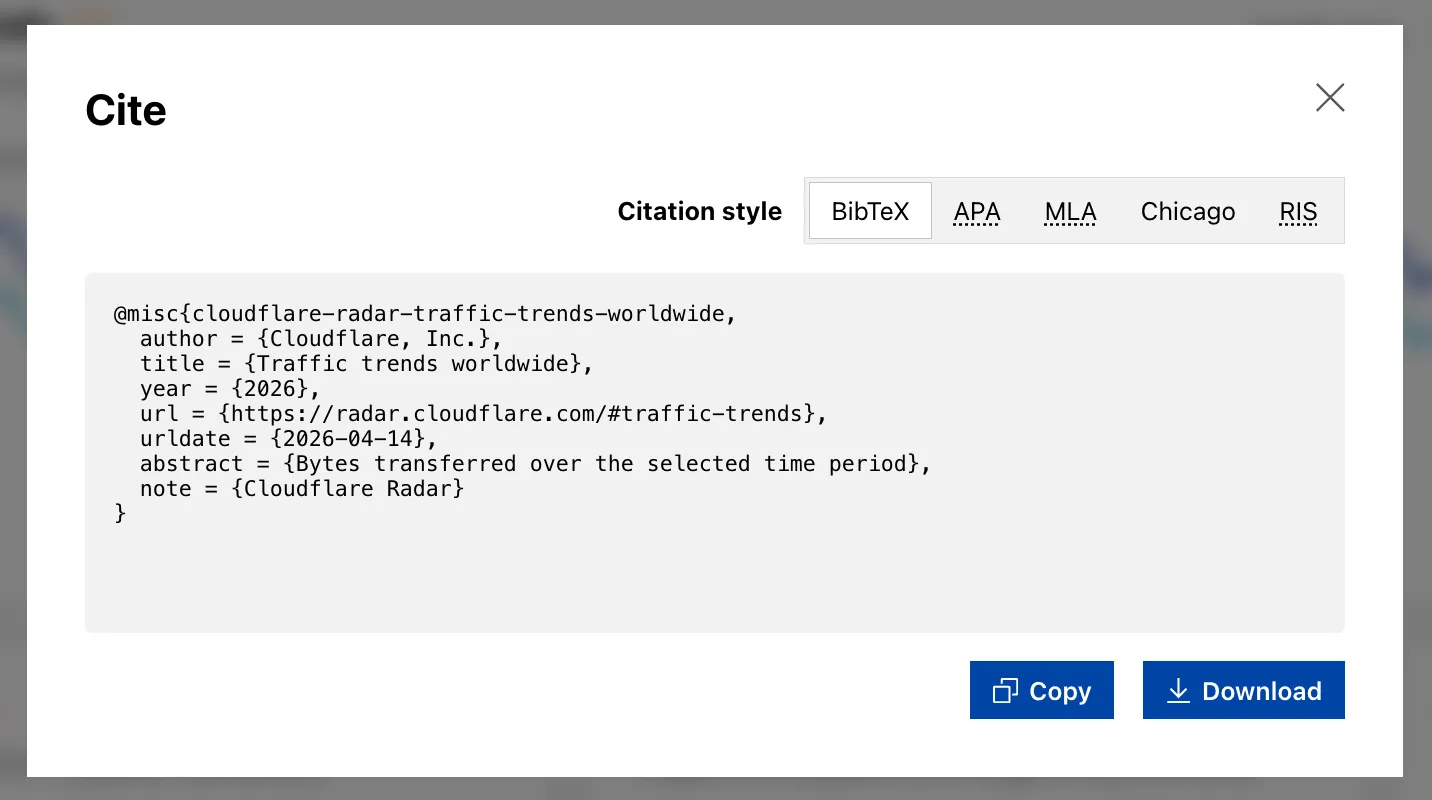
Explore the feature on any shareable widget at Cloudflare Radar ↗.
You can now automate your threat monitoring by setting up custom alerts in your saved views. Instead of manually checking the dashboard for updates, you can subscribe to notifications that trigger whenever new data matches your specific filter sets, like new activity associated to a particular threat actor or spikes in activity within your industry.
By linking your saved views to the Cloudflare Notifications Center, you can ensure the right information reaches your team at the right time.
-
Immediate Alerts: receive real-time notifications the moment a critical event is detected that matches your saved criteria. This is essential for high-priority monitoring, such as tracking active campaigns from specific APT groups.
-
Daily Digests: opt for a summarized report delivered once a day. This is ideal for maintaining situational awareness of broader trends, like regional activity shifts or industry-wide threat landscapes, without cluttering your inbox.
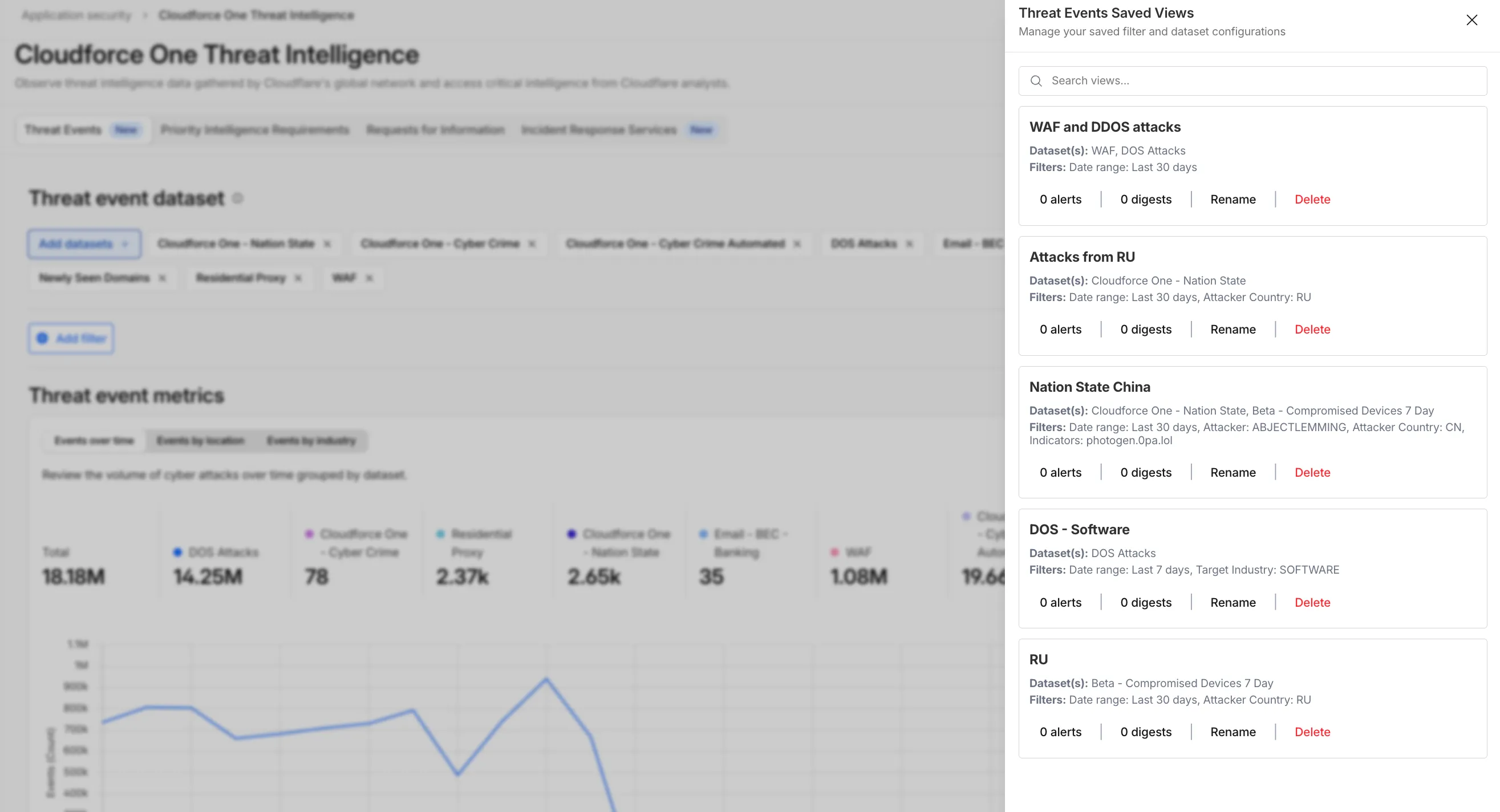
To set up an alert, go to Application Security > Threat Intelligence > Threat Events. From there:
- Choose your datasets and apply your desired filters and select Save View (or select an existing one).
- Open the Manage Saved Views menu.
- Select Add Alert next to your chosen view to configure your notification preferences in the Cloudflare dashboard.
For more technical details on configuring notifications, refer to the Threat Events documentation.
-