VPC Network bindings now give your Workers access to any service in your private network without pre-registering individual hosts or ports. This complements existing VPC Service bindings, which scope each binding to a specific host and port.
You can bind to a Cloudflare Tunnel by
tunnel_idto reach any service on the network where that tunnel is running, or bind to your Cloudflare Mesh network usingcf1:networkto reach any Mesh node, client device, or subnet route in your account:JSONC {"vpc_networks": [{"binding": "MESH","network_id": "cf1:network","remote": true}]}TOML [[vpc_networks]]binding = "MESH"network_id = "cf1:network"remote = trueAt runtime,
fetch()routes through the network to reach the service at the IP and port you specify:JavaScript const response = await env.MESH.fetch("http://10.0.1.50:8080/api/data");For configuration options and examples, refer to VPC Networks and Connect Workers to Cloudflare Mesh.
Each VPC Service now has a Metrics tab so you can monitor connection health and debug failures without leaving the dashboard.
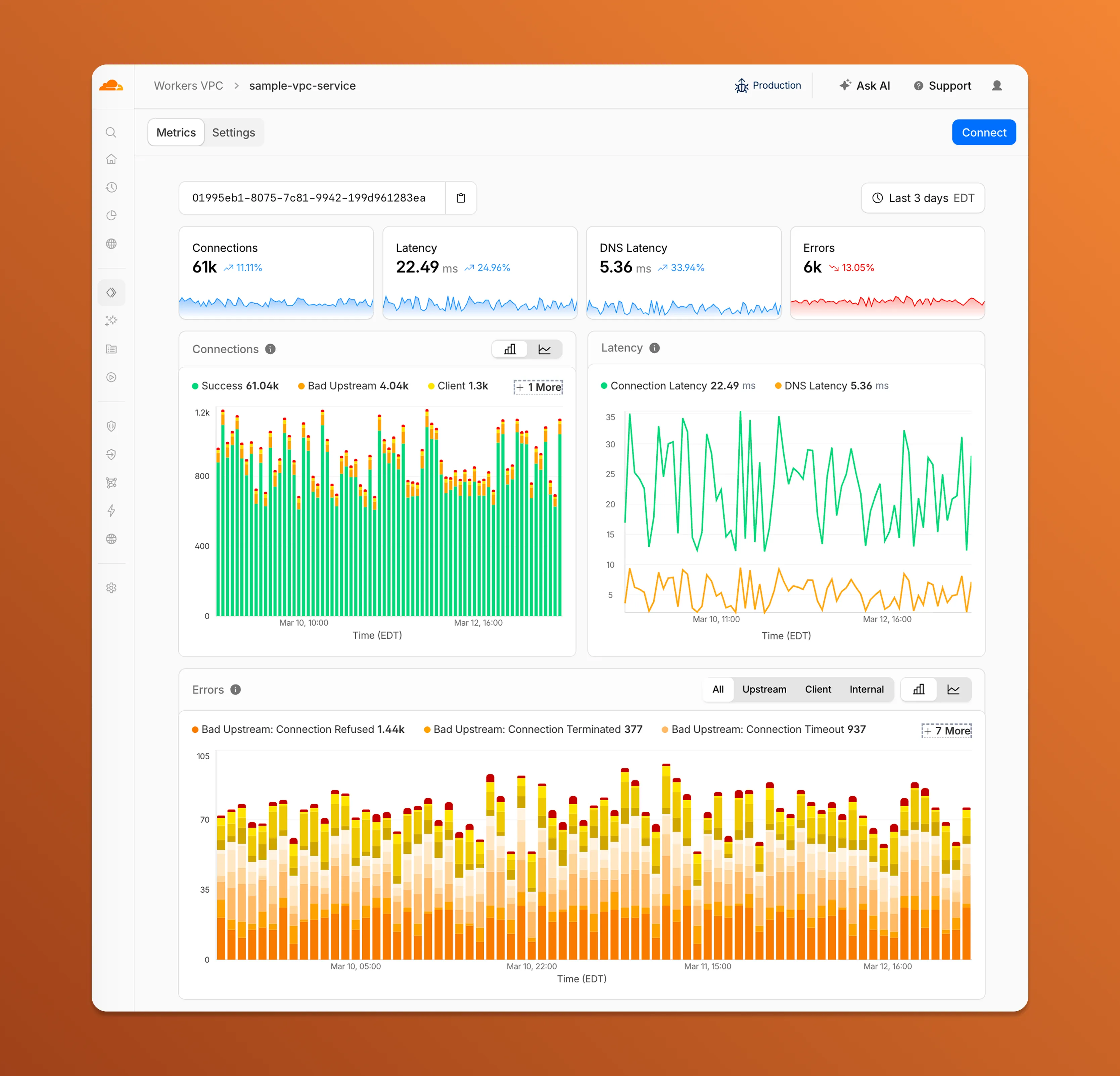
- Connections — See successful and failed connections over time, broken down by what is responsible: your origin (Bad Upstream), your configuration (Client), or Cloudflare (Internal).
- Latency — Track connection and DNS resolution latency trends.
- Errors — Drill into specific error codes grouped by category, with filters to isolate upstream, client, or internal failures.
You can also view and edit your VPC Service configuration, host details, and port assignments from the Settings tab.
For a full list of error codes and what they mean, refer to Troubleshooting.
Workers VPC now supports Cloudflare Origin CA certificates when connecting to your private services over HTTPS. Previously, Workers VPC only trusted certificates issued by publicly trusted certificate authorities (for example, Let's Encrypt, DigiCert).
With this change, you can use free Cloudflare Origin CA certificates on your origin servers within private networks and connect to them from Workers VPC using the
httpsscheme. This is useful for encrypting traffic between the tunnel and your service without needing to provision certificates from a public CA.For more information, refer to Supported TLS certificates.
Workers VPC Services is now available, enabling your Workers to securely access resources in your private networks, without having to expose them on the public Internet.
- VPC Services: Create secure connections to internal APIs, databases, and services using familiar Worker binding syntax
- Multi-cloud Support: Connect to resources in private networks in any external cloud (AWS, Azure, GCP, etc.) or on-premise using Cloudflare Tunnels
JavaScript export default {async fetch(request, env, ctx) {// Perform application logic in Workers here// Sample call to an internal API running on ECS in AWS using the bindingconst response = await env.AWS_VPC_ECS_API.fetch("https://internal-host.example.com");// Additional application logic in Workersreturn new Response();},};Set up a Cloudflare Tunnel, create a VPC Service, add service bindings to your Worker, and access private resources securely. Refer to the documentation to get started.