Changelog
New updates and improvements at Cloudflare.
A new GA release for the macOS WARP client is now available on the stable releases downloads page.
This release contains two significant changes all customers should be aware of:
- All DNS traffic now flows inside the WARP tunnel. Customers are no longer required to configure their local firewall rules to allow our DoH IP addresses and domains.
- When using MASQUE, the connection will fall back to HTTP/2 (TCP) when we detect that HTTP/3 traffic is blocked. This allows for a much more reliable connection on some public WiFi networks.
Changes and improvements
- Fixed an issue where the managed network policies could incorrectly report network location beacons as missing.
- Improved DEX test error reporting.
- Fixed an issue causing client notifications to fail in IPv6 only environments which prevented the client from receiving configuration changes to settings like device profile.
- Improved captive portal detection.
- Added a TCP fallback for the MASQUE tunnel protocol to improve connectivity on networks that block UDP or HTTP/3 specifically.
- Added new IP addresses for tunnel connectivity checks. If your organization uses a firewall or other policies you will need to exempt these IPs.
- DNS over HTTPS traffic is now included in the WARP tunnel by default.
- Improved the error message displayed in the client GUI when the rate limit for entering an incorrect admin override code is met.
- Improved handling of non-SLAAC IPv6 interface addresses for better connectivity in IPv6 only environments.
- Fixed an issue where frequent network changes could cause WARP to become unresponsive.
- Improvement for WARP to check if tunnel connectivity fails or times out at device wake before attempting to reconnect.
- Fixed an issue causing WARP connection disruptions after network changes.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
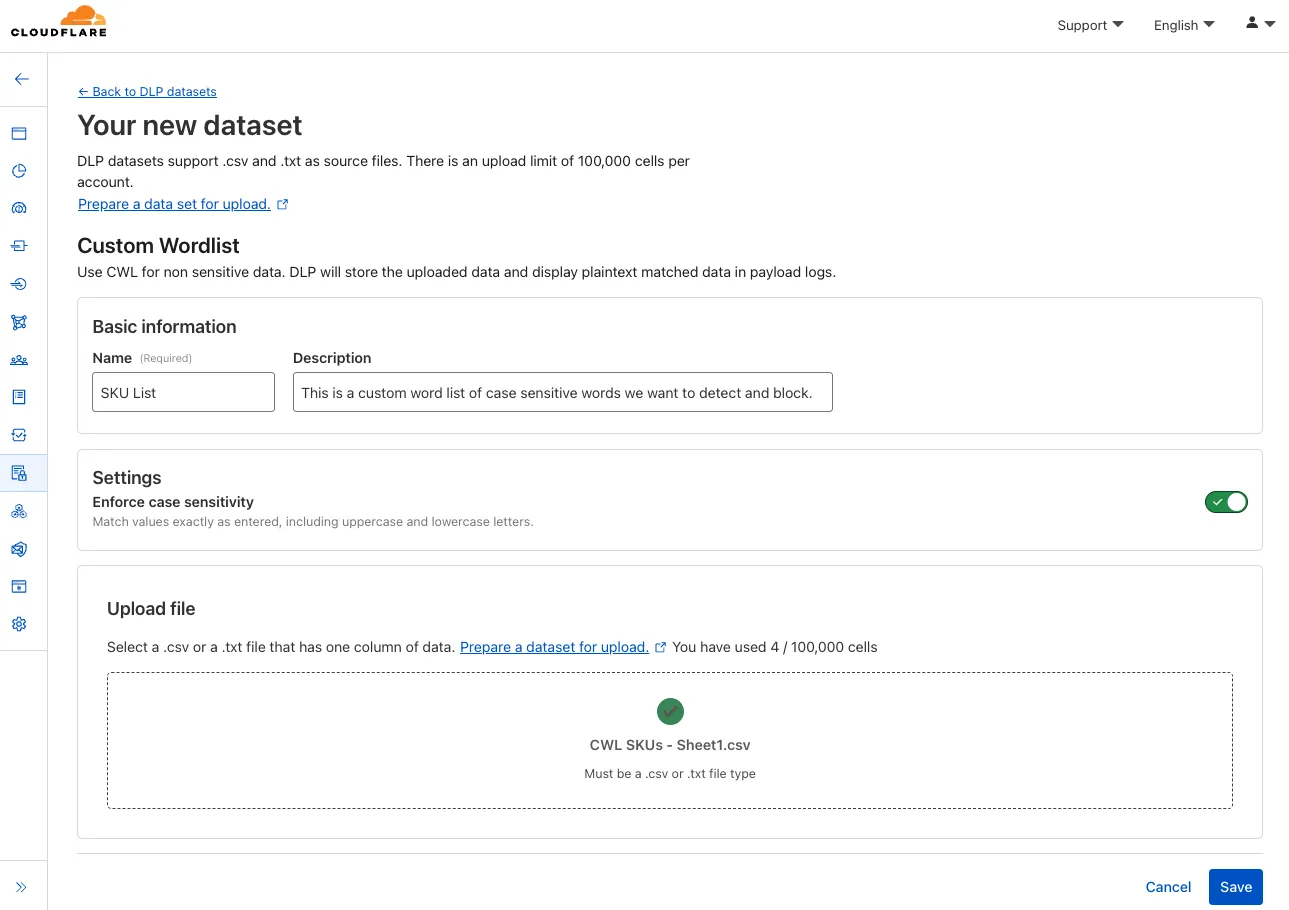
You can now configure custom word lists to enforce case sensitivity. This setting supports flexibility where needed and aims to reduce false positives where letter casing is critical.
You can now safely open links in emails to view and investigate them.

From Investigation, go to View details, and look for the Links identified section. Next to each link, the Cloudflare dashboard will display an Open in Browser Isolation icon which allows your team to safely open the link in a clientless, isolated browser with no risk to the analyst or your environment. Refer to Open links to learn more about this feature.
To use this feature, you must:
- Enable Clientless Web Isolation in your Zero Trust settings.
- Have Browser Isolation (RBI) seats assigned.
For more details, refer to our setup guide.
This feature is available across these Email security packages:
- Advantage
- Enterprise
- Enterprise + PhishGuard
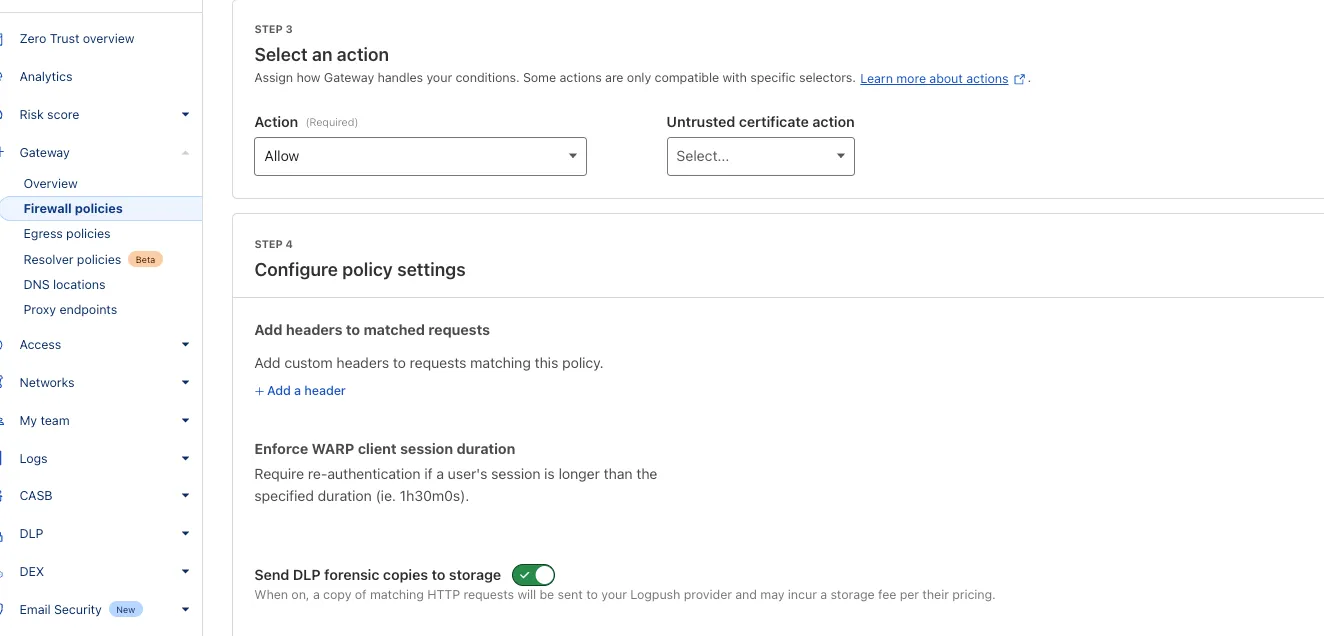
You can now send DLP forensic copies to third-party storage for any HTTP policy with an
AlloworBlockaction, without needing to include a DLP profile. This change increases flexibility for data handling and forensic investigation use cases.By default, Gateway will send all matched HTTP requests to your configured DLP Forensic Copy jobs.
Cloudflare Load Balancing now supports UDP (Layer 4) and ICMP (Layer 3) health monitors for private endpoints. This makes it simple to track the health and availability of internal services that don’t respond to HTTP, TCP, or other protocol probes.
- Set up ICMP ping monitors to check if your private endpoints are reachable.
- Use UDP monitors for lightweight health checks on non-TCP workloads, such as DNS, VoIP, or custom UDP-based services.
- Gain better visibility and uptime guarantees for services running behind Private Network Load Balancing, without requiring public IP addresses.
This enhancement is ideal for internal applications that rely on low-level protocols, especially when used in conjunction with Cloudflare Tunnel, WARP, and Magic WAN to create a secure and observable private network.
Learn more about Private Network Load Balancing or view the full list of supported health monitor protocols.
A new Browser Isolation Overview page is now available in the Cloudflare Zero Trust dashboard. This centralized view simplifies the management of Remote Browser Isolation (RBI) deployments, providing:
- Streamlined Onboarding: Easily set up and manage isolation policies from one location.
- Quick Testing: Validate clientless web application isolation with ease.
- Simplified Configuration: Configure isolated access applications and policies efficiently.
- Centralized Monitoring: Track aggregate usage and blocked actions.
This update consolidates previously disparate settings, accelerating deployment, improving visibility into isolation activity, and making it easier to ensure your protections are working effectively.
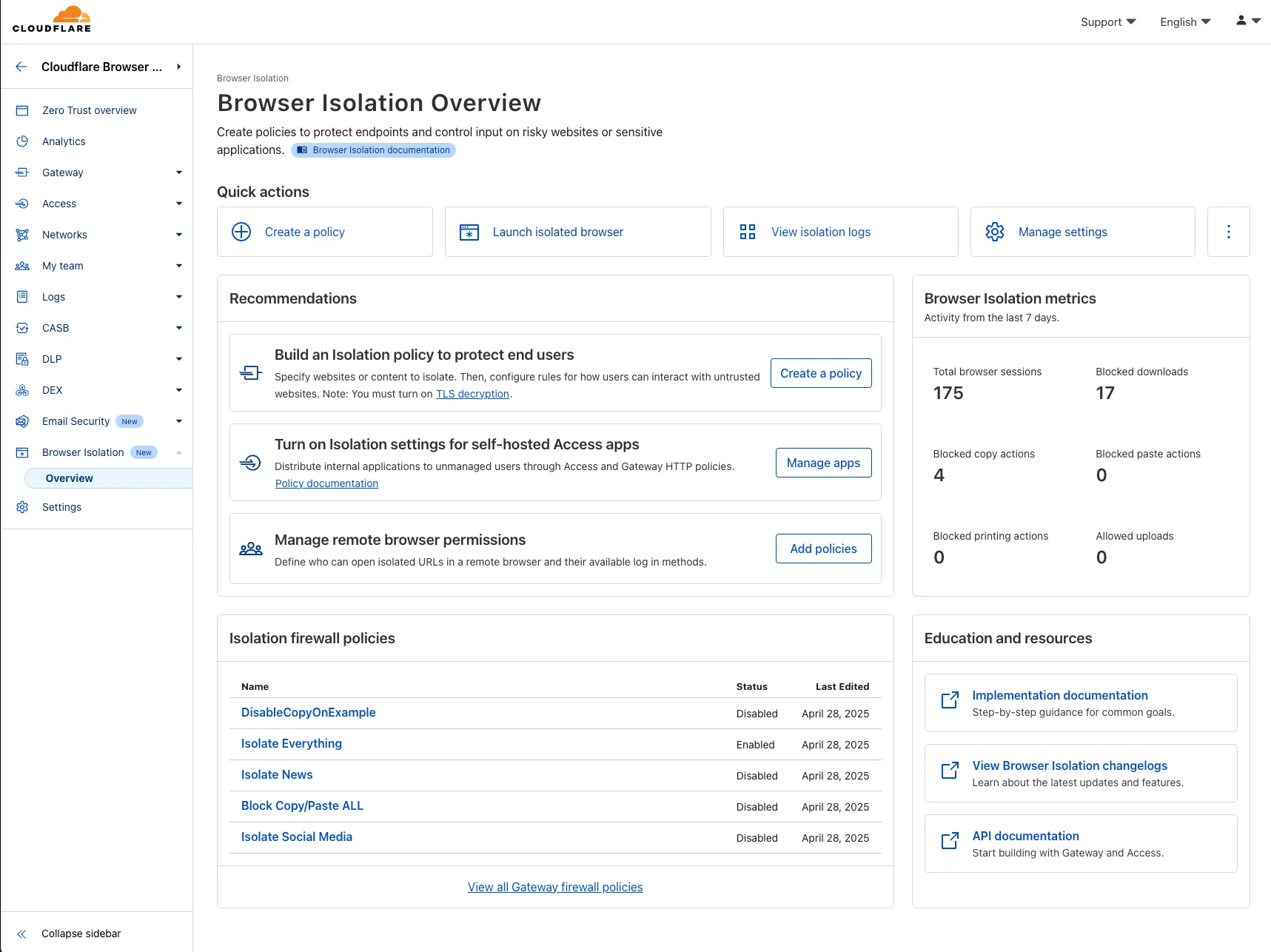
To access the new overview, log in to your Cloudflare Zero Trust dashboard ↗ and find Browser Isolation in the side navigation bar.
The Cloudflare Zero Trust dashboard ↗ now supports Cloudflare's native dark mode for all accounts and plan types.
Zero Trust Dashboard will automatically accept your user-level preferences for system settings, so if your Dashboard appearance is set to 'system' or 'dark', the Zero Trust dashboard will enter dark mode whenever the rest of your Cloudflare account does.
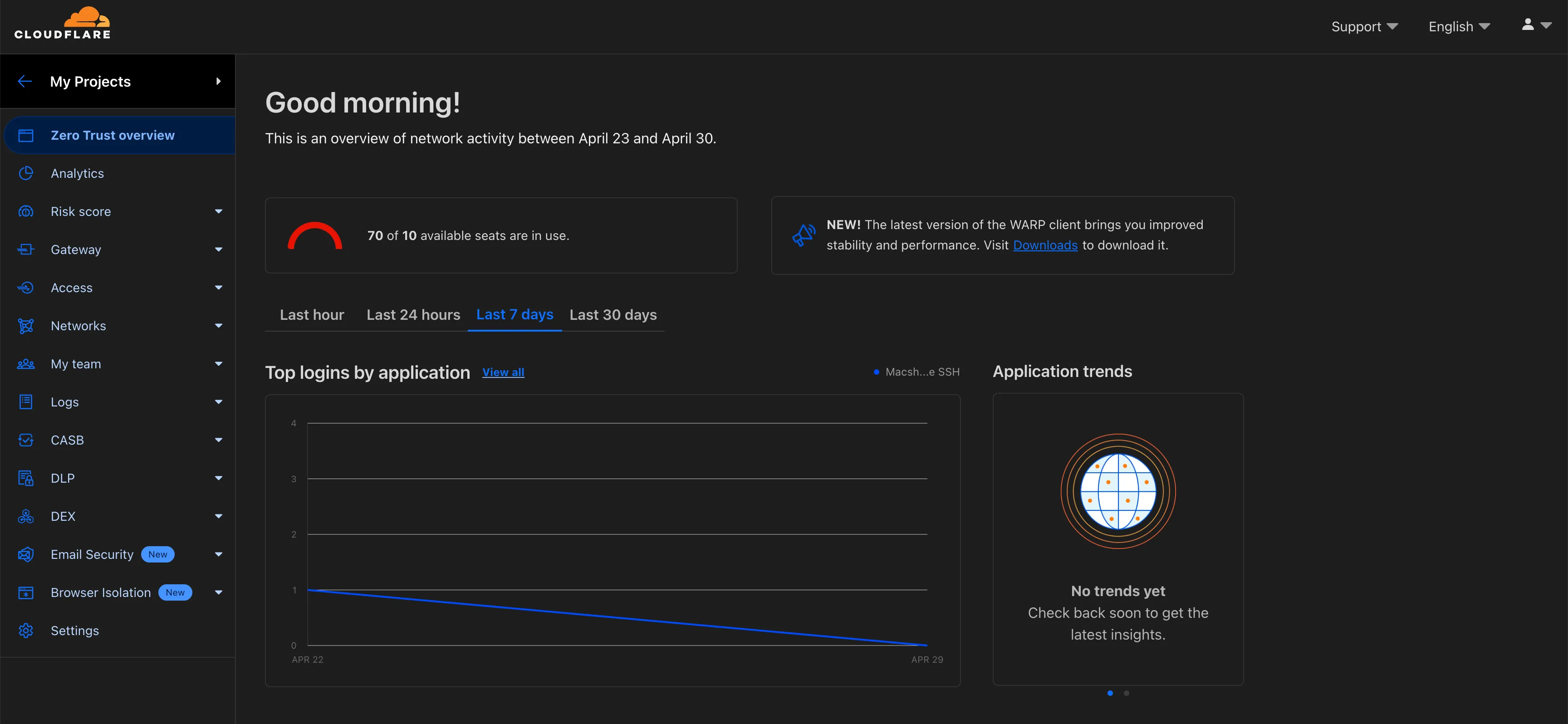
To update your view preference in the Zero Trust dashboard:
- Log into the Zero Trust dashboard ↗.
- Select your user icon.
- Select Dark Mode.
To update your view preference in the Core dashboard:
- Log into the Cloudflare dashboard ↗.
- Go to My Profile
- For Appearance, choose Dark.
Cloudflare One Appliance DHCP server settings now support specifying multiple DNS server IP addresses in the DHCP pool.
Previously, customers could only configure a single DNS server per DHCP pool. With this update, you can specify multiple DNS servers to provide redundancy for clients at branch locations.
For configuration details, refer to DHCP server.
Cloudflare One administrators can now control which egress IP is used based on a destination's fully qualified domain name (FDQN) within Gateway Egress policies.
- Host, Domain, Content Categories, and Application selectors are now available in the Gateway Egress policy builder in beta.
- During the beta period, you can use these selectors with traffic on-ramped to Gateway with the WARP client, proxy endpoints (commonly deployed with PAC files), or Cloudflare Browser Isolation.
- For WARP client support, additional configuration is required. For more information, refer to the WARP client configuration documentation.
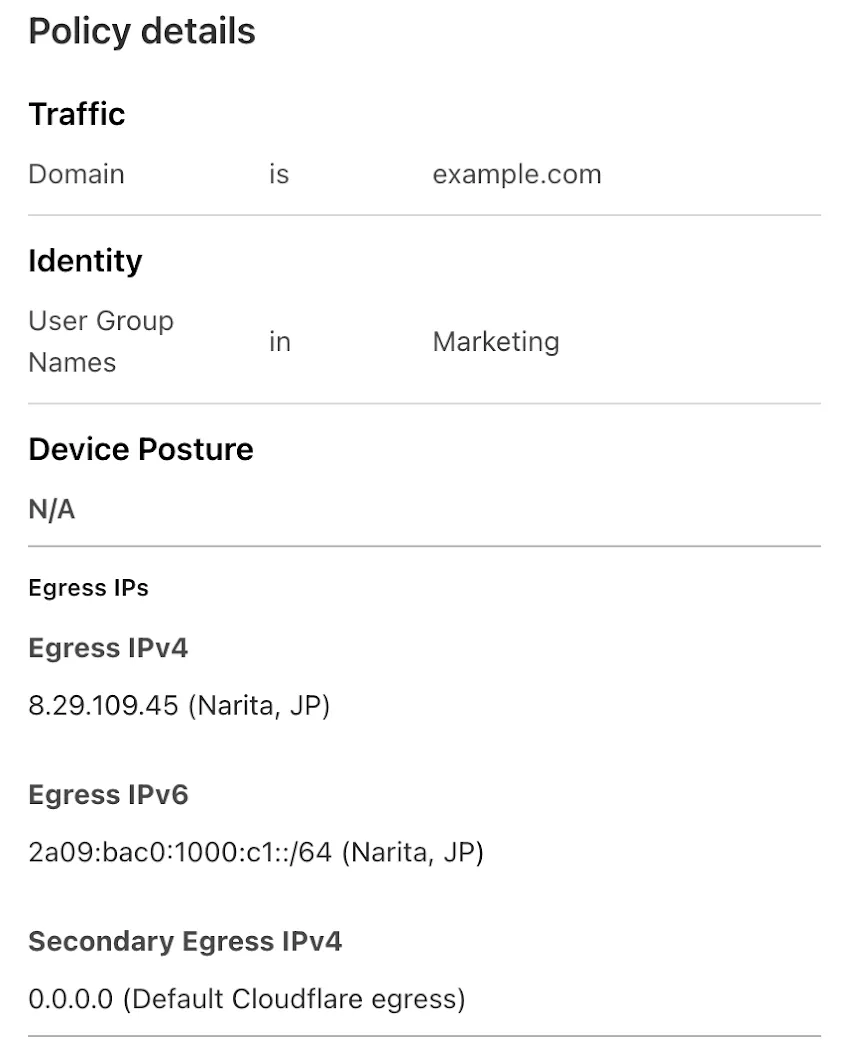
This will help apply egress IPs to your users' traffic when an upstream application or network requires it, while the rest of their traffic can take the most performant egress path.
A new Beta release for the Windows WARP client is now available on the beta releases downloads page.
Changes and improvements
- Fixed an issue causing reconnection loops when captive portals are detected.
- Fixed an issue that caused WARP client disk encryption posture checks to fail due to missing drive names.
- Fixed an issue where managed network policies could incorrectly report network location beacons as missing.
- Improved error reporting for DEX tests.
- Improved WARP client UI high contrast mode.
- Fixed an issue causing client notifications to fail in IPv6 only environments which prevented the client from receiving configuration changes to settings like device profile.
- Added a TCP fallback for the MASQUE tunnel protocol to improve compatibility with networks on MASQUE.
- Added new IP addresses for tunnel connectivity checks. If your organization uses a firewall or other policies you will need to exempt these IPs.
- DNS over HTTPS traffic is now included in the WARP tunnel by default.
- Improved the error message displayed in the client GUI when the rate limit for entering an incorrect admin override code is met.
- Added a Collect Captive Portal Diag button in the client GUI to make it easier for users to collect captive portal debugging diagnostics.
- Improved handling of non-SLAAC IPv6 interface addresses for better connectivity in IPv6 only environments.
- Fixed an issue where frequent network changes could cause WARP to become unresponsive.
Known issues
DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new Beta release for the macOS WARP client is now available on the beta releases downloads page.
Changes and improvements
- Fixed an issue where managed network policies could incorrectly report network location beacons as missing.
- Improved DEX test error reporting.
- Fixed an issue causing client notifications to fail in IPv6 only environments which prevented the client from receiving configuration changes to settings like device profile.
- Improved captive portal detection.
- Added a TCP fallback for the MASQUE tunnel protocol to improve compatibility with networks on MASQUE.
- Added new IP addresses for tunnel connectivity checks. If your organization uses a firewall or other policies you will need to exempt these IPs.
- DNS over HTTPS traffic is now included in the WARP tunnel by default.
- Improved the error message displayed in the client GUI when the rate limit for entering an incorrect admin override code is met.
- Added a Collect Captive Portal Diag button in the client GUI to make it easier for users to collect captive portal debugging diagnostics.
- Improved handling of non-SLAAC IPv6 interface addresses for better connectivity in IPv6 only environments.
- Fixed an issue where frequent network changes could cause WARP to become unresponsive.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
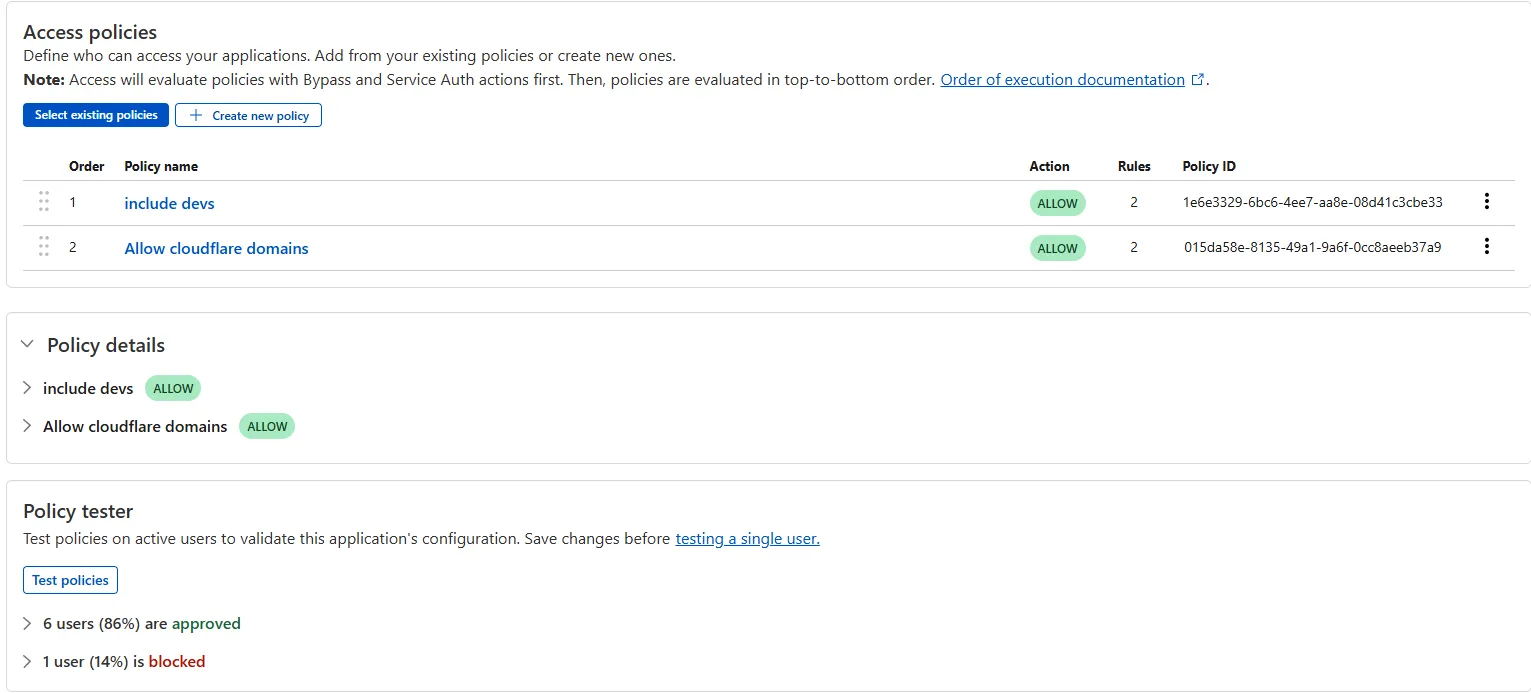
The Access bulk policy tester is now available in the Cloudflare Zero Trust dashboard. The bulk policy tester allows you to simulate Access policies against your entire user base before and after deploying any changes. The policy tester will simulate the configured policy against each user's last seen identity and device posture (if applicable).
You now have access to the World Health Organization (WHO) 2025 edition of the International Classification of Diseases 11th Revision (ICD-11) ↗ as a predefined detection entry. The new dataset can be found in the Health Information predefined profile.
ICD-10 dataset remains available for use.
You can now use more flexible redirect capabilities in Cloudflare One with Gateway.
- A new Redirect action is available in the HTTP policy builder, allowing admins to redirect users to any URL when their request matches a policy. You can choose to preserve the original URL and query string, and optionally include policy context via query parameters.
- For Block actions, admins can now configure a custom URL to display when access is denied. This block page redirect is set at the account level and can be overridden in DNS or HTTP policies. Policy context can also be passed along in the URL.
Learn more in our documentation for HTTP Redirect and Block page redirect.
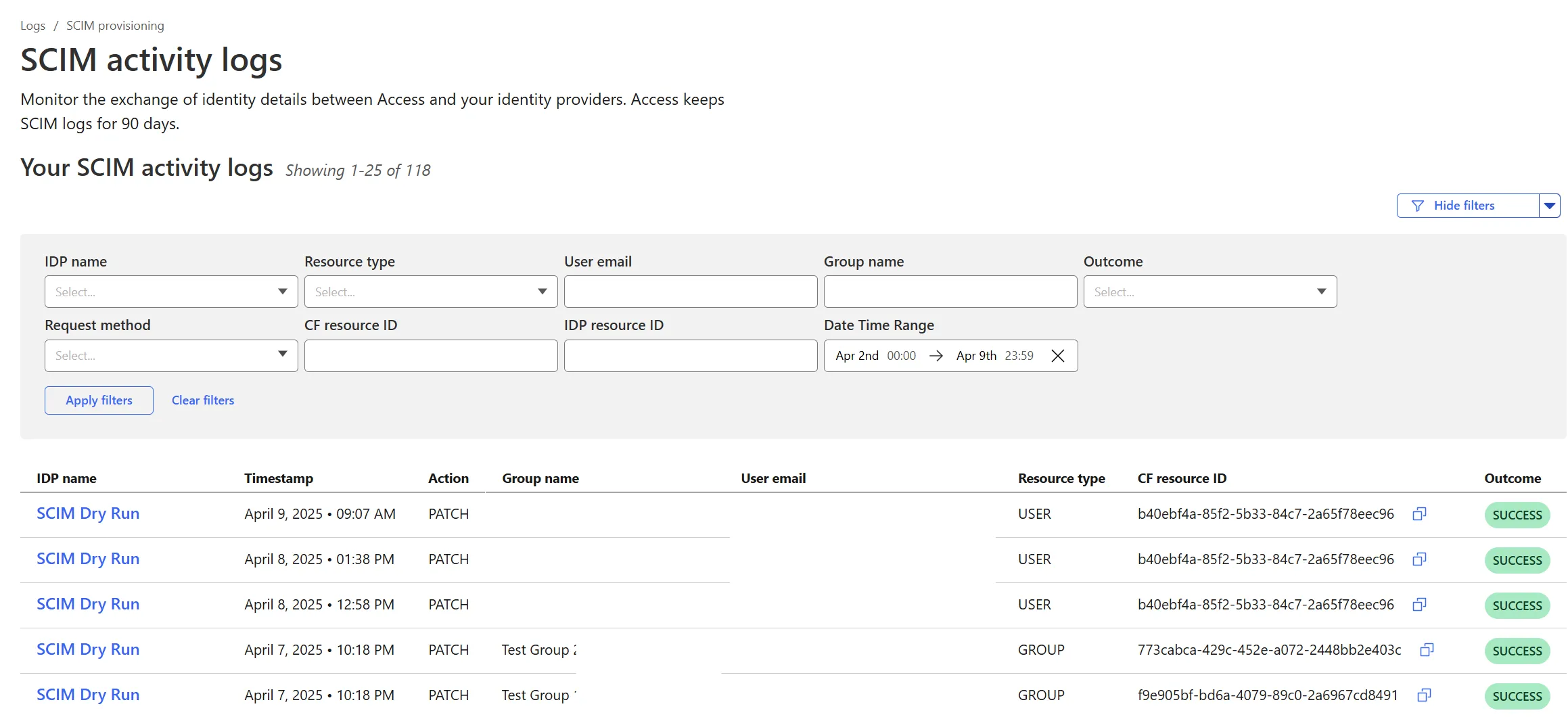
Cloudflare Zero Trust SCIM provisioning now has a full audit log of all create, update and delete event from any SCIM Enabled IdP. The SCIM logs support filtering by IdP, Event type, Result and many more fields. This will help with debugging user and group update issues and questions.
SCIM logs can be found on the Zero Trust Dashboard under Logs -> SCIM provisioning.
A new GA release for the Windows WARP client is now available on the stable releases downloads page.
This release contains a hotfix for captive portal detection for the 2025.2.600.0 release.
Changes and improvements
- Fix to reduce the number of browser tabs opened during captive portal logins.
Known issues
DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new GA release for the macOS WARP client is now available on the stable releases downloads page.
This release contains a hotfix for captive portal detection and PF state tables for the 2025.2.600.0 release.
Changes and improvements
- Fix to reduce the number of browser tabs opened during captive portal logins.
- Improvement to exclude local DNS traffic entries from PF state table to reduce risk of connectivity issues from exceeding table capacity.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
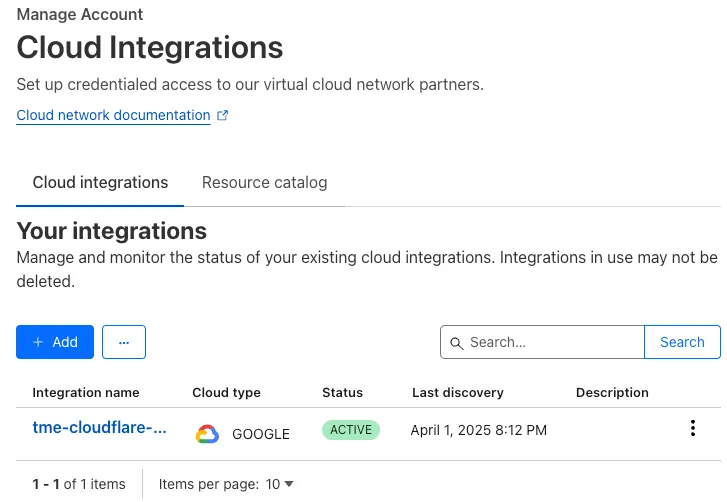
With Email security, you get two free CASB integrations.
Use one SaaS integration for Email security to sync with your directory of users, take actions on delivered emails, automatically provide EMLs for reclassification requests for clean emails, discover CASB findings and more.
With the other integration, you can have a separate SaaS integration for CASB findings for another SaaS provider.
Refer to Add an integration to learn more about this feature.
This feature is available across these Email security packages:
- Enterprise
- Enterprise + PhishGuard
We're excited to introduce the Cloudflare Zero Trust Secure DNS Locations Write role, designed to provide DNS filtering customers with granular control over third-party access when configuring their Protective DNS (PDNS) solutions.
Many DNS filtering customers rely on external service partners to manage their DNS location endpoints. This role allows you to grant access to external parties to administer DNS locations without overprovisioning their permissions.
Secure DNS Location Requirements:
-
Mandate usage of Bring your own DNS resolver IP addresses ↗ if available on the account.
-
Require source network filtering for IPv4/IPv6/DoT endpoints; token authentication or source network filtering for the DoH endpoint.
You can assign the new role via Cloudflare Dashboard (
Manage Accounts > Members) or via API. For more information, refer to the Secure DNS Locations documentation ↗.-
A new GA release for the Android Cloudflare One Agent is now available in the Google Play Store ↗. This release includes a new feature allowing team name insertion by URL during enrollment, as well as fixes and minor improvements.
Changes and improvements
- Improved in-app error messages.
- Improved mobile client login with support for team name insertion by URL.
- Fixed an issue preventing admin split tunnel settings taking priority for traffic from certain applications.
A new GA release for the iOS Cloudflare One Agent is now available in the iOS App Store ↗. This release includes a new feature allowing team name insertion by URL during enrollment, as well as fixes and minor improvements.
Changes and improvements
- Improved in-app error messages.
- Improved mobile client login with support for team name insertion by URL.
- Bug fixes and performance improvements.
Magic Firewall now supports a new managed list of Cloudflare IP ranges. This list is available as an option when creating a Magic Firewall policy based on IP source/destination addresses. When selecting "is in list" or "is not in list", the option "Cloudflare IP Ranges" will appear in the dropdown menu.
This list is based on the IPs listed in the Cloudflare IP ranges ↗. Updates to this managed list are applied automatically.
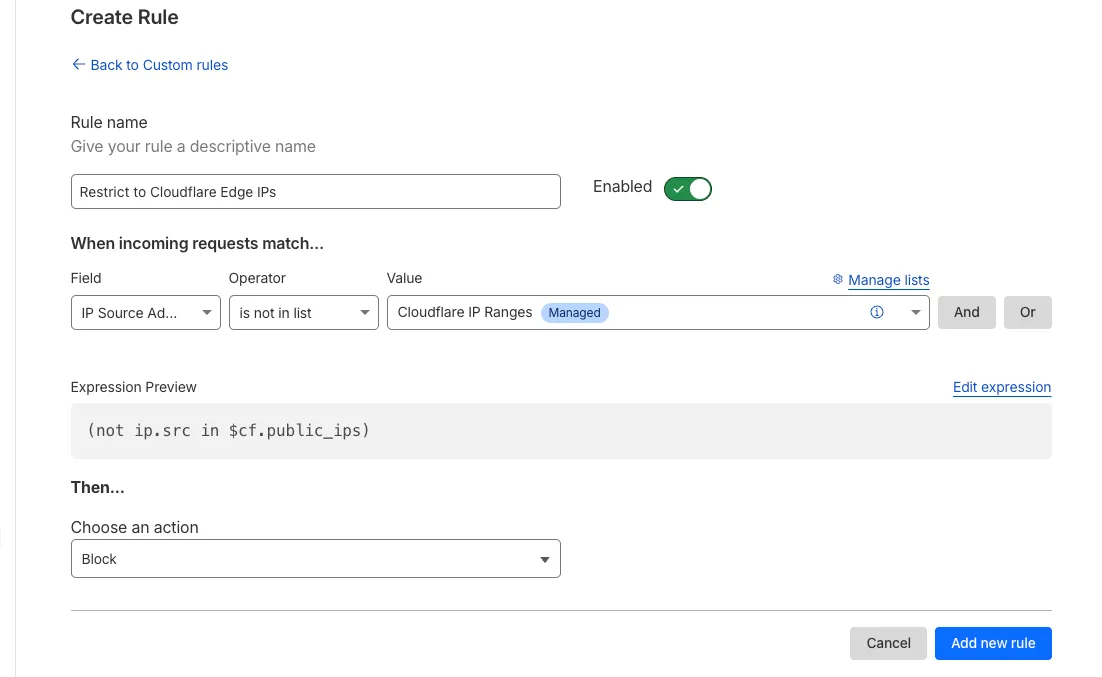
Note: IP Lists require a Cloudflare Advanced Network Firewall subscription. For more details about Cloudflare Network Firewall plans, refer to Plans.
Digital Experience Monitoring (DEX) provides visibility into device, network, and application performance across your Cloudflare SASE deployment. The latest release of the Cloudflare One agent (v2025.1.861) now includes device endpoint monitoring capabilities to provide deeper visibility into end-user device performance which can be analyzed directly from the dashboard.
Device health metrics are now automatically collected, allowing administrators to:
- View the last network a user was connected to
- Monitor CPU and RAM utilization on devices
- Identify resource-intensive processes running on endpoints
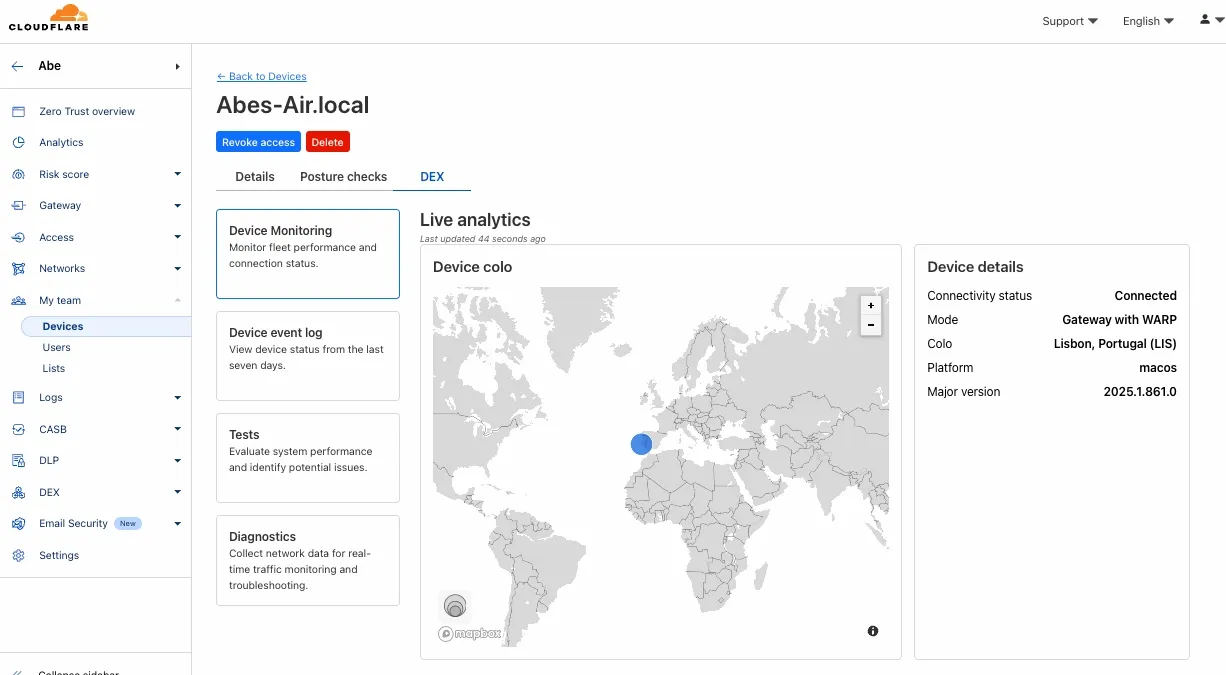
This feature complements existing DEX features like synthetic application monitoring and network path visualization, creating a comprehensive troubleshooting workflow that connects application performance with device state.
For more details refer to our DEX documentation.
We're excited to announce that new logging capabilities for Remote Browser Isolation (RBI) through Logpush are available in Beta starting today!
With these enhanced logs, administrators can gain visibility into end user behavior in the remote browser and track blocked data extraction attempts, along with the websites that triggered them, in an isolated session.
{"AccountID": "$ACCOUNT_ID","Decision": "block","DomainName": "www.example.com","Timestamp": "2025-02-27T23:15:06Z","Type": "copy","UserID": "$USER_ID"}User Actions available:
- Copy & Paste
- Downloads & Uploads
- Printing
Learn more about how to get started with Logpush in our documentation.
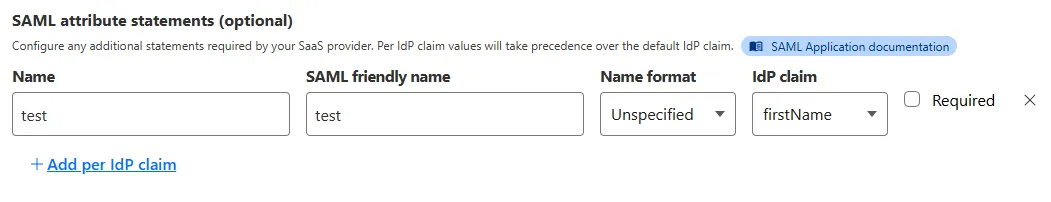
Access for SaaS applications now include more configuration options to support a wider array of SaaS applications.
SAML and OIDC Field Additions
OIDC apps now include:
- Group Filtering via RegEx
- OIDC Claim mapping from an IdP
- OIDC token lifetime control
- Advanced OIDC auth flows including hybrid and implicit flows
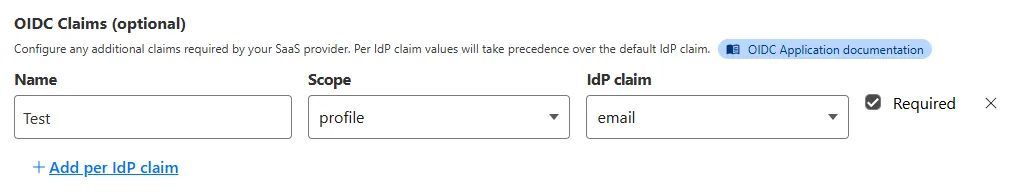
SAML apps now include improved SAML attribute mapping from an IdP.
SAML transformations
SAML identities sent to Access applications can be fully customized using JSONata expressions. This allows admins to configure the precise identity SAML statement sent to a SaaS application.