pfSense
This tutorial includes the steps required to configure IPsec tunnels to connect a pfSense firewall to Cloudflare Magic WAN.
| Manufacturer | Firmware revision |
|---|---|
| pfSense | 24.03 |
For this tutorial, you will need to know the following information:
- Your Anycast IP addresses (given to you by Cloudflare)
- External IP addresses
- Internal IP address ranges
- Inside tunnel
/31ranges
The following IP addresses are used throughout this tutorial. Any legally routable IP addresses have been replaced with IPv4 Address Blocks Reserved for Documentation (RFC 5737 ↗) addresses within the 203.0.113.0/24 subnet.
| Tunnel name | PF_TUNNEL_01 | PF_TUNNEL_02 |
|---|---|---|
| Interface address | 10.252.2.26/31 | 10.252.2.28/31 |
| Customer endpoint | 203.0.113.254 | 203.0.113.254 |
| Cloudflare endpoint | <YOUR_ANYCAST_IP_ADDRESS_1> | <YOUR_ANYCAST_IP_ADDRESS_2> |
| Pfsense IPsec Phase 2 Local IP | 10.252.2.27 | 10.252.2.29 |
| Pfsense IPsec Phase 2 Remote IP | 10.252.2.26 | 10.252.2.28 |
| Magic WAN static routes - Prefix | 10.1.100.0/24 | 10.1.100.0/24 |
| Magic WAN static routes - Next hop | PF_TUNNEL_01 | PF_TUNNEL_02 |
Use the Cloudflare dashboard or API to configure two IPsec tunnels. The settings mentioned below are used for the IPsec tunnels referenced throughout the remainder of this guide.
- Follow the Add tunnels instructions to create the required IPsec tunnels with the following options:
- Tunnel name:
PF_TUNNEL_01 - Interface address:
10.252.2.26/31 - Customer endpoint:
203.0.113.254 - Cloudflare endpoint: Enter the Anycast IP address provided by Cloudflare.
- Health check rate: Medium
- Health check type: Request
- Health check direction: Bidirectional
- Tunnel name:
- Select Add pre-shared key later > Add tunnels.
- Repeat the process to create a second IPsec tunnel with the following options:
- Tunnel name:
PF_TUNNEL_02 - Interface address:
10.252.2.28/31 - Customer endpoint:
203.0.113.254 - Cloudflare endpoint: Enter the Anycast IP address provided by Cloudflare.
- Health check rate: Medium
- Health check type: Request
- Health check direction: Bidirectional
- Tunnel name:
- Select Add pre-shared key later > Add tunnels.
When you create IPsec tunnels with the option Add pre-shared key later, the Cloudflare dashboard will show you a warning indicator.
- Select Edit to edit the properties of each IPsec tunnel you have created.
- Select Generate a new pre-shared key > Update and generate pre-shared key.
- Copy the pre-shared key value for each of your IPsec tunnels, and save these values somewhere safe. Then, select Done.
After creating your IPsec tunnels, the Cloudflare dashboard will list them under Tunnels. To retrieve your IPsec tunnel's user ID:
- Go to Magic WAN > Configuration.
- Select Tunnels.
- Select the IPsec tunnel.
- Scroll to User ID and copy the string. For example,
ipsec@long_string_of_letters_and_numbers.
The User ID will be required when configuring IKE Phase 1 on the pfSense firewall.
Create a static route for each of the two IPsec tunnels configured in the previous section, with the following settings (settings not mentioned here can be left with their default values):
- Description:
PF_TUNNEL_01 - Prefix:
10.1.100.0/24 - Tunnel/Next hop:
PF_TUNNEL_01
- Description:
PF_TUNNEL_02 - Prefix:
10.1.100.0/24 - Tunnel/Next hop:
PF_TUNNEL_02
Install pfSense and boot up. Then, assign and set LAN and WAN interfaces, as well as IP addresses. For example:
- LAN:
203.0.113.254 - WAN:
<YOUR_WAN_ADDRESS>
Add a new IPsec tunnel Phase 1 entry ↗, with the following settings:
- General Information
- Description:
CF1_IPsec_P1
- Description:
- IKE Endpoint Configuration
- Key exchange version: IKE_v2
- Internet Protocol: IPv4
- Interface: WAN
- Remote gateway: Enter your Cloudflare Anycast IP address.
- Phase 1 Proposal (Authentication)
- Authentication method: Mutual PSK
- My identifier: User Fully qualified domain name >
ipsec@long_string_of_letters_and_numbers
(You can get this identifier from your Cloudflare IPsec tunnel configuration > User ID) - Peer identifier: Peer IP Address (your Cloudflare Anycast IP)
- Pre-Shared Key: Enter the PSK you have on your Cloudflare IPsec tunnel.
- Phase 1 proposal (Encryption algorithm)
- Encryption algorithm: AES 256 bits
- Key length: 256 bits
- Hash algorithm: SHA256
- DH key group: 20
- Lifetime:
86400
Add a new IPsec tunnel Phase 2 entry ↗, with the following settings. You need to create an entry for tunnel 1 and 2, making the appropriate changes for the IP addresses for local and remote network:
- General Information
- Description:
CF1_IPsec_P2 - Mode: Routed (VTI)
- Description:
- Networks
- Local Network: Address > Upper IP address in the
/31assigned in Cloudflare tunnel. For example,10.252.2.27for tunnel 1 and10.252.2.29for tunnel 2. - Remote Network: Address > Lower IP address in the
/31for Cloudflare side. For example,10.252.2.26for tunnel 1, and10.252.2.28for tunnel 2.
- Local Network: Address > Upper IP address in the
- Phase 2 Proposal (SA/Key Exchange)
- Protocol: ESP
- Encryption algorithm: AES 256 bits
- Hash algorithm: SHA256
- DH key group: 20
- Lifetime:
28800
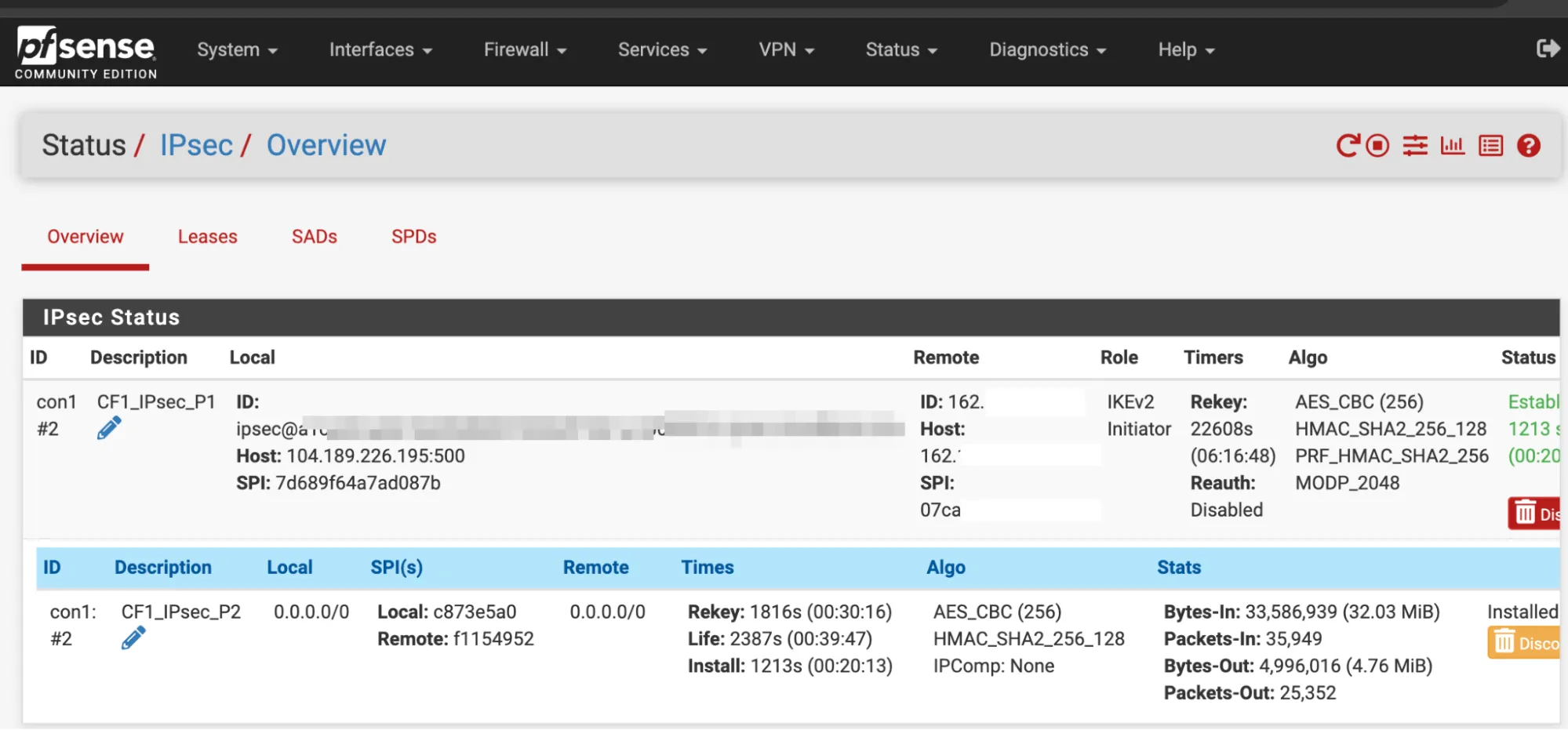
When you are finished, apply your changes. If you go to Status > IPsec, you should be able to check that both Phase 1 and Phase 2 are connected.
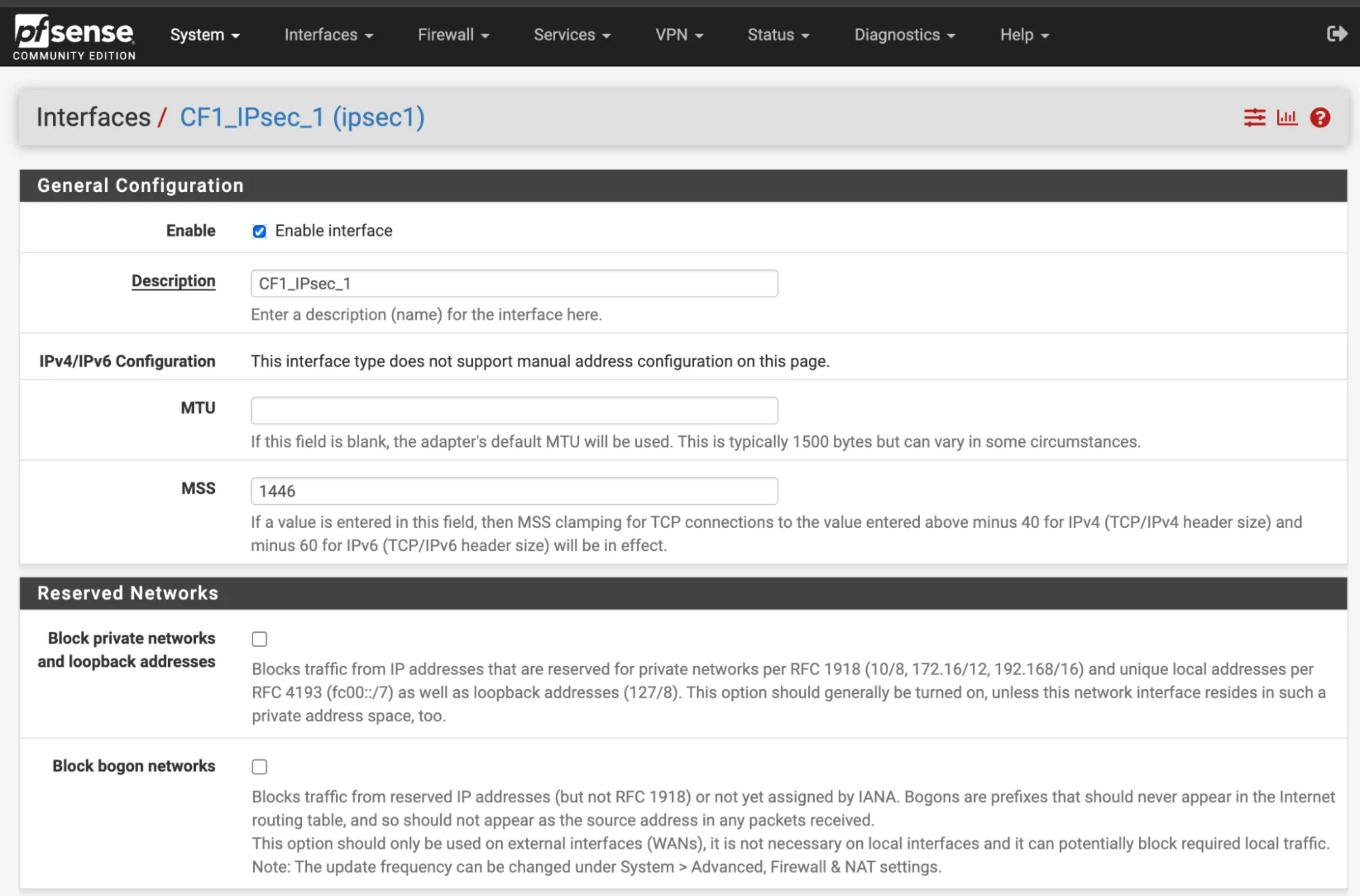
In Interfaces > Assignments > Add, create a new interface to assign to the first IPsec tunnel, with the following settings:
- General configuration
- Description:
CF1_IPsec_1 - MSS:
1446
- Description:
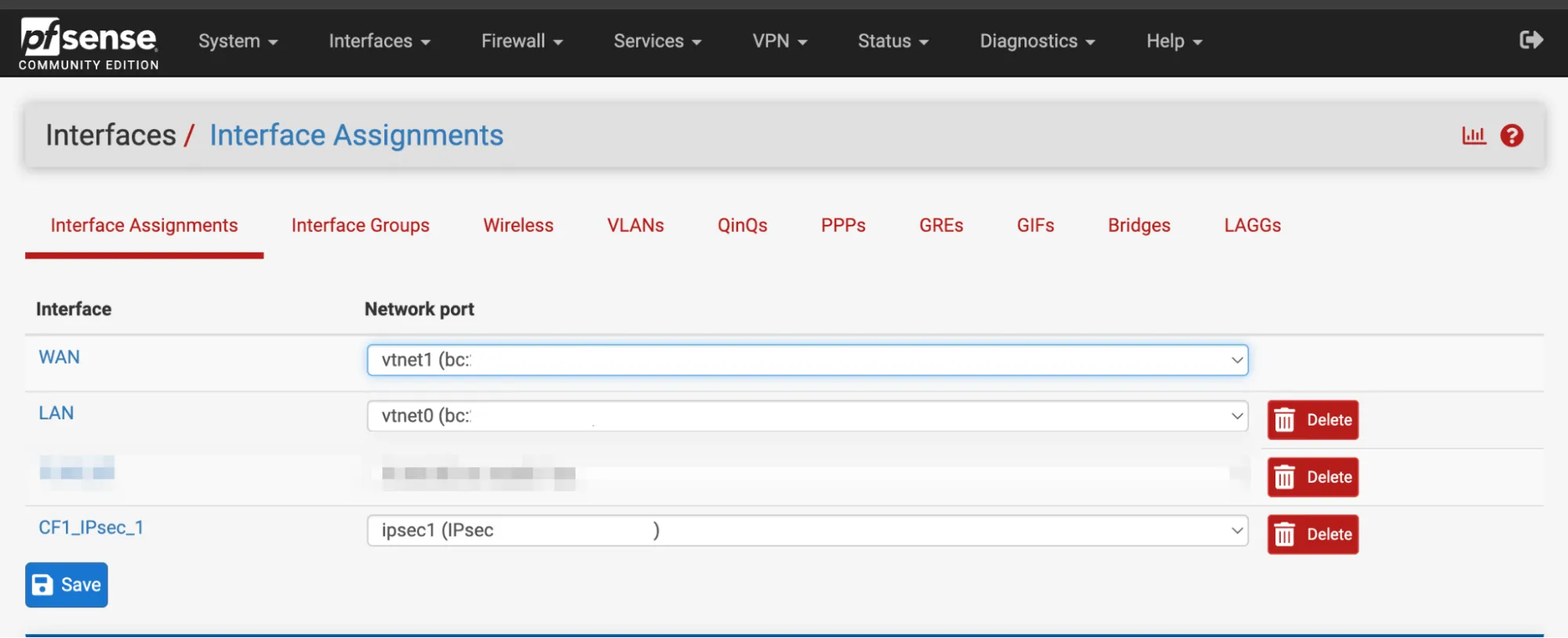
- Interface Assignments
- WAN: Add your WAN interface. For example,
vnet1. - LAN: Add your LAN interface. For example,
vnet0. - Add your CF_IPsec_1 that you have created above for Phase 1.
- WAN: Add your WAN interface. For example,
Select Save when you are finished.
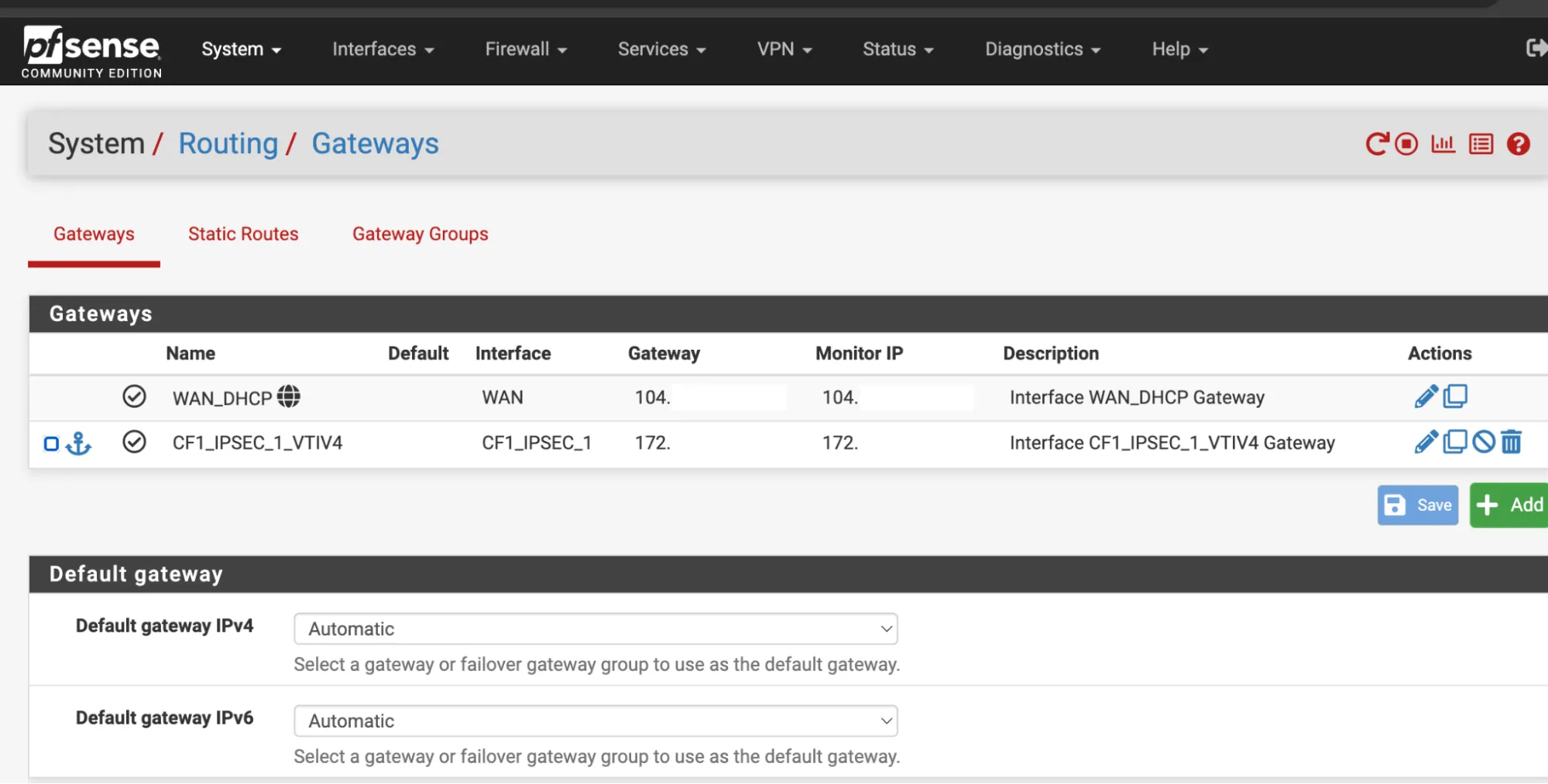
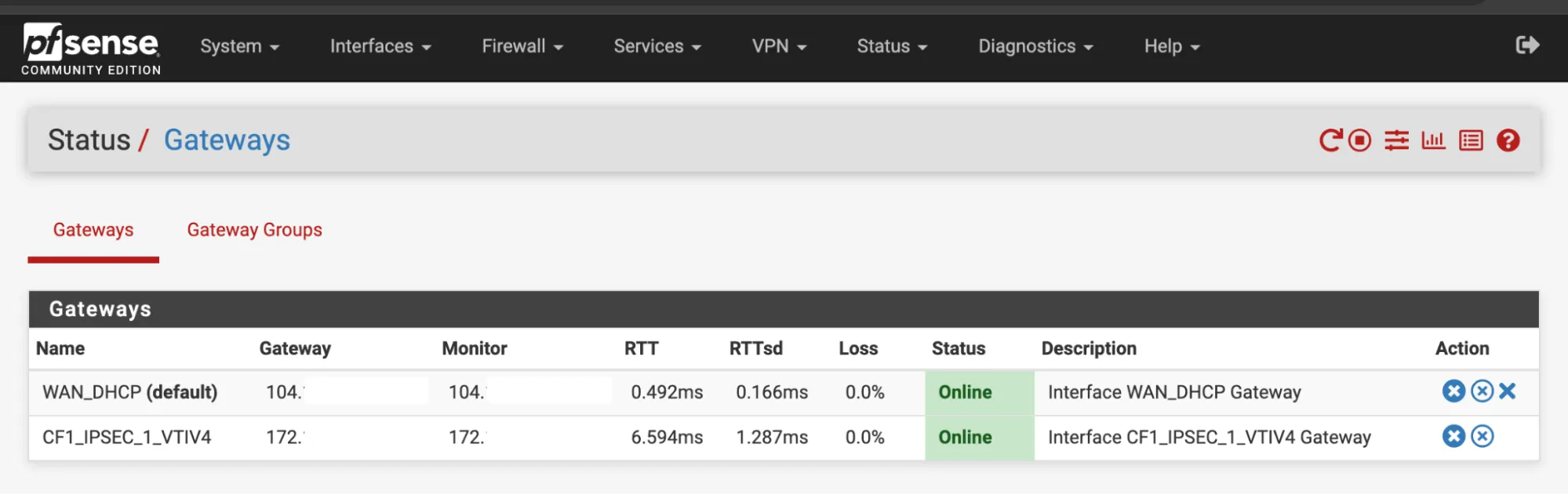
In System > Routing > Gateways there should already be a gateway. For this example, it is named CF1_IPSEC_1_VTIV4.
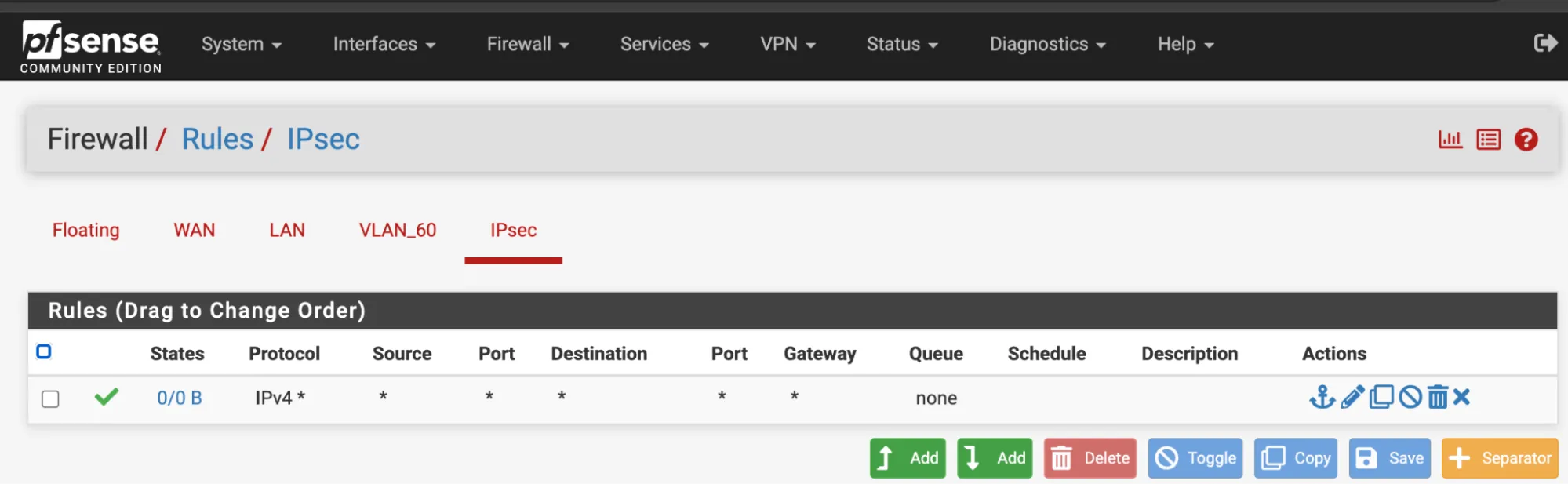
- In Firewall Rules > IPsec interface, allow any type of traffic.
- Navigate to Status > Gateways.
CF1_IPSEC_1_VTIV4should now be online.
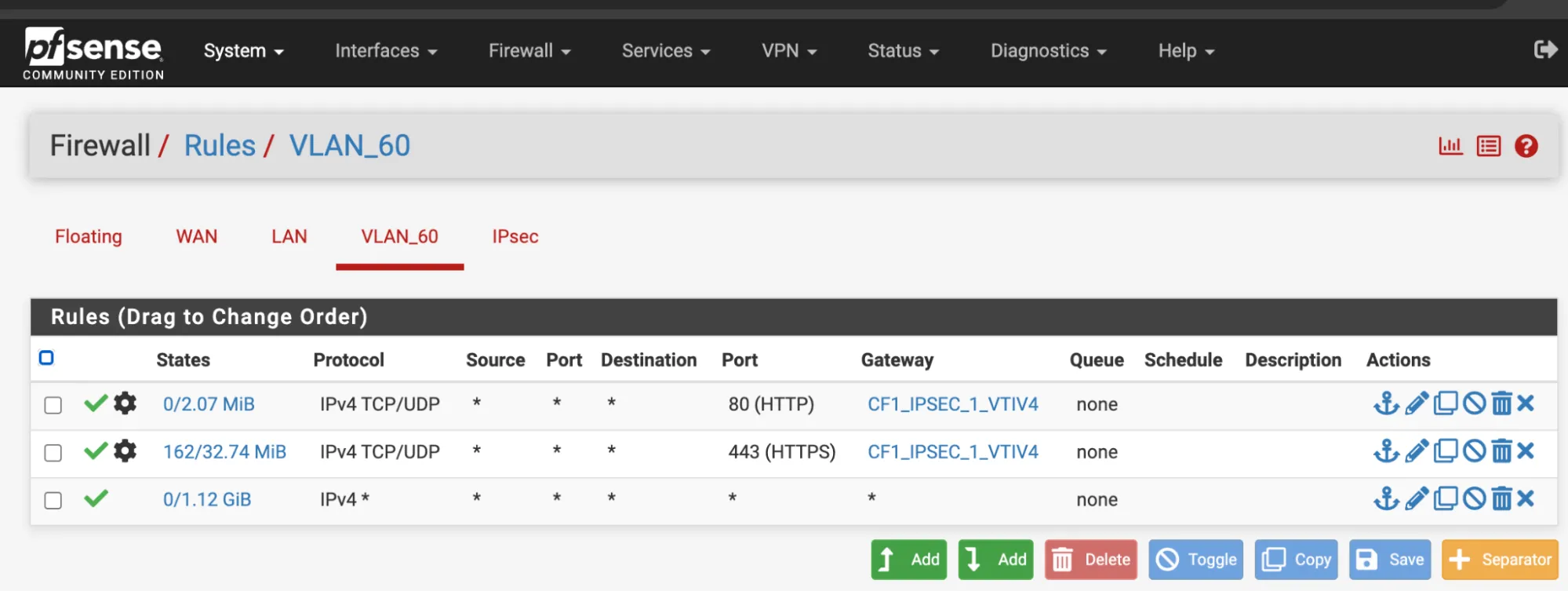
- In Firewall > Rules > LAN, allow any type of traffic.
- Expand the Advanced section.
- Change the Gateway to
CF1_IPSEC_1_VTIV4.
Was this helpful?
- Resources
- API
- New to Cloudflare?
- Products
- Sponsorships
- Open Source
- Support
- Help Center
- System Status
- Compliance
- GDPR
- Company
- cloudflare.com
- Our team
- Careers
- 2025 Cloudflare, Inc.
- Privacy Policy
- Terms of Use
- Report Security Issues
- Trademark