Default HTTP Privacy
Cloudflare runs one of the largest global anycast networks in the world — a network architecture where traffic is automatically routed to the nearest available data center. All current data center locations are accessible on the network map ↗.
Within Cloudflare data centers, and between the Cloudflare network and your origin server, traffic is encrypted during transit. You can select which encryption mode (controlling how strictly Cloudflare validates your server's certificate) and which cipher suites (the specific encryption algorithms used for the connection) to use.
Additionally, all request and response processing within a Cloudflare data center occurs in memory — traffic content is handled by automated systems and is not written to disk, except for eligible content for caching or Cache Rules you have configured. Automated controls prevent Cloudflare personnel from accessing traffic content in the processing pipeline. All cache disks are encrypted at rest (meaning data is encrypted when stored on disk, in addition to being encrypted during transmission).
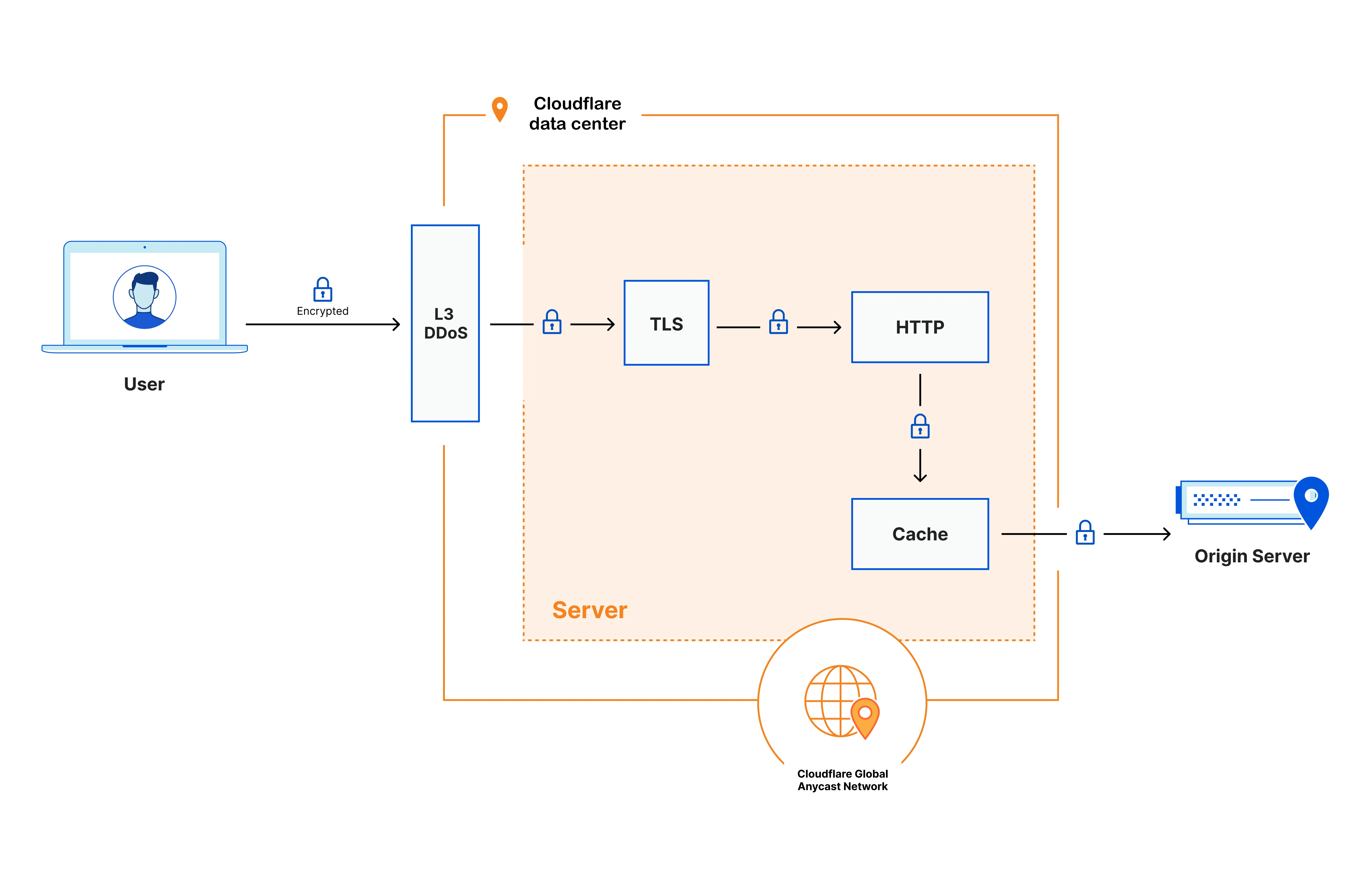
At a high level, when an end user's device connects to any Cloudflare data center, the request is processed in the following way:
-
Certain types of requests that can be used for cyber attacks are immediately dropped based on the addressing information (layer 3 / network layer).
-
Next, the encrypted request is decrypted (TLS termination) and inspected by the Cloudflare security and performance products you have configured — for example, Configuration Rules, WAF Custom Rules, and Rate Limiting Rules — applied in the order defined by the traffic sequence ↗. This process enables the detection and prevention of a variety of cyber attacks, including application-layer (layer 7) DDoS attacks, automated bot traffic, credential stuffing (attackers using stolen username/password combinations), and SQL injection (attackers inserting malicious database commands into web requests), among others.
-
The inspected request is then passed to the caching layer. If a cached copy of the requested content is available, it is served directly to the user. If not, the request is forwarded to your origin server. Traffic between the Cloudflare data center and your origin server is encrypted, unless you have configured a different encryption mode.
-
When the response arrives from your origin server, any static and eligible content is cached onto encrypted disks. The response then passes back through your configured security and performance products before being returned to the user.
By default, Cloudflare performs TLS termination (decryption of HTTPS traffic) in every data center globally — wherever the end user connects to a website or application behind Cloudflare. Customers who need to restrict where decryption occurs can configure Regional Services to specify which regions handle TLS termination and traffic processing.