This week highlights enhancements to detection signatures improving coverage for vulnerabilities in Adobe Commerce and Magento Open Source, linked to CVE-2025-54236.
Key Findings
This vulnerability allows unauthenticated attackers to take over customer accounts through the Commerce REST API and, in certain configurations, may lead to remote code execution. The latest update enhances detection logic to provide more resilient protection against exploitation attempts.
Impact
Adobe Commerce (CVE-2025-54236): Exploitation may allow attackers to hijack sessions, execute arbitrary commands, steal data, and disrupt storefronts, resulting in confidentiality and integrity risks for merchants. Administrators are strongly encouraged to apply vendor patches without delay.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Adobe Commerce - Remote Code Execution - CVE:CVE-2025-54236 N/A Block This is a New Detection
Developers can now programmatically retrieve a list of all file formats supported by the Markdown Conversion utility in Workers AI.
You can use the
env.AIbinding:TypeScript await env.AI.toMarkdown().supported()Or call the REST API:
Terminal window curl https://api.cloudflare.com/client/v4/accounts/{ACCOUNT_ID}/ai/tomarkdown/supported \-H 'Authorization: Bearer {API_TOKEN}'Both return a list of file formats that users can convert into Markdown:
[{"extension": ".pdf","mimeType": "application/pdf",},{"extension": ".jpeg","mimeType": "image/jpeg",},...]Learn more about our Markdown Conversion utility.
We have updated the default behavior for Cloudflare Workers Preview URLs. Going forward, if a preview URL setting is not explicitly configured during deployment, its default behavior will automatically match the setting of your
workers.devsubdomain.This change is intended to provide a more intuitive and secure experience by aligning your preview URL's default state with your
workers.devconfiguration to prevent cases where a preview URL might remain public even after you disabled yourworkers.devroute.What this means for you:
- If neither setting is configured: both the workers.dev route and the preview URL will default to enabled
- If your workers.dev route is enabled and you do not explicitly set Preview URLs to enabled or disabled: Preview URLs will default to enabled
- If your workers.dev route is disabled and you do not explicitly set Preview URLs to enabled or disabled: Preview URLs will default to disabled
You can override the default setting by explicitly enabling or disabling the preview URL in your Worker's configuration through the API, Dashboard, or Wrangler.
Wrangler Version Behavior
The default behavior depends on the version of Wrangler you are using. This new logic applies to the latest version. Here is a summary of the behavior across different versions:
- Before v4.34.0: Preview URLs defaulted to enabled, regardless of the workers.dev setting.
- v4.34.0 up to (but not including) v4.44.0: Preview URLs defaulted to disabled, regardless of the workers.dev setting.
- v4.44.0 or later: Preview URLs now default to matching your workers.dev setting.
Why we’re making this change
In July, we introduced preview URLs to Workers, which let you preview code changes before deploying to production. This made disabling your Worker’s workers.dev URL an ambiguous action — the preview URL, served as a subdomain of
workers.dev(ex:preview-id-worker-name.account-name.workers.dev) would still be live even if you had disabled your Worker’sworkers.devroute. If you misinterpreted what it meant to disable yourworkers.devroute, you might unintentionally leave preview URLs enabled when you didn’t mean to, and expose them to the public Internet.To address this, we made a one-time update to disable preview URLs on existing Workers that had their workers.dev route disabled and changed the default behavior to be disabled for all new deployments where a preview URL setting was not explicitly configured.
While this change helped secure many customers, it was disruptive for customers who keep their
workers.devroute enabled and actively use the preview functionality, as it now required them to explicitly enable preview URLs on every redeployment.This new, more intuitive behavior ensures that your preview URL settings align with yourworkers.devconfiguration by default, providing a more secure and predictable experience.Securing access to
workers.devand preview URL endpointsTo further secure your
workers.devsubdomain and preview URL, you can enable Cloudflare Access with a single click in your Worker's settings to limit access to specific users or groups.
AI Crawl Control now includes a Robots.txt tab that provides insights into how AI crawlers interact with your
robots.txtfiles.The Robots.txt tab allows you to:
- Monitor the health status of
robots.txtfiles across all your hostnames, including HTTP status codes, and identify hostnames that need arobots.txtfile. - Track the total number of requests to each
robots.txtfile, with breakdowns of successful versus unsuccessful requests. - Check whether your
robots.txtfiles contain Content Signals ↗ directives for AI training, search, and AI input. - Identify crawlers that request paths explicitly disallowed by your
robots.txtdirectives, including the crawler name, operator, violated path, specific directive, and violation count. - Filter
robots.txtrequest data by crawler, operator, category, and custom time ranges.
When you identify non-compliant crawlers, you can:
- Block the crawler in the Crawlers tab
- Create custom WAF rules for path-specific security
- Use Redirect Rules to guide crawlers to appropriate areas of your site
To get started, go to AI Crawl Control > Robots.txt in the Cloudflare dashboard. Learn more in the Track robots.txt documentation.
- Monitor the health status of
Admins can now create scheduled DNS policies directly from the Zero Trust dashboard, without using the API. You can configure policies to be active during specific, recurring times, such as blocking social media during business hours or gaming sites on school nights.
- Preset Schedules: Use built-in templates for common scenarios like Business Hours, School Days, Weekends, and more.
- Custom Schedules: Define your own schedule with specific days and up to three non-overlapping time ranges per day.
- Timezone Control: Choose to enforce a schedule in a specific timezone (for example, US Eastern) or based on the local time of each user.
- Combined with Duration: Policies can have both a schedule and a duration. If both are set, the duration's expiration takes precedence.
You can see the flow in the demo GIF:
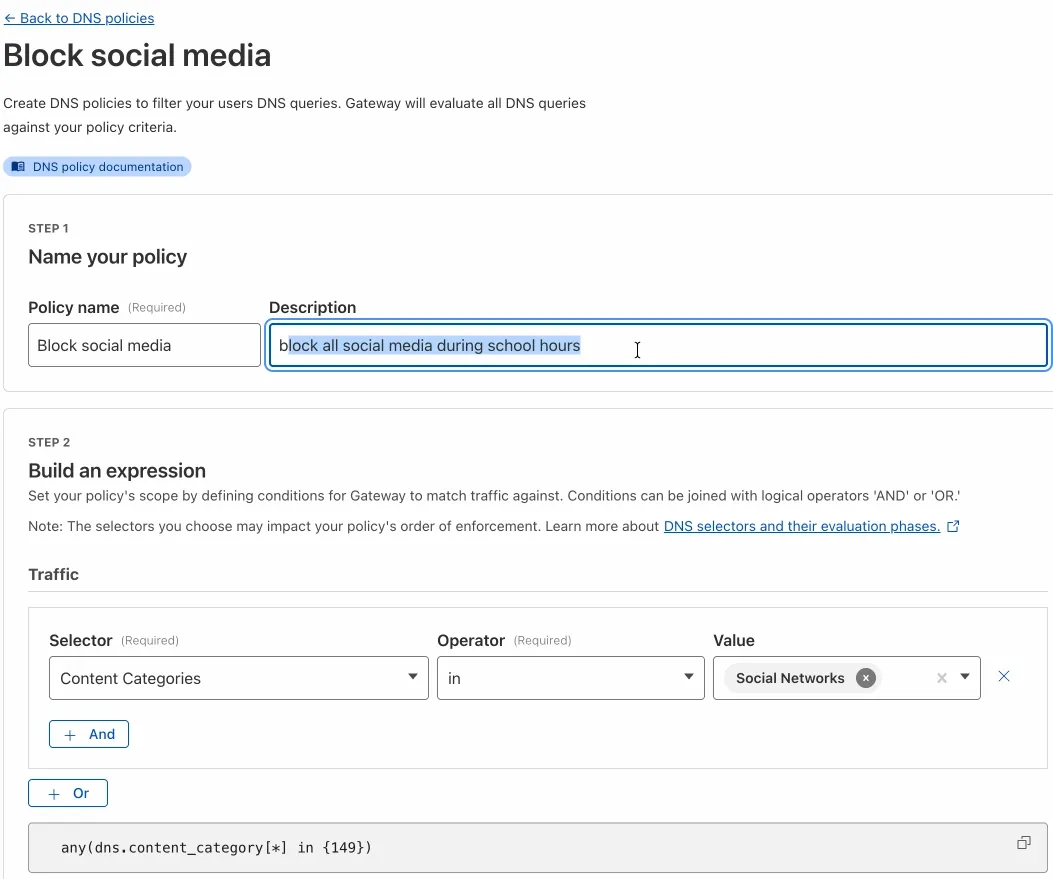
This update makes time-based DNS policies accessible to all Gateway customers, removing the technical barrier of the API.
This week’s update introduces an enhanced rule that expands detection coverage for a critical vulnerability in Oracle E-Business Suite. It also improves an existing rule to provide more reliable coverage in request processing.
Key Findings
New WAF rule deployed for Oracle E-Business Suite (CVE-2025-61882) to block unauthenticated attacker's network access via HTTP to compromise Oracle Concurrent Processing. If successfully exploited, this vulnerability may result in remote code execution.
Impact
- Successful exploitation of CVE-2025-61882 allows unauthenticated attackers to execute arbitrary code remotely by chaining multiple weaknesses, enabling lateral movement into internal services, data exfiltration, and large-scale extortionware deployment within Oracle E-Business Suite environments.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100598A Remote Code Execution - Common Bash Bypass - Beta Log Block This rule is merged into the original rule "Remote Code Execution - Common Bash Bypass" (ID: Cloudflare Managed Ruleset 100916A Oracle E-Business Suite - Remote Code Execution - CVE:CVE-2025-61882 - 2 Log Block This is a New Detection Cloudflare Managed Ruleset N/A HTTP Truncated N/A Disabled This is a New Detection
You can now generate on-demand security reports directly from the Cloudflare dashboard. This new feature provides a comprehensive overview of your email security posture, making it easier than ever to demonstrate the value of Cloudflare’s Email security to executives and other decision makers.
These reports offer several key benefits:
- Executive Summary: Quickly view the performance of Email security with a high-level executive summary.
- Actionable Insights: Dive deep into trend data, breakdowns of threat types, and analysis of top targets to identify and address vulnerabilities.
- Configuration Transparency: Gain a clear view of your policy, submission, and domain configurations to ensure optimal setup.
- Account Takeover Risks: Get a snapshot of your M365 risky users (requires a Microsoft Entra ID P2 license and M365 SaaS integration ↗).
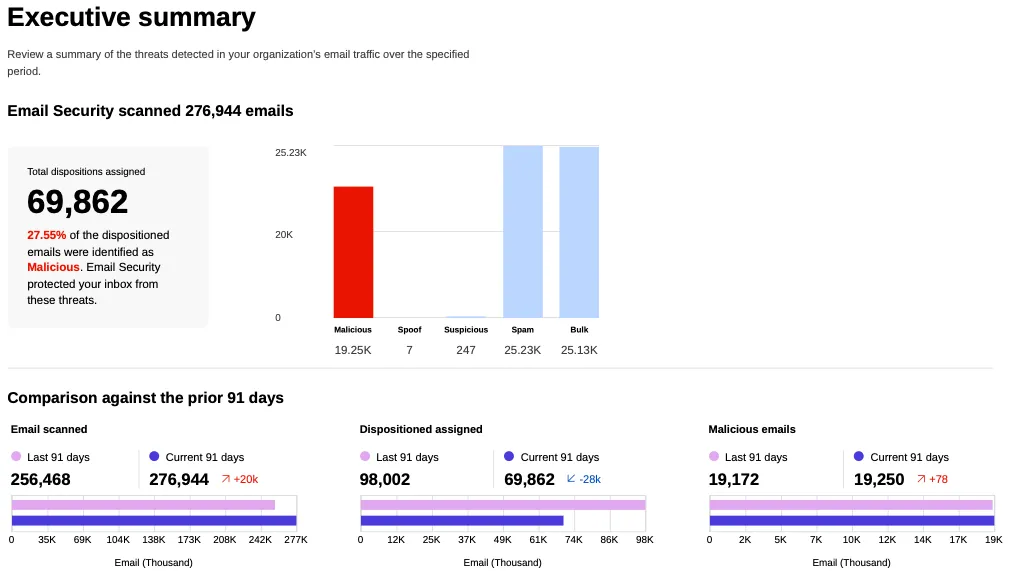
This feature is available across the following Email security packages:
- Advantage
- Enterprise
- Enterprise + PhishGuard
Cloudflare's new Application Security report, currently in Closed Beta, is now available in the dashboard.
Go to Security reportsThe reports are generated monthly and provide cyber security insights trends for all of the Enterprise zones in your Cloudflare account.
The reports also include an industry benchmark, comparing your cyber security landscape to peers in your industry.
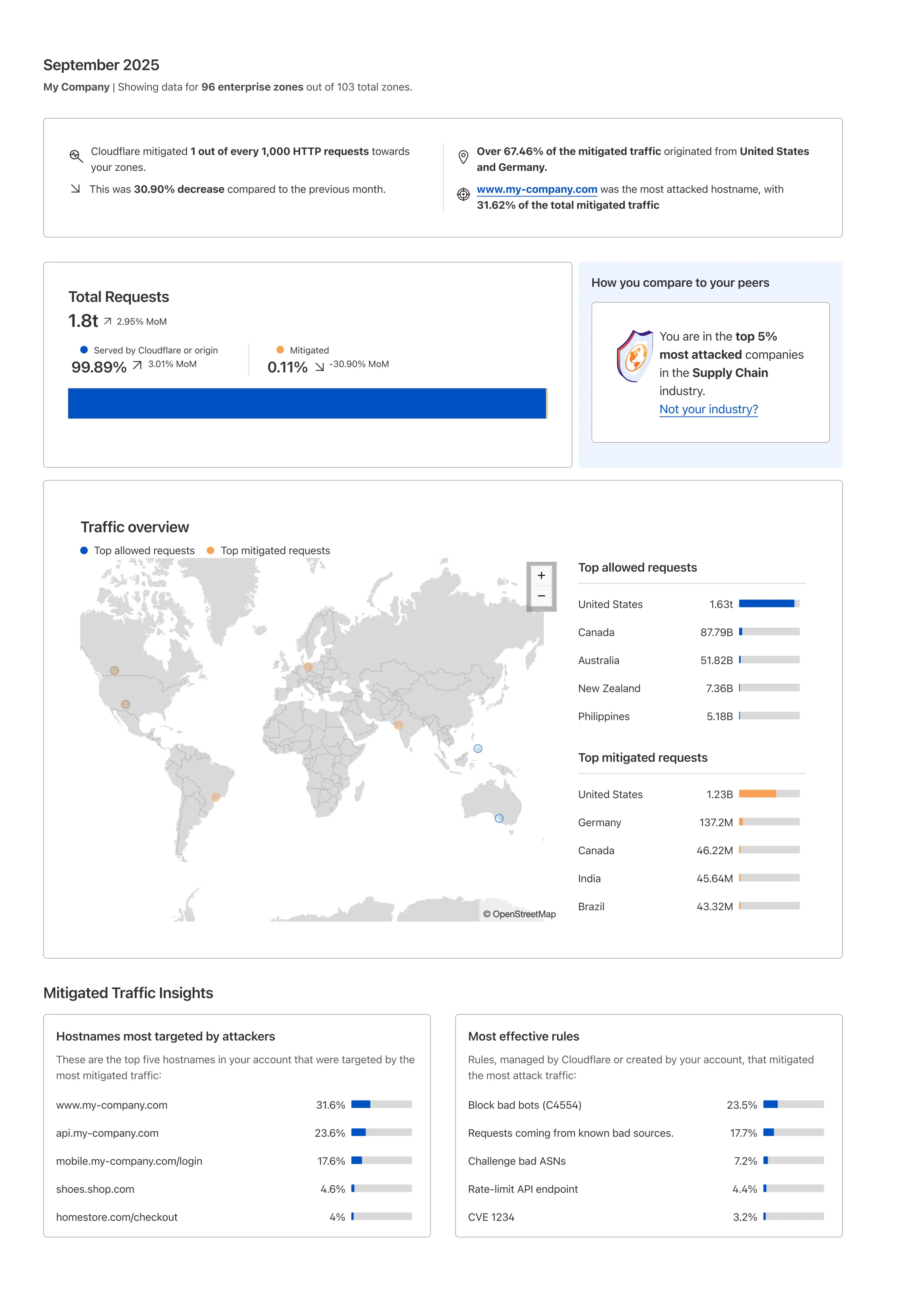
Learn more about the reports by referring to the Security Reports documentation.
Use the feedback survey link at the top of the page to help us improve the reports.
This week we introduced several new detections across Cloudflare Managed Rulesets, expanding coverage for high-impact vulnerability classes such as SSRF, SQLi, SSTI, Reverse Shell attempts, and Prototype Pollution. These rules aim to improve protection against attacker-controlled payloads that exploit misconfigurations or unvalidated input in web applications.
Key Findings
New detections added for multiple exploit categories:
SSRF (Server-Side Request Forgery) — new rules targeting both local and cloud metadata abuse patterns (Beta).
SQL Injection (SQLi) — rules for common patterns, sleep/time-based injections, and string/wait function exploitation across headers and URIs.
SSTI (Server-Side Template Injection) — arithmetic-based probe detections introduced across URI, header, and body fields.
Reverse Shell and XXE payloads — enhanced heuristics for command execution and XML external entity misuse.
Prototype Pollution — new Beta rule identifying common JSON payload structures used in object prototype poisoning.
PHP Wrapper Injection and HTTP Parameter Pollution detections — to catch path traversal and multi-parameter manipulation attempts.
Anomaly Header Checks — detecting CRLF injection attempts in header names.
Impact
These updates help detect multi-vector payloads that blend SSRF + RCE or SQLi + SSTI attacks, especially in cloud-hosted applications with exposed metadata endpoints or unsafe template rendering.
Prototype Pollution and HTTP parameter pollution rules address emerging JavaScript supply-chain exploitation patterns increasingly seen in real-world incidents.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Anomaly:Header - name - CR, LF N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - Reverse Shell - Body N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - Reverse Shell - Header N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - Reverse Shell - URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - XXE - Body N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - Common Patterns - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - Sleep Function - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - String Function - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - WaitFor Function - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Local - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Local - 2 - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Cloud - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Cloud - 2 - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSTI - Arithmetic Probe - URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSTI - Arithmetic Probe - Header N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSTI - Arithmetic Probe - Body N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A PHP Wrapper Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A PHP Wrapper Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A HTTP parameter pollution N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Prototype Pollution - Common Payloads - Beta N/A Disabled This is a New Detection
A new Beta release for the Windows WARP client is now available on the beta releases downloads page.
This release contains minor fixes, improvements, and new features including Path Maximum Transmission Unit Discovery (PMTUD). With PMTUD enabled, the client will dynamically adjust packet sizing to optimize connection performance. There is also a new connection status message in the GUI to inform users that the local network connection may be unstable. This will make it easier to debug connectivity issues.
Changes and improvements
- Improvements for Windows multi-user to maintain the Global WARP override state when switching between users.
- The GUI now displays the health of the tunnel and DNS connections by showing a connection status message when the network may be unstable. This will make it easier to debug connectivity issues.
- Deleting registrations no longer returns an error when succeeding.
- Path Maximum Transmission Unit Discovery (PMTUD) is now used to discover the effective MTU of the connection. This allows the client to improve connection performance optimized for the current network.
Known issues
For Windows 11 24H2 users, Microsoft has confirmed a regression that may lead to performance issues like mouse lag, audio cracking, or other slowdowns. Cloudflare recommends users experiencing these issues upgrade to a minimum Windows 11 24H2 KB5062553 or higher for resolution.
Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Devices with KB5055523 installed may receive a warning about
Win32/ClickFix.ABAbeing present in the installer. To resolve this false positive, update Microsoft Security Intelligence to version 1.429.19.0 or later.DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new Beta release for the macOS WARP client is now available on the beta releases downloads page.
This release contains minor fixes, improvements, and new features including Path Maximum Transmission Unit Discovery (PMTUD). With PMTUD enabled, the client will dynamically adjust packet sizing to optimize connection performance. There is also a new connection status message in the GUI to inform users that the local network connection may be unstable. This will make it easier to debug connectivity issues.
Changes and improvements
- The GUI now displays the health of the tunnel and DNS connections by showing a connection status message when the network may be unstable. This will make it easier to debug connectivity issues.
- Deleting registrations no longer returns an error when succeeding.
- Path Maximum Transmission Unit Discovery (PMTUD) is now used to discover the effective MTU of the connection. This allows the client to improve connection performance optimized for the current network.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
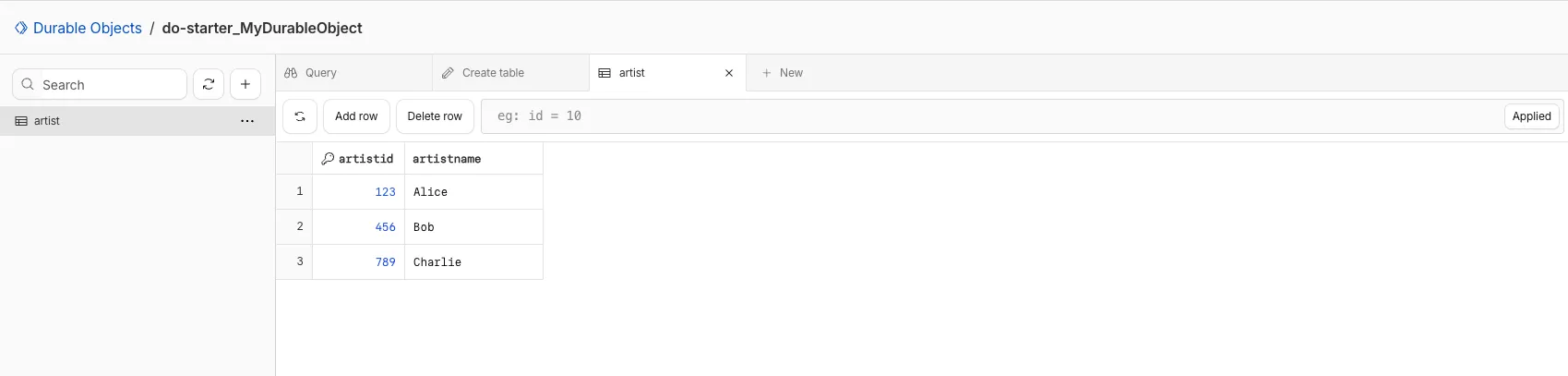
You can now view and write to each Durable Object's storage using a UI editor on the Cloudflare dashboard. Only Durable Objects using SQLite storage can use Data Studio.
Go to Durable ObjectsData Studio unlocks easier data access with Durable Objects for prototyping application data models to debugging production storage usage. Before, querying your Durable Objects data required deploying a Worker.
To access a Durable Object, you can provide an object's unique name or ID generated by Cloudflare. Data Studio requires you to have at least the
Workers Platform Adminrole, and all queries are captured with audit logging for your security and compliance needs. Queries executed by Data Studio send requests to your remote, deployed objects and incur normal usage billing.To learn more, visit the Data Studio documentation. If you have feedback or suggestions for the new Data Studio, please share your experience on Discord ↗
-
We're excited to announce a significant increase in the maximum header size supported by Cloudflare's Content Delivery Network (CDN). Cloudflare now supports up to 128 KB for both request and response headers.
Previously, customers were limited to a total of 32 KB for request or response headers, with a maximum of 16 KB per individual header. Larger headers could cause requests to fail with
HTTP 413(Request Header Fields Too Large) errors.
- Support for large headers: You can now utilize much larger headers, whether as a single large header up to 128 KB or split over multiple headers.
- Reduces
413and520HTTP errors: This change drastically reduces the likelihood of customers encounteringHTTP 413errors from large request headers orHTTP 520errors caused by oversized response headers, improving the overall reliability of your web applications. - Enhanced functionality: This is especially beneficial for applications that rely on:
- A large number of cookies.
- Large Content-Security-Policy (CSP) response headers.
- Advanced use cases with Cloudflare Workers that generate large response headers.
This enhancement improves compatibility with Cloudflare's CDN, enabling more use cases that previously failed due to header size limits.
To learn more and get started, refer to the Cloudflare Fundamentals documentation.
Cloudflare Load Balancing now supports Monitor Groups, a powerful new way to combine multiple health monitors into a single, logical group. This allows you to create sophisticated health checks that more accurately reflect the true availability of your applications by assessing multiple services at once.
With Monitor Groups, you can ensure that all critical components of an application are healthy before sending traffic to an origin pool, enabling smarter failover decisions and greater resilience. This feature is now available via the API for customers with an Enterprise Load Balancing subscription.
- Combine Multiple Monitors: Group different health monitors (for example, HTTP, TCP) that check various application components, like a primary API gateway and a specific
/loginservice. - Isolate Monitors for Observation: Mark a monitor as "monitoring only" to receive alerts and data without it affecting a pool's health status or traffic steering. This is perfect for testing new checks or observing non-critical dependencies.
- Improve Steering Intelligence: Latency for Dynamic Steering is automatically averaged across all active monitors in a group, providing a more holistic view of an origin's performance.
This enhancement is ideal for complex, multi-service applications where the health of one component depends on another. By aggregating health signals, Monitor Groups provide a more accurate and comprehensive assessment of your application's true status.
For detailed information and API configuration guides, please visit our developer documentation for Monitor Groups.
- Combine Multiple Monitors: Group different health monitors (for example, HTTP, TCP) that check various application components, like a primary API gateway and a specific
AI Crawl Control now provides enhanced metrics and CSV data exports to help you better understand AI crawler activity across your sites.
Visualize crawler activity patterns over time, and group data by different dimensions:
- By Crawler — Track activity from individual AI crawlers (GPTBot, ClaudeBot, Bytespider)
- By Category — Analyze crawler purpose or type
- By Operator — Discover which companies (OpenAI, Anthropic, ByteDance) are crawling your site
- By Host — Break down activity across multiple subdomains
- By Status Code — Monitor HTTP response codes to crawlers (200s, 300s, 400s, 500s)
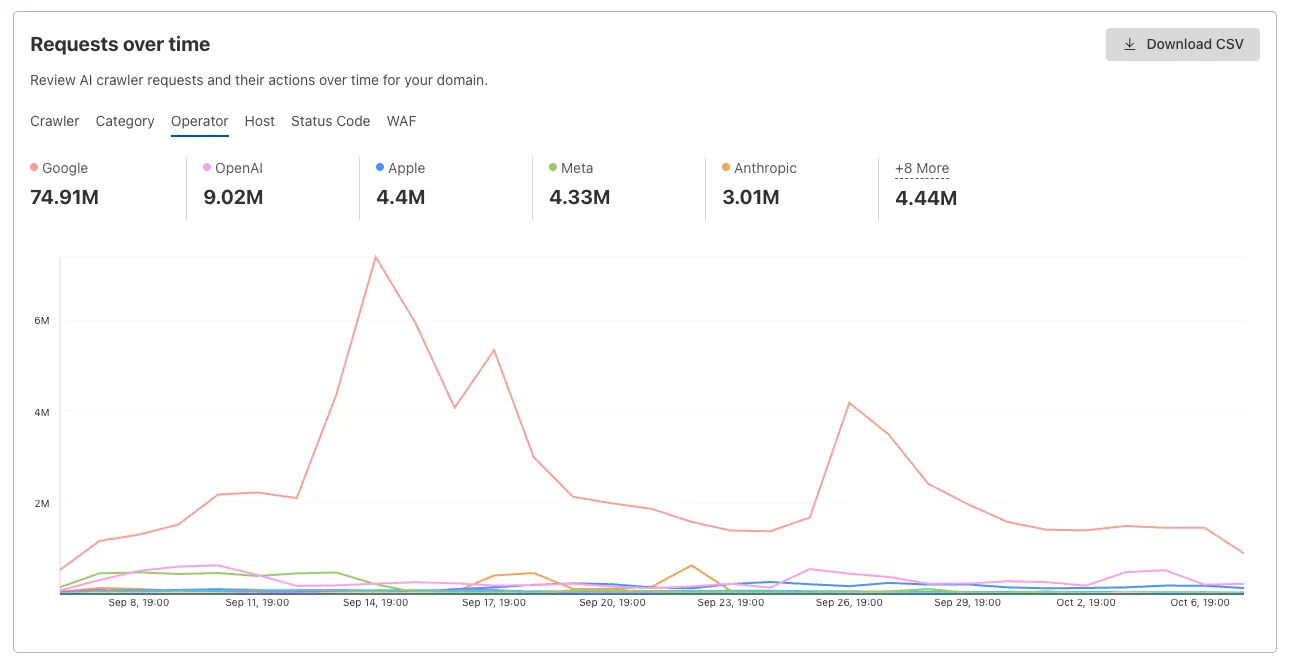
Interactive chart showing crawler requests over time with filterable dimensions Identify traffic sources with referrer analytics:
- View top referrers driving traffic to your site
- Understand discovery patterns and content popularity from AI operators
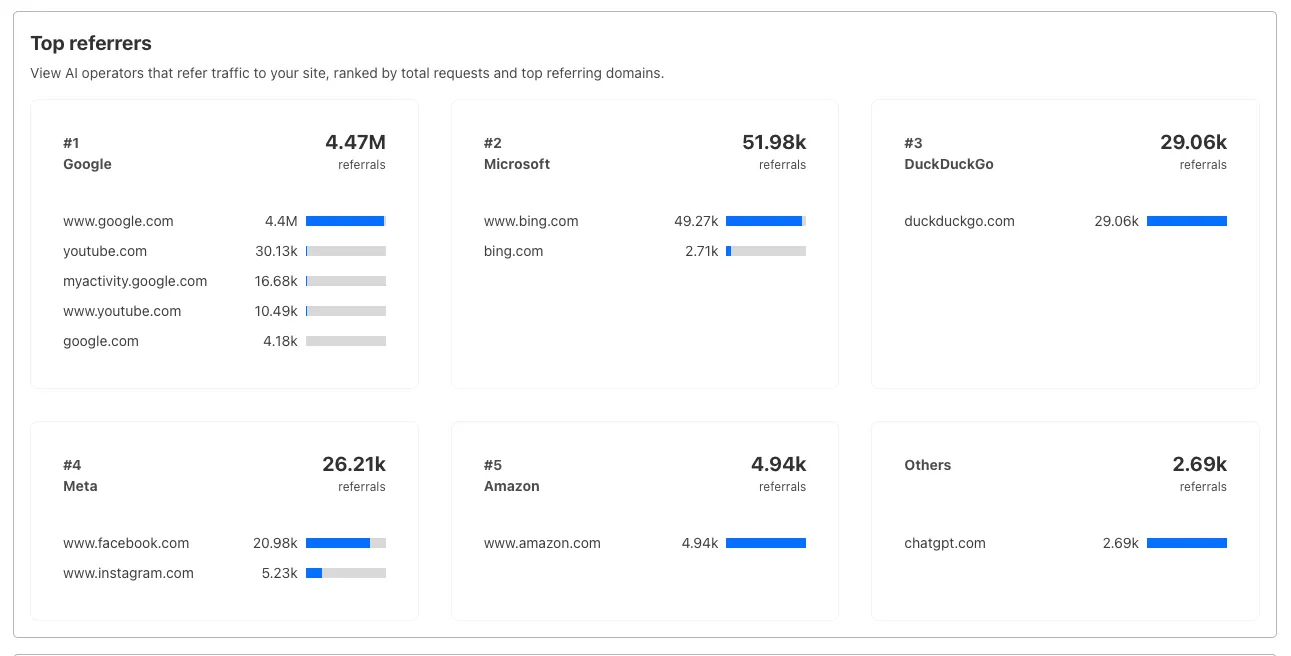
Bar chart showing top referrers and their respective traffic volumes Download your filtered view as a CSV:
- Includes all applied filters and groupings
- Useful for custom reporting and deeper analysis
- Log in to the Cloudflare dashboard, and select your account and domain.
- Go to AI Crawl Control > Metrics.
- Use the grouping tabs to explore different views of your data.
- Apply filters to focus on specific crawlers, time ranges, or response codes.
- Select Download CSV to export your filtered data for further analysis.
Learn more about AI Crawl Control.
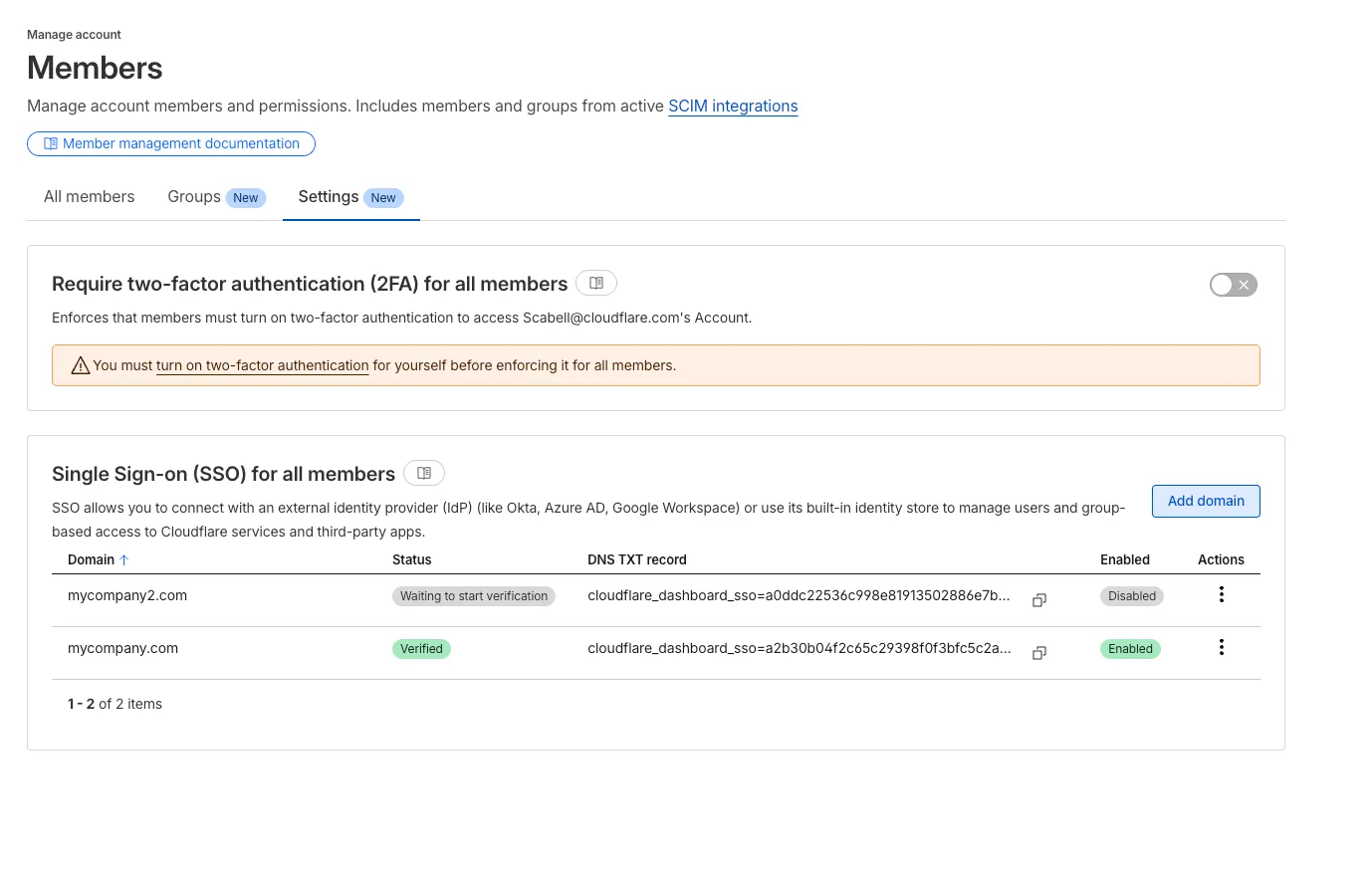
During Birthday Week, we announced that single sign-on (SSO) is available for free ↗ to everyone who signs in with a custom email domain and maintains a compatible identity provider ↗. SSO minimizes user friction around login and provides the strongest security posture available. At the time, this could only be configured using the API.
Today, we are launching a new user experience which allows users to manage their SSO configuration from within the Cloudflare dashboard. You can access this by going to Manage account > Members > Settings.
This week’s highlights include a new JinJava rule targeting a sandbox-bypass flaw that could allow malicious template input to escape execution controls. The rule improves detection for unsafe template rendering paths.
Key Findings
New WAF rule deployed for JinJava (CVE-2025-59340) to block a sandbox bypass in the template engine that permits attacker-controlled type construction and arbitrary class instantiation; in vulnerable environments this can escalate to remote code execution and full server compromise.
Impact
- CVE-2025-59340 — Exploitation enables attacker-supplied type descriptors / Jackson
ObjectMapperabuse, allowing arbitrary class loading, file/URL access (LFI/SSRF primitives) and, with suitable gadget chains, potential remote code execution and system compromise.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100892 JinJava - SSTI - CVE:CVE-2025-59340 Log Block This is a New Detection - CVE-2025-59340 — Exploitation enables attacker-supplied type descriptors / Jackson
We have added three new domain categories under the Technology parent category, to better reflect online content and improve DNS filtering.
New categories added
Parent ID Parent Name Category ID Category Name 26 Technology 194 Keep Awake Software 26 Technology 192 Remote Access 26 Technology 193 Shareware/Freeware Refer to Gateway domain categories to learn more.
You can now upload a Worker that takes up 1 second to parse and execute its global scope. Previously, startup time was limited to 400 ms.
This allows you to run Workers that import more complex packages and execute more code prior to requests being handled.
For more information, see the documentation on Workers startup limits.
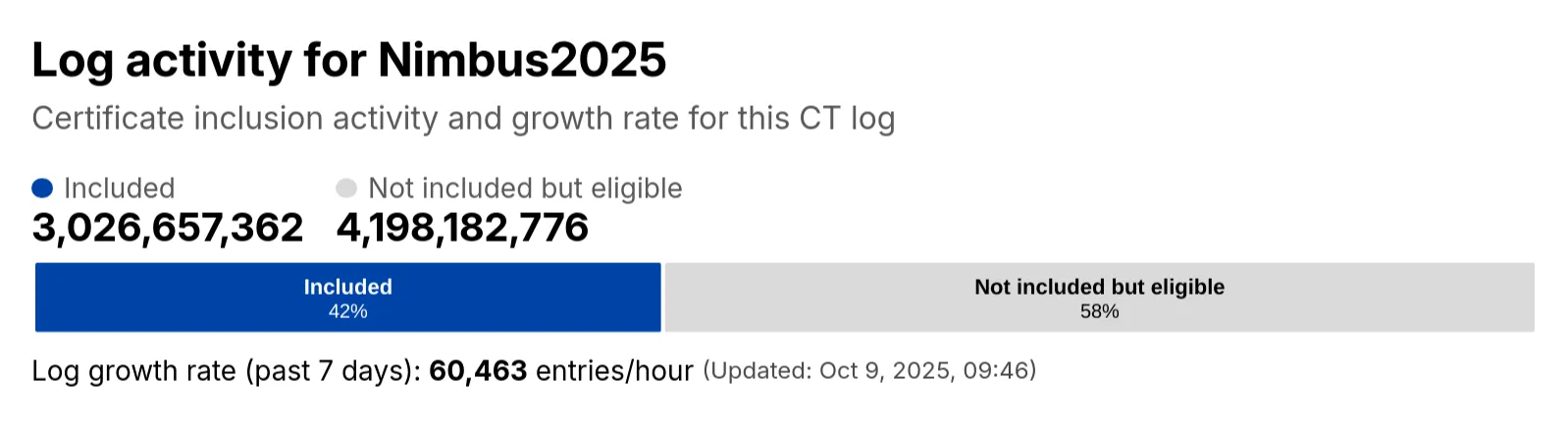
Radar has expanded its Certificate Transparency (CT) log insights with new stats that provide greater visibility into log activity:
- Log growth rate: The average throughput of the CT log over the past 7 days, measured in certificates per hour.
- Included certificate count: The total number of certificates already included in this CT log.
- Eligible-for-inclusion certificate count: The number of certificates eligible for inclusion in this log but not yet included. This metric is based on certificates signed by trusted root CAs within the log’s accepted date range.
- Last update: The timestamp of the most recent update to the CT log.
These new statistics have been added to the response of the Get Certificate Log Details API endpoint, and are displayed on the CT log information page ↗.
You can now upload Workers with static assets (like HTML, CSS, JavaScript, images) with the Cloudflare Terraform provider v5.11.0 ↗, making it even easier to deploy and manage full-stack apps with IaC.
Previously, you couldn't use Terraform to upload static assets without writing custom scripts to handle generating an asset manifest, calling the Cloudflare API to upload assets in chunks, and handling change detection.
Now, you simply define the directory where your assets are built, and we handle the rest. Check out the examples for what this looks like in Terraform configuration.
You can get started today with the Cloudflare Terraform provider (v5.11.0) ↗, using either the existing
cloudflare_workers_scriptresource ↗, or the betacloudflare_worker_versionresource ↗.Here's how you can use the existing
cloudflare_workers_script↗ resource to upload your Worker code and assets in one shot.resource "cloudflare_workers_script" "my_app" {account_id = var.account_idscript_name = "my-app"content_file = "./dist/worker/index.js"content_sha256 = filesha256("./dist/worker/index.js")main_module = "index.js"# Just point to your assets directory - that's it!assets = {directory = "./dist/static"}}And here's an example using the beta
cloudflare_worker_version↗ resource, alongside thecloudflare_worker↗ andcloudflare_workers_deployment↗ resources:# This tracks the existence of your Worker, so that you# can upload code and assets separately from tracking Worker state.resource "cloudflare_worker" "my_app" {account_id = var.account_idname = "my-app"}resource "cloudflare_worker_version" "my_app_version" {account_id = var.account_idworker_id = cloudflare_worker.my_app.id# Just point to your assets directory - that's it!assets = {directory = "./dist/static"}modules = [{name = "index.js"content_file = "./dist/worker/index.js"content_type = "application/javascript+module"}]}resource "cloudflare_workers_deployment" "my_app_deployment" {account_id = var.account_idscript_name = cloudflare_worker.my_app.namestrategy = "percentage"versions = [{version_id = cloudflare_worker_version.my_app_version.idpercentage = 100}]}Under the hood, the Cloudflare Terraform provider now handles the same logic that Wrangler uses for static asset uploads. This includes scanning your assets directory, computing hashes for each file, generating a manifest with file metadata, and calling the Cloudflare API to upload any missing files in chunks. We support large directories with parallel uploads and chunking, and when the asset manifest hash changes, we detect what's changed and trigger an upload for only those changed files.
- Get started with the Cloudflare Terraform provider (v5.11.0) ↗
- You can use either the existing
cloudflare_workers_scriptresource ↗ to upload your Worker code and assets in one resource. - Or you can use the new beta
cloudflare_worker_versionresource ↗ (along with thecloudflare_worker↗ andcloudflare_workers_deployment↗) resources to more granularly control the lifecycle of each Worker resource.
You can now create and manage Workflows using Terraform, now supported in the Cloudflare Terraform provider v5.11.0 ↗. Workflows allow you to build durable, multi-step applications -- without needing to worry about retrying failed tasks or managing infrastructure.
Now, you can deploy and manage Workflows through Terraform using the new
cloudflare_workflowresource ↗:resource "cloudflare_workflow" "my_workflow" {account_id = var.account_idworkflow_name = "my-workflow"class_name = "MyWorkflow"script_name = "my-worker"}Here are full examples of how to configure
cloudflare_workflowin Terraform, using the existingcloudflare_workers_scriptresource ↗, and the betacloudflare_worker_versionresource ↗.resource "cloudflare_workers_script" "workflow_worker" {account_id = var.cloudflare_account_idscript_name = "my-workflow-worker"content_file = "${path.module}/../dist/worker/index.js"content_sha256 = filesha256("${path.module}/../dist/worker/index.js")main_module = "index.js"}resource "cloudflare_workflow" "workflow" {account_id = var.cloudflare_account_idworkflow_name = "my-workflow"class_name = "MyWorkflow"script_name = cloudflare_workers_script.workflow_worker.script_name}You can more granularly control the lifecycle of each Worker resource using the beta
cloudflare_worker_version↗ resource, alongside thecloudflare_worker↗ andcloudflare_workers_deployment↗ resources.resource "cloudflare_worker" "workflow_worker" {account_id = var.cloudflare_account_idname = "my-workflow-worker"}resource "cloudflare_worker_version" "workflow_worker_version" {account_id = var.cloudflare_account_idworker_id = cloudflare_worker.workflow_worker.idmain_module = "index.js"modules = [{name = "index.js"content_file = "${path.module}/../dist/worker/index.js"content_type = "application/javascript+module"}]}resource "cloudflare_workers_deployment" "workflow_deployment" {account_id = var.cloudflare_account_idscript_name = cloudflare_worker.workflow_worker.namestrategy = "percentage"versions = [{version_id = cloudflare_worker_version.workflow_worker_version.idpercentage = 100}]}resource "cloudflare_workflow" "my_workflow" {account_id = var.cloudflare_account_idworkflow_name = "my-workflow"class_name = "MyWorkflow"script_name = cloudflare_worker.workflow_worker.name}- Get started with the Cloudflare Terraform provider (v5.11.0) ↗ and the new
cloudflare_workflowresource ↗.
- Get started with the Cloudflare Terraform provider (v5.11.0) ↗ and the new
A new GA release for the Linux WARP client is now available on the stable releases downloads page.
This release contains significant fixes and improvements including an updated public key for Linux packages. The public key must be updated if it was installed before September 12, 2025 to ensure the repository remains functional after December 4, 2025. Instructions to make this update are available at pkg.cloudflareclient.com.
Changes and improvements
Proxy mode has been enhanced for even faster resolution. Proxy mode now supports SOCKS4, SOCK5, and HTTP CONNECT over an L4 tunnel with custom congestion control optimizations instead of the previous L3 tunnel to Cloudflare's network. This has more than doubled Proxy mode throughput in lab speed testing, by an order of magnitude in some cases.
The MASQUE protocol is now the only protocol that can use Proxy mode. If you previously configured a device profile to use Proxy mode with Wireguard, you will need to select a new WARP mode or switch to the MASQUE protocol. Otherwise, all devices matching the profile will lose connectivity.
Known issues
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
A new GA release for the Windows WARP client is now available on the stable releases downloads page.
This release contains significant fixes and improvements.
Changes and improvements
Proxy mode has been enhanced for even faster resolution. Proxy mode now supports SOCKS4, SOCK5, and HTTP CONNECT over an L4 tunnel with custom congestion control optimizations instead of the previous L3 tunnel to Cloudflare's network. This has more than doubled Proxy mode throughput in lab speed testing, by an order of magnitude in some cases.
The MASQUE protocol is now the only protocol that can use Proxy mode. If you previously configured a device profile to use Proxy mode with Wireguard, you will need to select a new WARP mode or switch to the MASQUE protocol. Otherwise, all devices matching the profile will lose connectivity.
Known issues
For Windows 11 24H2 users, Microsoft has confirmed a regression that may lead to performance issues like mouse lag, audio cracking, or other slowdowns. Cloudflare recommends users experiencing these issues upgrade to a minimum Windows 11 24H2 KB5062553 or higher for resolution.
Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Devices with KB5055523 installed may receive a warning about
Win32/ClickFix.ABAbeing present in the installer. To resolve this false positive, update Microsoft Security Intelligence to version 1.429.19.0 or later.DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new GA release for the macOS WARP client is now available on the stable releases downloads page.
This release contains significant fixes and improvements.
Changes and improvements
Proxy mode has been enhanced for even faster resolution. Proxy mode now supports SOCKS4, SOCK5, and HTTP CONNECT over an L4 tunnel with custom congestion control optimizations instead of the previous L3 tunnel to Cloudflare's network. This has more than doubled Proxy mode throughput in lab speed testing, by an order of magnitude in some cases.
The MASQUE protocol is now the only protocol that can use Proxy mode. If you previously configured a device profile to use Proxy mode with Wireguard, you will need to select a new WARP mode or switch to the MASQUE protocol. Otherwise, all devices matching the profile will lose connectivity.
Known issues
macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.