Changelog
New updates and improvements at Cloudflare.
This emergency release introduces rules for CVE-2025-55183 and CVE-2025-55184, targeting server-side function exposure and resource-exhaustion patterns, respectively.
Key Findings
Added coverage for Leaking Server Functions (CVE-2025-55183) and React Function DoS detection (CVE-2025-55184).
Impact
These updates strengthen protection for server-function abuse techniques (CVE-2025-55183, CVE-2025-55184) that may expose internal logic or disrupt application availability.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A React - Leaking Server Functions - CVE:CVE-2025-55183 N/A Block This was labeled as Generic - Server Function Source Code Exposure. Cloudflare Free Ruleset N/A React - Leaking Server Functions - CVE:CVE-2025-55183 N/A Block This was labeled as Generic - Server Function Source Code Exposure. Cloudflare Managed Ruleset N/A React - DoS - CVE:CVE-2025-55184 N/A Disabled This was labeled as Generic – Server Function Resource Exhaustion.
This additional week's emergency release introduces improvements to our existing rule for React – Remote Code Execution – CVE-2025-55182 - 2, along with two new generic detections covering server-side function exposure and resource-exhaustion patterns.
Key Findings
Enhanced detection logic for React – RCE – CVE-2025-55182, added Generic – Server Function Source Code Exposure, and added Generic – Server Function Resource Exhaustion.
Impact
These updates strengthen protection against React RCE exploitation attempts and broaden coverage for common server-function abuse techniques that may expose internal logic or disrupt application availability.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A React - Remote Code Execution - CVE:CVE-2025-55182 - 2 N/A Block This is an improved detection. Cloudflare Free Ruleset N/A React - Remote Code Execution - CVE:CVE-2025-55182 - 2 N/A Block This is an improved detection. Cloudflare Managed Ruleset N/A Generic - Server Function Source Code Exposure N/A Block This is a new detection. Cloudflare Free Ruleset N/A Generic - Server Function Source Code Exposure N/A Block This is a new detection. Cloudflare Managed Ruleset N/A Generic - Server Function Resource Exhaustion N/A Disabled This is a new detection.
Cloudflare WAF now inspects request-payload size of up to 1 MB across all plans to enhance our detection capabilities for React RCE (CVE-2025-55182).
Key Findings
React payloads commonly have a default maximum size of 1 MB. Cloudflare WAF previously inspected up to 128 KB on Enterprise plans, with even lower limits on other plans.
Update: We later reinstated the maximum request-payload size the Cloudflare WAF inspects. Refer to Updating the WAF maximum payload values for details.
We are reinstating the maximum request-payload size the Cloudflare WAF inspects, with WAF on Enterprise zones inspecting up to 128 KB.
Key Findings
On December 5, 2025, we initially attempted to increase the maximum WAF payload limit to 1 MB across all plans. However, an automatic rollout for all customers proved impractical because the increase led to a surge in false positives for existing managed rules.
This issue was particularly notable within the Cloudflare Managed Ruleset and the Cloudflare OWASP Core Ruleset, impacting customer traffic.
Impact
Customers on paid plans can increase the limit to 1 MB for any of their zones by contacting Cloudflare Support. Free zones are already protected up to 1 MB and do not require any action.
The WAF rule deployed yesterday to block unsafe deserialization-based RCE has been updated. The rule description now reads “React – RCE – CVE-2025-55182”, explicitly mapping to the recently disclosed React Server Components vulnerability. Detection logic remains unchanged.
Key Findings
Rule description updated to reference React – RCE – CVE-2025-55182 while retaining existing unsafe-deserialization detection.
Impact
Improved classification and traceability with no change to coverage against remote code execution attempts.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A React - RCE - CVE:CVE-2025-55182 N/A Block Rule metadata description changed. Detection unchanged. Cloudflare Free Ruleset N/A React - RCE - CVE:CVE-2025-55182 N/A Block Rule metadata description changed. Detection unchanged.
This week's emergency release introduces a new rule to block a critical RCE vulnerability in widely-used web frameworks through unsafe deserialization patterns.
Key Findings
New WAF rule deployed for RCE Generic Framework to block malicious POST requests containing unsafe deserialization patterns. If successfully exploited, this vulnerability allows attackers with network access via HTTP to execute arbitrary code remotely.
Impact
- Successful exploitation allows unauthenticated attackers to execute arbitrary code remotely through crafted serialization payloads, enabling complete system compromise, data exfiltration, and potential lateral movement within affected environments.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A RCE Generic - Framework N/A Block This is a new detection. Cloudflare Free Ruleset N/A RCE Generic - Framework N/A Block This is a new detection.
This week’s release introduces new detections for remote code execution attempts targeting Monsta FTP (CVE-2025-34299), alongside improvements to an existing XSS detection to enhance coverage.
Key Findings
- CVE-2025-34299 is a critical remote code execution flaw in Monsta FTP, arising from improper handling of user-supplied parameters within the file-handling interface. Certain builds allow crafted requests to bypass sanitization and reach backend PHP functions that execute arbitrary commands. Attackers can send manipulated parameters through the web panel to trigger command execution within the application’s runtime environment.
Impact
If exploited, the vulnerability enables full remote command execution on the underlying server, allowing takeover of the hosting environment, unauthorized file access, and potential lateral movement. As the flaw can be triggered without authentication on exposed Monsta FTP instances, it represents a severe risk for publicly reachable deployments.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Monsta FTP - Remote Code Execution - CVE:CVE-2025-34299 Log Block This is a new detection Cloudflare Managed Ruleset N/A XSS - JS Context Escape - Beta Log Block This rule is merged into the original rule "XSS - JS Context Escape" (ID:
This week highlights enhancements to detection signatures improving coverage for vulnerabilities in FortiWeb, linked to CVE-2025-64446, alongside new detection logic expanding protection against PHP Wrapper Injection techniques.
Key Findings
This vulnerability enables an unauthenticated attacker to bypass access controls by abusing the
CGIINFOheader. The latest update strengthens detection logic to ensure a reliable identification of crafted requests attempting to exploit this flaw.Impact
- FortiWeb (CVE-2025-64446): Exploitation allows a remote unauthenticated adversary to circumvent authentication mechanisms by sending a manipulated
CGIINFOheader to FortiWeb’s backend CGI handler. Successful exploitation grants unintended access to restricted administrative functionality, potentially enabling configuration tampering or system-level actions.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A FortiWeb - Authentication Bypass via CGIINFO Header - CVE:CVE-2025-64446 Log Block This is a new detection Cloudflare Managed Ruleset N/A PHP Wrapper Injection - Body - Beta Log Disabled This rule has been merged into the original rule "PHP Wrapper Injection - Body" (ID: Cloudflare Managed Ruleset N/A PHP Wrapper Injection - URI - Beta Log Disabled This rule has been merged into the original rule "PHP Wrapper Injection - URI" (ID: - FortiWeb (CVE-2025-64446): Exploitation allows a remote unauthenticated adversary to circumvent authentication mechanisms by sending a manipulated
The threat events platform now has threat insights available for some relevant parent events. Threat intelligence analyst users can access these insights for their threat hunting activity. Insights are also highlighted in the Cloudflare dashboard by a small
lightning iconand the insights can refer to multiple, connected events, potentially part of the same attack or campaign and associated with the same threat actor.For more information, refer to Analyze threat events.
This week’s release introduces a critical detection for CVE-2025-61757, a vulnerability in the Oracle Identity Manager REST WebServices component.
Key Findings
This flaw allows unauthenticated attackers with network access over HTTP to fully compromise the Identity Manager, potentially leading to a complete takeover.
Impact
Oracle Identity Manager (CVE-2025-61757): Exploitation could allow an unauthenticated remote attacker to bypass security checks by sending specially crafted requests to the application's message processor. This enables the creation of arbitrary employee accounts, which can be leveraged to modify system configurations and achieve full system compromise.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Oracle Identity Manager - Pre-Auth RCE - CVE:CVE-2025-61757 N/A Block This is a new detection.
This week highlights enhancements to detection signatures improving coverage for vulnerabilities in DELMIA Apriso, linked to CVE-2025-6205.
Key Findings
This vulnerability allows unauthenticated attackers to gain privileged access to the application. The latest update provides enhanced detection logic for resilient protection against exploitation attempts.
Impact
- DELMIA Apriso (CVE-2025-6205): Exploitation could allow an unauthenticated remote attacker to bypass security checks by sending specially crafted requests to the application's message processor. This enables the creation of arbitrary employee accounts, which can be leveraged to modify system configurations and achieve full system compromise.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A DELMIA Apriso - Auth Bypass - CVE:CVE-2025-6205 Log Block This is a new detection. Cloudflare Managed Ruleset N/A PHP Wrapper Injection - Body N/A Disabled Rule metadata description refined. Detection unchanged. Cloudflare Managed Ruleset N/A PHP Wrapper Injection - URI N/A Disabled Rule metadata description refined. Detection unchanged.
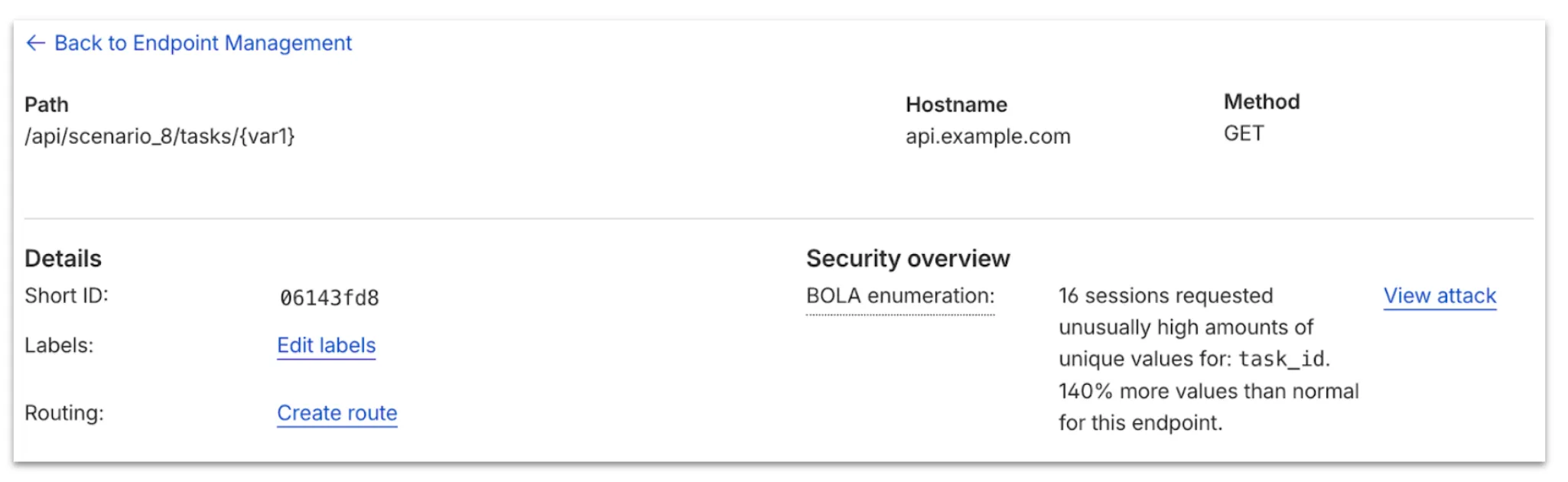
Now, API Shield automatically searches for and highlights Broken Object Level Authorization (BOLA) attacks on managed API endpoints. API Shield will highlight both BOLA enumeration attacks and BOLA pollution attacks, telling you what was attacked, by who, and for how long.
You can find these attacks three different ways: Security Overview, Endpoint details, or Security Analytics. If these attacks are not found on your managed API endpoints, there will not be an overview card or security analytics suspicious activity card.

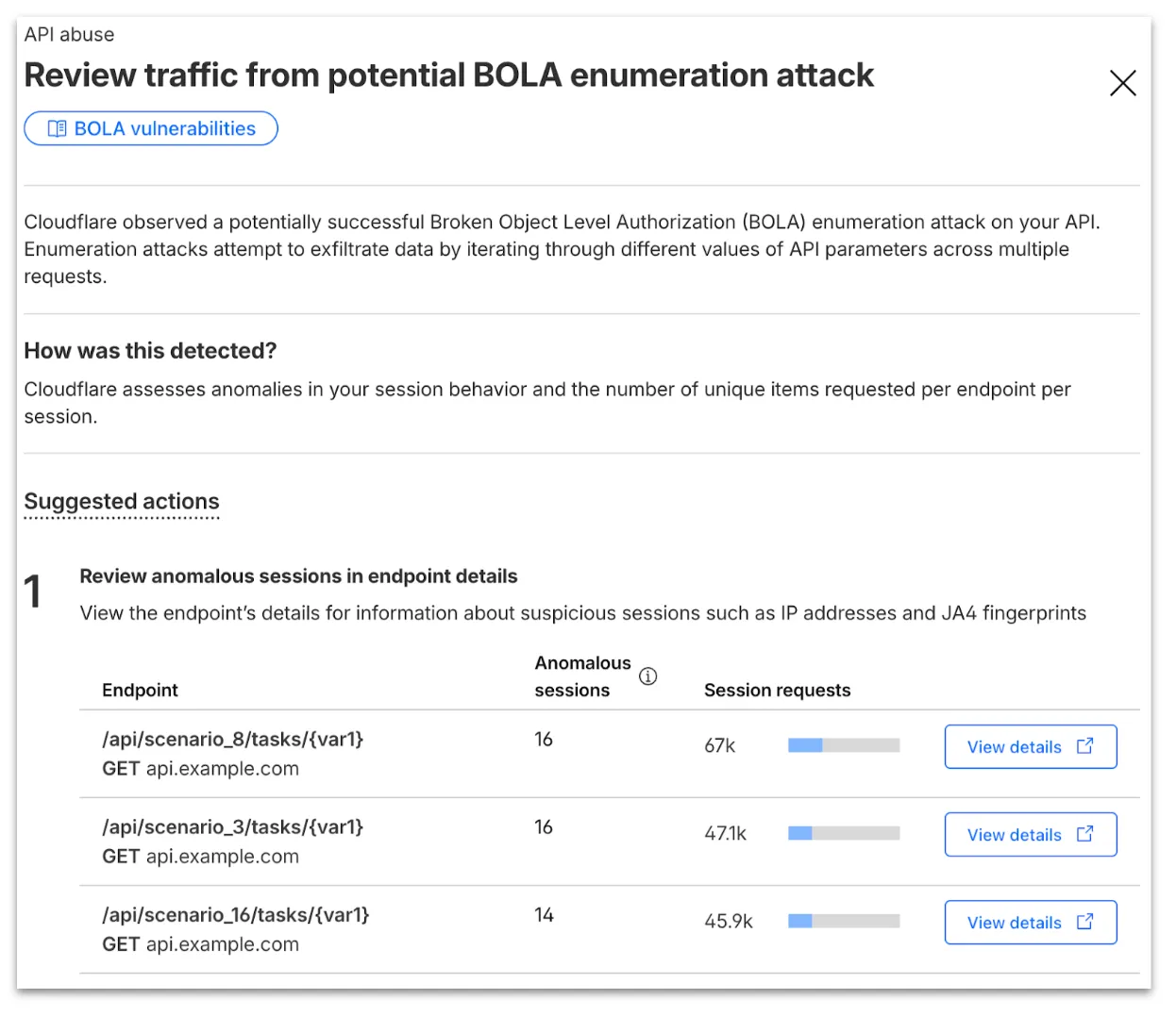
From the endpoint details, you can select View attack to find details about the BOLA attacker’s sessions.
From here, select View in Analytics to observe attacker traffic over time for the last seven days.
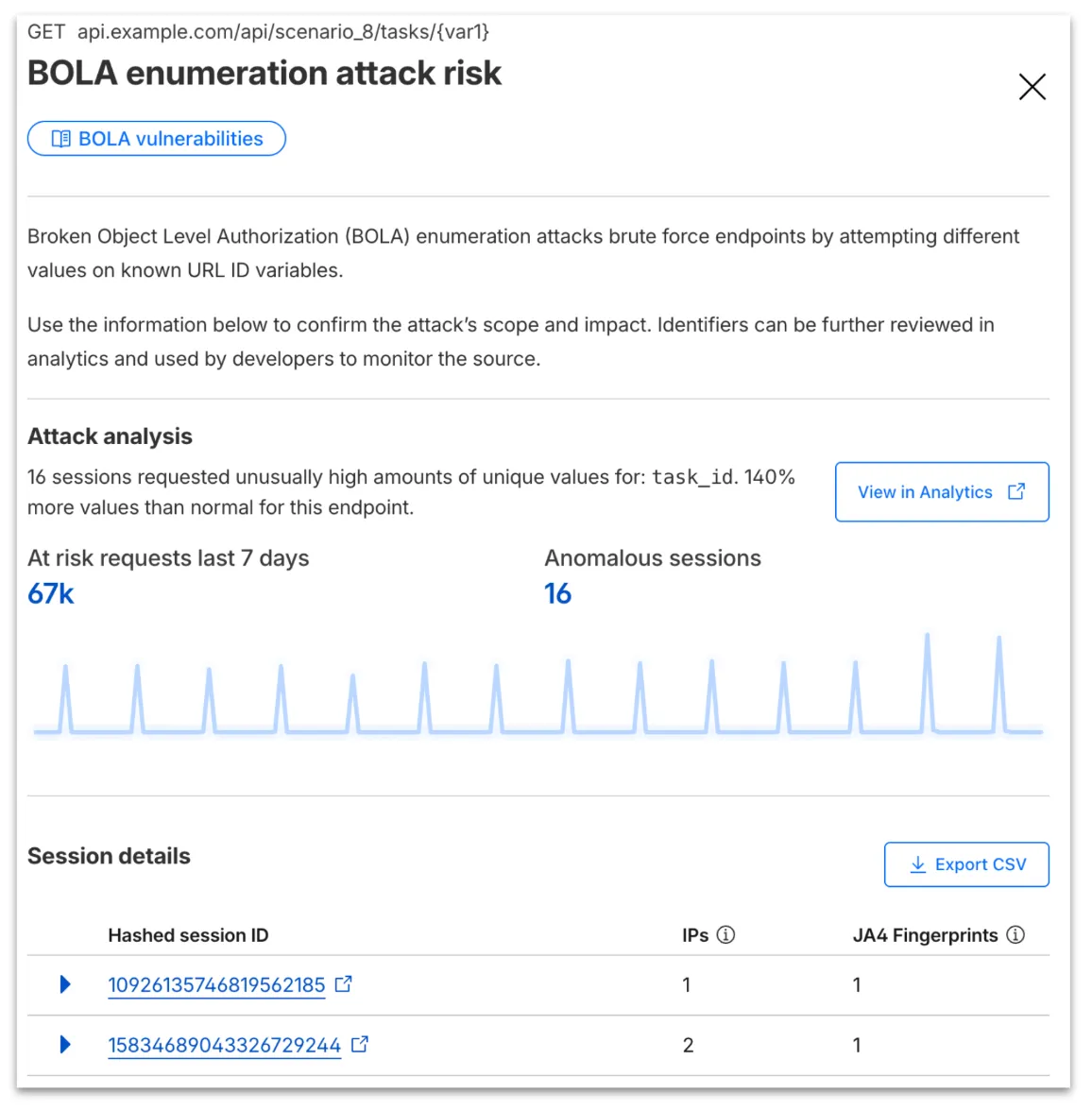
Your search will filter to traffic on that endpoint in the last seven days, along with the malicious session IDs found in the attack. Session IDs are hashed for privacy and will not be found in your origin logs. Refer to IP and JA4 fingerprint to cross-reference behavior at the origin.
At any time, you can also start your investigation into attack traffic from Security Analytics by selecting the suspicious activity card.

We urge you to take all of this client information to your developer team to research the attacker behavior and ensure any broken authorization policies in your API are fixed at the source in your application, preventing further abuse.
In addition, this release marks the end of the beta period for these scans. All Enterprise customers with API Shield subscriptions will see these new attacks if found on their zone.
Starting February 2, 2026, the
cloudflared proxy-dnscommand will be removed from all newcloudflaredreleases.This change is being made to enhance security and address a potential vulnerability in an underlying DNS library. This vulnerability is specific to the
proxy-dnscommand and does not affect any othercloudflaredfeatures, such as the core Cloudflare Tunnel service.The
proxy-dnscommand, which runs a client-side DNS-over-HTTPS (DoH) proxy, has been an officially undocumented feature for several years. This functionality is fully and securely supported by our actively developed products.Versions of
cloudflaredreleased before this date will not be affected and will continue to operate. However, note that our official support policy for anycloudflaredrelease is one year from its release date.We strongly advise users of this undocumented feature to migrate to one of the following officially supported solutions before February 2, 2026, to continue benefiting from secure DNS-over-HTTPS.
The preferred method for enabling DNS-over-HTTPS on user devices is the Cloudflare WARP client. The WARP client automatically secures and proxies all DNS traffic from your device, integrating it with your organization's Zero Trust policies and posture checks.
For scenarios where installing a client on every device is not possible (such as servers, routers, or IoT devices), we recommend using the WARP Connector.
Instead of running
cloudflared proxy-dnson a machine, you can install the WARP Connector on a single Linux host within your private network. This connector will act as a gateway, securely routing all DNS and network traffic from your entire subnet to Cloudflare for filtering and logging.
This week’s release introduces new detections for Prototype Pollution across three common vectors: URI, Body, and Header/Form.
Key Findings
- These attacks can affect both API and web applications by altering normal behavior or bypassing security controls.
Impact
Exploitation may allow attackers to change internal logic or cause unexpected behavior in applications using JavaScript or Node.js frameworks. Developers should sanitize input keys and avoid merging untrusted data structures.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Generic Rules - Prototype Pollution - URI Log Disabled This is a new detection Cloudflare Managed Ruleset N/A Generic Rules - Prototype Pollution - Body Log Disabled This is a new detection Cloudflare Managed Ruleset N/A Generic Rules - Prototype Pollution - Header - Form Log Disabled This is a new detection
This week’s emergency release introduces a new detection signature that enhances coverage for a critical vulnerability in the React Native Metro Development Server, tracked as CVE-2025-11953.
Key Findings
The Metro Development Server exposes an HTTP endpoint that is vulnerable to OS command injection (CWE-78). An unauthenticated network attacker can send a crafted request to this endpoint and execute arbitrary commands on the host running Metro. The vulnerability affects Metro/cli-server-api builds used by React Native Community CLI in pre-patch development releases.
Impact
Successful exploitation of CVE-2025-11953 may result in remote command execution on developer workstations or CI/build agents, leading to credential and secret exposure, source tampering, and potential lateral movement into internal networks. Administrators and developers are strongly advised to apply the vendor's patches and restrict Metro’s network exposure to reduce this risk.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A React Native Metro - Command Injection - CVE:CVE-2025-11953 N/A Block This is a New Detection
This week highlights enhancements to detection signatures improving coverage for vulnerabilities in Adobe Commerce and Magento Open Source, linked to CVE-2025-54236.
Key Findings
This vulnerability allows unauthenticated attackers to take over customer accounts through the Commerce REST API and, in certain configurations, may lead to remote code execution. The latest update provides enhanced detection logic for resilient protection against exploitation attempts.
Impact
- Adobe Commerce (CVE-2025-54236): Exploitation may allow attackers to hijack sessions, execute arbitrary commands, steal data, and disrupt storefronts, resulting in confidentiality and integrity risks for merchants. Administrators are strongly encouraged to apply vendor patches without delay.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100774C Adobe Commerce - Remote Code Execution - CVE:CVE-2025-54236 Log Block This is an improved detection.
The Brand Protection logo query dashboard now allows you to use the Report to Cloudflare button to submit an Abuse report directly from the Brand Protection logo queries dashboard. While you could previously report new domains that were impersonating your brand before, now you can do the same for websites found to be using your logo wihtout your permission. The abuse reports wiull be prefilled and you will only need to validate a few fields before you can click the submit button, after which our team process your request.
Ready to start? Check out the Brand Protection docs.
-
Cloudflare now provides two new request fields in the Ruleset engine that let you make decisions based on whether a request used TCP and the measured TCP round-trip time between the client and Cloudflare. These fields help you understand protocol usage across your traffic and build policies that respond to network performance. For example, you can distinguish TCP from QUIC traffic or route high latency requests to alternative origins when needed.
Field Type Description cf.edge.client_tcpBoolean Indicates whether the request used TCP. A value of true means the client connected using TCP instead of QUIC. cf.timings.client_tcp_rtt_msecNumber Reports the smoothed TCP round-trip time between the client and Cloudflare in milliseconds. For example, a value of 20 indicates roughly twenty milliseconds of RTT. Example filter expression:
cf.edge.client_tcp && cf.timings.client_tcp_rtt_msec < 100More information can be found in the Rules language fields reference.
This week’s release introduces a new detection signature that enhances coverage for a critical vulnerability in Oracle E-Business Suite, tracked as CVE-2025-61884.
Key Findings
The flaw is easily exploitable and allows an unauthenticated attacker with network access to compromise Oracle Configurator, which can grant access to sensitive resources and configuration data. The affected versions include 12.2.3 through 12.2.14.
Impact
Successful exploitation of CVE-2025-61884 may result in unauthorized access to critical business data or full exposure of information accessible through Oracle Configurator. Administrators are strongly advised to apply vendor's patches and recommended mitigations to reduce this exposure.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Oracle E-Business Suite - SSRF - CVE:CVE-2025-61884 N/A Block This is a New Detection
The Requests for Information (RFI) dashboard now shows users the number of tokens used by each submitted RFI to better understand usage of tokens and how they relate to each request submitted.
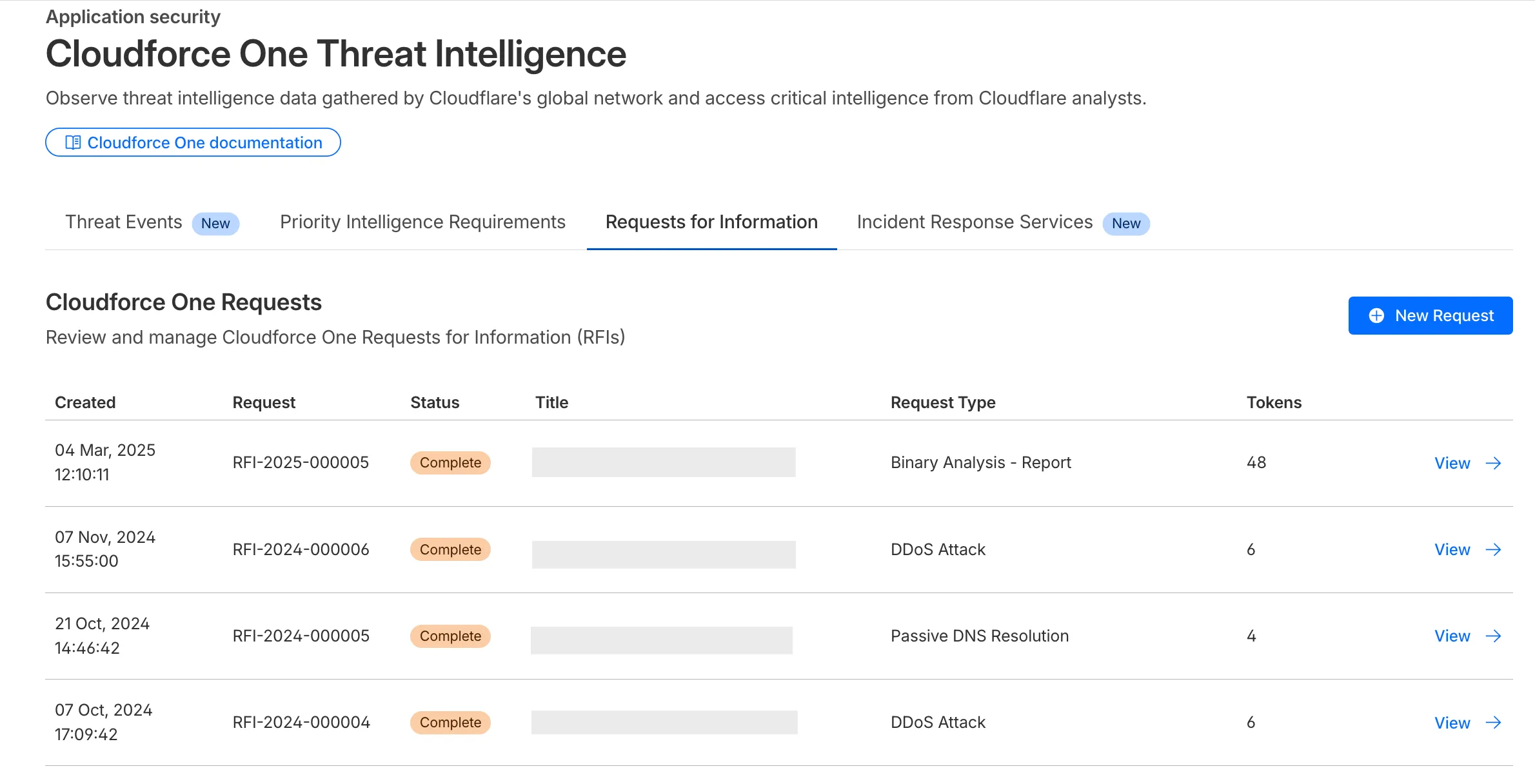
What’s new:
- Users can now see the number of tokens used for a submitted request for information.
- Users can see the remaining tokens allocated to their account for the quarter.
- Users can only select the Routine priority for the
Strategic Threat Researchrequest type.
Cloudforce One subscribers can try it now in Application Security > Threat Intelligence > Requests for Information ↗.
This week’s release introduces a new detection signature that enhances coverage for a critical vulnerability in Windows Server Update Services (WSUS), tracked as CVE-2025-59287.
Key Findings
The vulnerability allows unauthenticated attackers to potentially achieve remote code execution. The updated detection logic strengthens defenses by improving resilience against exploitation attempts targeting this flaw.
Impact
Successful exploitation of CVE-2025-59287 could enable attackers to hijack sessions, execute arbitrary commands, exfiltrate sensitive data, and disrupt storefront operations. These actions pose significant confidentiality and integrity risks to affected environments. Administrators should apply vendor patches immediately to mitigate exposure.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Windows Server - Deserialization - CVE:CVE-2025-59287 N/A Block This is a New Detection
This week highlights enhancements to detection signatures improving coverage for vulnerabilities in Adobe Commerce and Magento Open Source, linked to CVE-2025-54236.
Key Findings
This vulnerability allows unauthenticated attackers to take over customer accounts through the Commerce REST API and, in certain configurations, may lead to remote code execution. The latest update enhances detection logic to provide more resilient protection against exploitation attempts.
Impact
Adobe Commerce (CVE-2025-54236): Exploitation may allow attackers to hijack sessions, execute arbitrary commands, steal data, and disrupt storefronts, resulting in confidentiality and integrity risks for merchants. Administrators are strongly encouraged to apply vendor patches without delay.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Adobe Commerce - Remote Code Execution - CVE:CVE-2025-54236 N/A Block This is a New Detection
This week’s update introduces an enhanced rule that expands detection coverage for a critical vulnerability in Oracle E-Business Suite. It also improves an existing rule to provide more reliable coverage in request processing.
Key Findings
New WAF rule deployed for Oracle E-Business Suite (CVE-2025-61882) to block unauthenticated attacker's network access via HTTP to compromise Oracle Concurrent Processing. If successfully exploited, this vulnerability may result in remote code execution.
Impact
- Successful exploitation of CVE-2025-61882 allows unauthenticated attackers to execute arbitrary code remotely by chaining multiple weaknesses, enabling lateral movement into internal services, data exfiltration, and large-scale extortionware deployment within Oracle E-Business Suite environments.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100598A Remote Code Execution - Common Bash Bypass - Beta Log Block This rule is merged into the original rule "Remote Code Execution - Common Bash Bypass" (ID: Cloudflare Managed Ruleset 100916A Oracle E-Business Suite - Remote Code Execution - CVE:CVE-2025-61882 - 2 Log Block This is a New Detection Cloudflare Managed Ruleset N/A HTTP Truncated N/A Disabled This is a New Detection
Cloudflare's new Application Security report, currently in Closed Beta, is now available in the dashboard.
Go to Security reportsThe reports are generated monthly and provide cyber security insights trends for all of the Enterprise zones in your Cloudflare account.
The reports also include an industry benchmark, comparing your cyber security landscape to peers in your industry.
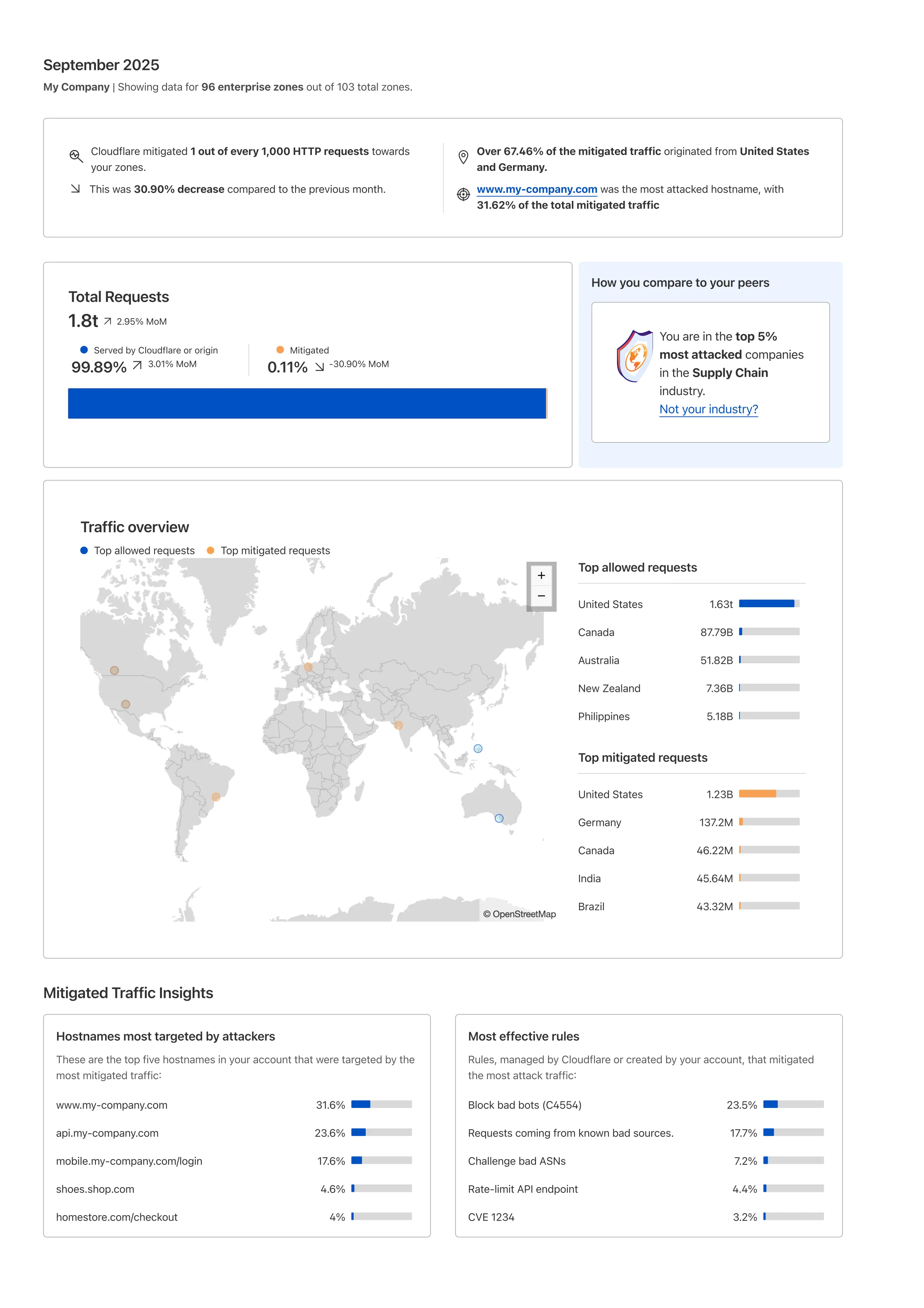
Learn more about the reports by referring to the Security Reports documentation.
Use the feedback survey link at the top of the page to help us improve the reports.
This week we introduced several new detections across Cloudflare Managed Rulesets, expanding coverage for high-impact vulnerability classes such as SSRF, SQLi, SSTI, Reverse Shell attempts, and Prototype Pollution. These rules aim to improve protection against attacker-controlled payloads that exploit misconfigurations or unvalidated input in web applications.
Key Findings
New detections added for multiple exploit categories:
SSRF (Server-Side Request Forgery) — new rules targeting both local and cloud metadata abuse patterns (Beta).
SQL Injection (SQLi) — rules for common patterns, sleep/time-based injections, and string/wait function exploitation across headers and URIs.
SSTI (Server-Side Template Injection) — arithmetic-based probe detections introduced across URI, header, and body fields.
Reverse Shell and XXE payloads — enhanced heuristics for command execution and XML external entity misuse.
Prototype Pollution — new Beta rule identifying common JSON payload structures used in object prototype poisoning.
PHP Wrapper Injection and HTTP Parameter Pollution detections — to catch path traversal and multi-parameter manipulation attempts.
Anomaly Header Checks — detecting CRLF injection attempts in header names.
Impact
These updates help detect multi-vector payloads that blend SSRF + RCE or SQLi + SSTI attacks, especially in cloud-hosted applications with exposed metadata endpoints or unsafe template rendering.
Prototype Pollution and HTTP parameter pollution rules address emerging JavaScript supply-chain exploitation patterns increasingly seen in real-world incidents.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset N/A Anomaly:Header - name - CR, LF N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - Reverse Shell - Body N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - Reverse Shell - Header N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - Reverse Shell - URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - XXE - Body N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - Common Patterns - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - Sleep Function - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - String Function - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Generic Rules - SQLi - WaitFor Function - Header URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Local - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Local - 2 - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Cloud - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSRF - Cloud - 2 - Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSTI - Arithmetic Probe - URI N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSTI - Arithmetic Probe - Header N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A SSTI - Arithmetic Probe - Body N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A PHP Wrapper Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A PHP Wrapper Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A HTTP parameter pollution N/A Disabled This is a New Detection Cloudflare Managed Ruleset N/A Prototype Pollution - Common Payloads - Beta N/A Disabled This is a New Detection