We have upgraded WAF Payload Logging to enhance rule diagnostics and usability:
- Targeted logging: Logs now capture only the specific portions of requests that triggered WAF rules, rather than entire request segments.
- Visual highlighting: Matched content is visually highlighted in the UI for faster identification.
- Enhanced context: Logs now include surrounding context to make diagnostics more effective.
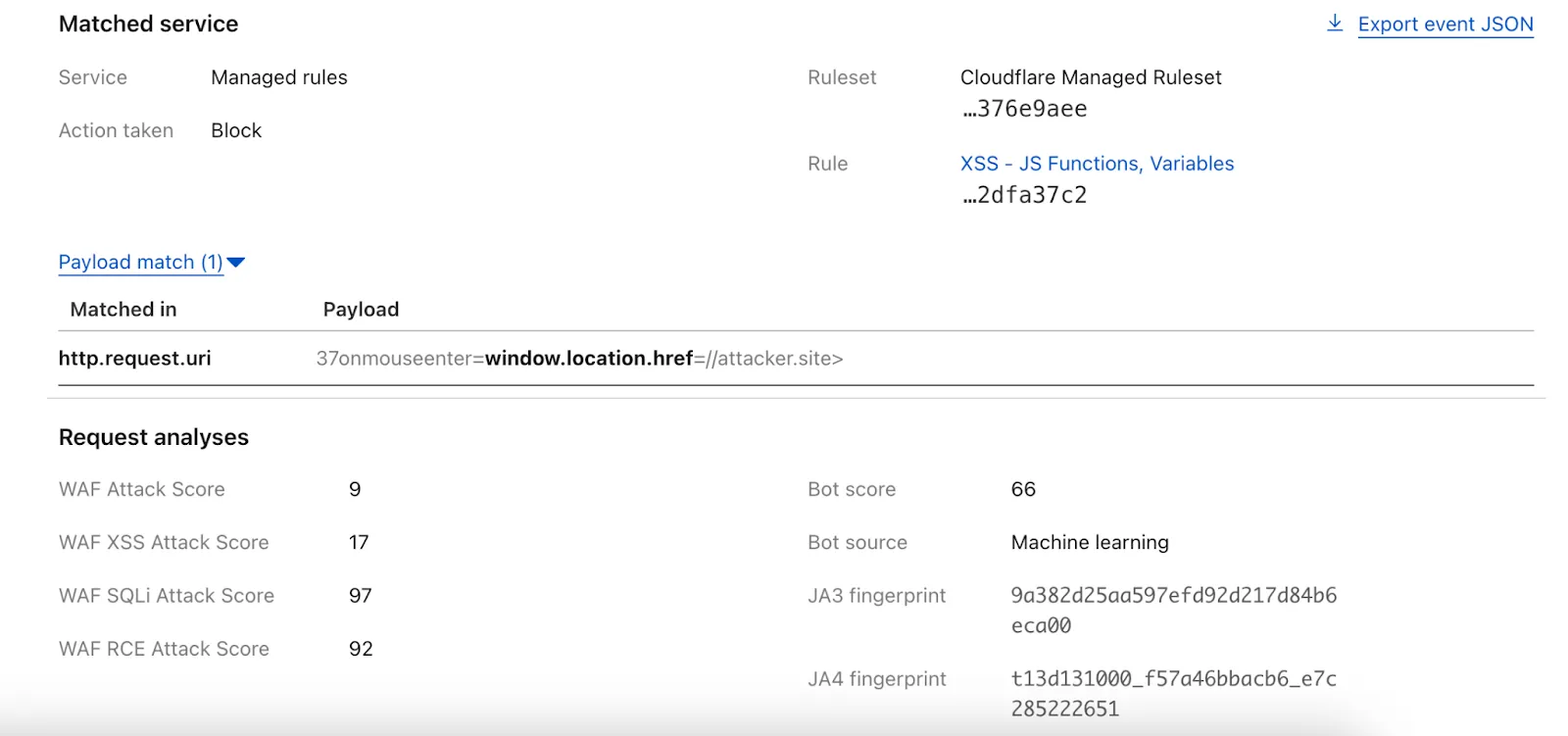
Payload Logging is available to all Enterprise customers. If you have not used Payload Logging before, check how you can get started.
Note: The structure of the
encrypted_matched_datafield in Logpush has changed fromMap<Field, Value>toMap<Field, {Before: bytes, Content: Value, After: bytes}>. If you rely on this field in your Logpush jobs, you should review and update your processing logic accordingly.
This week's analysis covers five CVEs with varying impact levels. Four are rated critical, while one is rated high severity. Remote Code Execution vulnerabilities dominate this set.
Key Findings
GFI KerioControl (CVE-2024-52875) contains an unauthenticated Remote Code Execution (RCE) vulnerability that targets firewall appliances. This vulnerability can let attackers gain root level system access, making this CVE particularly attractive for threat actors.
The SonicWall SMA vulnerabilities remain concerning due to their continued exploitation since 2021. These critical vulnerabilities in remote access solutions create dangerous entry points to networks.
Impact
Customers using the Managed Ruleset will receive rule coverage following this week's release. Below is a breakdown of the recommended prioritization based on current exploitation trends:
- GFI KerioControl (CVE-2024-52875) - Highest priority; unauthenticated RCE
- SonicWall SMA (Multiple vulnerabilities) - Critical for network appliances
- XWiki (CVE-2025-24893) - High priority for development environments
- Langflow (CVE-2025-3248) - Important for AI workflow platforms
- MinIO (CVE-2025-31489) - Important for object storage implementations
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100724 GFI KerioControl - Remote Code Execution - CVE:CVE-2024-52875 Log Block This is a New Detection Cloudflare Managed Ruleset 100748 XWiki - Remote Code Execution - CVE:CVE-2025-24893 Log Block This is a New Detection Cloudflare Managed Ruleset 100750 SonicWall SMA - Dangerous File Upload - CVE:CVE-2021-20040, CVE:CVE-2021-20041, CVE:CVE-2021-20042
Log Block This is a New Detection Cloudflare Managed Ruleset 100751 Langflow - Remote Code Execution - CVE:CVE-2025-3248 Log Block This is a New Detection Cloudflare Managed Ruleset 100752 MinIO - Auth Bypass - CVE:CVE-2025-31489 Log Block This is a New Detection
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100755 React.js - Router and Remix Vulnerability - CVE:CVE-2025-43864, CVE:CVE-2025-43865
Block Block This is a New Detection
Each of this week's rule releases covers a distinct CVE, with half of the rules targeting Remote Code Execution (RCE) attacks. Of the 6 CVEs covered, four were scored as critical, with the other two scored as high.
When deciding which exploits to tackle, Cloudflare tunes into the attackers' areas of focus. Cloudflare's network intelligence provides a unique lens into attacker activity – for instance, through the volume of blocked requests related with CVE exploits after updating WAF Managed Rules with new detections.
From this week's releases, one indicator that RCE is a "hot topic" attack type is the fact that the Oracle PeopleSoft RCE rule accounts for half of all of the new rule matches. This rule patches CVE-2023-22047, a high-severity vulnerability in the Oracle PeopleSoft suite that allows unauthenticated attackers to access PeopleSoft Enterprise PeopleTools data through remote code execution. This is particularly concerning because of the nature of the data managed by PeopleSoft – this can include payroll records or student profile information. This CVE, along with five others, are addressed with the latest detection update to WAF Managed Rules.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100738 GitLab - Auth Bypass - CVE:CVE-2023-7028 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100740 Splunk Enterprise - Remote Code Execution - CVE:CVE-2025-20229 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100741 Oracle PeopleSoft - Remote Code Execution - CVE:CVE-2023-22047 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100742 CrushFTP - Auth Bypass - CVE:CVE-2025-31161 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100743 Ivanti - Buffer Error - CVE:CVE-2025-22457 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100744 Oracle Access Manager - Remote Code Execution - CVE:CVE-2021-35587
Log Disabled This is a New Detection
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100739A Next.js - Auth Bypass - CVE:CVE-2025-29927 - 2 Log Disabled This is a New Detection
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100732 Sitecore - Code Injection - CVE:CVE-2025-27218 Log Block This is a New Detection Cloudflare Managed Ruleset 100733 Angular-Base64-Upload - Remote Code Execution - CVE:CVE-2024-42640
Log Block This is a New Detection Cloudflare Managed Ruleset 100734 Apache Camel - Remote Code Execution - CVE:CVE-2025-29891 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100735 Progress Software WhatsUp Gold - Remote Code Execution - CVE:CVE-2024-4885
Log Block This is a New Detection Cloudflare Managed Ruleset 100737 Apache Tomcat - Remote Code Execution - CVE:CVE-2025-24813 Log Block This is a New Detection Cloudflare Managed Ruleset 100659 Common Payloads for Server-side Template Injection N/A Disabled N/A Cloudflare Managed Ruleset 100659 Common Payloads for Server-side Template Injection - Base64 N/A Disabled N/A Cloudflare Managed Ruleset 100642 LDAP Injection N/A Disabled N/A Cloudflare Managed Ruleset 100642 LDAP Injection Base64 N/A Disabled N/A Cloudflare Managed Ruleset 100005 DotNetNuke - File Inclusion - CVE:CVE-2018-9126, CVE:CVE-2011-1892, CVE:CVE-2022-31474
N/A Disabled N/A Cloudflare Managed Ruleset 100527 Apache Struts - CVE:CVE-2021-31805 N/A Block N/A Cloudflare Managed Ruleset 100702 Command Injection - CVE:CVE-2022-24108 N/A Block N/A Cloudflare Managed Ruleset 100622C Ivanti - Command Injection - CVE:CVE-2023-46805, CVE:CVE-2024-21887, CVE:CVE-2024-22024
N/A Block N/A Cloudflare Managed Ruleset 100536C GraphQL Command Injection N/A Disabled N/A Cloudflare Managed Ruleset 100536 GraphQL Injection N/A Disabled N/A Cloudflare Managed Ruleset 100536A GraphQL Introspection N/A Disabled N/A Cloudflare Managed Ruleset 100536B GraphQL SSRF N/A Disabled N/A Cloudflare Managed Ruleset 100559A Prototype Pollution - Common Payloads N/A Disabled N/A Cloudflare Managed Ruleset 100559A Prototype Pollution - Common Payloads - Base64 N/A Disabled N/A Cloudflare Managed Ruleset 100734 Apache Camel - Remote Code Execution - CVE:CVE-2025-29891 N/A Disabled N/A
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100739 Next.js - Auth Bypass - CVE:CVE-2025-29927 N/A Disabled This is a New Detection
Update: Mon Mar 24th, 11PM UTC: Next.js has made further changes to address a smaller vulnerability introduced in the patches made to its middleware handling. Users should upgrade to Next.js versions
15.2.4,14.2.26,13.5.10or12.3.6. If you are unable to immediately upgrade or are running an older version of Next.js, you can enable the WAF rule described in this changelog as a mitigation.Update: Mon Mar 24th, 8PM UTC: Next.js has now backported the patch for this vulnerability ↗ to cover Next.js v12 and v13. Users on those versions will need to patch to
13.5.9and12.3.5(respectively) to mitigate the vulnerability.Update: Sat Mar 22nd, 4PM UTC: We have changed this WAF rule to opt-in only, as sites that use auth middleware with third-party auth vendors were observing failing requests.
We strongly recommend updating your version of Next.js (if eligible) to the patched versions, as your app will otherwise be vulnerable to an authentication bypass attack regardless of auth provider.
This rule is opt-in only for sites on the Pro plan or above in the WAF managed ruleset.
To enable the rule:
- Head to Security > WAF > Managed rules in the Cloudflare dashboard for the zone (website) you want to protect.
- Click the three dots next to Cloudflare Managed Ruleset and choose Edit
- Scroll down and choose Browse Rules
- Search for CVE-2025-29927 (ruleId:
34583778093748cc83ff7b38f472013e) - Change the Status to Enabled and the Action to Block. You can optionally set the rule to Log, to validate potential impact before enabling it. Log will not block requests.
- Click Next
- Scroll down and choose Save
This will enable the WAF rule and block requests with the
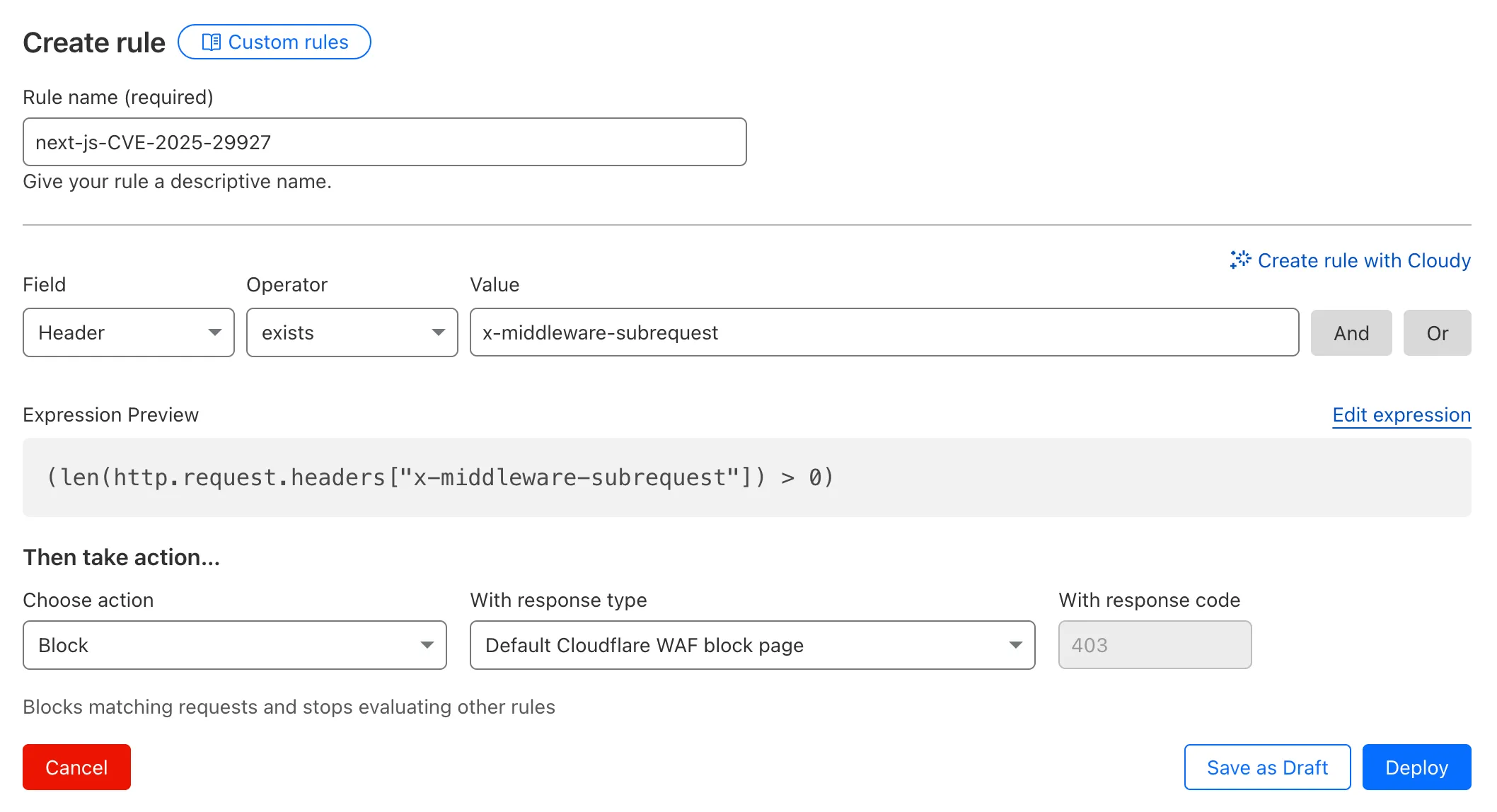
x-middleware-subrequestheader regardless of Next.js version.For users on the Free plan, or who want to define a more specific rule, you can create a Custom WAF rule to block requests with the
x-middleware-subrequestheader regardless of Next.js version.To create a custom rule:
- Head to Security > WAF > Custom rules in the Cloudflare dashboard for the zone (website) you want to protect.
- Give the rule a name - e.g.
next-js-CVE-2025-29927 - Set the matching parameters for the rule match any request where the
x-middleware-subrequestheaderexistsper the rule expression below.
Terminal window (len(http.request.headers["x-middleware-subrequest"]) > 0)- Set the action to 'block'. If you want to observe the impact before blocking requests, set the action to 'log' (and edit the rule later).
- Deploy the rule.
We've made a WAF (Web Application Firewall) rule available to all sites on Cloudflare to protect against the Next.js authentication bypass vulnerability ↗ (
CVE-2025-29927) published on March 21st, 2025.Note: This rule is not enabled by default as it blocked requests across sites for specific authentication middleware.
- This managed rule protects sites using Next.js on Workers and Pages, as well as sites using Cloudflare to protect Next.js applications hosted elsewhere.
- This rule has been made available (but not enabled by default) to all sites as part of our WAF Managed Ruleset and blocks requests that attempt to bypass authentication in Next.js applications.
- The vulnerability affects almost all Next.js versions, and has been fully patched in Next.js
14.2.26and15.2.4. Earlier, interim releases did not fully patch this vulnerability. - Users on older versions of Next.js (
11.1.4to13.5.6) did not originally have a patch available, but this the patch for this vulnerability and a subsequent additional patch have been backported to Next.js versions12.3.6and13.5.10as of Monday, March 24th. Users on Next.js v11 will need to deploy the stated workaround or enable the WAF rule.
The managed WAF rule mitigates this by blocking external user requests with the
x-middleware-subrequestheader regardless of Next.js version, but we recommend users using Next.js 14 and 15 upgrade to the patched versions of Next.js as an additional mitigation.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100736 Generic HTTP Request Smuggling N/A Disabled This is a New Detection
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100725 Fortinet FortiManager - Remote Code Execution - CVE:CVE-2023-42791, CVE:CVE-2024-23666
Log Block Cloudflare Managed Ruleset 100726 Ivanti - Remote Code Execution - CVE:CVE-2024-8190 Log Block Cloudflare Managed Ruleset 100727 Cisco IOS XE - Remote Code Execution - CVE:CVE-2023-20198 Log Disabled Fixed action value in changelog; no rule changes. Cloudflare Managed Ruleset 100728 Sitecore - Remote Code Execution - CVE:CVE-2024-46938 Log Block Cloudflare Managed Ruleset 100729 Microsoft SharePoint - Remote Code Execution - CVE:CVE-2023-33160 Log Block Cloudflare Managed Ruleset 100730 Pentaho - Template Injection - CVE:CVE-2022-43769, CVE:CVE-2022-43939
Log Block Cloudflare Managed Ruleset 100700 Apache SSRF vulnerability CVE-2021-40438 N/A Block
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100731 Apache Camel - Code Injection - CVE:CVE-2025-27636 N/A Block This is a New Detection
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100722 Ivanti - Information Disclosure - CVE:CVE-2025-0282 Log Block This is a New Detection Cloudflare Managed Ruleset 100723 Cisco IOS XE - Information Disclosure - CVE:CVE-2023-20198 Log Block This is a New Detection
Added new records to the leaked credentials database. The record sources are: Have I Been Pwned (HIBP) database, RockYou 2024 dataset, and another third-party database.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100721 Ivanti - Remote Code Execution - CVE:CVE-2024-13159, CVE:CVE-2024-13160, CVE:CVE-2024-13161
Log Block This is a New Detection Cloudflare Managed Ruleset 100596 Citrix Content Collaboration ShareFile - Remote Code Execution - CVE:CVE-2023-24489
N/A Block
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100718A SonicWall SSLVPN 2 - Auth Bypass - CVE:CVE-2024-53704 Log Block This is a New Detection Cloudflare Managed Ruleset 100720 Palo Alto Networks - Auth Bypass - CVE:CVE-2025-0108 Log Block This is a New Detection
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100715 FortiOS - Auth Bypass - CVE:CVE-2024-55591 Log Block This is a New Detection Cloudflare Managed Ruleset 100716 Ivanti - Auth Bypass - CVE:CVE-2021-44529 Log Block This is a New Detection Cloudflare Managed Ruleset 100717 SimpleHelp - Auth Bypass - CVE:CVE-2024-57727 Log Block This is a New Detection Cloudflare Managed Ruleset 100718 SonicWall SSLVPN - Auth Bypass - CVE:CVE-2024-53704 Log Block This is a New Detection Cloudflare Managed Ruleset 100719 Yeti Platform - Auth Bypass - CVE:CVE-2024-46507 Log Block This is a New Detection
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100708 Aviatrix Network - Remote Code Execution - CVE:CVE-2024-50603 Log Block This is a New Detection Cloudflare Managed Ruleset 100709 Next.js - Remote Code Execution - CVE:CVE-2024-46982 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100710 Progress Software WhatsUp Gold - Directory Traversal - CVE:CVE-2024-12105
Log Block This is a New Detection Cloudflare Managed Ruleset 100711 WordPress - Remote Code Execution - CVE:CVE-2024-56064 Log Block This is a New Detection Cloudflare Managed Ruleset 100712 WordPress - Remote Code Execution - CVE:CVE-2024-9047 Log Block This is a New Detection Cloudflare Managed Ruleset 100713 FortiOS - Auth Bypass - CVE:CVE-2022-40684 Log Block This is a New Detection
Added new records to the leaked credentials database from a third-party database.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100303 Command Injection - Nslookup Log Block This was released as
Cloudflare Managed Ruleset 100534 Web Shell Activity Log Block This was released as
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100704 Cleo Harmony - Auth Bypass - CVE:CVE-2024-55956, CVE:CVE-2024-55953
Log Block New Detection Cloudflare Managed Ruleset 100705 Sentry - SSRF Log Block New Detection Cloudflare Managed Ruleset 100706 Apache Struts - Remote Code Execution - CVE:CVE-2024-53677 Log Block New Detection Cloudflare Managed Ruleset 100707 FortiWLM - Remote Code Execution - CVE:CVE-2023-48782, CVE:CVE-2023-34993, CVE:CVE-2023-34990
Log Block New Detection Cloudflare Managed Ruleset 100007C_BETA Command Injection - Common Attack Commands Disabled
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Specials 100678 Pandora FMS - Remote Code Execution - CVE:CVE-2024-11320 Log Block New Detection Cloudflare Specials 100679 Palo Alto Networks - Remote Code Execution - CVE:CVE-2024-0012, CVE:CVE-2024-9474
Log Block New Detection Cloudflare Specials 100680 Ivanti - Command Injection - CVE:CVE-2024-37397 Log Block New Detection Cloudflare Specials 100681 Really Simple Security - Auth Bypass - CVE:CVE-2024-10924 Log Block New Detection Cloudflare Specials 100682 Magento - XXE - CVE:CVE-2024-34102 Log Block New Detection Cloudflare Specials 100683 CyberPanel - Remote Code Execution - CVE:CVE-2024-51567 Log Block New Detection Cloudflare Specials 100684 Microsoft SharePoint - Remote Code Execution - CVE:CVE-2024-38094, CVE:CVE-2024-38024, CVE:CVE-2024-38023
Log Block New Detection Cloudflare Specials 100685 CyberPanel - Remote Code Execution - CVE:CVE-2024-51568 Log Block New Detection Cloudflare Specials 100686 Seeyon - Remote Code Execution Log Block New Detection Cloudflare Specials 100687 WordPress - Remote Code Execution - CVE:CVE-2024-10781, CVE:CVE-2024-10542
Log Block New Detection Cloudflare Specials 100688 ProjectSend - Remote Code Execution - CVE:CVE-2024-11680 Log Block New Detection Cloudflare Specials 100689 Palo Alto GlobalProtect - Remote Code Execution - CVE:CVE-2024-5921
Log Block New Detection Cloudflare Specials 100690 Ivanti - Remote Code Execution - CVE:CVE-2024-37404 Log Block New Detection Cloudflare Specials 100691 Array Networks - Remote Code Execution - CVE:CVE-2023-28461 Log Block New Detection Cloudflare Specials 100692 CyberPanel - Remote Code Execution - CVE:CVE-2024-51378 Log Block New Detection Cloudflare Specials 100693 Symfony Profiler - Auth Bypass - CVE:CVE-2024-50340 Log Block New Detection Cloudflare Specials 100694 Citrix Virtual Apps - Remote Code Execution - CVE:CVE-2024-8069 Log Block New Detection Cloudflare Specials 100695 MSMQ Service - Remote Code Execution - CVE:CVE-2023-21554 Log Block New Detection Cloudflare Specials 100696 Nginxui - Remote Code Execution - CVE:CVE-2024-49368 Log Block New Detection Cloudflare Specials 100697 Apache ShardingSphere - Remote Code Execution - CVE:CVE-2022-22733
Log Block New Detection Cloudflare Specials 100698 Mitel MiCollab - Auth Bypass - CVE:CVE-2024-41713 Log Block New Detection Cloudflare Specials 100699 Apache Solr - Auth Bypass - CVE:CVE-2024-45216 Log Block New Detection