Changelog
New updates and improvements at Cloudflare.
This week’s highlights include a new JinJava rule targeting a sandbox-bypass flaw that could allow malicious template input to escape execution controls. The rule improves detection for unsafe template rendering paths.
Key Findings
New WAF rule deployed for JinJava (CVE-2025-59340) to block a sandbox bypass in the template engine that permits attacker-controlled type construction and arbitrary class instantiation; in vulnerable environments this can escalate to remote code execution and full server compromise.
Impact
- CVE-2025-59340 — Exploitation enables attacker-supplied type descriptors / Jackson
ObjectMapperabuse, allowing arbitrary class loading, file/URL access (LFI/SSRF primitives) and, with suitable gadget chains, potential remote code execution and system compromise.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100892 JinJava - SSTI - CVE:CVE-2025-59340 Log Block This is a New Detection - CVE-2025-59340 — Exploitation enables attacker-supplied type descriptors / Jackson
This week highlights multiple critical Cisco vulnerabilities (CVE-2025-20363, CVE-2025-20333, CVE-2025-20362). This flaw stems from improper input validation in HTTP(S) requests. An authenticated VPN user could send crafted requests to execute code as root, potentially compromising the device. The initial two rules were made available on September 28, with a third rule added today, October 7, for more robust protection.
- Cisco (CVE-2025-20333, CVE-2025-20362, CVE-2025-20363): Multiple vulnerabilities that could allow attackers to exploit unsafe deserialization and input validation flaws. Successful exploitation may result in arbitrary code execution, privilege escalation, or command injection on affected systems.
Impact
Cisco (CVE-2025-20333, CVE-2025-20362, CVE-2025-20363): Exploitation enables attackers to escalate privileges or achieve remote code execution via command injection. Administrators are strongly advised to apply vendor updates immediately.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100788B Cisco Secure Firewall Adaptive Security Appliance - Remote Code Execution - CVE:CVE-2025-20333, CVE:CVE-2025-20362, CVE:CVE-2025-20363 N/A Block This is a New Detection
This week’s highlights prioritise an emergency Oracle E-Business Suite RCE rule deployed to block active, high-impact exploitation. Also addressed are high-severity Chaos Mesh controller command-injection flaws that enable unauthenticated in-cluster RCE and potential cluster compromise, plus a form-data multipart boundary issue that permits HTTP Parameter Pollution (HPP). Two new generic SQLi detections were added to catch inline-comment obfuscation and information disclosure techniques.
Key Findings
-
New emergency rule released for Oracle E-Business Suite (CVE-2025-61882) addressing an actively exploited remote code execution vulnerability in core business application modules. Immediate mitigation deployed to protect enterprise workloads.
-
Chaos Mesh (CVE-2025-59358,CVE-2025-59359,CVE-2025-59360,CVE-2025-59361): A GraphQL debug endpoint on the Chaos Controller Manager is exposed without authentication; several controller mutations (
cleanTcs,killProcesses,cleanIptables) are vulnerable to OS command injection. -
Form-Data (CVE-2025-7783): Attackers who can observe
Math.random()outputs and control request fields in form-data may exploit this flaw to perform HTTP parameter pollution, leading to request tampering or data manipulation. -
Two new generic SQLi detections added to enhance baseline coverage against inline-comment obfuscation and information disclosure attempts.
Impact
-
CVE-2025-61882 — Oracle E-Business Suite remote code execution (emergency detection): attacker-controlled input can yield full system compromise, data exfiltration, and operational outage; immediate blocking enforced.
-
CVE-2025-59358 / CVE-2025-59359 / CVE-2025-59360 / CVE-2025-59361 — Unauthenticated command-injection in Chaos Mesh controllers allowing remote code execution, cluster compromise, and service disruption (high availability risk).
-
CVE-2025-7783 — Predictable multipart boundaries in form-data enabling HTTP Parameter Pollution; results include request tampering, parameter overwrite, and downstream data integrity loss.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100882 Chaos Mesh - Missing Authentication - CVE:CVE-2025-59358 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100883 Chaos Mesh - Command Injection - CVE:CVE-2025-59359 Log Block This is a New Detection Cloudflare Managed Ruleset 100884 Chaos Mesh - Command Injection - CVE:CVE-2025-59361 Log Block This is a New Detection Cloudflare Managed Ruleset 100886 Form-Data - Parameter Pollution - CVE:CVE-2025-7783 Log Block This is a New Detection Cloudflare Managed Ruleset 100888 Chaos Mesh - Command Injection - CVE:CVE-2025-59360 Log Block This is a New Detection Cloudflare Managed Ruleset 100916 Oracle E-Business Suite - Remote Code Execution - CVE:CVE-2025-61882 N/A Block This is a New Detection Cloudflare Managed Ruleset 100917 Generic Rules - SQLi - Inline Comment Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100918 Generic Rules - SQLi - Information Disclosure N/A Disabled This is a New Detection -
Managed Ruleset Updated
This update introduces 21 new detections in the Cloudflare Managed Ruleset (all currently set to Disabled mode to preserve remediation logic and allow quick activation if needed). The rules cover a broad spectrum of threats - SQL injection techniques, command and code injection, information disclosure of common files, URL anomalies, and cross-site scripting.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100902 Generic Rules - Command Execution - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100908 Generic Rules - Command Execution - 3 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100910 Generic Rules - Command Execution - 4 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100915 Generic Rules - Command Execution - 5 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100899 Generic Rules - Content-Type Abuse N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100914 Generic Rules - Content-Type Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100911 Generic Rules - Cookie Header Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100905 Generic Rules - NoSQL Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100913 Generic Rules - NoSQL Injection - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100907 Generic Rules - Parameter Pollution N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100906 Generic Rules - PHP Object Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100904 Generic Rules - Prototype Pollution N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100897 Generic Rules - Prototype Pollution 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100903 Generic Rules - Reverse Shell N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100909 Generic Rules - Reverse Shell - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100898 Generic Rules - SSJI NoSQL N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100896 Generic Rules - SSRF N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100895 Generic Rules - Template Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100895A Generic Rules - Template Injection - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100912 Generic Rules - XXE N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100900 Relative Paths - Anomaly Headers N/A Disabled This is a New Detection
This week highlights four important vendor- and component-specific issues: an authentication bypass in SimpleHelp (CVE-2024-57727), an information-disclosure flaw in Flowise Cloud (CVE-2025-58434), an SSRF in the WordPress plugin Ditty (CVE-2025-8085), and a directory-traversal bug in Vite (CVE-2025-30208). These are paired with improvements to our generic detection coverage (SQLi, SSRF) to raise the baseline and reduce noisy gaps.
Key Findings
-
SimpleHelp (CVE-2024-57727): Authentication bypass in SimpleHelp that can allow unauthorized access to management interfaces or sessions.
-
Flowise Cloud (CVE-2025-58434): Information-disclosure vulnerability in Flowise Cloud that may expose sensitive configuration or user data to unauthenticated or low-privileged actors.
-
WordPress:Plugin: Ditty (CVE-2025-8085): SSRF in the Ditty WordPress plugin enabling server-side requests that could reach internal services or cloud metadata endpoints.
-
Vite (CVE-2025-30208): Directory-traversal vulnerability in Vite allowing access to filesystem paths outside the intended web root.
Impact
These vulnerabilities allow attackers to gain access, escalate privileges, or execute actions that were previously unavailable:
-
SimpleHelp (CVE-2024-57727): An authentication bypass that can let unauthenticated attackers access management interfaces or hijack sessions — enabling lateral movement, credential theft, or privilege escalation within affected environments.
-
Flowise Cloud (CVE-2025-58434): Information-disclosure flaw that can expose sensitive configuration, tokens, or user data; leaked secrets may be chained into account takeover or privileged access to backend services.
-
WordPress:Plugin: Ditty (CVE-2025-8085): SSRF that enables server-side requests to internal services or cloud metadata endpoints, potentially allowing attackers to retrieve credentials or reach otherwise inaccessible infrastructure, leading to privilege escalation or cloud resource compromise.
-
Vite (CVE-2025-30208): Directory-traversal vulnerability that can expose filesystem contents outside the web root (configuration files, keys, source code), which attackers can use to escalate privileges or further compromise systems.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100717 SimpleHelp - Auth Bypass - CVE:CVE-2024-57727 Log Block This rule is merged to 100717 in legacy WAF and Cloudflare Managed Ruleset 100775 Flowise Cloud - Information Disclosure - CVE:CVE-2025-58434 Log Block This is a New Detection Cloudflare Managed Ruleset 100881 WordPress:Plugin:Ditty - SSRF - CVE:CVE-2025-8085 Log Block This is a New Detection Cloudflare Managed Ruleset 100887 Vite - Directory Traversal - CVE:CVE-2025-30208 Log Block This is a New Detection -
This week highlights multiple critical Cisco vulnerabilities (CVE-2025-20363, CVE-2025-20333, CVE-2025-20362). This flaw stems from improper input validation in HTTP(S) requests. An authenticated VPN user could send crafted requests to execute code as root, potentially compromising the device.
Key Findings
- Cisco (CVE-2025-20333, CVE-2025-20362, CVE-2025-20363): Multiple vulnerabilities that could allow attackers to exploit unsafe deserialization and input validation flaws. Successful exploitation may result in arbitrary code execution, privilege escalation, or command injection on affected systems.
Impact
Cisco (CVE-2025-20333, CVE-2025-20362, CVE-2025-20363): Exploitation enables attackers to escalate privileges or achieve remote code execution via command injection.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100788 Cisco Secure Firewall Adaptive Security Appliance - Remote Code Execution - CVE:CVE-2025-20333, CVE:CVE-2025-20362, CVE:CVE-2025-20363 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100788A Cisco Secure Firewall Adaptive Security Appliance - Remote Code Execution - CVE:CVE-2025-20333, CVE:CVE-2025-20362, CVE:CVE-2025-20363 N/A Disabled This is a New Detection
Managed Ruleset Updated
This update introduces 11 new detections in the Cloudflare Managed Ruleset (all currently set to Disabled mode to preserve remediation logic and allow quick activation if needed). The rules cover a broad spectrum of threats - SQL injection techniques, command and code injection, information disclosure of common files, URL anomalies, and cross-site scripting.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100859A SQLi - UNION - 3 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100889 Command Injection - Generic 9 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100890 Information Disclosure - Common Files - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100891 Anomaly:URL - Relative Paths N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100894 XSS - Inline Function N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100895 XSS - DOM N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100896 SQLi - MSSQL Length Enumeration N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100897 Generic Rules - Code Injection - 3 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100898 SQLi - Evasion N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100899 SQLi - Probing 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100900 SQLi - Probing N/A Disabled This is a New Detection
This week highlights a critical vendor-specific vulnerability: a deserialization flaw in the License Servlet of Fortra’s GoAnywhere MFT. By forging a license response signature, an attacker can trigger deserialization of arbitrary objects, potentially leading to command injection.
Key Findings
- GoAnywhere MFT (CVE-2025-10035): Deserialization vulnerability in the License Servlet that allows attackers with a forged license response signature to deserialize arbitrary objects, potentially resulting in command injection.
Impact
GoAnywhere MFT (CVE-2025-10035): Exploitation enables attackers to escalate privileges or achieve remote code execution via command injection.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100787 Fortra GoAnywhere - Auth Bypass - CVE:CVE-2025-10035 N/A Block This is a New Detection
This week emphasizes two critical vendor-specific vulnerabilities: a full elevation-of-privilege in Microsoft Azure Networking (CVE-2025-54914) and a server-side template injection (SSTI) leading to remote code execution (RCE) in Skyvern (CVE-2025-49619). These are complemented by enhancements in generic detections (SQLi, SSRF) to improve baseline coverage.
Key Findings
-
Azure (CVE-2025-54914): Vulnerability in Azure Networking allowing elevation of privileges.
-
Skyvern (CVE-2025-49619): Skyvern ≤ 0.1.85 has a server-side template injection (SSTI) vulnerability in its Prompt field (workflow blocks) via Jinja2. Authenticated users with low privileges can get remote code execution (blind).
-
Generic SQLi / SSRF improvements: Expanded rule coverage to detect obfuscated SQL injection patterns and SSRF across host, local, and cloud contexts.
Impact
These vulnerabilities allow attackers to escalate privileges or execute code under conditions where previously they could not:
-
Azure CVE-2025-54914 enables an attacker from the network with no credentials to gain high-level access within Azure Networking; could lead to full compromise of networking components.
-
Skyvern CVE-2025-49619 allows authenticated users with minimal privilege to exploit SSTI for remote code execution, undermining isolation of workflow components.
-
The improvements for SQLi and SSRF reduce risk from common injection and request-based attacks.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100146 SSRF - Host - 2 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100146B SSRF - Local - 2 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100146C SSRF - Cloud - 2 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100714 Azure - Auth Bypass - CVE:CVE-2025-54914 Log Block This is a New Detection Cloudflare Managed Ruleset 100758 Skyvern - Remote Code Execution - CVE:CVE-2025-49619 Log Block This is a New Detection Cloudflare Managed Ruleset 100773 Next.js - SSRF Log Block This is a New Detection Cloudflare Managed Ruleset 100774 Adobe Commerce - Remote Code Execution - CVE:CVE-2025-54236 Log Block This is a New Detection Cloudflare Managed Ruleset 100800_BETA SQLi - Obfuscated Boolean - Beta Log Block This rule has been merged into the original rule (ID: -
You can now route private traffic to Cloudflare Tunnel based on a hostname or domain, moving beyond the limitations of IP-based routing. This new capability is free for all Cloudflare One customers.
Previously, Tunnel routes could only be defined by IP address or CIDR range. This created a challenge for modern applications with dynamic or ephemeral IP addresses, often forcing administrators to maintain complex and brittle IP lists.
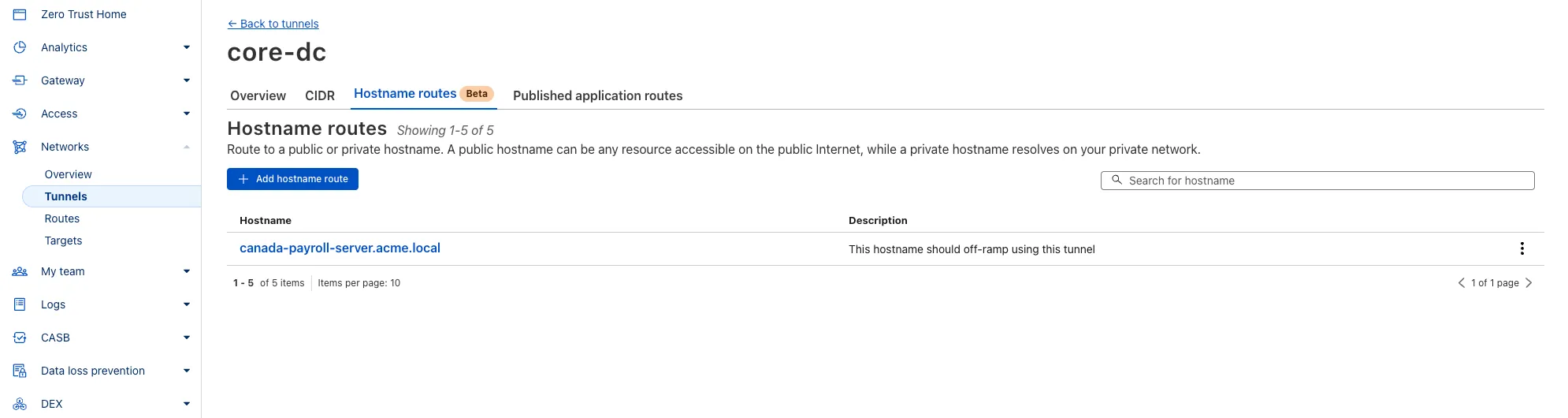
What’s new:
- Hostname & Domain Routing: Create routes for individual hostnames (e.g.,
payroll.acme.local) or entire domains (e.g.,*.acme.local) and direct their traffic to a specific Tunnel. - Simplified Zero Trust Policies: Build resilient policies in Cloudflare Access and Gateway using stable hostnames, making it dramatically easier to apply per-resource authorization for your private applications.
- Precise Egress Control: Route traffic for public hostnames (e.g.,
bank.example.com) through a specific Tunnel to enforce a dedicated source IP, solving the IP allowlist problem for third-party services. - No More IP Lists: This feature makes the workaround of maintaining dynamic IP Lists for Tunnel connections obsolete.
Get started in the Tunnels section of the Zero Trust dashboard with your first private hostname or public hostname route.
Learn more in our blog post ↗.
- Hostname & Domain Routing: Create routes for individual hostnames (e.g.,
This week's update
This week's focus highlights newly disclosed vulnerabilities in DevOps tooling, data visualization platforms, and enterprise CMS solutions. These issues include sensitive information disclosure and remote code execution, putting organizations at risk of credential leakage, unauthorized access, and full system compromise.
Key Findings
-
Argo CD (CVE-2025-55190): Exposure of sensitive information could allow attackers to access credential data stored in configurations, potentially leading to compromise of Kubernetes workloads and secrets.
-
DataEase (CVE-2025-57773): Insufficient input validation enables JNDI injection and insecure deserialization, resulting in remote code execution (RCE). Successful exploitation grants attackers control over the application server.
-
Sitecore (CVE-2025-53694): A sensitive information disclosure flaw allows unauthorized access to confidential information stored in Sitecore deployments, raising the risk of data breaches and privilege escalation.
Impact
These vulnerabilities expose organizations to serious risks, including credential theft, unauthorized access, and full system compromise. Argo CD's flaw may expose Kubernetes secrets, DataEase exploitation could give attackers remote execution capabilities, and Sitecore's disclosure issue increases the likelihood of sensitive data leakage and business impact.
Administrators are strongly advised to apply vendor patches immediately, rotate exposed credentials, and review access controls to mitigate these risks.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100646 Argo CD - Information Disclosure - CVE:CVE-2025-55190s Log Disabled This is a New Detection Cloudflare Managed Ruleset 100874 DataEase - JNDI injection - CVE:CVE-2025-57773 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100880 Sitecore - Information Disclosure - CVE:CVE-2025-53694 Log Block This is a New Detection -
This week's update
This week’s focus highlights newly disclosed vulnerabilities in web frameworks, enterprise applications, and widely deployed CMS plugins. The vulnerabilities include SSRF, authentication bypass, arbitrary file upload, and remote code execution (RCE), exposing organizations to high-impact risks such as unauthorized access, system compromise, and potential data exposure. In addition, security rule enhancements have been deployed to cover general command injection and server-side injection attacks, further strengthening protections.
Key Findings
-
Next.js (CVE-2025-57822): Improper handling of redirects in custom middleware can lead to server-side request forgery (SSRF) when user-supplied headers are forwarded. Attackers could exploit this to access internal services or cloud metadata endpoints. The issue has been resolved in versions 14.2.32 and 15.4.7. Developers using custom middleware should upgrade and verify proper redirect handling in
next()calls. -
ScriptCase (CVE-2025-47227, CVE-2025-47228): In the Production Environment extension in Netmake ScriptCase through 9.12.006 (23), two vulnerabilities allow attackers to reset admin accounts and execute system commands, potentially leading to full compromise of affected deployments.
-
Sar2HTML (CVE-2025-34030): In Sar2HTML version 3.2.2 and earlier, insufficient input sanitization of the plot parameter allows remote, unauthenticated attackers to execute arbitrary system commands. Exploitation could compromise the underlying server and its data.
-
Zhiyuan OA (CVE-2025-34040): An arbitrary file upload vulnerability exists in the Zhiyuan OA platform. Improper validation in the
wpsAssistServletinterface allows unauthenticated attackers to upload crafted files via path traversal, which can be executed on the web server, leading to remote code execution. -
WordPress:Plugin:InfiniteWP Client (CVE-2020-8772): A vulnerability in the InfiniteWP Client plugin allows attackers to perform restricted actions and gain administrative control of connected WordPress sites.
Impact
These vulnerabilities could allow attackers to gain unauthorized access, execute malicious code, or take full control of affected systems. The Next.js SSRF flaw may expose internal services or cloud metadata endpoints to attackers. Exploitations of ScriptCase and Sar2HTML could result in remote code execution, administrative takeover, and full server compromise. In Zhiyuan OA, the arbitrary file upload vulnerability allows attackers to execute malicious code on the web server, potentially exposing sensitive data and applications. The authentication bypass in WordPress InfiniteWP Client enables attackers to gain administrative access, risking data exposure and unauthorized control of connected sites.
Administrators are strongly advised to apply vendor patches immediately, remove unsupported software, and review authentication and access controls to mitigate these risks.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100007D Command Injection - Common Attack Commands Args Log Block This rule has been merged into the original rule "Command Injection - Common Attack Commands" (ID: Cloudflare Managed Ruleset 100617 Next.js - SSRF - CVE:CVE-2025-57822 Log Block This is a New Detection Cloudflare Managed Ruleset 100659_BETA Common Payloads for Server-Side Template Injection - Beta Log Block This rule is merged into the original rule "Common Payloads for Server-Side Template Injection" (ID: Cloudflare Managed Ruleset 100824B CrushFTP - Remote Code Execution - CVE:CVE-2025-54309 - 3 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100848 ScriptCase - Auth Bypass - CVE:CVE-2025-47227 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100849 ScriptCase - Command Injection - CVE:CVE-2025-47228 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100872 WordPress:Plugin:InfiniteWP Client - Missing Authorization - CVE:CVE-2020-8772 Log Block This is a New Detection Cloudflare Managed Ruleset 100873 Sar2HTML - Command Injection - CVE:CVE-2025-34030 Log Block This is a New Detection Cloudflare Managed Ruleset 100875 Zhiyuan OA - Remote Code Execution - CVE:CVE-2025-34040 Log Block This is a New Detection -
This week's update
This week, new critical vulnerabilities were disclosed in Sitecore’s Sitecore Experience Manager (XM), Sitecore Experience Platform (XP), specifically versions 9.0 through 9.3, and 10.0 through 10.4. These flaws are caused by unsafe data deserialization and code reflection, leaving affected systems at high risk of exploitation.
Key Findings
- CVE-2025-53690: Remote Code Execution through Insecure Deserialization
- CVE-2025-53691: Remote Code Execution through Insecure Deserialization
- CVE-2025-53693: HTML Cache Poisoning through Unsafe Reflections
Impact
Exploitation could allow attackers to execute arbitrary code remotely on the affected system and conduct cache poisoning attacks, potentially leading to further compromise. Applying the latest vendor-released solution without delay is strongly recommended.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100878 Sitecore - Remote Code Execution - CVE:CVE-2025-53691 N/A Block This is a new detection Cloudflare Managed Ruleset 100631 Sitecore - Cache Poisoning - CVE:CVE-2025-53693 N/A Block This is a new detection Cloudflare Managed Ruleset 100879 Sitecore - Remote Code Execution - CVE:CVE-2025-53690 N/A Block This is a new detection
Starting December 1, 2025, list endpoints for the Cloudflare Tunnel API and Zero Trust Networks API will no longer return deleted tunnels, routes, subnets and virtual networks by default. This change makes the API behavior more intuitive by only returning active resources unless otherwise specified.
No action is required if you already explicitly set
is_deleted=falseor if you only need to list active resources.This change affects the following API endpoints:
- List all tunnels:
GET /accounts/{account_id}/tunnels - List Cloudflare Tunnels:
GET /accounts/{account_id}/cfd_tunnel - List WARP Connector tunnels:
GET /accounts/{account_id}/warp_connector - List tunnel routes:
GET /accounts/{account_id}/teamnet/routes - List subnets:
GET /accounts/{account_id}/zerotrust/subnets - List virtual networks:
GET /accounts/{account_id}/teamnet/virtual_networks
The default behavior of the
is_deletedquery parameter will be updated.Scenario Previous behavior (before December 1, 2025) New behavior (from December 1, 2025) is_deletedparameter is omittedReturns active & deleted tunnels, routes, subnets and virtual networks Returns only active tunnels, routes, subnets and virtual networks If you need to retrieve deleted (or all) resources, please update your API calls to explicitly include the
is_deletedparameter before December 1, 2025.To get a list of only deleted resources, you must now explicitly add the
is_deleted=truequery parameter to your request:Terminal window # Example: Get ONLY deleted Tunnelscurl "https://api.cloudflare.com/client/v4/accounts/$ACCOUNT_ID/tunnels?is_deleted=true" \-H "Authorization: Bearer $API_TOKEN"# Example: Get ONLY deleted Virtual Networkscurl "https://api.cloudflare.com/client/v4/accounts/$ACCOUNT_ID/teamnet/virtual_networks?is_deleted=true" \-H "Authorization: Bearer $API_TOKEN"Following this change, retrieving a complete list of both active and deleted resources will require two separate API calls: one to get active items (by omitting the parameter or using
is_deleted=false) and one to get deleted items (is_deleted=true).This update is based on user feedback and aims to:
- Create a more intuitive default: Aligning with common API design principles where list operations return only active resources by default.
- Reduce unexpected results: Prevents users from accidentally operating on deleted resources that were returned unexpectedly.
- Improve performance: For most users, the default query result will now be smaller and more relevant.
To learn more, please visit the Cloudflare Tunnel API and Zero Trust Networks API documentation.
- List all tunnels:
This week's update
This week, a critical vulnerability was disclosed in Fortinet FortiWeb (versions 7.6.3 and below, versions 7.4.7 and below, versions 7.2.10 and below, and versions 7.0.10 and below), linked to improper parameter handling that could allow unauthorized access.
Key Findings
- Fortinet FortiWeb (CVE-2025-52970): A vulnerability may allow an unauthenticated remote attacker with access to non-public information to log in as any existing user on the device via a specially crafted request.
Impact
Exploitation could allow an unauthenticated attacker to impersonate any existing user on the device, potentially enabling them to modify system settings or exfiltrate sensitive information, posing a serious security risk. Upgrading to the latest vendor-released version is strongly recommended.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100586 Fortinet FortiWeb - Auth Bypass - CVE:CVE-2025-52970 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100136C XSS - JavaScript - Headers and Body N/A N/A Rule metadata description refined. Detection unchanged.
This week's update
This week, new critical vulnerabilities were disclosed in Next.js’s image optimization functionality, exposing a broad range of production environments to risks of data exposure and cache manipulation.
Key Findings
-
CVE-2025-55173: Arbitrary file download from the server via image optimization.
-
CVE-2025-57752: Cache poisoning leading to unauthorized data disclosure.
Impact
Exploitation could expose sensitive files, leak user or backend data, and undermine application trust. Given Next.js’s wide use, immediate patching and cache hardening are strongly advised.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100613 Next.js - Dangerous File Download - CVE:CVE-2025-55173 N/A Block This is a new detection Cloudflare Managed Ruleset 100616 Next.js - Information Disclosure - CVE:CVE-2025-57752 N/A Block This is a new detection -
Cloudflare Secrets Store is now integrated with AI Gateway, allowing you to store, manage, and deploy your AI provider keys in a secure and seamless configuration through Bring Your Own Key ↗. Instead of passing your AI provider keys directly in every request header, you can centrally manage each key with Secrets Store and deploy in your gateway configuration using only a reference, rather than passing the value in plain text.
You can now create a secret directly from your AI Gateway in the dashboard ↗ by navigating into your gateway -> Provider Keys -> Add.
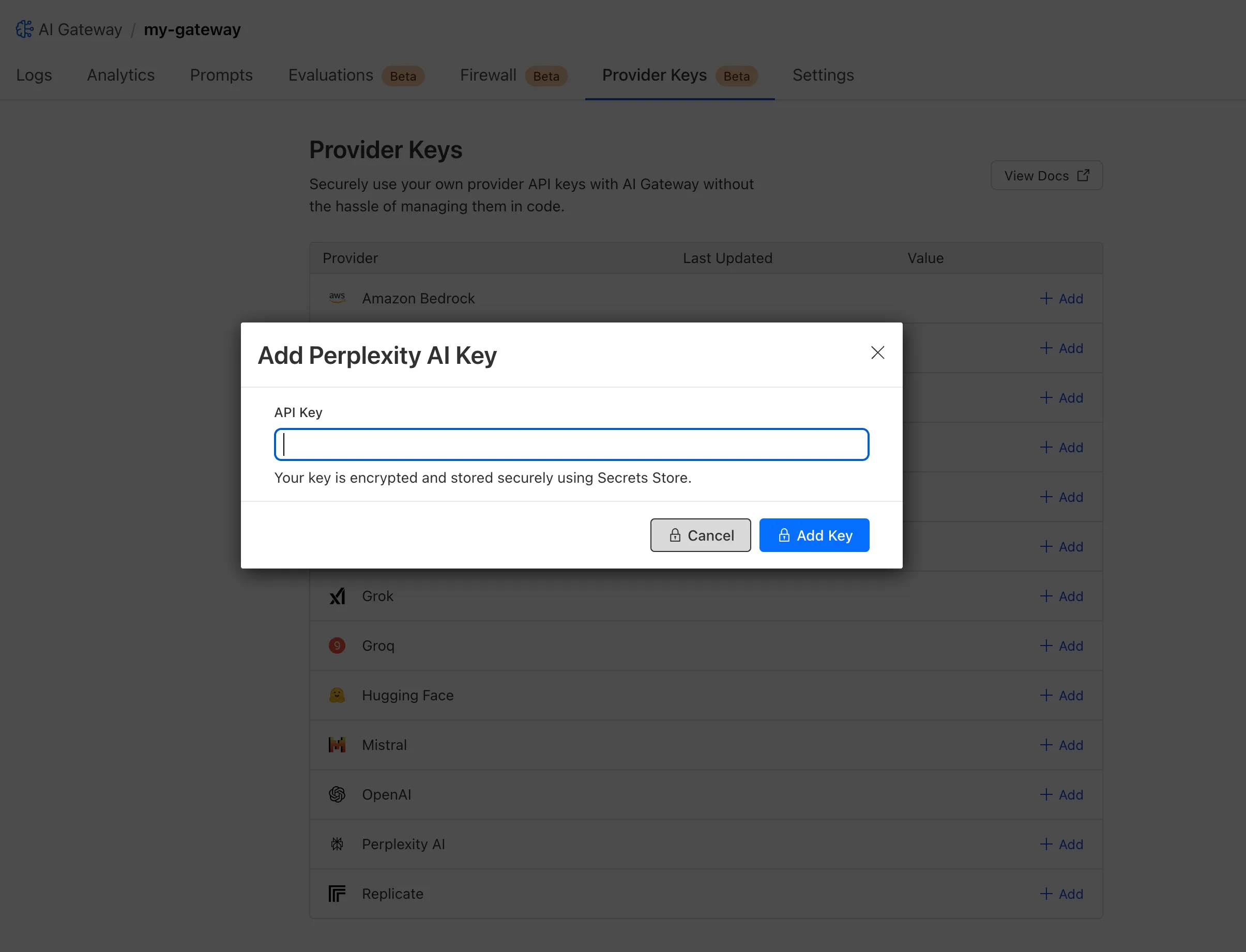
You can also create your secret with the newly available ai_gateway scope via wrangler ↗, the Secrets Store dashboard ↗, or the API ↗.
Then, pass the key in the request header using its Secrets Store reference:
curl -X POST https://gateway.ai.cloudflare.com/v1/<ACCOUNT_ID>/my-gateway/anthropic/v1/messages \--header 'cf-aig-authorization: ANTHROPIC_KEY_1 \--header 'anthropic-version: 2023-06-01' \--header 'Content-Type: application/json' \--data '{"model": "claude-3-opus-20240229", "messages": [{"role": "user", "content": "What is Cloudflare?"}]}'Or, using Javascript:
import Anthropic from '@anthropic-ai/sdk';const anthropic = new Anthropic({apiKey: "ANTHROPIC_KEY_1",baseURL: "https://gateway.ai.cloudflare.com/v1/<ACCOUNT_ID>/my-gateway/anthropic",});const message = await anthropic.messages.create({model: 'claude-3-opus-20240229',messages: [{role: "user", content: "What is Cloudflare?"}],max_tokens: 1024});For more information, check out the blog ↗!
This week's update
This week, critical vulnerabilities were disclosed that impact widely used open-source infrastructure, creating high-risk scenarios for code execution and operational disruption.
Key Findings
-
Apache HTTP Server – Code Execution (CVE-2024-38474): A flaw in Apache HTTP Server allows attackers to achieve remote code execution, enabling full compromise of affected servers. This vulnerability threatens the confidentiality, integrity, and availability of critical web services.
-
Laravel (CVE-2024-55661): A security flaw in Laravel introduces the potential for remote code execution under specific conditions. Exploitation could provide attackers with unauthorized access to application logic and sensitive backend data.
Impact
These vulnerabilities pose severe risks to enterprise environments and open-source ecosystems. Remote code execution enables attackers to gain deep system access, steal data, disrupt services, and establish persistent footholds for broader intrusions. Given the widespread deployment of Apache HTTP Server and Laravel in production systems, timely patching and mitigation are critical.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100822_BETA WordPress:Plugin:WPBookit - Remote Code Execution - CVE:CVE-2025-6058 N/A Disabled This was merged in to the original rule "WordPress:Plugin:WPBookit - Remote Code Execution - CVE:CVE-2025-6058" (ID: Cloudflare Managed Ruleset 100831 Apache HTTP Server - Code Execution - CVE:CVE-2024-38474 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100846 Laravel - Remote Code Execution - CVE:CVE-2024-55661 Log Disabled This is a New Detection -
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100850 Command Injection - Generic 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100851 Remote Code Execution - Java Deserialization N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100852 Command Injection - Generic 3 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100853 Remote Code Execution - Common Bash Bypass Beta N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100854 XSS - Generic JavaScript N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100855 Command Injection - Generic 4 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100856 PHP Object Injection N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100857 Generic - Parameter Fuzzing N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100858 Code Injection - Generic 4 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100859 SQLi - UNION - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100860 Command Injection - Generic 5 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100861 Command Execution - Generic N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100862 GraphQL Injection - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100863 Command Injection - Generic 6 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100864 Code Injection - Generic 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100865 PHP Object Injection - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100866 SQLi - LIKE 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100867 SQLi - DROP - 2 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100868 Code Injection - Generic 3 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100869 Command Injection - Generic 7 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100870 Command Injection - Generic 8 N/A Disabled This is a New Detection Cloudflare Managed Ruleset 100871 SQLi - LIKE 3 N/A Disabled This is a New Detection
This week's update
This week, a series of critical vulnerabilities were discovered impacting core enterprise and open-source infrastructure. These flaws present a range of risks, providing attackers with distinct pathways for remote code execution, methods to breach internal network boundaries, and opportunities for critical data exposure and operational disruption.
Key Findings
-
SonicWall SMA (CVE-2025-32819, CVE-2025-32820, CVE-2025-32821): A remote authenticated attacker with SSLVPN user privileges can bypass path traversal protections. These vulnerabilities enable a attacker to bypass security checks to read, modify, or delete arbitrary files. An attacker with administrative privileges can escalate this further, using a command injection flaw to upload malicious files, which could ultimately force the appliance to reboot to its factory default settings.
-
Ms-Swift Project (CVE-2025-50460): An unsafe deserialization vulnerability exists in the Ms-Swift project's handling of YAML configuration files. If an attacker can control the content of a configuration file passed to the application, they can embed a malicious payload that will execute arbitrary code and it can be executed during deserialization.
-
Apache Druid (CVE-2023-25194): This vulnerability in Apache Druid allows an attacker to cause the server to connect to a malicious LDAP server. By sending a specially crafted LDAP response, the attacker can trigger an unrestricted deserialization of untrusted data. If specific "gadgets" (classes that can be abused) are present in the server's classpath, this can be escalated to achieve Remote Code Execution (RCE).
-
Tenda AC8v4 (CVE-2025-51087, CVE-2025-51088): Vulnerabilities allow an authenticated attacker to trigger a stack-based buffer overflow. By sending malformed arguments in a request to specific endpoints, an attacker can crash the device or potentially achieve arbitrary code execution.
-
Open WebUI (CVE-2024-7959): This vulnerability allows a user to change the OpenAI URL endpoint to an arbitrary internal network address without proper validation. This flaw can be exploited to access internal services or cloud metadata endpoints, potentially leading to remote command execution if the attacker can retrieve instance secrets or access sensitive internal APIs.
-
BentoML (CVE-2025-54381): The vulnerability exists in the serialization/deserialization handlers for multipart form data and JSON requests, which automatically download files from user-provided URLs without proper validation of internal network addresses. This allows attackers to fetch from unintended internal services, including cloud metadata and localhost.
-
Adobe Experience Manager Forms (CVE-2025-54254): An Improper Restriction of XML External Entity Reference ('XXE') vulnerability that could lead to arbitrary file system read in Adobe AEM (≤6.5.23).
Impact
These vulnerabilities affect core infrastructure, from network security appliances like SonicWall to data platforms such as Apache Druid and ML frameworks like BentoML. The code execution and deserialization flaws are particularly severe, offering deep system access that allows attackers to steal data, disrupt services, and establish a foothold for broader intrusions. Simultaneously, SSRF and XXE vulnerabilities undermine network boundaries, exposing sensitive internal data and creating pathways for lateral movement. Beyond data-centric threats, flaws in edge devices like the Tenda router introduce the tangible risk of operational disruption, highlighting a multi-faceted threat to the security and stability of key enterprise systems.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100574 SonicWall SMA - Remote Code Execution - CVE:CVE-2025-32819, CVE:CVE-2025-32820, CVE:CVE-2025-32821 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100576 Ms-Swift Project - Remote Code Execution - CVE:CVE-2025-50460 Log Block This is a New Detection Cloudflare Managed Ruleset 100585 Apache Druid - Remote Code Execution - CVE:CVE-2023-25194 Log Block This is a New Detection Cloudflare Managed Ruleset 100834 Tenda AC8v4 - Auth Bypass - CVE:CVE-2025-51087, CVE:CVE-2025-51088 Log Block This is a New Detection Cloudflare Managed Ruleset 100835 Open WebUI - SSRF - CVE:CVE-2024-7959 Log Block This is a New Detection Cloudflare Managed Ruleset 100837 SQLi - OOB Log Block This is a New Detection Cloudflare Managed Ruleset 100841 BentoML - SSRF - CVE:CVE-2025-54381 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100841A BentoML - SSRF - CVE:CVE-2025-54381 - 2 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100841B BentoML - SSRF - CVE:CVE-2025-54381 - 3 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100845 Adobe Experience Manager Forms - XSS - CVE:CVE-2025-54254 Log Block This is a New Detection Cloudflare Managed Ruleset 100845A Adobe Experience Manager Forms - XSS - CVE:CVE-2025-54254 - 2 Log Block This is a New Detection -
Brand Protection detects domains that may be impersonating your brand — from common misspellings (
cloudfalre.com) to malicious concatenations (cloudflare-okta.com). Saved search queries run continuously and alert you when suspicious domains appear.You can now create and save multiple queries in a single step, streamlining setup and management. Available now via the Brand Protection bulk query creation API.
This week's update focuses on a wide range of enterprise software, from network infrastructure and security platforms to content management systems and development frameworks. Flaws include unsafe deserialization, OS command injection, SSRF, authentication bypass, and arbitrary file upload — many of which allow unauthenticated remote code execution. Notable risks include Cisco Identity Services Engine and Ivanti EPMM, where successful exploitation could grant attackers full administrative control of core network infrastructure and popular web services such as WordPress, SharePoint, and Ingress-Nginx, where security bypasses and arbitrary file uploads could lead to complete site or server compromise.
Key Findings
-
Cisco Identity Services Engine (CVE-2025-20281): Insufficient input validation in a specific API of Cisco Identity Services Engine (ISE) and ISE-PIC allows an unauthenticated, remote attacker to execute arbitrary code with root privileges on an affected device.
-
Wazuh Server (CVE-2025-24016): An unsafe deserialization vulnerability in Wazuh Server (versions 4.4.0 to 4.9.0) allows for remote code execution and privilege escalation. By injecting unsanitized data, an attacker can trigger an exception to execute arbitrary code on the server.
-
CrushFTP (CVE-2025-54309): A flaw in AS2 validation within CrushFTP allows remote attackers to gain administrative access via HTTPS on systems not using the DMZ proxy feature. This flaw can lead to unauthorized file access and potential system compromise.
-
Kentico Xperience CMS (CVE-2025-2747, CVE-2025-2748): Vulnerabilities in Kentico Xperience CMS could enable cross-site scripting (XSS), allowing attackers to inject malicious scripts into web pages. Additionally, a flaw could allow unauthenticated attackers to bypass the Staging Sync Server's authentication, potentially leading to administrative control over the CMS.
-
Node.js (CVE-2025-27210): An incomplete fix for a previous vulnerability (CVE-2025-23084) in Node.js affects the
path.join()API method on Windows systems. The vulnerability can be triggered using reserved Windows device names such asCON,PRN, orAUX. -
WordPress:Plugin:Simple File List (CVE-2025-34085, CVE-2020-36847): This vulnerability in the Simple File List plugin for WordPress allows an unauthenticated remote attacker to upload arbitrary files to a vulnerable site. This can be exploited to achieve remote code execution on the server.
(Note: CVE-2025-34085 has been rejected as a duplicate.) -
GeoServer (CVE-2024-29198): A Server-Side Request Forgery (SSRF) vulnerability exists in GeoServer's Demo request endpoint, which can be exploited where the Proxy Base URL has not been configured.
-
Ivanti EPMM (CVE-2025-6771): An OS command injection vulnerability in Ivanti Endpoint Manager Mobile (EPMM) before versions 12.5.0.2, 12.4.0.3, and 12.3.0.3 allows a remote, authenticated attacker with high privileges to execute arbitrary code.
-
Microsoft SharePoint (CVE-2024-38018): This is a remote code execution vulnerability affecting Microsoft SharePoint Server.
-
Manager-IO (CVE-2025-54122): A critical unauthenticated full read Server-Side Request Forgery (SSRF) vulnerability is present in the proxy handler of both Manager Desktop and Server editions up to version 25.7.18.2519. This allows an unauthenticated attacker to bypass network isolation and access internal services.
-
Ingress-Nginx (CVE-2025-1974): A vulnerability in the Ingress-Nginx controller for Kubernetes allows an attacker to bypass access control rules. An unauthenticated attacker with access to the pod network can achieve arbitrary code execution in the context of the ingress-nginx controller.
-
PaperCut NG/MF (CVE-2023-2533): A Cross-Site Request Forgery (CSRF) vulnerability has been identified in PaperCut NG/MF. Under specific conditions, an attacker could exploit this to alter security settings or execute arbitrary code if they can deceive an administrator with an active login session into clicking a malicious link.
-
SonicWall SMA (CVE-2025-40598): This vulnerability could allow an unauthenticated attacker to bypass security controls. This allows a remote, unauthenticated attacker to potentially execute arbitrary JavaScript code.
-
WordPress (CVE-2025-5394): The "Alone – Charity Multipurpose Non-profit WordPress Theme" for WordPress is vulnerable to arbitrary file uploads. A missing capability check allows unauthenticated attackers to upload ZIP files containing webshells disguised as plugins, leading to remote code execution.
Impact
These vulnerabilities span a broad range of enterprise technologies, including network access control systems, monitoring platforms, web servers, CMS platforms, cloud services, and collaboration tools. Exploitation techniques range from remote code execution and command injection to authentication bypass, SQL injection, path traversal, and configuration weaknesses.
A critical flaw in perimeter devices like Ivanti EPMM or SonicWall SMA could allow an unauthenticated attacker to gain remote code execution, completely breaching the primary network defense. A separate vulnerability within Cisco's Identity Services Engine could then be exploited to bypass network segmentation, granting an attacker widespread internal access. Insecure deserialization issues in platforms like Wazuh Server and CrushFTP could then be used to run malicious payloads or steal sensitive files from administrative consoles. Weaknesses in web delivery controllers like Ingress-Nginx or popular content management systems such as WordPress, SharePoint, and Kentico Xperience create vectors to bypass security controls, exfiltrate confidential data, or fully compromise servers.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100538 GeoServer - SSRF - CVE:CVE-2024-29198 Log Block This is a New Detection Cloudflare Managed Ruleset 100548 Ivanti EPMM - Remote Code Execution - CVE:CVE-2025-6771 Log Block This is a New Detection Cloudflare Managed Ruleset 100550 Microsoft SharePoint - Remote Code Execution - CVE:CVE-2024-38018 Log Block This is a New Detection Cloudflare Managed Ruleset 100562 Manager-IO - SSRF - CVE:CVE-2025-54122 Log Block This is a New Detection Cloudflare Managed Ruleset 100565 Cisco Identity Services Engine - Remote Code Execution - CVE:CVE-2025-20281
Log Block This is a New Detection Cloudflare Managed Ruleset 100567 Ingress-Nginx - Remote Code Execution - CVE:CVE-2025-1974 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100569 PaperCut NG/MF - Remote Code Execution - CVE:CVE-2023-2533 Log Block This is a New Detection Cloudflare Managed Ruleset 100571 SonicWall SMA - XSS - CVE:CVE-2025-40598 Log Block This is a New Detection Cloudflare Managed Ruleset 100573 WordPress - Dangerous File Upload - CVE:CVE-2025-5394 Log Block This is a New Detection Cloudflare Managed Ruleset 100806 Wazuh Server - Remote Code Execution - CVE:CVE-2025-24016 Log Block This is a New Detection Cloudflare Managed Ruleset 100824 CrushFTP - Remote Code Execution - CVE:CVE-2025-54309 Log Block This is a New Detection Cloudflare Managed Ruleset 100824A CrushFTP - Remote Code Execution - CVE:CVE-2025-54309 - 2 Log Block This is a New Detection Cloudflare Managed Ruleset 100825 AMI MegaRAC - Auth Bypass - CVE:CVE-2024-54085 Log Block This is a New Detection Cloudflare Managed Ruleset 100826 Kentico Xperience CMS - Auth Bypass - CVE:CVE-2025-2747 Log Block This is a New Detection Cloudflare Managed Ruleset 100827 Kentico Xperience CMS - XSS - CVE:CVE-2025-2748 Log Block This is a New Detection Cloudflare Managed Ruleset 100828 Node.js - Directory Traversal - CVE:CVE-2025-27210 Log Block This is a New Detection Cloudflare Managed Ruleset 100829 WordPress:Plugin:Simple File List - Remote Code Execution - CVE:CVE-2025-34085
Log Block This is a New Detection Cloudflare Managed Ruleset 100829A WordPress:Plugin:Simple File List - Remote Code Execution - CVE:CVE-2025-34085 - 2
Log Disabled This is a New Detection -
This week’s highlight focuses on two critical vulnerabilities affecting key infrastructure and enterprise content management platforms. Both flaws present significant remote code execution risks that can be exploited with minimal or no user interaction.
Key Findings
-
Squid (≤6.3) — CVE-2025-54574: A heap buffer overflow occurs when processing Uniform Resource Names (URNs). This vulnerability may allow remote attackers to execute arbitrary code on the server. The issue has been resolved in version 6.4.
-
Adobe AEM (≤6.5.23) — CVE-2025-54253: Due to a misconfiguration, attackers can achieve remote code execution without requiring any user interaction, posing a severe threat to affected deployments.
Impact
Both vulnerabilities expose critical attack vectors that can lead to full server compromise. The Squid heap buffer overflow allows remote code execution by crafting malicious URNs, which can lead to server takeover or denial of service. Given Squid’s widespread use as a caching proxy, this flaw could be exploited to disrupt network traffic or gain footholds inside secure environments.
Adobe AEM’s remote code execution vulnerability enables attackers to run arbitrary code on the content management server without any user involvement. This puts sensitive content, application integrity, and the underlying infrastructure at extreme risk. Exploitation could lead to data theft, defacement, or persistent backdoor installation.
These findings reinforce the urgency of updating to the patched versions — Squid 6.4 and Adobe AEM 6.5.24 or later — and reviewing configurations to prevent exploitation.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100844 Adobe Experience Manager Forms - Remote Code Execution - CVE:CVE-2025-54253 N/A Block This is a New Detection Cloudflare Managed Ruleset 100840 Squid - Buffer Overflow - CVE:CVE-2025-54574 N/A Block This is a New Detection -
This week's highlight focuses on a series of significant vulnerabilities identified across widely adopted web platforms, from enterprise-grade CMS to essential backend administration tools. The findings reveal multiple vectors for attack, including critical flaws that allow for full server compromise and others that enable targeted attacks against users.
Key Findings
-
Sitecore (CVE-2025-34509, CVE-2025-34510, CVE-2025-34511): A hardcoded credential allows remote attackers to access administrative APIs. Once authenticated, they can exploit an additional vulnerability to upload arbitrary files, leading to remote code execution.
-
Grafana (CVE-2025-4123): A cross-site scripting (XSS) vulnerability allows an attacker to redirect users to a malicious website, which can then execute arbitrary JavaScript in the victim's browser.
-
LaRecipe (CVE-2025-53833): Through Server-Side Template Injection, attackers can execute arbitrary commands on the server, potentially access sensitive environment variables, and escalate access depending on server configuration.
-
CentOS WebPanel (CVE-2025-48703): A command injection vulnerability could allow a remote attacker to execute arbitrary commands on the server.
-
WordPress (CVE-2023-5561): This vulnerability allows unauthenticated attackers to determine the email addresses of users who have published public posts on an affected website.
-
WordPress Plugin - WPBookit (CVE-2025-6058): A missing file type validation allows unauthenticated attackers to upload arbitrary files to the server, creating the potential for remote code execution.
-
WordPress Theme - Motors (CVE-2025-4322): Due to improper identity validation, an unauthenticated attacker can change the passwords of arbitrary users, including administrators, to gain access to their accounts.
Impact
These vulnerabilities pose a multi-layered threat to widely adopted web technologies, ranging from enterprise-grade platforms like Sitecore to everyday solutions such as WordPress, and backend tools like CentOS WebPanel. The most severe risks originate in remote code execution (RCE) flaws found in Sitecore, CentOS WebPanel, LaRecipe, and the WPBookit plugin. These allow attackers to bypass security controls and gain deep access to the server, enabling them to steal sensitive data, deface websites, install persistent malware, or use the compromised server as a launchpad for further attacks.
The privilege escalation vulnerability is the Motors theme, which allows for a complete administrative account takeover on WordPress sites. This effectively hands control of the application to an attacker, who can then manipulate content, exfiltrate user data, and alter site functionality without needing to breach the server itself.
The Grafana cross-site scripting (XSS) flaw can be used to hijack authenticated user sessions or steal credentials, turning a trusted user's browser into an attack vector.
Meanwhile, the information disclosure flaw in WordPress core provides attackers with valid user emails, fueling targeted phishing campaigns that aim to secure the same account access achievable through the other exploits.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100535A Sitecore - Dangerous File Upload - CVE:CVE-2025-34510, CVE:CVE-2025-34511 Log Block This is a New Detection Cloudflare Managed Ruleset 100535 Sitecore - Information Disclosure - CVE:CVE-2025-34509 Log Block This is a New Detection Cloudflare Managed Ruleset 100543 Grafana - Directory Traversal - CVE:CVE-2025-4123 Log Block This is a New Detection Cloudflare Managed Ruleset 100545 WordPress - Information Disclosure - CVE:CVE-2023-5561 Log Block This is a New Detection Cloudflare Managed Ruleset 100820 CentOS WebPanel - Remote Code Execution - CVE:CVE-2025-48703 Log Block This is a New Detection Cloudflare Managed Ruleset 100821 LaRecipe - SSTI - CVE:CVE-2025-53833 Log Block This is a New Detection Cloudflare Managed Ruleset 100822 WordPress:Plugin:WPBookit - Remote Code Execution - CVE:CVE-2025-6058 Log Block This is a New Detection Cloudflare Managed Ruleset 100823 WordPress:Theme:Motors - Privilege Escalation - CVE:CVE-2025-4322 Log Block This is a New Detection -
Any template which uses Worker environment variables, secrets, or Secrets Store secrets can now be deployed using a Deploy to Cloudflare button.
Define environment variables and secrets store bindings in your Wrangler configuration file as normal:
{"name": "my-worker","main": "./src/index.ts",// Set this to today's date"compatibility_date": "2026-03-13","vars": {"API_HOST": "https://example.com",},"secrets_store_secrets": [{"binding": "API_KEY","store_id": "demo","secret_name": "api-key"}]}name = "my-worker"main = "./src/index.ts"# Set this to today's datecompatibility_date = "2026-03-13"[vars]API_HOST = "https://example.com"[[secrets_store_secrets]]binding = "API_KEY"store_id = "demo"secret_name = "api-key"Add secrets to a
.dev.vars.exampleor.env.examplefile:.dev.vars.example COOKIE_SIGNING_KEY=my-secret # commentAnd optionally, you can add a description for these bindings in your template's
package.jsonto help users understand how to configure each value:package.json {"name": "my-worker","private": true,"cloudflare": {"bindings": {"API_KEY": {"description": "Select your company's API key for connecting to the example service."},"COOKIE_SIGNING_KEY": {"description": "Generate a random string using `openssl rand -hex 32`."}}}}These secrets and environment variables will be presented to users in the dashboard as they deploy this template, allowing them to configure each value. Additional information about creating templates and Deploy to Cloudflare buttons can be found in our documentation.