Changelog
New updates and improvements at Cloudflare.
Key Findings
- Existing rule enhancements have been deployed to improve detection resilience against broad classes of web attacks and strengthen behavioral coverage.
Continuous Rule Improvements
We are continuously refining our managed rules to provide more resilient protection and deeper insights into attack patterns. To ensure an optimal security posture, we recommend consistently monitoring the Security Events dashboard and adjusting rule actions as these enhancements are deployed.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Sitecore - Cache Poisoning - CVE:CVE-2025-53693 Beta N/A Block This rule is merged into the original rule "Sitecore - Cache Poisoning - CVE:CVE-2025-53693" (ID:
This emergency release introduces two new rules to detect nginx heap buffer overflow and heap spray exploitation attempts targeting the rewrite module's
is_argsstale-state bug (CVE-2026-42945).Key Findings
CVE-2026-42945: nginx Heap Buffer Overflow via Stale
is_argsin Rewrite ModuleSuccessful exploitation allows remote attackers to trigger a heap buffer overflow in nginx's rewrite module by sending crafted URIs containing escapable characters. A length/copy pass mismatch in
ngx_http_script_copy_capture_code()causes the copy pass to write escaped data into an undersized buffer, leading to heap corruption. This enables denial of service (worker process crash) and, with heap feng shui techniques, potential remote code execution.We strongly recommend upgrading to nginx 1.30.1 (or later) immediately to address the underlying vulnerability. If you cannot upgrade immediately, avoid
rewritedirectives with?in the replacement string followed bysetorifreferencing capture groups.Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A nginx - Remote Code Execution - Buffer Overread - CVE:CVE-2026-42945 N/A Block This is a new detection.
Cloudflare Managed Ruleset N/A nginx - Remote Code Execution - Heap Spray - CVE:CVE-2026-42945 N/A Block This is a new detection.
Key Findings
- Existing rule enhancements have been deployed to improve detection resilience against broad classes of web attacks and strengthen behavioral coverage.
Continuous Rule Improvements
We are continuously refining our managed rules to provide more resilient protection and deeper insights into attack patterns. To ensure an optimal security posture, we recommend consistently monitoring the Security Events dashboard and adjusting rule actions as these enhancements are deployed.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Remote Code Execution - Java Deserialization - Body - Beta Block Disabled This is a new detection. This rule is merged into the original rule "Remote Code Execution - Java Deserialization" (ID:
Announcement Date Release Date Release Behavior Legacy Rule ID Rule ID Description Comments 2026-05-11 2026-05-18 Disabled N/A Sitecore - Cache Poisoning - CVE:CVE-2025-53693 This is a new detection. This rule will be merged into the original rule "Remote Code Execution - Java Deserialization" (ID:
Multiple security vulnerabilities were disclosed by the React team and Vercel affecting React Server Components and Next.js. These include denial of service, middleware and proxy bypass, server-side request forgery, cross-site scripting, and cache poisoning issues across a range of severity levels.
We strongly recommend updating your application and its dependencies immediately. Patched versions are available for React (
react-server-dom-webpack,react-server-dom-parcel, andreact-server-dom-turbopack19.0.6,19.1.7, and19.2.6) and Next.js (15.5.16and16.2.5).Cloudflare WAF rules deployed in response to prior React Server Component CVEs (
CVE-2025-55184↗ andCVE-2026-23864↗) already provide coverage for the newly disclosed denial-of-service vulnerabilities. These rules are enabled by default with a Block action for all customers using the Cloudflare Managed Ruleset, including Free plan customers using the Free Managed Ruleset.Ruleset Rule description Rule ID Default action Cloudflare Managed Ruleset React - DoS - CVE-2025-55184↗2694f1610c0b471393b21aef102ec699Block Cloudflare Managed Ruleset React - DoS - CVE-2026-23864↗aaede80b4d414dc89c443cea61680354Block The existing rules detect the underlying attack patterns generically. As a result, they apply to the new
CVE-2026-23870↗ denial-of-service vulnerability in Server Components and the corresponding Next.js advisoryGHSA-8h8q-6873-q5fj↗.Cloudflare is investigating whether WAF rules can be safely and effectively deployed for three of the high-severity advisories:
CVE-2026-23870↗ /GHSA-8h8q-6873-q5fj↗,GHSA-267c-6grr-h53f↗, andGHSA-mg66-mrh9-m8jx↗. If it is possible to create a managed WAF rule that mitigates these CVEs and does not potentially break application behavior, Cloudflare will add additional managed WAF rules. These rules will be announced through the WAF changelog. Because these vulnerabilities were shared with Cloudflare with minimal advance notice, we are still investigating what WAF mitigations are possible.Several of the disclosed vulnerabilities are not possible to block in WAF. We strongly recommend updating your applications so they are not purely reliant on WAF mitigations.
Customers on Pro, Business, or Enterprise plans should ensure that Managed Rules are enabled.
Vinext: Vinext ↗ is a Vite plugin that reimplements the Next.js API surface. Vinext's latest release is not vulnerable to any of the disclosed CVEs. Vinext's architecture differs from stock Next.js in ways that sidestep the affected code paths. For example, it does not implement the PPR resume protocol, does not expose Pages Router data-route endpoints, and strips internal headers such as
x-nextjs-dataat request boundaries. As an extra layer of defense, we added a React19.2.6or later requirement when runningvinext init(PR #1118 ↗, PR #1112 ↗) to prevent accidentally running a vulnerable version of React with Vinext.OpenNext on Cloudflare: OpenNext is an adapter that lets you deploy Next.js apps to the Cloudflare Workers platform. OpenNext itself is not directly vulnerable to the React denial-of-service CVE, but users must update the Next.js version in their application. The OpenNext team has updated the adapter to further harden against these vectors and released a new version of the Cloudflare adapter. Test fixtures and examples have been updated to use patched versions (PR #1255 ↗).
Advisory Severity Issue WAF status CVE-2026-23870↗ /GHSA-8h8q-6873-q5fj↗High Denial of service in Server Components WAF rules in place: 2694f1610c0b471393b21aef102ec699,aaede80b4d414dc89c443cea61680354
Cloudflare is investigating additional managed WAF coverageGHSA-267c-6grr-h53f↗High Middleware bypass via segment-prefetch routes Cloudflare is investigating if this can be safely and effectively mitigated by a managed WAF rule GHSA-mg66-mrh9-m8jx↗High Denial of service via connection exhaustion in Cache Components Cloudflare is investigating if this can be safely and effectively mitigated by a managed WAF rule GHSA-492v-c6pp-mqqv↗High Middleware bypass via dynamic route parameter injection Not possible to safely enable a managed WAF rule without potentially breaking application behavior GHSA-c4j6-fc7j-m34r↗High SSRF via WebSocket upgrades Not possible to safely enable a managed WAF rule without potentially breaking application behavior GHSA-36qx-fr4f-26g5↗High Middleware bypass in Pages Router i18n Custom WAF rule possible; global managed rule could potentially break application behavior GHSA-ffhc-5mcf-pf4q↗Moderate XSS via CSP nonces Custom WAF rule possible; global managed rule could potentially break application behavior GHSA-gx5p-jg67-6x7h↗Moderate XSS in beforeInteractivescriptsNot possible to safely enable a managed WAF rule without potentially breaking application behavior GHSA-h64f-5h5j-jqjh↗Moderate Denial of service in Image Optimization API Custom WAF rule possible; global managed rule could potentially break application behavior GHSA-wfc6-r584-vfw7↗Moderate Cache poisoning in RSC responses Custom WAF rule possible; global managed rule could potentially break application behavior GHSA-vfv6-92ff-j949↗Low Cache poisoning via RSC cache-busting collisions Not possible to safely enable a managed WAF rule without potentially breaking application behavior GHSA-3g8h-86w9-wvmq↗Low Middleware redirect cache poisoning Custom WAF rule possible; global managed rule could potentially break application behavior
You can now export your Requests for Information (RFI) history to a CSV document and customize your dashboard view by choosing how many RFI records to load per page.
These quality-of-life updates focus on data portability and dashboard performance, allowing power users to manage high volumes of requests more efficiently:
- The new CSV export allows you to move RFI data into external tools for custom reporting, internal auditing, or cross-referencing with other security projects without manual data entry
- With adjustable page density, you can now choose to load more records at once (10, 25 or 50) to scan through history faster
Cloudforce One subscribers can find these new options in Cloudflare Dashboard > Application Security > Threat Intelligence > Requests for Information ↗.
This emergency release introduces a new rule to detect Next.js App Router middleware and proxy bypass attempts via segment-prefetch routes (CVE-2026-44575).
Key Findings
CVE-2026-44575: Next.js Middleware / Proxy Bypass in App Router Applications via Segment-Prefetch Routes
Successful exploitation allows unauthenticated attackers to bypass middleware or proxy-based authorization checks in affected Next.js App Router applications. This leads to unauthorized access to protected content, potential exposure of sensitive application data, and compromise of application security boundaries.
We strongly recommend upgrading to Next.js 15.5.16 or 16.2.5 (or later) immediately to address the underlying vulnerability. If you cannot upgrade immediately, enforce authorization in the underlying route or page logic instead of relying solely on middleware.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Next.js - Middleware Bypass via Invalid RSC Header - CVE:CVE-2026-44575 N/A Disabled This is a new detection.
The Cloudforce One Threat Events API now supports TAXII ↗ as an output format, enabling standardized, automated sharing of cyber threat intelligence with your existing security stack.
- You can now ingest Cloudforce One threat data directly into your SIEM, TIP or SOAR tools that prefer TAXII-formatted streams without needing custom translation scripts.
- By supporting the TAXII format parameter in our API, security teams can automate the synchronization of indicator data, reducing the manual overhead of updating blocklists and detection rules.
- This alignment with industry standards ensures that your threat data remains consistent across different security ecosystems and partner integrations.
When calling the Threat Events API, you can now specify
taxiiin theformatquery parameter:GET /accounts/{account_id}/cloudforce_one/threat_events?format=taxiiYou can find the updated documentation in the Cloudflare API Reference ↗.
This week's release focuses on new detections to expand coverage across command injection, SQL injection, PHP object injection, remote code execution, and XSS attack vectors.
Key Findings
- Existing rule enhancements have been deployed to improve detection resilience against broad classes of web attacks and strengthen behavioral coverage.
Continuous Rule Improvements
We are continuously refining our managed rules to provide more resilient protection and deeper insights into attack patterns. To ensure an optimal security posture, we recommend consistently monitoring the Security Events dashboard and adjusting rule actions as these enhancements are deployed.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A XSS, HTML Injection - Object Tag - Body (beta) Log Block This is a new detection. This rule is merged into the original rule "XSS, HTML Injection - Object Tag" (ID:
Cloudflare Managed Ruleset N/A XSS, HTML Injection - Object Tag - Headers Log Block This is a new detection. The rule previously known as "XSS, HTML Injection - Object Tag - Headers (beta)" is now renamed to "XSS, HTML Injection - Object Tag - Headers".
Cloudflare Managed Ruleset N/A XSS, HTML Injection - Object Tag - URI Log Block This is a new detection. The rule previously known as "XSS, HTML Injection - Object Tag - URI (beta)" is now renamed to "XSS, HTML Injection - Object Tag - URI".
Cloudflare Managed Ruleset N/A Command Injection - Generic 9 - Body Vector - Beta N/A Disabled This is a new detection. This rule is merged into the original rule "Command Injection - Generic 9 - Body Vector" (ID:
Cloudflare Managed Ruleset N/A Command Injection - Generic 9 - Header Vector - Beta N/A Disabled This is a new detection. This rule is merged into the original rule "Command Injection - Generic 9 - Header Vector" (ID:
Cloudflare Managed Ruleset N/A Command Injection - Generic 9 - URI Vector - Beta N/A Disabled This is a new detection. This rule is merged into the original rule "Command Injection - Generic 9 - URI Vector" (ID:
Cloudflare Managed Ruleset N/A Command Injection - Sleep - Body N/A Disabled This is a new detection. The rule previously known as "Command Injection
- Sleep" is now renamed to "Command Injection - Sleep - Body".
Cloudflare Managed Ruleset N/A Command Injection - Sleep - Headers N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A Command Injection - Sleep - URI N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A Fortinet FortiSandbox - Command Injection - CVE:CVE-2026-39808 Log Block This is a new detection. Cloudflare Managed Ruleset N/A Remote Code Execution - Common Bash Bypass - Headers N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A Remote Code Execution - Common Bash Bypass - URI N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A Remote Code Execution - Common Bash Bypass - Body - Beta N/A Disabled This is a new detection. This rule is merged into the original rule "Remote Code Execution - Common Bash Bypass Body" (ID:
Cloudflare Managed Ruleset N/A PHP Object Injection - 2 - Body - Beta N/A Disabled This is a new detection. This rule is merged into the original rule "PHP Object Injection - 2" (ID:
Cloudflare Managed Ruleset N/A PHP Object Injection - 2 - Headers N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A PHP Object Injection - 2 - URI N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - DROP - 2 - Beta N/A Disabled This is a new detection. This rule is merged into the original rule "SQLi - DROP - 2" (ID:
Cloudflare Managed Ruleset N/A SQLi - DROP - 2 - Headers N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - DROP - 2 - URI N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A SmarterMail - Remote Code Execution - CVE:CVE-2026-24423 Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - SELECT Expression - Body Block Disabled Action changed Cloudflare Managed Ruleset N/A SQLi - String Concatenation - URI Block Disabled Action changed
This emergency release introduces a new rule to block a cPanel & WHM Authentication Bypass related to CVE-2026-41940.
Key Findings
- CVE-2026-41940: A critical authentication bypass vulnerability in cPanel & WHM allows unauthenticated remote attackers to bypass authentication mechanisms and gain unauthorized administrative access to the web hosting control panel. This vulnerability affects the session validation logic, enabling attackers to craft malicious requests that circumvent normal authentication checks.
Impact
Successful exploitation allows unauthenticated attackers to gain administrative control over affected cPanel & WHM installations. This leads to complete server compromise, potential theft or manipulation of hosted data, and significant service disruption across managed environments.
We strongly recommend applying official vendor patches for cPanel & WHM immediately to address the underlying vulnerability.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A cPanel - Auth Bypass - CVE:CVE-2026-41940 N/A Block This is a new detection.
We have introduced a unified investigation workspace within Brand Protection to help analysts manage complex brand portfolios. Instead of jumping between individual queries, you can now consolidate your workflow into a single, cohesive view.
- You can now elect multiple saved queries from your dashboard to generate a consolidated "Combined Matches" view. This allows you to triage results from different brand queries in one unified table
- You can open query extended views in distinct tabs within the Brand Protection dashboard. This enables you to maintain multiple investigation contexts simultaneously and switch between them without losing your place.
- You can reset your workspace using the new "Clear Selection" action, making it easier to pivot between different investigation sets.
- Eliminate fragmented workflows by viewing all matches across different query buckets in a single table, reducing the need to click through dozens of individual query pages
- Correlate related campaigns by seeing similar domains or infrastructure patterns that appear across multiple saved queries
Learn more in our Brand Protection documentation.
This week's release focuses on new improvements to enhance coverage.
Key Findings
- Existing rule enhancements have been deployed to improve detection resilience against broad classes of web attacks and strengthen behavioral coverage.
Continuous Rule Improvements
We are continuously refining our managed rules to provide more resilient protection and deeper insights into attack patterns. To ensure an optimal security posture, we recommend consistently monitoring the Security Events dashboard and adjusting rule actions as these enhancements are deployed.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A PostgreSQL - SQLi - COPY - Beta Log Block This is a new detection. This rule is merged into the original rule "PostgreSQL - SQLi - COPY - Body (ID:
Cloudflare Managed Ruleset N/A PostgreSQL - SQLi - COPY - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A PostgreSQL - SQLi - COPY - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - AND/OR MAKE_SET/ELT - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - AND/OR MAKE_SET/ELT - Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - AND/OR MAKE_SET/ELT - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - AND/OR MAKE_SET/ELT - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Common Patterns - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - Common Patterns - Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - Common Patterns - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Common Patterns - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Equation - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - Equation - Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - Equation - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Equation - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - AND/OR Digit Operator Digit - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - AND/OR Digit Operator Digit - Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - AND/OR Digit Operator Digit - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - AND/OR Digit Operator Digit - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Benchmark Function - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - Benchmark Function - Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - Benchmark Function - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Benchmark Function - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Comparison - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - Comparison - Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - Comparison - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Comparison - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - String Concatenation - Body - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - String Concatenation - Headers" (ID: Cloudflare Managed Ruleset N/A SQLi - String Concatenation - Headers Log Block This is a new detection.(Former Id was Cloudflare Managed Ruleset N/A SQLi - String Concatenation - URI Log Block This is a new detection. (Former Id was Cloudflare Managed Ruleset N/A SQLi - SELECT Expression - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - SELECT Expression - Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - SELECT Expression - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - SELECT Expression - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - ORD and ASCII - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - ORD and ASCII- Body" (ID:
Cloudflare Managed Ruleset N/A SQLi - ORD and ASCII - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - ORD and ASCII - Headers Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Destructive Operations Log Block This is a new detection.
This week's release introduces a new detection for a Remote Code Execution (RCE) vulnerability in Apache ActiveMQ (CVE-2026-34197) and an updated signature for Magento 2 - Unrestricted File Upload. Alongside these detections, we are continuing our work on rule refinements to provide deeper security insights for our customers.
Key Findings
-
Apache ActiveMQ (CVE-2026-34197): A vulnerability in Apache ActiveMQ allows an unauthenticated, remote attacker to execute arbitrary code. This flaw occurs during the processing of specially crafted network packets, leading to potential full system compromise.
-
Magento 2 - Unrestricted File Upload - 2: This is a follow-up enhancement to our existing protections for Magento and Adobe Commerce.
Impact
Successful exploitation of these vulnerabilities could allow unauthenticated attackers to execute arbitrary code or gain full administrative control over affected servers. We strongly recommend applying official vendor patches for Apache ActiveMQ and Magento to address the underlying vulnerabilities.
Continuous Rule Improvements
We are continuously refining our managed rules to provide more resilient protection and deeper insights into attack patterns. To ensure an optimal security posture, we recommend consistently monitoring the Security Events dashboard and adjusting rule actions as these enhancements are deployed.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Command Injection - Generic 8 - uri Log Block This is a new detection. Previous description was "Command Injection - Generic 8 - uri - Beta" Cloudflare Managed Ruleset N/A Command Injection - Generic 8 - body - Beta Disabled Disabled This is a new detection. This rule is merged into the original rule "Command Injection - Generic 8 - body" (ID:
Cloudflare Managed Ruleset N/A MySQL - SQLi - Executable Comment - Beta Log Block This is a new detection. This rule is merged into the original rule "MySQL - SQLi - Executable Comment - Body" (ID:
Cloudflare Managed Ruleset N/A MySQL - SQLi - Executable Comment - Headers Log Block This is a new detection.
Cloudflare Managed Ruleset N/A MySQL - SQLi - Executable Comment - URI Log Block This is a new detection.
Cloudflare Managed Ruleset N/A Magento 2 - Unrestricted file upload - 2 Log Block This is a new detection.
Cloudflare Managed Ruleset N/A Apache ActiveMQ - Remote Code Execution - CVE:CVE-2026-34197 Log Block This is a new detection.
Cloudflare Managed Ruleset N/A SQLi - Sleep Function - Beta Log Block This is a new detection. This rule is merged into the original rule "SQLi - Sleep Function" (ID:
Cloudflare Managed Ruleset N/A SQLi - Sleep Function - Headers Log Block This is a new detection.
Cloudflare Managed Ruleset N/A SQLi - Sleep Function - URI Log Block This is a new detection.
Cloudflare Managed Ruleset N/A SQLi - Probing - uri Log Block This is a new detection.
Cloudflare Managed Ruleset N/A SQLi - Probing - header Log Block This is a new detection.
Cloudflare Managed Ruleset N/A SQLi - Probing - body Disabled Disabled This is a new detection. This rule is merged into the original rule "SQLi - Probing" (ID:
Cloudflare Managed Ruleset N/A SQLi - Probing 2 Disabled Disabled This rule had duplicate detection logic and has been deprecated.
Cloudflare Managed Ruleset N/A SQLi - UNION in MSSQL - Body Disabled Disabled This rule has been renamed to differentiate from "SQLi - UNION in MSSQL" (ID:
Cloudflare Managed Ruleset N/A SQLi - UNION - 3 Disabled Disabled This rule had duplicate detection logic and has been deprecated.
Cloudflare Managed Ruleset N/A XSS, HTML Injection - Embed Tag - URI Disabled Disabled This is a new detection.
Cloudflare Managed Ruleset N/A XSS, HTML Injection - Embed Tag - Headers Log Block This is a new detection.
Cloudflare Managed Ruleset N/A XSS, HTML Injection - IFrame Tag - Src and Srcdoc Attributes - Headers Log Disabled This is a new detection.
Cloudflare Managed Ruleset N/A XSS, HTML Injection - Link Tag - Headers Log Disabled This is a new detection.
Cloudflare Managed Ruleset N/A XSS, HTML Injection - Link Tag - URI Disabled Disabled This is a new detection.
-
-
Introducing enhanced archiving capabilities for security action items within the Security Overview dashboard. This update allows security teams to maintain a cleaner workspace by removing resolved, accepted, or irrelevant items from their active list while maintaining a clear paper trail for compliance.
Managing a high volume of security insights can be overwhelming. Previously, users lacked a structured way to dismiss items without losing the context of why they were ignored.
With these new archiving options—False Positive, Accept Risk, and Other—you can now suppress items indefinitely with required rationale text for risk-based decisions. This ensures that your team remains focused on critical, actionable vulnerabilities while preserving institutional knowledge for audits.
- Structured Archiving: Choose from specific categories to define why an action item is being moved.
- Required Rationale: For "Accept Risk" and "Other" categories, users must provide documentation, ensuring accountability for security decisions.
- Audit Log Transparency: New API endpoints allow you to programmatically retrieve the history of status changes and rationale for any insight at the account or zone level.
- Reversible Actions: Any archived item can be moved back to the active list at any time if the security context changes.
To review the history and rationale of a specific archived issue at the account level, you can use the following API command:
Terminal window curl "[https://api.cloudflare.com/client/v4/accounts/](https://api.cloudflare.com/client/v4/accounts/){account_id}/insights/{insight_id}/audit-log" \-H "Authorization: Bearer <API_TOKEN>" \-H "Content-Type: application/json"
This week's release introduces a new detection for a critical Remote Code Execution (RCE) vulnerability in Mesop (CVE-2026-33057), alongside protections for high-impact vulnerabilities in Cisco Secure Firewall Management Center (CVE-2026-20079) and FortiClient EMS (CVE-2026-21643). Additionally, this release includes an update to our existing React Server DoS coverage to address recently identified resource exhaustion vectors (CVE-2026-23869).
Key Findings
-
Cisco Secure FMC (CVE-2026-20079): A vulnerability in the web-based management interface of Cisco Secure Firewall Management Center (FMC) that allows an unauthenticated, remote attacker to execute arbitrary commands or bypass security filters.
-
FortiClient EMS (CVE-2026-21643): A critical vulnerability in the FortiClient EMS permitting unauthorized access or administrative configuration manipulation via crafted HTTP requests.
-
Mesop (CVE-2026-33057): A vulnerability in the Mesop Python-based UI framework where unauthenticated attackers can execute arbitrary code by sending specially crafted, Base64-encoded payloads in the request body.
Impact
Successful exploitation of these vulnerabilities could allow unauthenticated attackers to execute arbitrary code, gain administrative control over network management infrastructure, or trigger server-side resource exhaustion. Administrators are strongly encouraged to apply official vendor updates.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Cisco Secure FMC - RCE via upgradeReadinessCall - CVE:CVE-2026-20079 Log Block This is a new detection. Cloudflare Managed Ruleset N/A FortiClient EMS - Pre-Auth SQL Injection - CVE:CVE-2026-21643 Log Block This is a new detection. Cloudflare Managed Ruleset N/A Mesop - Remote Code Execution - Base64 Payload - CVE:CVE-2026-33057 Log Block This is a new detection. Cloudflare Managed Ruleset N/A React Server - DOS - CVE:CVE-2026-23864 - 1 - Beta Log Block This rule has been merged into the original rule "React Server - DOS - CVE:CVE-2026-23864 - 1" (ID: Cloudflare Managed Ruleset N/A XSS, HTML Injection - Link Tag - URI (beta) N/A Disabled This is a new detection. Cloudflare Managed Ruleset N/A XSS, HTML Injection - Embed Tag - URI (beta) N/A Disabled This is a new detection. -
The decode script injected by Email Address Obfuscation now loads with the
deferattribute. This means the script no longer blocks page rendering. It downloads in parallel with HTML parsing and executes after the document is fully parsed, before theDOMContentLoadedevent.This improves page loading performance, contributing to better Core Web Vitals, for all zones with Email Address Obfuscation on. No action is required.
If you have custom JavaScript that depends on email addresses being decoded at a specific point during page load, note that the decode script now executes after HTML parsing completes rather than inline during parsing.
You can now automate your threat monitoring by setting up custom alerts in your saved views. Instead of manually checking the dashboard for updates, you can subscribe to notifications that trigger whenever new data matches your specific filter sets, like new activity associated to a particular threat actor or spikes in activity within your industry.
By linking your saved views to the Cloudflare Notifications Center, you can ensure the right information reaches your team at the right time.
-
Immediate Alerts: receive real-time notifications the moment a critical event is detected that matches your saved criteria. This is essential for high-priority monitoring, such as tracking active campaigns from specific APT groups.
-
Daily Digests: opt for a summarized report delivered once a day. This is ideal for maintaining situational awareness of broader trends, like regional activity shifts or industry-wide threat landscapes, without cluttering your inbox.
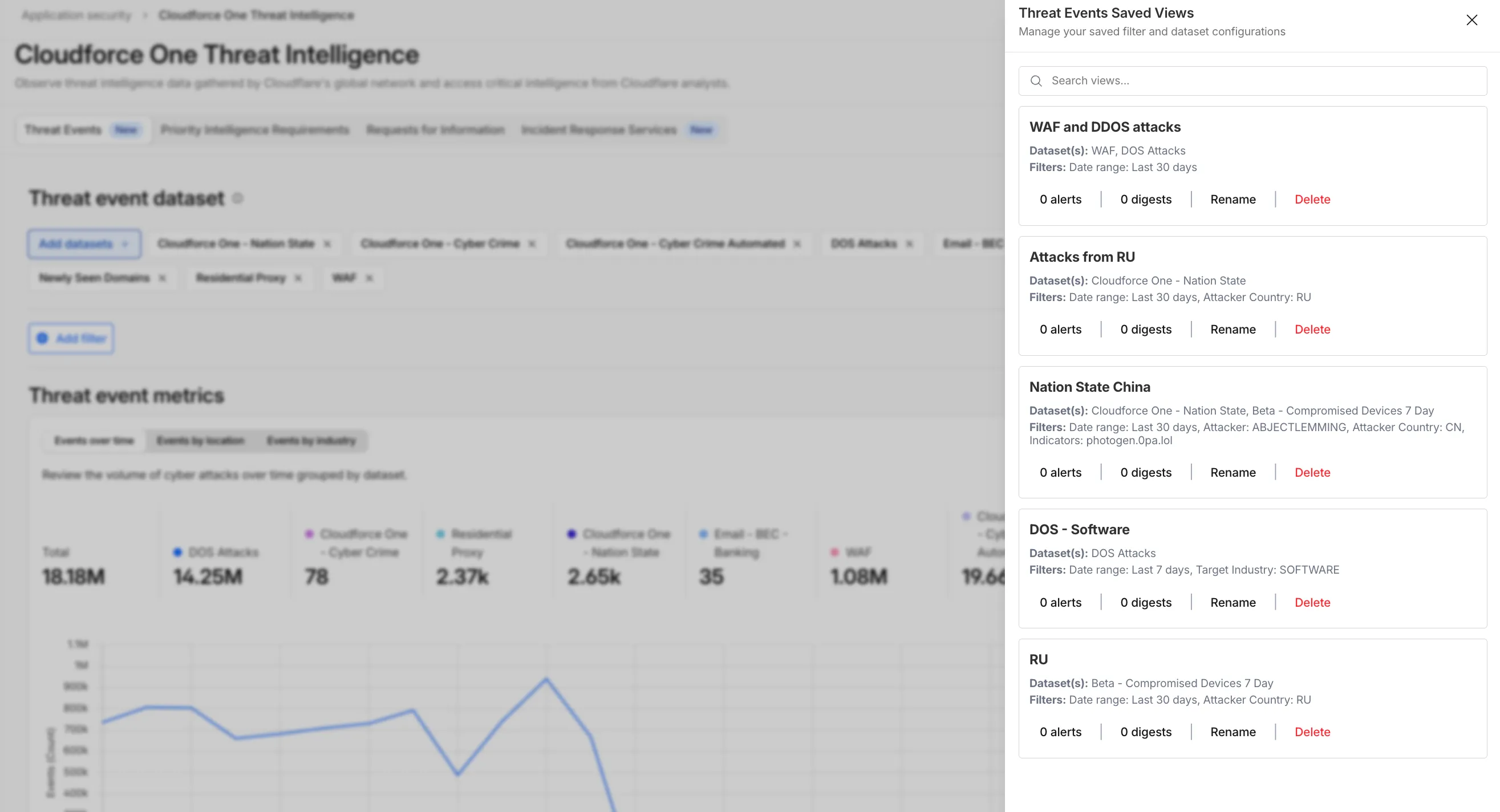
To set up an alert, go to Application Security > Threat Intelligence > Threat Events. From there:
- Choose your datasets and apply your desired filters and select Save View (or select an existing one).
- Open the Manage Saved Views menu.
- Select Add Alert next to your chosen view to configure your notification preferences in the Cloudflare dashboard.
For more technical details on configuring notifications, refer to the Threat Events documentation.
-
You can now manage mutual TLS (mTLS) and Bring Your Own Certificate Authority (BYO CA) configurations directly from the Cloudflare dashboard — no API required.
Previously, these advanced workflows required the Cloudflare API. The following are now available in the dashboard:
- AOP certificate management — Upload and manage your own certificate authorities for Authenticated Origin Pulls (AOP) directly from the dashboard.
- BYO Client mTLS certificate management — Upload and manage your own CA certificates for client mTLS enforcement without needing API access.
- CDN hostname to client mTLS certificate mapping — Associate client mTLS certificates with specific hostnames directly from the dashboard.
This week's release introduces new detections for a critical Remote Code Execution (RCE) vulnerability in MCP Server (CVE-2026-23744), alongside targeted protection for an authentication bypass vulnerability in SolarWinds products (CVE-2025-40552). Additionally, this release includes a new generic detection rule designed to identify and block Cross-Site Scripting (XSS) injection attempts leveraging "OnEvent" handlers within HTTP cookies.
Key Findings
-
MCP Server (CVE-2026-23744): A vulnerability in the Model Context Protocol (MCP) server implementation where malformed input payloads can trigger a memory corruption state, allowing for arbitrary code execution.
-
SolarWinds (CVE-2025-40552): A critical flaw in the authentication module allows unauthenticated attackers to bypass security filters and gain unauthorized access to the management console due to improper identity token validation.
-
XSS OnEvents Cookies: This generic rule identifies malicious event handlers (such as onload or onerror) embedded within HTTP cookie values.
Impact
Successful exploitation of the MCP Server and SolarWinds vulnerabilities could allow unauthenticated attackers to execute arbitrary code or gain administrative control, leading to a full system takeover. Additionally, the new generic XSS detection prevents attackers from leveraging browser event handlers in cookies to hijack user sessions or execute malicious scripts.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Generic Rules - Command Execution - 5 - Body Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A Generic Rules - Command Execution - 5 - Header Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A Generic Rules - Command Execution - 5 - URI Log Block This is a new detection. Cloudflare Managed Ruleset N/A MCP Server - Remote Code Execution - CVE:CVE-2026-23744 Log Block This is a new detection. Cloudflare Managed Ruleset N/A XSS - OnEvents - Cookies Log Block This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Evasion - Body Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Evasion - Headers Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - Evasion - URI Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - LIKE 3 - Body Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - LIKE 3 - URI Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - UNION - 2 - Body Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A SQLi - UNION - 2 - URI Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A SolarWinds - Auth Bypass - CVE:CVE-2025-40552 Log Block This is a new detection. -
Two new fields are now available in rule expressions that surface Layer 4 transport telemetry from the client connection. Together with the existing
cf.timings.client_tcp_rtt_msecfield, these fields give you a complete picture of connection quality for both TCP and QUIC traffic — enabling transport-aware rules without requiring any client-side changes.Previously, QUIC RTT and delivery rate data was only available via the
Server-Timing: cfL4response header. These new fields make the same data available directly in rule expressions, so you can use them in Transform Rules, WAF Custom Rules, and other phases that support dynamic fields.Field Type Description cf.timings.client_quic_rtt_msecInteger The smoothed QUIC round-trip time (RTT) between Cloudflare and the client in milliseconds. Only populated for QUIC (HTTP/3) connections. Returns 0for TCP connections.cf.edge.l4.delivery_rateInteger The most recent data delivery rate estimate for the client connection, in bytes per second. Returns 0when L4 statistics are not available for the request.Use a request header transform rule to tag requests from high-latency connections, so your origin can serve a lighter page variant:
Rule expression:
cf.timings.client_tcp_rtt_msec > 200 or cf.timings.client_quic_rtt_msec > 200Header modifications:
Operation Header name Value Set X-High-Latencytruecf.edge.l4.delivery_rate > 0 and cf.edge.l4.delivery_rate < 100000For more information, refer to Request Header Transform Rules and the fields reference.
This week's release introduces new detections for a critical authentication bypass vulnerability in Fortinet products (CVE-2025-59718), alongside three new generic detection rules designed to identify and block HTTP Parameter Pollution attempts. Additionally, this release includes targeted protection for a high-impact unrestricted file upload vulnerability in Magento and Adobe Commerce.
Key Findings
-
CVE-2025-59718: An improper cryptographic signature verification vulnerability in Fortinet FortiOS, FortiProxy, and FortiSwitchManager. This may allow an unauthenticated attacker to bypass the FortiCloud SSO login authentication using a maliciously crafted SAML message, if that feature is enabled on the device.
-
Magento 2 - Unrestricted File Upload: A critical flaw in Magento and Adobe Commerce allows unauthenticated attackers to bypass security checks and upload malicious files to the server, potentially leading to Remote Code Execution (RCE).
Impact
Successful exploitation of the Fortinet and Magento vulnerabilities could allow unauthenticated attackers to gain administrative control or deploy webshells, leading to complete server compromise and data theft.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Generic Rules - Parameter Pollution - Body Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A Generic Rules - Parameter Pollution - Header - Form Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A Generic Rules - Parameter Pollution - URI Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A Magento 2 - Unrestricted file upload Log Block This is a new detection. Cloudflare Managed Ruleset N/A Fortinet FortiCloud SSO - Authentication Bypass - CVE:CVE-2025-59718 Log Block This is a new detection. -
Cloudflare now exposes four new fields in the Transform Rules phase that encode client certificate data in RFC 9440 ↗ format. Previously, forwarding client certificate information to your origin required custom parsing of PEM-encoded fields or non-standard HTTP header formats. These new fields produce output in the standardized
Client-CertandClient-Cert-Chainheader format defined by RFC 9440, so your origin can consume them directly without any additional decoding logic.Each certificate is DER-encoded, Base64-encoded, and wrapped in colons. For example,
:MIIDsT...Vw==:. A chain of intermediates is expressed as a comma-separated list of such values.Field Type Description cf.tls_client_auth.cert_rfc9440String The client leaf certificate in RFC 9440 format. Empty if no client certificate was presented. cf.tls_client_auth.cert_rfc9440_too_largeBoolean trueif the leaf certificate exceeded 10 KB and was omitted. In practice this will almost always befalse.cf.tls_client_auth.cert_chain_rfc9440String The intermediate certificate chain in RFC 9440 format as a comma-separated list. Empty if no intermediate certificates were sent or if the chain exceeded 16 KB. cf.tls_client_auth.cert_chain_rfc9440_too_largeBoolean trueif the intermediate chain exceeded 16 KB and was omitted.The chain encoding follows the same ordering as the TLS handshake: the certificate closest to the leaf appears first, working up toward the trust anchor. The root certificate is not included.
Add a request header transform rule to set the
Client-CertandClient-Cert-Chainheaders on requests forwarded to your origin server. For example, to forward headers for verified, non-revoked certificates:Rule expression:
cf.tls_client_auth.cert_verified and not cf.tls_client_auth.cert_revokedHeader modifications:
Operation Header name Value Set Client-Certcf.tls_client_auth.cert_rfc9440Set Client-Cert-Chaincf.tls_client_auth.cert_chain_rfc9440To get the most out of these fields, upload your client CA certificate to Cloudflare so that Cloudflare validates the client certificate at the edge and populates
cf.tls_client_auth.cert_verifiedandcf.tls_client_auth.cert_revoked.For more information, refer to Mutual TLS authentication, Request Header Transform Rules, and the fields reference.
Two new fields are now available in the
httpRequestsAdaptiveandhttpRequestsAdaptiveGroupsGraphQL Analytics API datasets:webAssetsOperationId— the ID of the saved endpoint that matched the incoming request.webAssetsLabelsManaged— the managed labels mapped to the matched operation at the time of the request (for example,cf-llm,cf-log-in). At most 10 labels are returned per request.
Both fields are empty when no operation matched.
webAssetsLabelsManagedis also empty when no managed labels are assigned to the matched operation.These fields allow you to determine, per request, which Web Assets operation was matched and which managed labels were active. This is useful for troubleshooting downstream security detection verdicts — for example, understanding why AI Security for Apps did or did not flag a request.
Refer to Endpoint labeling service for GraphQL query examples.
This week's release focuses on new improvements to enhance coverage.
Key Findings
- Existing rule enhancements have been deployed to improve detection resilience against broad classes of web attacks and strengthen behavioral coverage.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Command Injection - Generic 9 - URI Vector Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A Command Injection - Generic 9 - Header Vector Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A Command Injection - Generic 9 - Body Vector Log Disabled This is a new detection. Cloudflare Managed Ruleset N/A PHP, vBulletin, jQuery File Upload - Code Injection, Dangerous File Upload - CVE:CVE-2018-9206, CVE:CVE-2019-17132 (beta) Log Block This rule has been merged into the original rule "PHP, vBulletin, jQuery File Upload - Code Injection, Dangerous File Upload - CVE:CVE-2018-9206, CVE:CVE-2019-17132" (ID:
In the Cloudflare One dashboard, the overview page for a specific Cloudflare Tunnel now shows all replicas of that tunnel and supports streaming logs from multiple replicas at once.
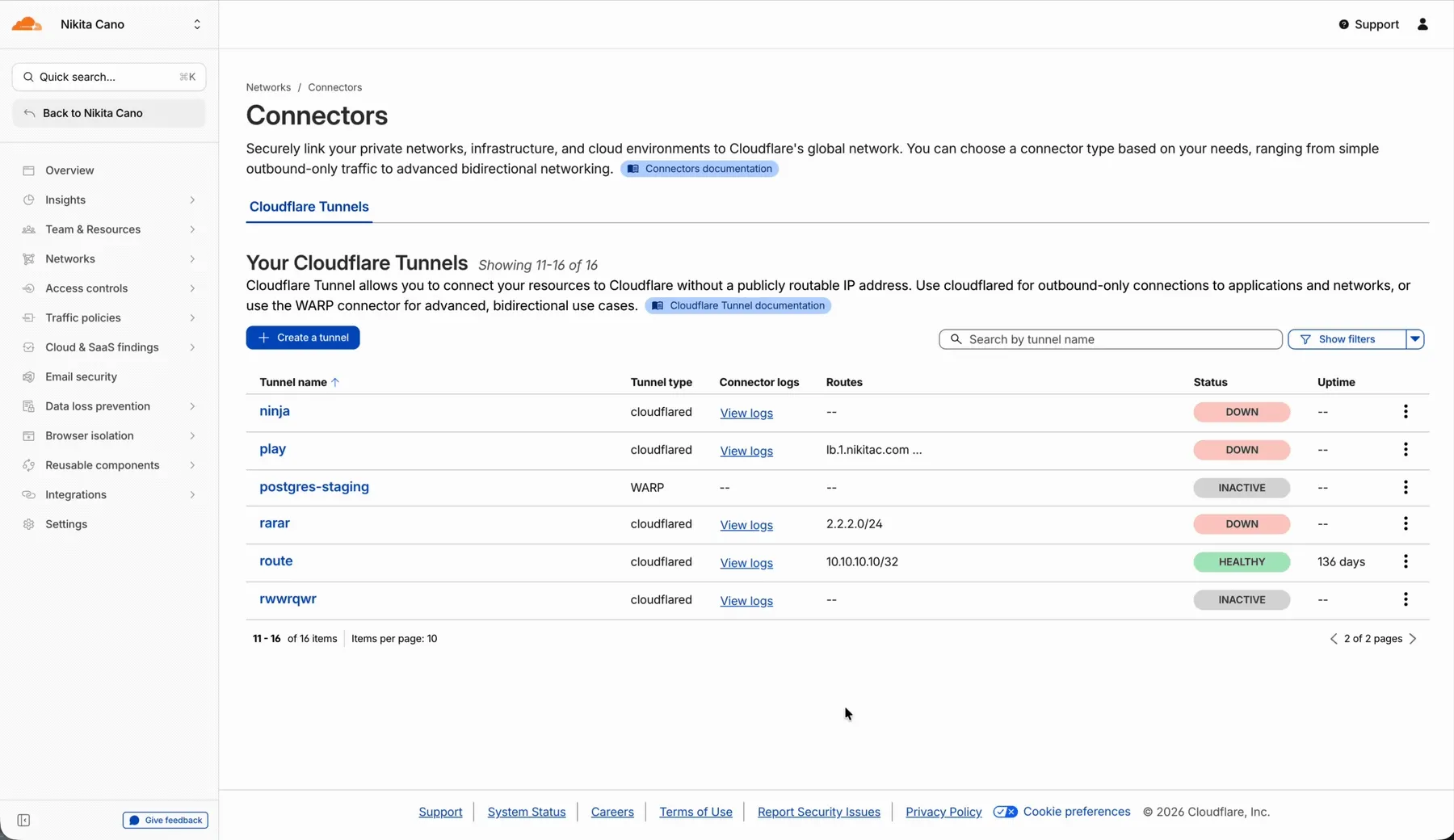
Previously, you could only stream logs from one replica at a time. With this update:
- Replicas on the tunnel overview — All active replicas for the selected tunnel now appear on that tunnel's overview page under Connectors. Select any replica to stream its logs.
- Multi-connector log streaming — Stream logs from multiple replicas simultaneously, making it easier to correlate events across your infrastructure during debugging or incident response. To try it out, log in to Cloudflare One ↗ and go to Networks > Connectors > Cloudflare Tunnels. Select View logs next to the tunnel you want to monitor.
For more information, refer to Tunnel log streams and Deploy replicas.