You can now disable Cloudflare's reverse proxy across all zones in your account simultaneously using the new
enforce_dns_onlysetting. When enabled, Cloudflare responds to DNS queries for all proxied records with your origin IP addresses instead of Cloudflare's anycast IPs. This account-level kill switch is designed for incident response scenarios where you need to quickly route traffic directly to your origin servers.- Account-level — Affects all zones in the account simultaneously with a single API call.
- Non-destructive — Does not modify your DNS records. Disabling the setting restores normal proxy behavior.
- API-only — Available through the API only, not in the Cloudflare dashboard.
Included: Standard proxied A, AAAA, and CNAME records, Load Balancing records, and records matching Worker routes.
Excluded: Spectrum applications, Cloudflare Tunnel CNAMEs, R2 custom domains, Web3 gateways, and Workers custom domains continue to operate normally.
- Verify your origin servers can handle direct traffic without Cloudflare's caching and filtering.
- Review which origin IPs will become publicly visible through DNS queries.
- Test the API in a staging account before relying on it for incident response.
Available via API to all Cloudflare customers.
For information on how to use it, refer to Enforce DNS-only developer documentation .
Internal DNS is now in open beta.
Internal DNS is bundled as a part of Cloudflare Gateway and is now available to every Enterprise customer with one of the following subscriptions:
- Cloudflare Zero Trust Enterprise
- Cloudflare Gateway Enterprise
To learn more and get started, refer to the Internal DNS documentation.
DNS Analytics is now available for customers with Customer Metadata Boundary (CMB) set to EU. Query your DNS analytics data while keeping metadata stored in the EU region.
This update includes:
- DNS Analytics — Access the same DNS analytics experience for zones in CMB=EU accounts.
- EU data residency — Analytics data is stored and queried from the EU region, meeting data localization requirements.
- DNS Firewall Analytics — DNS Firewall analytics is now supported for CMB=EU customers.
Available to customers with the Data Localization Suite who have Customer Metadata Boundary configured for the EU region.
-
Authoritative DNS: In the Cloudflare dashboard, select your zone and go to the Analytics page.
Go to Analytics -
DNS Firewall: In the Cloudflare dashboard, go to the DNS Firewall Analytics page.
Go to Analytics
For more information, refer to DNS Analytics and DNS Firewall Analytics.
-
Access GraphQL-powered DNS Firewall analytics directly in the Cloudflare dashboard.
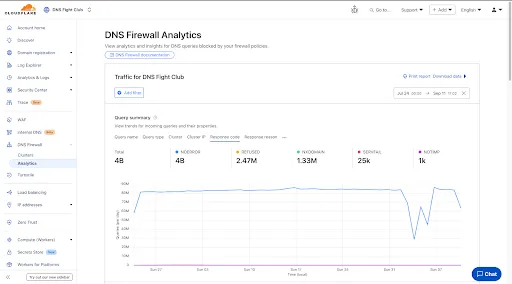
- Query summary: Describes trends over time, segmented by dimensions.
- Query statistics: Describes totals, cached/uncached queries, and processing/response times.
- DNS queries by data center: Describes global view and the top 10 data centers.
- Top query statistics: Shows a breakdown by key dimensions, with search and expand options (up to top 100 items).
Additional features:
- Apply filters and time ranges once. Changes reflect across all panels.
- Filter by dimensions like query name, query type, cluster, data center, protocol (UDP/TCP), IP version, response code/reason, and more.
- Access up to 62 days of historical data with flexible intervals.
Available to all DNS Firewall customers as part of their existing subscription.
-
In the Cloudflare dashboard, go to the DNS Firewall page.
Go to Analytics -
Refer to the DNS Firewall Analytics to learn more.
Authoritative DNS analytics are now available on the account level via the Cloudflare GraphQL Analytics API.
This allows users to query DNS analytics across multiple zones in their account, by using the
accountsfilter.Here is an example to retrieve the most recent DNS queries across all zones in your account that resulted in an
NXDOMAINresponse over a given time frame. Please replacea30f822fcd7c401984bf85d8f2a5111cwith your actual account ID.GraphQL example for account-level DNS analytics query GetLatestNXDOMAINResponses {viewer {accounts(filter: { accountTag: "a30f822fcd7c401984bf85d8f2a5111c" }) {dnsAnalyticsAdaptive(filter: {date_geq: "2025-06-16"date_leq: "2025-06-18"responseCode: "NXDOMAIN"}limit: 10000orderBy: [datetime_DESC]) {zoneTagqueryNameresponseCodequeryTypedatetime}}}}To learn more and get started, refer to the DNS Analytics documentation.
Participating beta testers can now fully configure Internal DNS directly in the Cloudflare dashboard ↗.
-
Map internal hostnames to private IPs for services, devices, and applications not exposed to the public Internet
-
Resolve internal DNS queries securely through Cloudflare Gateway
-
Use split-horizon DNS to return different responses based on network context
-
Consolidate internal and public DNS zones within a single management platform
- Beta participants can now create and manage internal zones and views in the Cloudflare dashboard
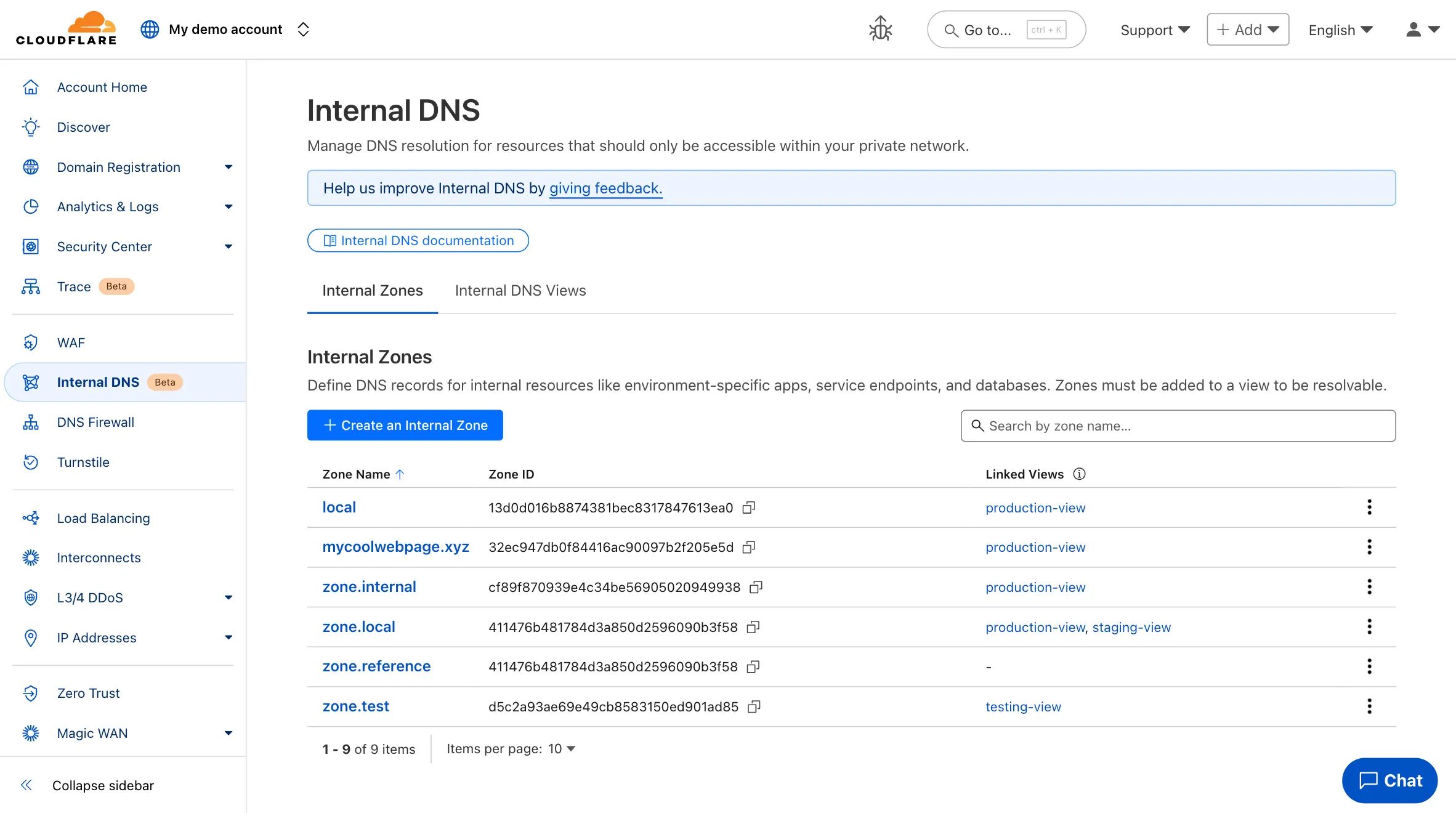
To learn more and get started, refer to the Internal DNS documentation.
-
Enterprise customers can now select NSEC3 as method for proof of non-existence on their zones.
What's new:
-
NSEC3 support for live-signed zones – For both primary and secondary zones that are configured to be live-signed (also known as "on-the-fly signing"), NSEC3 can now be selected as proof of non-existence.
-
NSEC3 support for pre-signed zones – Secondary zones that are transferred to Cloudflare in a pre-signed setup now also support NSEC3 as proof of non-existence.
For more information and how to enable NSEC3, refer to the NSEC3 documentation.
-
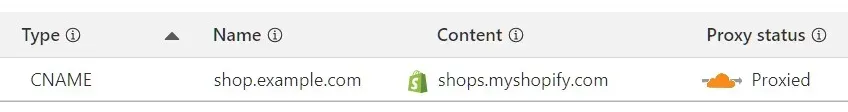
Shopify merchants can now onboard to O2O automatically, without needing to contact support or community members.
What's new:
-
Automatic enablement – O2O is available for all mutual Cloudflare and Shopify customers.
-
Branded record display – Merchants see a Shopify logo in DNS records, complete with helpful tooltips.
-
Checkout protection – Workers and Snippets are blocked from running on the checkout path to reduce risk and improve security.
For more information, refer to the provider guide.
-
Cloudflare is removing five fields from the
metaobject of DNS records. These fields have been unused for more than a year and are no longer set on new records. This change may take up to four weeks to fully roll out.The affected fields are:
- the
auto_addedboolean - the
managed_by_appsboolean and correspondingapps_install_id - the
managed_by_argo_tunnelboolean and correspondingargo_tunnel_id
An example record returned from the API would now look like the following:
Updated API Response {"result": {"id": "<ID>","zone_id": "<ZONE_ID>","zone_name": "example.com","name": "www.example.com","type": "A","content": "192.0.2.1","proxiable": true,"proxied": false,"ttl": 1,"locked": false,"meta": {"auto_added": false,"managed_by_apps": false,"managed_by_argo_tunnel": false,"source": "primary"},"comment": null,"tags": [],"created_on": "2025-03-17T20:37:05.368097Z","modified_on": "2025-03-17T20:37:05.368097Z"},"success": true,"errors": [],"messages": []}For more guidance, refer to Manage DNS records.
- the